- AppLock (АпЛок) 1.0
- AppLocker
- When to use AppLocker
- Installing AppLocker
- Using AppLocker on Server Core
- Virtualization considerations
- Security considerations
- AppLocker 1.3
- Блокировка
- Добавление программ в список
- Удаление из списка
- Снятие блокировки
- Преимущества
- Недостатки
- Use AppLocker to create a Windows 10 kiosk that runs multiple apps
- Install apps
- Use AppLocker to set rules for apps
- Other settings to lock down
- Customize Start screen layout for the device (recommended)
AppLock (АпЛок) 1.0
Владельцам мобильных устройств с операционной системой Андроид может быть знакомо популярное приложение AppLock, которое позволяет блокировать доступ к любым приложениям или играм, находящимся на вашем смартфоне или планшете.
Так вот для ОС Windows появилась аналогичная одноименная бесплатная программа с тем же функционалом, а именно возможностью ограничения запуска программного обеспечения и игр. Благодаря АпЛок вы сможете предотвратить открытие указанных приложений на компьютере.
Чтобы App Lock начал работать, вам нужно сформировать список программ, которые будут блокированы, а затем активировать блокировщик. После этого другие пользователи не смогут использовать приложения, находящиеся в составленном списке.
Для большей надежности на это ПО можно установить ключ, это действие не даст другим юзерам разблокировать доступ к программам или играм. А если вам понадобится воспользоваться приложением из списка, просто отключите блокировщик.
Список заблокированных программ можно изменять в любое время, т.е. вы можете добавлять в него новые элементы или удалять имеющиеся, когда захотите, эти операции облегчает интуитивно-понятный интерфейс.
Если вам нужно ограничить запуск определенных приложений на вашем ПК, тогда стоит скачать AppLock на русском языке. Программа схожа с подобным приложением для Android имеющим такое же название и обеспечивает ничуть не худшие возможности, хоть и создано другими разработчиками.
AppLocker
Applies to
This topic provides a description of AppLocker and can help you decide if your organization can benefit from deploying AppLocker application control policies. AppLocker helps you control which apps and files users can run. These include executable files, scripts, Windows Installer files, dynamic-link libraries (DLLs), packaged apps, and packaged app installers.
AppLocker is unable to control processes running under the system account on any operating system.
AppLocker can help you:
- Define rules based on file attributes that persist across app updates, such as the publisher name (derived from the digital signature), product name, file name, and file version. You can also create rules based on the file path and hash.
- Assign a rule to a security group or an individual user.
- Create exceptions to rules. For example, you can create a rule that allows all users to run all Windows binaries, except the Registry Editor (regedit.exe).
- Use audit-only mode to deploy the policy and understand its impact before enforcing it.
- Create rules on a staging server, test them, then export them to your production environment and import them into a Group Policy Object.
- Simplify creating and managing AppLocker rules by using Windows PowerShell.
AppLocker helps reduce administrative overhead and helps reduce the organization’s cost of managing computing resources by decreasing the number of Help Desk calls that result from users running unapproved apps. AppLocker addresses the following app security scenarios:
Application inventory
AppLocker has the ability to enforce its policy in an audit-only mode where all app access activity is registered in event logs. These events can be collected for further analysis. Windows PowerShell cmdlets also help you analyze this data programmatically.
Protection against unwanted software
AppLocker has the ability to deny apps from running when you exclude them from the list of allowed apps. When AppLocker rules are enforced in the production environment, any apps that are not included in the allowed rules are blocked from running.
Licensing conformance
AppLocker can help you create rules that preclude unlicensed software from running and restrict licensed software to authorized users.
Software standardization
AppLocker policies can be configured to allow only supported or approved apps to run on computers within a business group. This permits a more uniform app deployment.
Manageability improvement
AppLocker includes a number of improvements in manageability as compared to its predecessor Software Restriction Policies. Importing and exporting policies, automatic generation of rules from multiple files, audit-only mode deployment, and Windows PowerShell cmdlets are a few of the improvements over Software Restriction Policies.
When to use AppLocker
In many organizations, information is the most valuable asset, and ensuring that only approved users have access to that information is imperative. Access control technologies, such as Active Directory Rights Management Services (ADВ RMS) and access control lists (ACLs), help control what users are allowed to access.
However, when a user runs a process, that process has the same level of access to data that the user has. As a result, sensitive information could easily be deleted or transmitted out of the organization if a user knowingly or unknowingly runs malicious software. AppLocker can help mitigate these types of security breaches by restricting the files that users or groups are allowed to run. Software publishers are beginning to create more apps that can be installed by non-administrative users. This could jeopardize an organization’s written security policy and circumvent traditional app control solutions that rely on the inability of users to install apps. By creating an allowed list of approved files and apps, AppLocker helps prevent such per-user apps from running. Because AppLocker can control DLLs, it is also useful to control who can install and run ActiveX controls.
AppLocker is ideal for organizations that currently use Group Policy to manage their PCs.
The following are examples of scenarios in which AppLocker can be used:
- Your organization’s security policy dictates the use of only licensed software, so you need to prevent users from running unlicensed software and also restrict the use of licensed software to authorized users.
- An app is no longer supported by your organization, so you need to prevent it from being used by everyone.
- The potential that unwanted software can be introduced in your environment is high, so you need to reduce this threat.
- The license to an app has been revoked or it is expired in your organization, so you need to prevent it from being used by everyone.
- A new app or a new version of an app is deployed, and you need to prevent users from running the old version.
- Specific software tools are not allowed within the organization, or only specific users should have access to those tools.
- A single user or small group of users needs to use a specific app that is denied for all others.
- Some computers in your organization are shared by people who have different software usage needs, and you need to protect specific apps.
- In addition to other measures, you need to control the access to sensitive data through app usage.
AppLocker is a defense-in-depth security feature and not a security boundary. Windows Defender Application Control should be used when the goal is to provide robust protection against a threat and there are expected to be no by-design limitations that would prevent the security feature from achieving this goal.
AppLocker can help you protect the digital assets within your organization, reduce the threat of malicious software being introduced into your environment, and improve the management of application control and the maintenance of application control policies.
Installing AppLocker
AppLocker is included with enterprise-level editions of Windows. You can author AppLocker rules for a single computer or for a group of computers. For a single computer, you can author the rules by using the Local Security Policy editor (secpol.msc). For a group of computers, you can author the rules within a Group Policy Object by using the Group Policy Management Console (GPMC).
The GPMC is available in client computers running Windows only by installing the Remote Server Administration Tools. On computer running Windows Server, you must install the Group Policy Management feature.
Using AppLocker on Server Core
AppLocker on Server Core installations is not supported.
Virtualization considerations
You can administer AppLocker policies by using a virtualized instance of Windows provided it meets all the system requirements listed previously. You can also run Group Policy in a virtualized instance. However, you do risk losing the policies that you created and maintain if the virtualized instance is removed or fails.
Security considerations
Application control policies specify which apps are allowed to run on the local computer.
The variety of forms that malicious software can take make it difficult for users to know what is safe to run. When activated, malicious software can damage content on a hard disk drive, flood a network with requests to cause a denial-of-service (DoS) attack, send confidential information to the Internet, or compromise the security of a computer.
The countermeasure is to create a sound design for your application control policies on PCs in your organization, and then thoroughly test the policies in a lab environment before you deploy them in a production environment. AppLocker can be part of your app control strategy because you can control what software is allowed to run on your computers.
A flawed application control policy implementation can disable necessary applications or allow malicious or unintended software to run. Therefore, it is important that organizations dedicate sufficient resources to manage and troubleshoot the implementation of such policies.
For additional information about specific security issues, see Security considerations for AppLocker.
When you use AppLocker to create application control policies, you should be aware of the following security considerations:
- Who has the rights to set AppLocker policies?
- How do you validate that the policies are enforced?
- What events should you audit?
For reference in your security planning, the following table identifies the baseline settings for a PC with AppLocker installed:
AppLocker 1.3
Запускать программы на компьютере может каждый человек, который им пользуется. Это довольно сложно ограничить, и из-за этого страдает безопасность ваших личных данных. Но при помощи специальных программных инструментов для блокировки приложений это можно сделать быстро и надежно.
AppLocker является таким инструментом, и, хотя функционала в ней маловато, она очень четко выполняет свою главную функцию, и поможет отключить доступ к программам нежелательным пользователям.
Блокировка
Чтобы заблокировать доступ к тому или иному приложению, достаточно просто отметить его галочкой и сохранить изменения.
Добавление программ в список
Добавление приложений в список выполнено очень неудобно если сравнивать с AskAdmin. Софт нельзя добавлять в список напрямую из каталога, где он хранится, нельзя перетащить в список. Единственный способ добавить тот или иной продукт, это указать имя его исполняемого файла.
Удаление из списка
Из списка программы можно удалить поодиночке, либо все сразу.
Снятие блокировки
Чтобы снять блокировку, необходимо убрать галочку рядом с ней и сохранить изменения. Или можно нажать кнопку «Unlock All», чтобы разблокировать все приложения разом.
Преимущества
Недостатки
- Неудобная
- Нет возможности установить пароль
- Допускает самоблокировку
- Мало функций
AppLocker является слегка неудобной, но лаконичной программой, которая умеет делать только одно — блокировать приложения. В ней нельзя установить пароль на софт, как в Program Blocker, нельзя инвертировать выбранные и еще много чего, но именно поэтому разобраться в ней довольно просто.
Use AppLocker to create a Windows 10 kiosk that runs multiple apps
Applies to
Learn how to configure a device running WindowsВ 10 Enterprise or WindowsВ 10 Education, version 1703 and earlier, so that users can only run a few specific apps. The result is similar to a kiosk device, but with multiple apps available. For example, you might set up a library computer so that users can search the catalog and browse the Internet, but can’t run any other apps or change computer settings.
For devices running Windows 10, version 1709, we recommend the multi-app kiosk method.
You can restrict users to a specific set of apps on a device running WindowsВ 10 Enterprise or WindowsВ 10 Education by using AppLocker. AppLocker rules specify which apps are allowed to run on the device.
AppLocker rules are organized into collections based on file format. If no AppLocker rules for a specific rule collection exist, all files with that file format are allowed to run. However, when an AppLocker rule for a specific rule collection is created, only the files explicitly allowed in a rule are permitted to run. For more information, see How AppLocker works.
This topic describes how to lock down apps on a local device. You can also use AppLocker to set rules for applications in a domain by using Group Policy.
Install apps
First, install the desired apps on the device for the target user account(s). This works for both Unified Windows Platform (UWP) apps and Windows desktop apps. For UWP apps, you must log on as that user for the app to install. For desktop apps, you can install an app for all users without logging on to the particular account.
Use AppLocker to set rules for apps
After you install the desired apps, set up AppLocker rules to only allow specific apps, and block everything else.
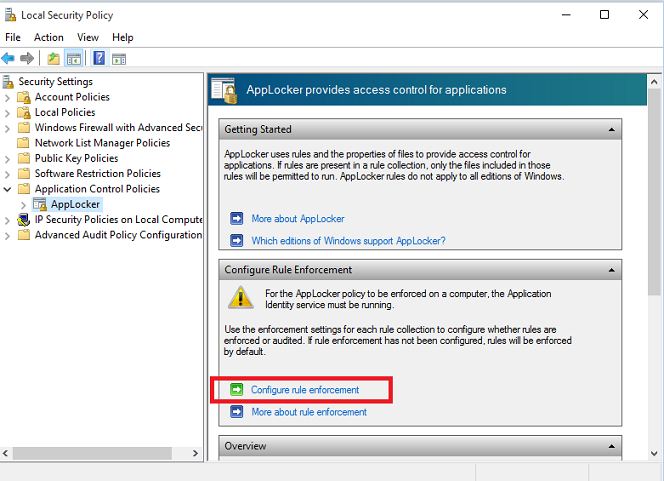
Run Local Security Policy (secpol.msc) as an administrator.
Go to Security Settings > Application Control Policies > AppLocker, and select Configure rule enforcement.
Check Configured under Executable rules, and then click OK.
Right-click Executable Rules and then click Automatically generate rules.
Select the folder that contains the apps that you want to permit, or select C:\ to analyze all apps.
Type a name to identify this set of rules, and then click Next.
On the Rule Preferences page, click Next. Be patient, it might take awhile to generate the rules.
On the Review Rules page, click Create. The wizard will now create a set of rules allowing the installed set of apps.
Read the message and click Yes.
(optional) If you want a rule to apply to a specific set of users, right-click on the rule and select Properties. Then use the dialog to choose a different user or group of users.
(optional) If rules were generated for apps that should not be run, you can delete them by right-clicking on the rule and selecting Delete.
Before AppLocker will enforce rules, the Application Identity service must be turned on. To force the Application Identity service to automatically start on reset, open a command prompt and run:
Restart the device.
Other settings to lock down
In addition to specifying the apps that users can run, you should also restrict some settings and functions on the device. For a more secure experience, we recommend that you make the following configuration changes to the device:
Remove All apps.
Go to Group Policy Editor > User Configuration > Administrative Templates\Start Menu and Taskbar\Remove All Programs list from the Start menu.
Hide Ease of access feature on the logon screen.
Go to Control Panel > Ease of Access > Ease of Access Center, and turn off all accessibility tools.
Disable the hardware power button.
Go to Power Options > Choose what the power button does, change the setting to Do nothing, and then Save changes.
Disable the camera.
Go to Settings > Privacy > Camera, and turn off Let apps use my camera.
Turn off app notifications on the lock screen.
Go to Group Policy Editor > Computer Configuration > Administrative Templates\System\Logon\Turn off app notifications on the lock screen.
Disable removable media.
Go to Group Policy Editor > Computer Configuration > Administrative Templates\System\Device Installation\Device Installation Restrictions. Review the policy settings available in Device Installation Restrictions for the settings applicable to your situation.
NoteВ В To prevent this policy from affecting a member of the Administrators group, in Device Installation Restrictions, enable Allow administrators to override Device Installation Restriction policies.
To learn more about locking down features, see Customizations for Windows 10 Enterprise.
Customize Start screen layout for the device (recommended)
Configure the Start menu on the device to only show tiles for the permitted apps. You will make the changes manually, export the layout to an .xml file, and then apply that file to devices to prevent users from making changes. For instructions, see Manage Windows 10 Start layout options.