- BIND 9
- Why use BIND 9?
- BIND Uses on the Internet
- Almost every Internet connection starts with a DNS lookup
- BIND 9 on the Internet
- Getting Started
- Choosing a version
- Installation
- Configuration
- Maintenance
- Minimal ANY Responses
- Minimum Re-load Time
- HSM Support
- DNSSEC with In-line Signing
- Catalog Zones
- DNSTAP
- Scaleable Primary-Secondary Hierarchy
- NX Domain re-direct
- Maximum Cache Hit Rate
- Flexible Cache Controls
- Views — Split DNS
- Resolver Rate-limiting
- DNSSEC Validation
- Response Policy Zones — RPZ
- DNS Privacy
- Download BIND
- ISC builds and maintains packages for every major operating system or download sources and build it yourself.
- Установка и настройка DNS сервера BIND под Windows для разблокировки ЖЖ и Гугла
- Bind windows 64 bit
- Download and install the Bind 9 Software
- Configure Bind
- Configure your zone
- Start the Bind service
- Create a Bind Reload batch file
- If you wish your Bind server to serve recursion
- Active Directory Integration
BIND 9
Versatile, classic, complete name server software
Why use BIND 9?
BIND 9 has evolved to be a very flexible, full-featured DNS system. Whatever your application is, BIND 9 probably has the required features. As the first, oldest, and most commonly deployed solution, there are more network engineers who are already familiar with BIND 9 than with any other system.
BIND 9 is transparent open source, licensed under the MPL 2.0 license. Users are free to add functionality to BIND 9 and contribute back to the community through our open Gitlab.
If you want source code, download current version from the ISC website or our FTP site. Or, install our updated ISC packages for Ubuntu, CentOS/Fedora, and the standard Debian package. If you prefer Docker, get our official Docker image.
Help is available via our community mailing list, or you may purchase a support subscription for expert, confidential, 24Г—7 support from the ISC team.
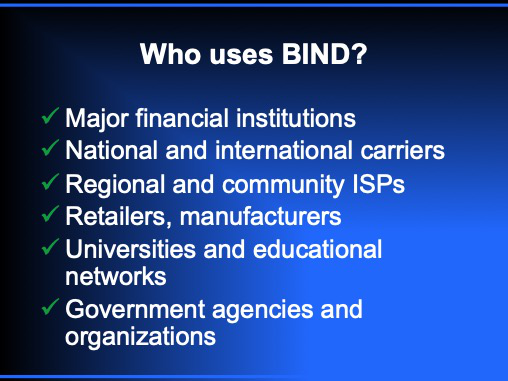
BIND Uses on the Internet
Almost every Internet connection starts with a DNS lookup
Before your mail server sends an email, before your web browser displays a web page, there is a DNS lookup to resolve a DNS name to an IP address. Watch this DNS Fundamentals presentation from Eddy Winstead of ISC.
BIND 9 on the Internet
BIND is used successfully for every application from publishing the (DNSSEC-signed) DNS root zone and many top-level domains, to hosting providers who publish very large zone files with many small zones, to enterprises with both internal (private) and external zones, to service providers with large resolver farms.
Getting Started
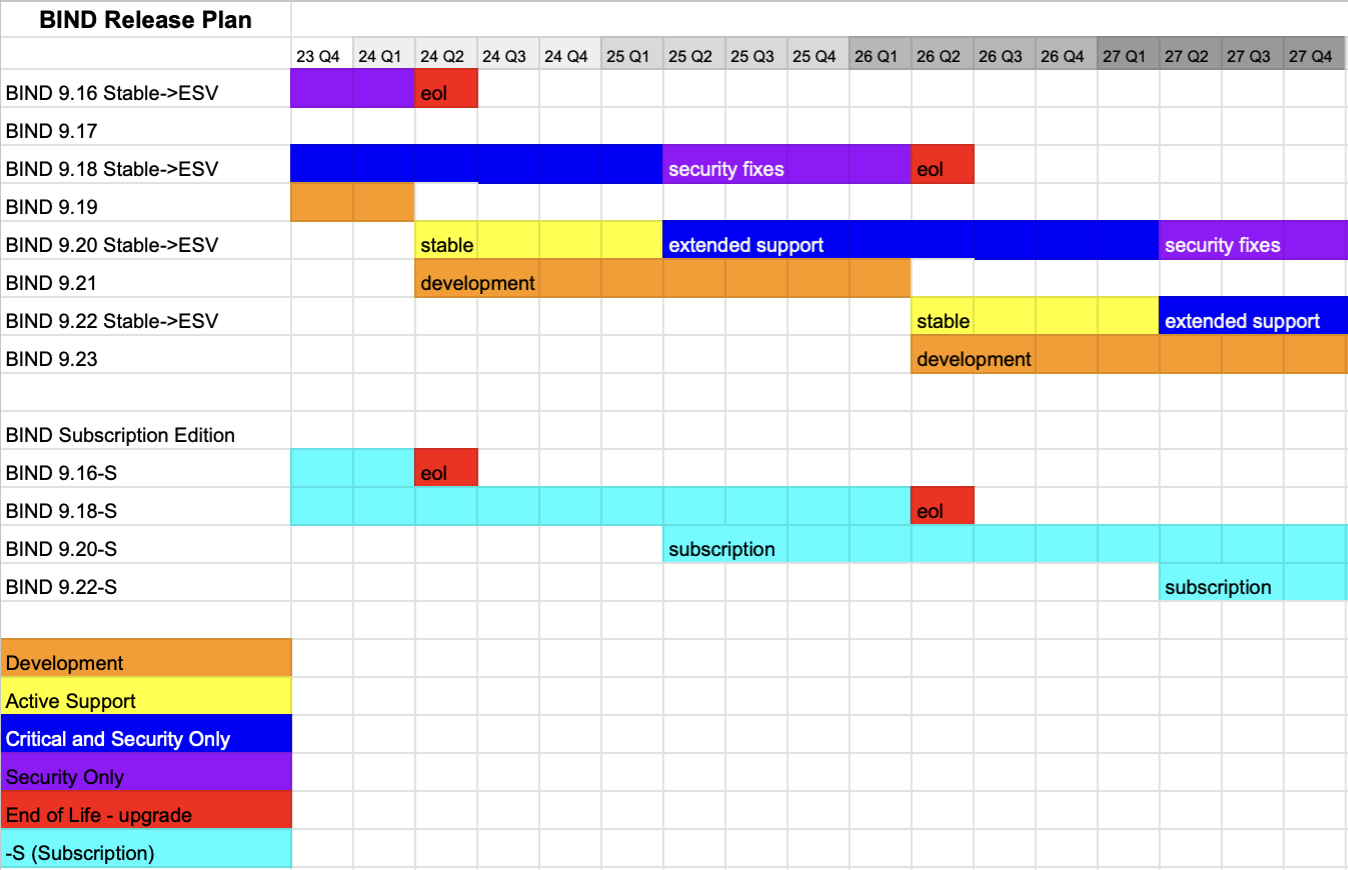
Choosing a version
We support three major branches of BIND 9 at a time: Stable, Extended-Support, and Development. See this advice: Which version of BIND do I want to download and install? as well as our list of supported platforms.
If you would prefer a GUI management interface, you might consider a Commercial Product based on BIND.
Installation
Instructions are available for Installing and Upgrading BIND 9. ISC provides executables for Windows and packages for Ubuntu and CentOS and Fedora and Debian — BIND9 ESV, Debian — BIND 9 Stable, Debian — BIND 9 Development version. We also have official Docker images. Most operating systems also offer BIND 9 packages for their users. These may be built with a different set of defaults than the standard BIND 9 distribution, and some of them add a version number of their own that does not map exactly to the BIND 9 version.
Configuration
The BIND Administrator Reference Manual (ARM) included in the BIND distribution is the primary reference for BIND configuration. See the Best Practices documents in our Knowledgebase for configuration recommendations.
Resolver users may find Getting started with Recursive Resolvers to be useful. There are a number of excellent books on BIND; Ron Hutchinson’s DNS for Rocket Scientists is generously posted on the Internet at Zytrax.com and can be a very helpful online reference tool.
Maintenance
Most users will benefit from joining the bind-users mailing list. We advise all users to subscribe to bind-announce@lists.isc.org to get announcements about new versions and security vulnerabilities. For other news, see our BIND blogs.
Our partners at Men and Mice run a very good series of hands-on training classes. If your DNS is critical to your business, we recommend you subscribe for technical support from ISC.
An authoritative DNS server answers requests from resolvers, using information about the domain names it is authoritative for. You can provide DNS services on the Internet by installing this software on a server and giving it information about your domain names. The BIND 9 documentation includes a description of the Primary/Secondary/Stealth Secondary roles for authoritative servers.
Response Rate Limiting (RRL) is an enhancement to named to reduce the problem of “amplification attacks” by rate-limiting DNS responses. This feature is on by default because it has proven to be so effective; it’s now even more effective with DNS Cookies, which focus rate-limiting on unknown clients. DNS cookies, per RFC 7873, are exchanged between client and server to provide IP address identity, helping to prevent attacks using forged IP addresses. Servers enforcing cookies are less susceptible to being used as an effective attack vector for DNS DDOS attacks.
Minimal ANY Responses
Queries for ANY records are a possible abuse mechanism because they typically extract a response much larger than the query. The minimal-any option reduces the size of answers to UDP queries for type ANY by implementing one of the strategies in “draft-ietf-dnsop-refuse-any”: returning a single arbitrarily-selected RRset that matches the query name rather than returning all of the matching RRsets.
Dynamically-Loadable Zones (DLZ) enable BIND 9 to retrieve zone data directly from an external database. Not recommended for high-query rate authoritative environments.
Minimum Re-load Time
Update your BIND 9 server zone files with the remote name daemon control (rndc) utility, without restarting BIND 9. For those times when you do have to restart, the ‘map’ zone file format can dramatically speed up reloading a large zone file into BIND 9, such as on restart.
HSM Support
BIND 9 supports the use of Hardware Security Modules through either a native PKCS#11 interface, or the OpenSSL PKCS#11 provider. HSMs are used to store key material outside of BIND 9 for security reasons.
DNSSEC with In-line Signing
BIND 9 fully supports DNSSEC and has a mature, full-featured, easy-to-use implementation. Once you have initially signed your zones, BIND 9 can automatically re-sign dynamically updated records with inline signing.
Catalog Zones
Catalog zones facilitate the provisioning of zone information across a nameserver constellation. Catalog zones are particularly useful when there is a large number of secondary servers. This feature will automatically propagate new zones added to the primary to the secondary servers, or remove zones deleted from the primary, eliminating the need for separate scripts to do this.
DNSTAP
Dnstap is a fast, flexible method for capturing and logging DNS traffic, developed by Robert Edmonds at Farsight Security, Inc. Dnstap is supported by several open-source DNS servers, including BIND. Using dnstap enables capturing both query and response logs, with a reduced impact on the overall throughput of the BIND server than native BIND logging. Messages may be logged to a file or to a UNIX socket. Support for log-file rotation will depend on which option you choose. A utility ‘dnstap-read’ has been added to allow dnstap data to be presented in a human-readable format.
Scaleable Primary-Secondary Hierarchy
A DNS authoritative system is composed of a primary with one or more secondary servers. Zone files are established and updated on a primary server. Secondaries maintain copies of the zone files and answer queries. This configuration allows scaling the answer capacity by adding more secondaries, while zone information is maintained in only one place. The primary signals that updated information is available with a NOTIFY message to the secondaries, and the secondaries then initiate a zone transfer from the primary. BIND 9 fully supports both the AXFR (complete transfer) and IXFR (incremental transfer) methods, using the standard TSIG security mechanism between servers. There are a number of configuration options for controlling the zone updating process.
A resolver is a program that resolves questions about names by sending those questions to appropriate servers and responding to the servers’ replies. In the most common application, a web browser uses a local stub resolver library on the same computer to look up names in the DNS. That stub resolver is part of the operating system. The stub resolver usually will forward queries to a caching resolver, a server or group of servers on the network dedicated to DNS services. Those resolvers will send queries to one or multiple authoritative servers in order to find the IP address for that DNS name.
NX Domain re-direct
When a customer searches for a non-existent domain (NXDOMAIN response), you can redirect the user to another web page. This is done using the BIND 9 DLZ feature.
Maximum Cache Hit Rate
Prefetch popular records before they expire from the cache. This will improve the performance delivered to end users for resolving names that have short expiration times.
Flexible Cache Controls
From time to time you may get incorrect or outdated records in the resolver cache. BIND 9 gives you the ability to remove them selectively or as a group.
Views — Split DNS
BIND 9 is unique in providing the ability to configure different views in a single BIND server. This allows you to give internal (on-network) and external (from the Internet) users different views of your DNS data, keeping some DNS information private.
Resolver Rate-limiting
BIND 9 offers two configuration parameters, fetches-per-zone and fetches-per-server. These features enable rate-limiting queries to authoritative systems that appear to be under attack. These features have been successful in mitigating the impact of a DDoS attack on resolvers in the path of the attack.
DNSSEC Validation
Protect your clients from imposter sites by validating DNSSEC. In BIND 9, this is enabled with a single command. BIND 9 also has a Negative Trust Anchor feature, which temporarily disables DNSSEC validation when there is a problem with the authoritative server’s DNSSEC support. BIND 9 offers support for RFC 5011 maintenance of root key trust anchors.
Response Policy Zones — RPZ
A Response Policy Zone or RPZ is a specially constructed zone that specifies a policy rule set. The primary application is for blocking access to domains that are believed to be published for abusive or illegal purposes. There are companies that specialize in identifying abusive sites on the Internet, which market these lists in the form of RPZ feeds. For more information on RPZ, including a list of DNS reputation feed providers, see https://dnsrpz.info.
DNS Privacy
BIND supports QNAME minimization by default. This feature minimizes leakage of excessive detail about the query to systems that need those details. BIND does not yet support encryption natively (e.g. DNS over TLS), but this can be accomplished by deploying BIND with stunnel.
Download BIND
ISC builds and maintains packages for every major operating system or download sources and build it yourself.
ISC packages may be found at: CentOS Epl & Fedora, Ubuntu Launchpad, and Debian. We also have an official Docker image. Download sources here and follow these instructions to verify a download file.
Установка и настройка DNS сервера BIND под Windows для разблокировки ЖЖ и Гугла
Установка BIND
- Скачайте bind для windows по ссылке — ftp://ftp.isc.org/isc/bind9/9.8.1/BIND9.8.1.zip
- Извлеките содержимое архива в заранее созданную пустую папку и запустите BINDInstall.exe
- Установщик спросит в какую папку установить программу. В своем случае я выбрал «C:\bind». Далее придумайте логин и пароль для сервиса.
Настройка
Сохраните их в указанных папках С:\bind\etc\named.conf C:\bind\zones\db.livejournal.com.txt C:\bind\zones\db.googleusercontent.com.txt
- Запустите командную строку (Пуск — Выполнить — cmd) и выполните по очереди следующие команды
cd С:\bind\bin
rndc-confgen -a
rndc-confgen > ..\etc\rndc.conf
В файле С:\bind\etc\named.conf поменяйте значение поля secret на аналогичное из файла C:\bind\etc\rndc.key
Запуск
- Пуск — Выполнить — services.msc
- Найдите службу ISC Bind и запустите ее
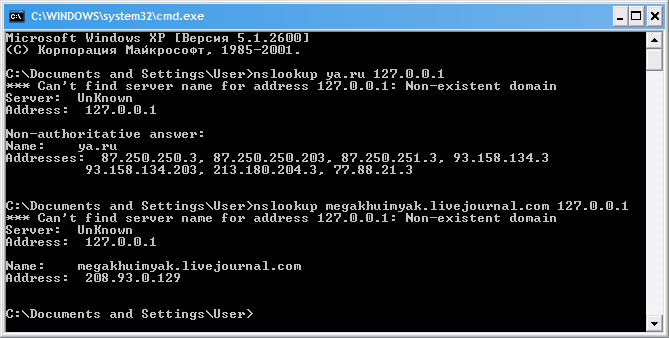
Проверка
- Пропишите в свойствах сетевой карты dns сервер 127.0.0.1
- Наберите в командной строке nslookup ya.ru 127.0.0.1
- Для проверки ЖЖ наберите nslookup megakhuimyak.livejournal.com 127.0.0.1
Если ответ как на картинке значит все ОК
PS
Для того что бы перезапускать bind после правки в конфигурации остановите службу ISC Bind? выполните в командной строке c:\bind\bin\rndc reload и запустите службу снова
Bind windows 64 bit
This document is designed to give Windows administrators a helping hand getting Bind going. The most recent update was written for Windows 7, other versions of Windows will probably have differences.
Last tested against BIND 9.9.2-P1
Cynthia Haselton for the updates around the BIND 9 installer and Active Directory integration.
It’s worth noting that Bind works admirably on many operating systems (I’ve run it on Linux, Solaris and Irix as well as Windows) and these may be preferable in a security focused environment.
Download and install the Bind 9 Software
- Download the latest version of bind from http://www.isc.org/downloads
- Create a folder on your desktop called bind and extract the downloaded zip to it.
- Open the newly created bind folder and right click on BINDInstall.exe and select «Run as administrator»
- In the Bind 9 Installer window enter:
- Target Directory: c:\named
- Service Account Name: named
- Service Account Password: Enter a secure password to use for the service to use
- Confirm Service Account Password: Enter the password again
- Ensure that Automatic Startup is selected
- Ensure that Keep Config files after uninstall is selected.
- Click Install.
- When the installer reports «BIND Installation completed successfully», click OK.
- Click Exit to close the installer.
Configure Bind
- Create a c:\named\zones folder
- Download named.conf and db.yourdomain.com.txtand save them to:
- c:\named\etc\named.conf
- c:\named\zones\db.yourdomain.com.txt
- Open a command prompt and run:
- Close the command prompt
- Open c:\named\etc\rndc.conf in notepad
- Cut to the clipboard the section belowthe line that says: # Use with the following in named.conf, adjusting the allow list as needed:
- Save & close rndc.conf
- Open c:\named\etc\named.conf in notepad
- Paste the contents of the clipboard into the bottom of this file
- Remove the hashes (#) from the beginning of the pasted lines.
- Remove the line that says «End of named.conf»
- Save & close named.conf
Configure your zone
- Open c:\named\etc\named.conf in notepad.
- In the zone definition for yourdomain.com, modify the zone and file lines to reflect the domain you are configuring.
- Save and close named.conf
- Rename c:\named\zones\db.yourdomain.com.txt to reflect your previous change in named.conf
- Open this zone file in notepad.
- Substitute all references to yourdomain.com for the domain you are configuring.
- Substitute namesever-hostname for the hostname of your nameserver.
- Edit the last line so that the A record reflects the IP address of your server.
- Edit the serial line to reflect today’s date. The format for this line is YYYYMMDDRR where: YYYY = The year (e.g. 2005) MM = The month (e.g. 02) DD = The day (e.g. 22) RR = Today’s revision of this file (e.g. 01)
- Save and close the zone file.
Start the Bind service
- Start -> right click on «Computer» and select «Manage» -> Services and Applications -> Services
- Locate the «ISC Bind» service, right click on it and select start.
- If it fails to start, errors can be found in the Event Viewer.
Create a Bind Reload batch file
To make reloading your nameserver easier, I recommend placing a batch file on your desktop to reload the nameserver. Reloading the nameserver enables Bind to re-read all the configuration and zone files (and thus allow implement any changes) without the need to restart the service.
- Create a text file called «reload bind.bat» on the desktop, with the following content
If you wish your Bind server to serve recursion
Should you require your Bind server to allow recursive queries, that is that it will need to be able to look up zones other than the ones you are hosting on this server (e.g. if this is to provide DNS service to a local network), you will need to enable recursion.
You will first need to generate a root hints file so your server knows where the root servers are. Ensure your Windows DNS configuration is pointing to a working DNS server (such as that of your ISP), open a command prompt and run:
Now add the following lines to your c:\named\etc\named.conf configuration file:
Also, in the global «options» section, change «recursion no» to «recursion yes» and, on the follwing line, add the following line to specify the range of IP addresses which you wish to allow recursion for:
Reload Bind for these changes to take effect.
Active Directory Integration
Should you wish for BIND to be the authoritative source of information for your Active Directory domain (if you don’t know what this is, don’t worry about this section) then you will need to delegate some of the special Active Directory subdomains to your Active Directory server.