- 15 Linux ping command examples for network diagnostics
- What is the use of the ping command?
- How does ping command work?
- Can I ping with a proxy?
- Ping IPv6 protocol
- Ping a specific port
- Ping with time
- Ping all the hosts on a given subnet
- How to end a ping?
- End after a specific count
- Linux ping command
- Description
- Syntax
- Options
- Notes
- ICMP packet details
- Duplicate and damaged packets
- Trying different data patterns
- TTL details
- Additional notes
- Examples
- Related pages
- Related commands
15 Linux ping command examples for network diagnostics
Thanks to Linux, we have access to many tools that facilitate networking administration & diagnostics. In this sense, the Linux ping command is one of the most useful tools for sysadmins and network administrators.
Its basic function is to determine if one host of the network is reachable or not. However, in this post, we will address other more advanced capabilities of the Linux Ping command.
Table of Contents
What is the use of the ping command?
The ping command is one of the most basic tools for working with networks. Its purpose is to diagnose network connection errors.
In this way, it is possible to know if a network node has lost connectivity. On the other hand, it is also useful to perform other diagnostic tasks such as the following:
- Measure the time taken by two network nodes to communicate.
- We will also be able to identify the IP address of a specific host. We can use this feature on both the Internet and in a private network.
- The ping command can be used in a bash script to perform automatic checks with network nodes.
- It allows knowing if there is a connection with specific equipment.
As you can see, it is a necessary command for the administration of networks and servers.
How does ping command work?
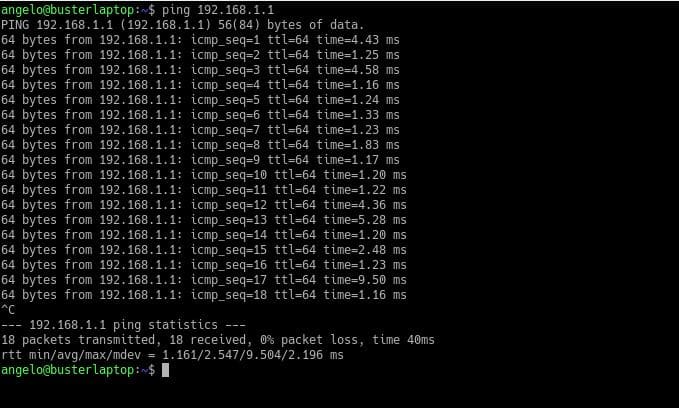
In Linux, the functioning of the ping command is quite simple to explain. The command sends a series of small packets to a specific node.
You can test this node using either the IP address or the hostname. Then, after you send the packet, the command verifies and measures the time it takes to receive a response from the destination node.
As you may expect, the response time may be affected due to conditions such as the geographical location between the connection points or any piece of the hardware used between the two nodes.
For example, in wired private networks, the command will get better times than with a network with multiple routers or bridges.
However, the information that the command will generate will judge whether the network is in good or bad condition.
The syntax of the command is as follows:
Some of the most useful and used options of the ping command are the following:
- -c: With this option, you can specify how many packets to send.
- -s: This option allows you to change the default size of the packets.
- -v: verbose mode.
- -w: Specifies a time in seconds that the execution of the command will end. No matter how many packets the command has sent or received.
- -i: With this option, you can specify the network interface to use.
The destination node can be specified by an IP address or a hostname.
Can I ping with a proxy?
A proxy is a server or application that acts as an intermediary for the connection between two points on a network. It is the man in the middle who makes the request directly to another node.
The problem is that the Ping command requires a direct network connection between the nodes.
Therefore, the Ping command generally cannot function properly if there is a proxy behind it.
A possible solution is that many websites offer the Ping command service. On the other hand, for some tasks of the ping command, it is possible to use the curl command. Also, you can use a VPN so that it will hide your IP.
However, in some Linux distributions, this command is not installed by default. First, verify it and then install it if it is not installed.
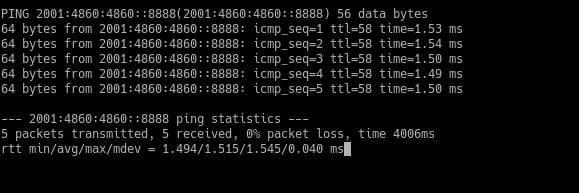
Ping IPv6 protocol
Normally, when using the Ping command, we use IP addresses with the IPv4 protocol. However, with the advent of the IPv6 protocol, it is increasingly common to notice addresses in this format.
The Linux kernel supports the IPv6 protocol since version 2.2, so all Linux distributions currently support it.
The basic syntax is as follows:
On old versions, there was ping6 command. On recent versions of Linux, ping6 doesn’t exist anymore, and its functionality has been merged into ping, and it works the same way as you saw.
The basic syntax is as follows:
With the option -c, we can specify the number of packets to send and with -i for the network interface you will use. For example:
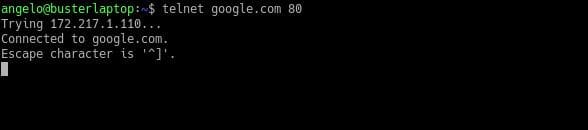
Ping a specific port
Sometimes we want to know if a specific port on a node is active. However, the ping command does not provide this functionality, but it is possible to do it with the telnet command that is installed by default on Linux.
To do this, just use the following syntax:
In this way, it is possible to ping a specific port of a network node in a primitive way.
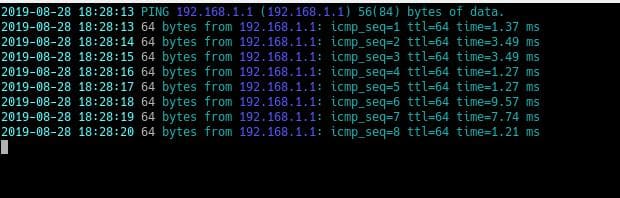
Ping with time
Although the ping command displays useful information, it may be a little simple. However, it is possible to modify the operation of the command a little, to make it show the date the packet is sent.
This can make the information pleasing to the eye and might be useful for scripts and logs.
This syntax is sufficient to do it. However, you need to install the ccze package.
As you can see, it shows the time for every packet sent.
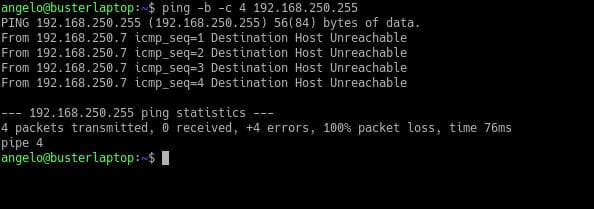
Ping all the hosts on a given subnet
You can send a ping signal to all hosts on a network or subnet. For this, it is enough to add the option -b and ping the broadcast IP address of any network which ends with 255.
So if the destination is unreachable, maybe they block ICMP packets sent by the ping command, or maybe there is a network problem or a problem on the routing table.
How to end a ping?
By default, the ping command on Linux continuously sends test packets to hosts. However, once the information is available, it becomes necessary to terminate the execution of the ping command.
To do so, simply press the following keys:
This way, the command will immediately stop working.
End after a specific count
You can limit the count of packets to 10 or whatever. When it finishes sending the ten packets, it will stop.
Источник
Linux ping command
On Unix-like operating systems, the ping command sends ICMP ECHO_REQUEST packets to network hosts.
This page covers the Linux version of ping.
Description
ping is a simple way to send network data to, and receive network data from, another computer on a network. It is frequently used to test, at the most basic level, whether another system is reachable over a network, and if so, how much time it takes for that data to be exchanged.
The ping utility uses the ICMP protocol’s mandatory ECHO_REQUEST datagram to elicit an ICMP ECHO_RESPONSE from a host or gateway. ECHO_REQUEST datagrams («pings») have an IP and ICMP header, followed by a struct timeval and then an arbitrary number of «pad» bytes used to fill out the packet.
Syntax
Options
| -a | Audible ping. |
| -A | Adaptive ping. Interpacket interval adapts to round-trip time, so that effectively not more than one (or more, if preload is set) unanswered probes are present in the network. Minimal interval is 200msec for any user other than the super-user. On networks with low RTT (round trip time), this mode is essentially equivalent to flood mode (see -f, below). |
| -b | Allow pinging a broadcast address. |
| -B | Do not allow ping to change source address of probes. The address is bound to one selected when ping starts. |
| -m mark | Use mark to tag the packets going out. This is useful for variety of reasons in the kernel such as using policy routing to select specific outbound processing. |
| -c count | Stop after sending count ECHO_REQUEST packets. With the deadline option, ping waits for count ECHO_REPLY packets, until the timeout expires. |
| -d | Set the SO_DEBUG option on the socket being used. This socket option is not used by Linux kernel. |
| -f | Flood ping. For every ECHO_REQUEST sent, a period («.«) is printed, while for every ECHO_REPLY received, a backspace is printed. This provides a rapid display of how many packets are being dropped. If an interval is not given (see -i, below), it sets interval to zero and outputs packets as fast as they come back or one hundred times per second, whichever is more. Only the super-user may use this option with an interval of zero. |
| -i interval | Wait interval seconds between sending each packet. The default is to wait for one second between each packet normally, or not to wait at all in flood mode (see -f, above). Only super-user may set interval to values less 0.2 seconds. |
| -I interface-address | Set source address to specified interface address. Argument may be a numeric IP address or the name of the device. When pinging IPv6 link-local addresses, this option is required. |
| -l preload | If preload is specified, ping sends that many packets not waiting for reply. Only the super-user may select a preload of more than 3. |
| -L | Suppress loopback of multicast packets. This flag only applies if the ping destination is a multicast address. |
| -N nioption | Send ICMPv6 Node Information Queries (RFC 4620), instead of Echo Requests. nioption may be one of the following: |
| name | Queries for Node Names. | ||||||||
| ipv6 | Queries for IPv6 Addresses. There are several IPv6 specific flags:
| ||||||||
| ipv4 | Queries for IPv4 addresses. There is one IPv4 specific flag:
| ||||||||
| subject-ipv6=ipv6addr | IPv6 subject address. | ||||||||
| subject-ipv4=ipv4addr | IPv4 subject address. | ||||||||
| subject-name=nodename | Subject name. If it contains more than one dot, fully-qualified domain name is assumed. | ||||||||
| subject-fqdn=nodename | Subject name. Fully-qualified domain name is always assumed. |
Notes
When using ping for fault isolation, it should first run on the localhost, to verify that the local network interface is up and running. Then, hosts and gateways further and further away should be «pinged». Round-trip times and packet loss statistics are computed. If duplicate packets are received, they are not included in the packet loss calculation, although the round trip time of these packets is used in calculating the minimum/average/maximum round-trip time numbers. When the specified number of packets are sent (and received) or if the program is terminated with a SIGINT signal, a summary is displayed. Shorter current statistics can be obtained without termination of process with signal SIGQUIT.
If ping does not receive any reply packets at all it will exit with code 1. If a packet count and deadline are both specified, and fewer than count packets are received by the time the deadline has arrived, it also exits with code 1. On other error it exits with code 2. Otherwise, it exits with code 0. This makes it possible to use the exit code to see if a host is alive or not.
ping is intended for use in network testing, measurement and management. Because of the load it can impose on the network, it is unwise to use ping during normal operations or from automated scripts.
ICMP packet details
An IP header without options is 20 bytes. An ICMP ECHO_REQUEST packet contains an additional 8 bytes worth of ICMP header followed by an arbitrary amount of data. When a packetsize is given, this indicated the size of this extra piece of data (the default is 56). Thus the amount of data received inside of an IP packet of type ICMP ECHO_REPLY is always 8 bytes more than the requested data space (the ICMP header).
If the data space is at least of size of struct timeval, ping uses the beginning bytes of this space to include a timestamp which it uses in the computation of round trip times. If the data space is shorter, no round trip times are given.
Duplicate and damaged packets
ping will report duplicate and damaged packets. Duplicate packets should never occur, and seem to be caused by inappropriate link-level retransmissions. Duplicates may occur in many situations and are rarely (if ever) a good sign, although the presence of low levels of duplicates may not always be cause for alarm.
Damaged packets are serious cause for alarm and often indicate broken hardware somewhere in the ping packet’s path (in the network or in the hosts).
Trying different data patterns
The (inter)network layer should never treat packets differently depending on the data contained in the data portion. Unfortunately, data-dependent problems were known to sneak into networks and remain undetected for long periods of time. In many cases, the particular pattern having problems is something that doesn’t have sufficient «transitions,» such as all ones or all zeros, or a pattern right at the edge, such as almost all zeros. It isn’t necessarily enough to specify a data pattern of all zeros (for example) on the command line because the pattern that is of interest is at the data link level, and the relationship between what you type and what the controllers transmit can be complicated.
This means that if you have a data-dependent problem you will probably have to do a lot of testing to find it. If you are lucky, you may manage to find a file that either can’t be sent across your network or that takes much longer to transfer than other similar length files. You can then examine this file for repeated patterns that you can test using the -p option.
TTL details
The TTL (time-to-live) value of an IP packet represents the maximum number of IP routers that the packet can go through before being thrown away. In practice, you can expect each router in the Internet to decrement the TTL field by exactly one.
The TCP/IP specification states that the TTL field for TCP packets should be set to 60, but many systems use smaller values (4.3 BSD uses 30, 4.2 used 15).
The maximum possible value of this field is 255, and most Unix systems set the TTL field of ICMP ECHO_REQUEST packets to 255. This is why you find you can ping some hosts, but not reach them with telnet or ftp.
In normal operation, ping prints the ttl value from the packet it receives. When a remote system receives a ping packet, it can do one of three things with the TTL field in its response:
- Not change it; this is what Berkeley Unix systems did before the 4.3 BSD Tahoe release. In this case, the TTL value in the received packet will be 255 minus the number of routers in the round-trip path.
- Set it to 255; this is what current Berkeley Unix systems do. In this case, the TTL value in the received packet will be 255 minus the number of routers in the path from the remote system to the pinging host.
- Set it to some other value. Some machines use the same value for ICMP packets that they use for TCP packets, for example either 30 or 60. Others may use completely wild values.
Additional notes
- Many hosts and gateways ignore the RECORD_ROUTE option.
- The maximum IP header length is too small for options like RECORD_ROUTE to be completely useful, although there’s not much that can be done about this.
- Flood pinging is not recommended in general, and flood pinging the broadcast address should only be done under very controlled conditions.
Examples
Ping the host google.com to see if it’s alive.
Ping the host google.com once. Output resembles the following:
Related pages
Related commands
host — Convert a hostname to an IP address and vice versa.
ifconfig — View or modify the configuration of network interfaces.
netstat — Print information about network connections, routing tables, interface statistics, masquerade connections, and multicast memberships.
rpcinfo — Report information about remote procedure calls.
traceroute — Trace the route that packets take to a remote host.
Источник