- Cisco AnyConnect Secure Mobility Client Supported Operating Systems and Requirements
- Available Languages
- Download Options
- Objective
- Software Version
- AnyConnect Supported Operating Systems and Requirements
- AnyConnect Support for Microsoft Windows
- Windows Operating Systems
- Windows Requirements
- AnyConnect Support for Linux
- Linux Operating Systems
- Linux Requirements
- AnyConnect (Versions 4.8 and above) Support for macOS
- Supported Operating Systems
- AnyConnect (Versions 4.7 and below) Support for Mac OS X
- Supported Operating Systems
- Mac OS X Requirements
- Cisco any client linux
- Configure AnyConnect Secure Mobility Client for Linux using Client Certificate Authentication on an ASA
- Available Languages
- Download Options
- Contents
- Introduction
- Prerequisites
- Requirements
- Components Used
- Backgound Information
- Configure
- Network Diagram
- Configurations
- Verify
- Troubleshoot
Cisco AnyConnect Secure Mobility Client Supported Operating Systems and Requirements
Available Languages
Download Options
Objective
The objective of this document is to provide details about the supported operating systems (Windows, Linux, Mac) of the Cisco AnyConnect Secure Mobility Client and their requirements.
The Cisco AnyConnect Secure Mobility Client, also known as the Cisco AnyConnect VPN Client, is a software application for connecting to a Virtual Private Network (VPN) that works on various operating systems and hardware configurations. This software application makes it possible for remote resources of another network become accessible as if the user is directly connected to the network, but in a secure way. Cisco AnyConnect Secure Mobility Client provides an innovative way to protect mobile users on computer-based or smart-phone platforms, providing a more seamless, always-protected experience for end users, and comprehensive policy enforcement for an IT administrator.
For additional information on AnyConnect licensing on the RV340 series routers, see this article .
Software Version
- AnyConnect Secure Mobility Client 4.9.x | (Download latest)
AnyConnect Supported Operating Systems and Requirements
AnyConnect Support for Microsoft Windows
Windows Operating Systems
- Microsoft-supported versions of Windows 10 for ARM64-based PCs
- Windows 7 Special Pack (SP) 1
- Windows 8
- Windows 8.1
- Windows 10 x86 (32-bit) and x64 (64-bit)
Windows Requirements
- Pentium class processor or greater
- 100 MB hard disk space
- Microsoft Installer version 3.1
- Upgrading to Windows 8.1 from any previous Windows release requires you to uninstall AnyConnect, and reinstall it after your Windows upgrade is complete.
- Upgrading from Windows XP to any later Windows release requires a clean install since the Cisco AnyConnect Virtual Adapter is not preserved during the upgrade. Manually uninstall AnyConnect, upgrade Windows, and then reinstall AnyConnect manually or via WebLaunch.
- To start AnyConnect with WebLaunch, you must use the 32-bit version of Firefox 3.0+ and enable ActiveX or install Sun JRE 1.4+.
- ASDM version 7.02 or higher is required when using Windows 8 or 8.1
AnyConnect Support for Linux
Linux Operating Systems
- Linux Red Hat 6
- Linux Red Hat 7
- Linix Red Hat 8.2
- Ubuntu 16.04 Long Term Support (LTS)
- Ubuntu 18.04 (LTS)
- Ubuntu 20.04 (LTS) (64-bit only)
Linux Requirements
- x86 instruction set
- 64-bit processor
- 32 MB Random Access Memory (RAM)
- 20 MB hard disk space
- Superuser privileges are required for installation
- libstdc++ users must have libstdc++.so.6 (GLIBCXX_3.4) or higher, but below version 4
- Java 5 (1.5) or later. The only version that works for web installation is Sun Java. You must install Sun Java and configure your browser to use that instead of the default package.
- zlib — to support SSL deflate compression
- xterm — only required if you’re doing initial deployment of AnyConnect via Weblaunch from ASA clientless portal
- gtk 2.0.0
- gdk 2.0.0
- libpango 1.0
- iptables 1.2.7a or later
- tun module supplied with kernel 2.4.21 or 2.6
AnyConnect (Versions 4.8 and above) Support for macOS
Supported Operating Systems
- macOS 10.13
- macOS 10.14
- macOS 10.15 ( Details from Apple | AnyConnect 4.8 Release Notes)
- macOS 11.x (AnyConnect macOS 11 Big Sur Advisory)
AnyConnect (Versions 4.7 and below) Support for Mac OS X
Supported Operating Systems
- Mac OS X 10.10
- Mac OS X 10.11
- macOS 10.12
- macOS 10.13
- macOS 10.14
Mac OS X Requirements
- AnyConnect requires 50 MB of hard disk space.
- To operate correctly with Mac OS X, AnyConnect requires a minimum display resolution of 1024 by 640 pixels.
Check out the AnyConnect Release Notes, for the most updated information.
Источник
Cisco any client linux
В данной статье рассмотрим как установить VPN соединение и подключиться через удаленный рабочий стол на удаленную машину.
Первым делом, открываем терминал и выполняем обновление списка пакетов:
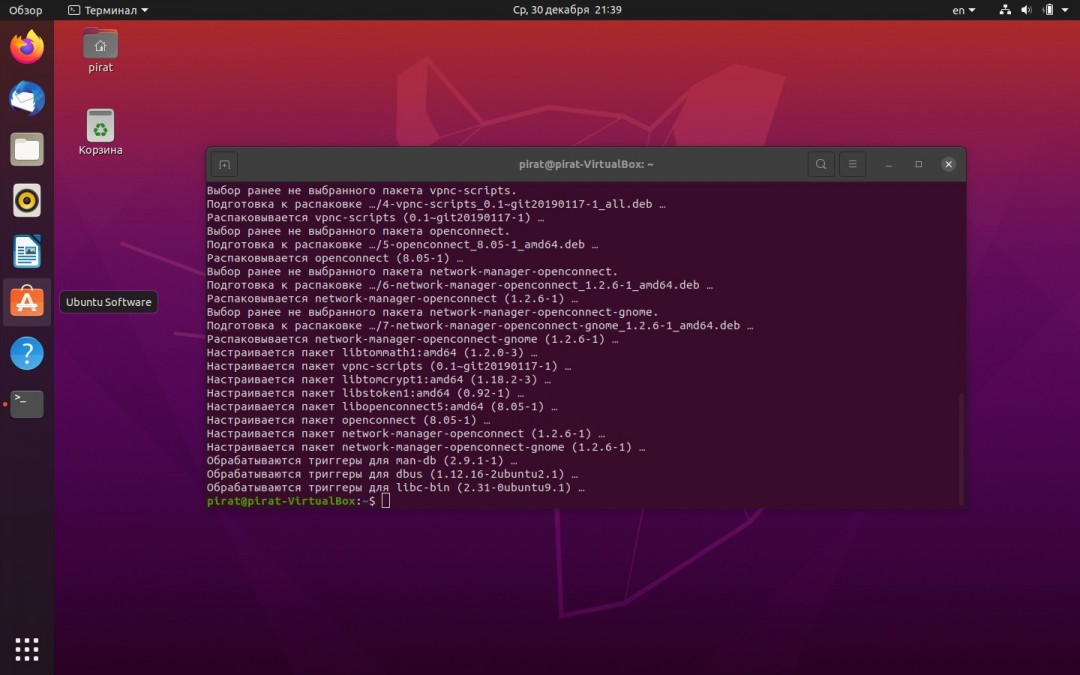
Следующим шагом установим пакет «openconnect», который включает в себя в том числе и клиент cisco anyconnect для linux.
Для установки пакета набираем следующую команду в терминале:
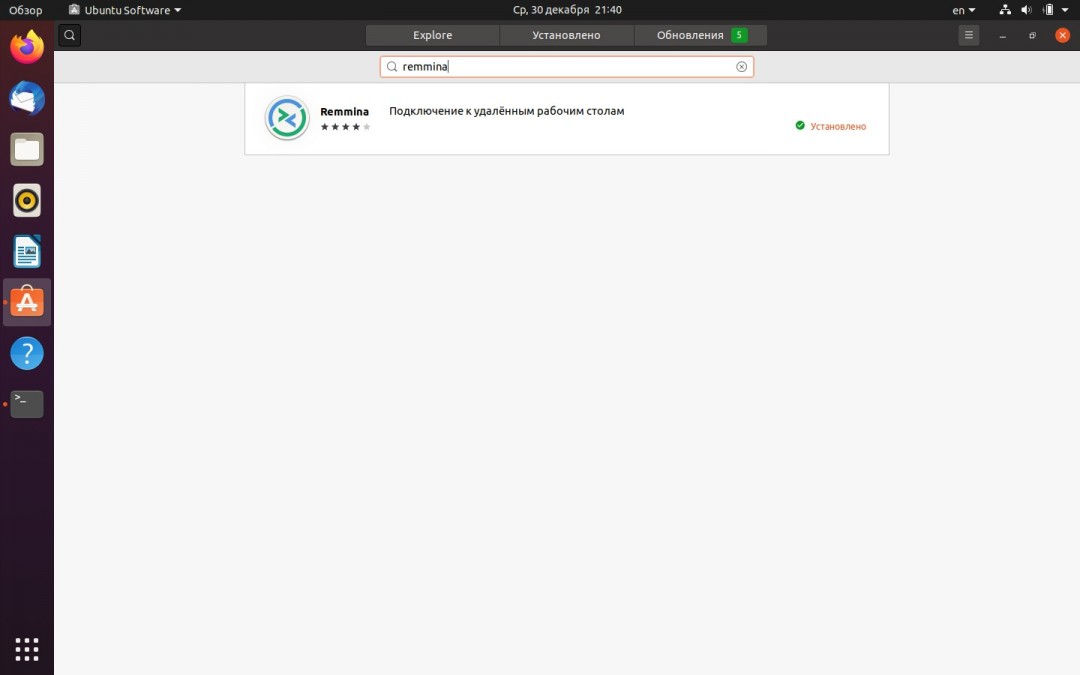
Установив openconnect, следующим шагом необходимо установить «Remmina» — ПО для подключения к удаленным рабочим столам. Самый простой способ сделать это — установить через стандартное средство «Ubuntu Software» (находим в меню приложений):
Находим «Remmina» через поиск и устанавливаем:
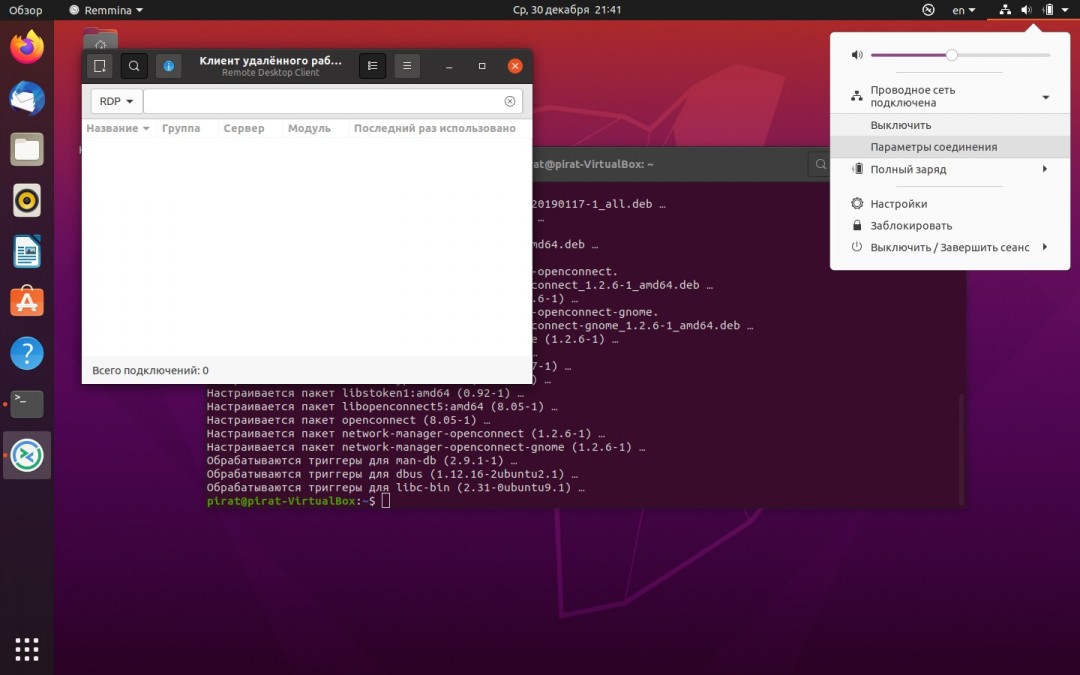
Кликаем по иконке сетевых подключений в меню справа, далее во всплывающем окне щелкаем «Проводная сеть» — «Параметры соединения»:
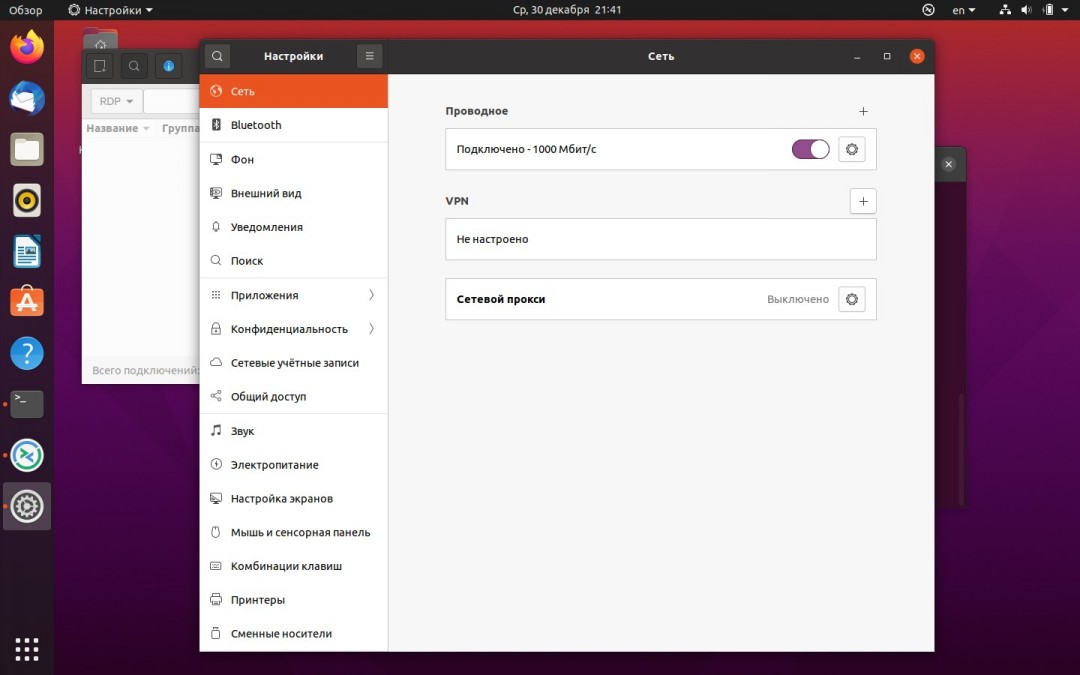
В окне «Настройки сети» в разделе «VPN» щелкаем по кнопке «Добавить» (в виде плюса):
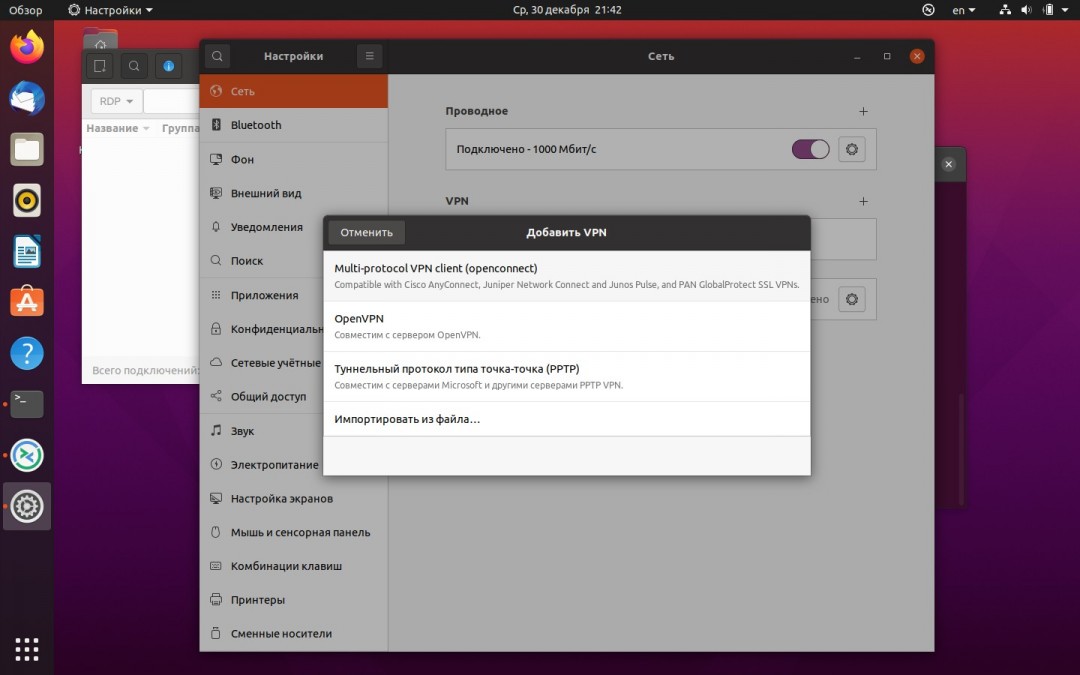
Появится окно «Добавить VPN», в котором выбираем «Multi-protocol VPN Client Openconnect»:
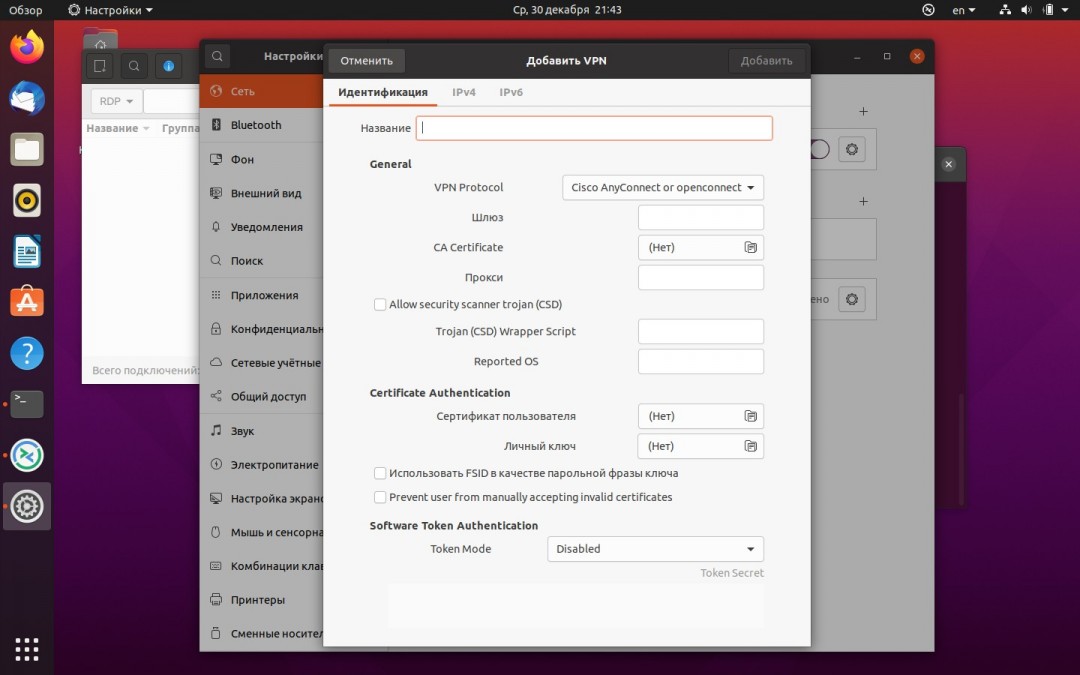
Далее в окне с настройками указываем название VPN соединения, шлюз и другие необходимые настройки, после заполнения настроек нажимаем кнопку «Добавить»:
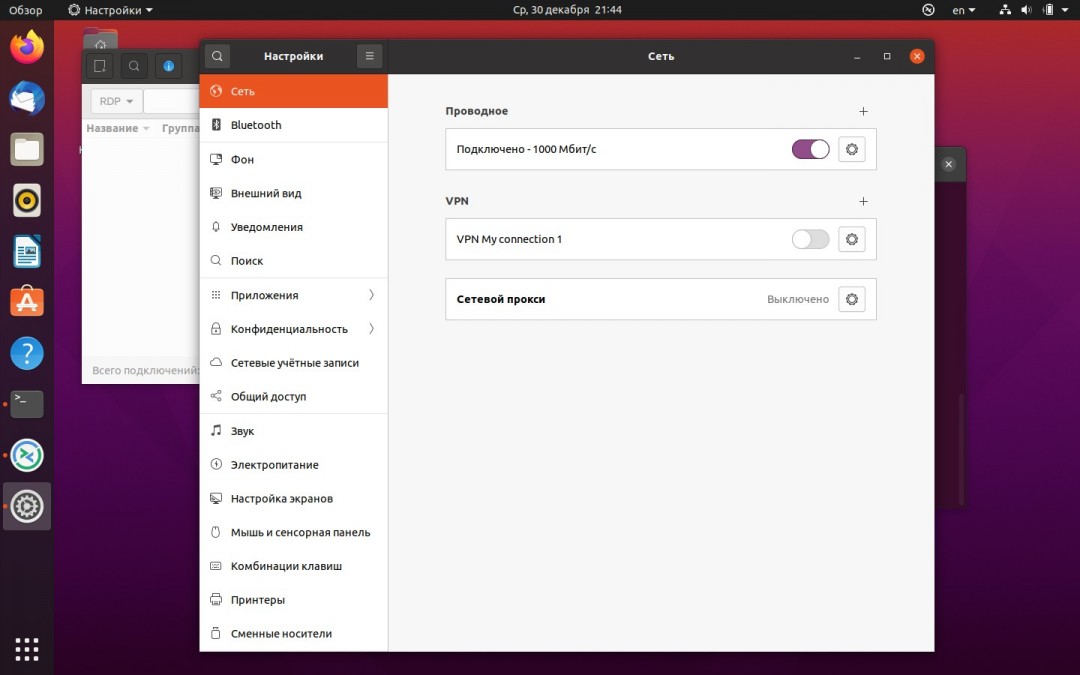
Как видим, у нас появилось новое VPN соединение, для его включения передвигаем ползунок вправо:
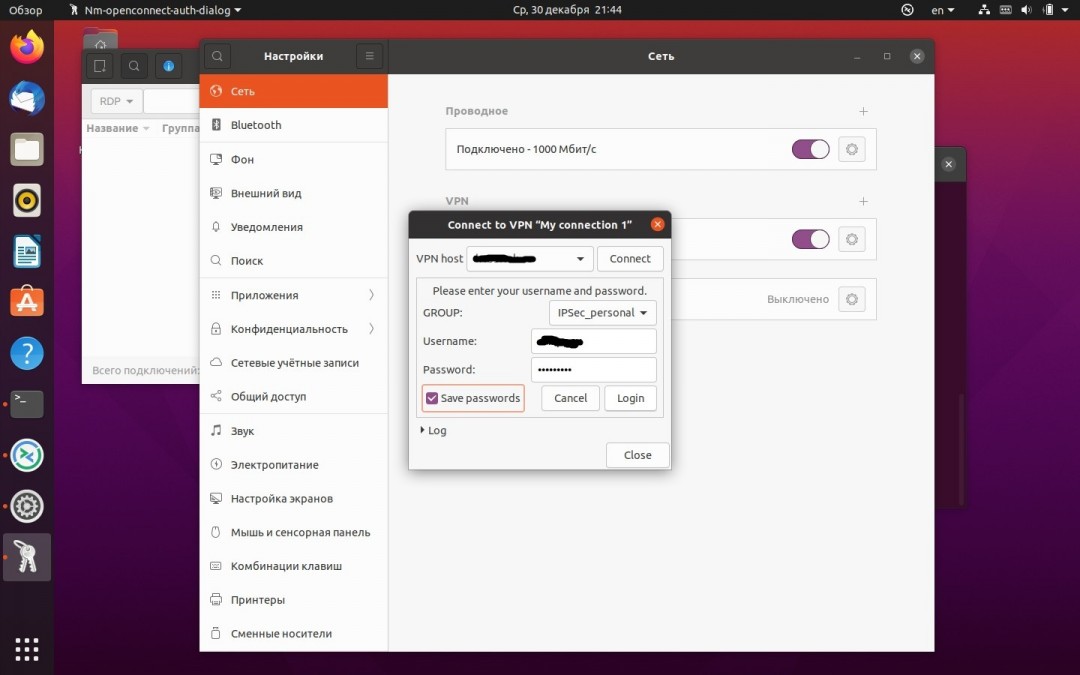
В окне авторизации вводим группу, логин и пароль, нажимаем кнопку «Login» для входа:
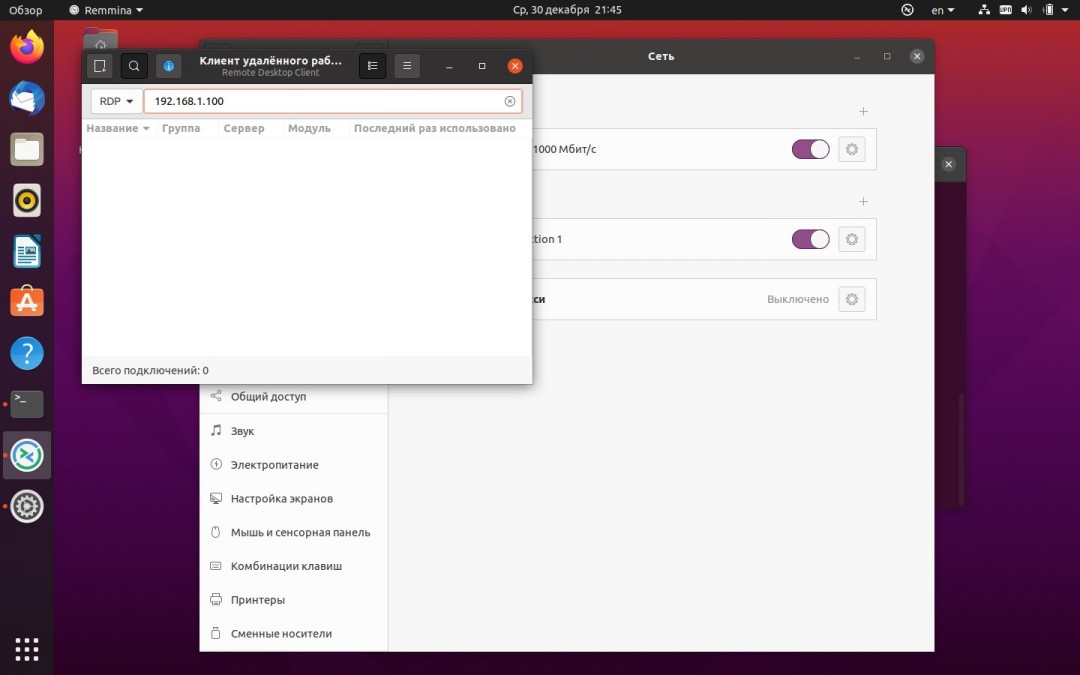
Когда мы подключены к VPN, необходимо выполнить подключение к удаленному рабочему столу. Для этого запускаем Remmina, выбираем протокол RDP, в адресной строке пишем ip-адрес удаленной машины, затем нажимаем «Enter»:
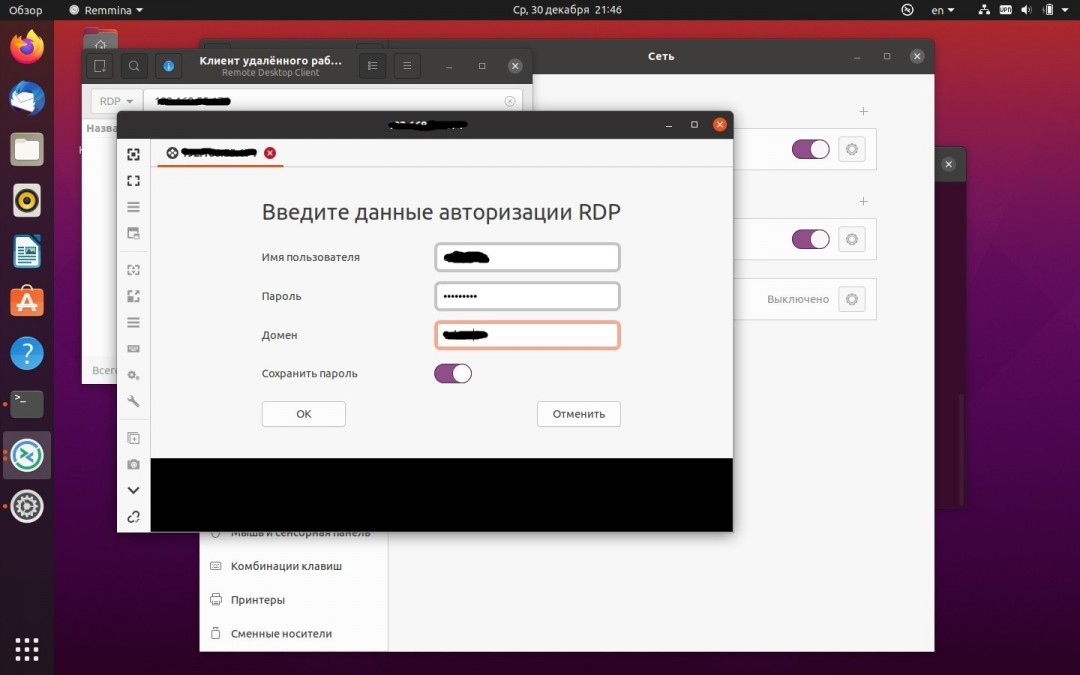
В окне авторизации RDP указываем данные вашей учетной записи с удаленной машины и нажимаем «ОК»:
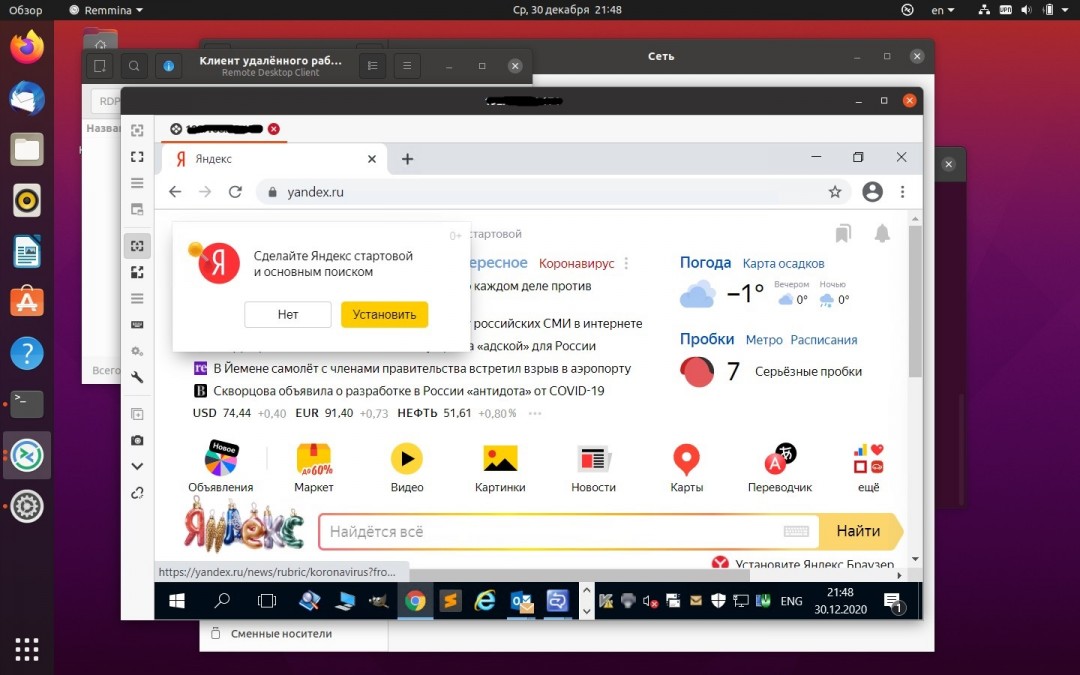
Если все ок, попадаем на рабочий стол удаленной машины:
Как вы уже убедились, нет ничего сложного в подключении к VPN на Ubuntu.
Источник
Configure AnyConnect Secure Mobility Client for Linux using Client Certificate Authentication on an ASA
Available Languages
Download Options
Contents
Introduction
This document describes a configuration example for Adaptive Security Appliance (ASA) Cisco AnyConnect Secure Mobility Client access that uses client certificate for authentication for a Linux Operative System (OS) for an AnyConnect user to connect successfully to an ASA Headend.
Contributed by Dinesh Moudgil, Cisco HTTS Engineer.
Prerequisites
Requirements
This document assumes that the ASA is fully operational and configured to allow the Cisco Adaptive Security Device Manager (ASDM) or Command Line Interface (CLI) to make configuration changes.
Cisco recommends that you have knowledge of these topics:
Basic knowledge of ASA’s CLI and ASDM
SSLVPN configuration on the Cisco ASA Head End
Fundamental knowledge of PKI
Familiarity with Linux OS
Components Used
The information in this document is based on these software and hardware versions:
Cisco Adaptive Security Appliance ASA5585-SSP-20
Cisco Adaptive Security Appliance Software Version 9.9(2)36
Adaptive Security Device Manager Version 7.9(1)
AnyConnect Version 4.6.03049
Ubuntu OS 16.04.1 LTS
Note: Download the AnyConnect VPN Client package (anyconnect-linux*.pkg) from the Cisco Software Download (registered customers only) site. Copy the AnyConnect VPN client to the ASA’s flash memory, which is then downloaded to the remote user computers in order to establish the SSL VPN connection with the ASA.
The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, make sure that you understand the potential impact of any command.
Backgound Information
For a successful client certificate authentication on Linux devices, AnyConnect secure mobility client supports the following certificate stores:
1. Linux OS (PEM) certificate store
2. Firefox (NSS) certificate store
This document is based on client certificate authentication using a Linux OS (PEM) certificate store.
1. To use Linux OS certificate store, PEM file-based certificates are placed in these directories.
| Entity | Path | Example |
| Certificate authority (CA) certificate | /opt/.cisco/certificates/ca | tactest: $ ls /opt/.cisco/certificates/ca |
| User certificate | /home/tactest/.cisco/certificates/client | tactest: $ ls /home/tactest/.cisco/certificates/client |
| User private key [Initially used to create CSR] : | /home/tactest/.cisco/certificates/client/private | tactest: $ ls /home/tactest/.cisco/certificates/client/private |
Note: By default, the path for installing client certificate and the private key is not present so it needs to be manually created using this command.
mkdir -p .cisco/certificates/client/private/
If you are using a Windows Certificate Authority,
1. Download the CA Certificate (Base64 encoded) with extension .cer
2. Download the User Identity Certificate (Base64 encoded) with extension .cer
3. Change the extension of certificates from .cer to .pem extension
2. To use Firefox (NSS) certificate store, user can import their certificate via Firefox.
The CA certificate for the ASA can be imported into NSS certificate store by AnyConnect client automatically if the user clicks “Always Connect” button on the certificate security warning dialog when browsing to ASA via HTTPS.
AnyConnect Linux uses Firefox certificate store (NSS) as default, if it fails then it would turn to use Linux OS certificate store.
Note: Currently, AnyConnect on a Linux OS doesn’t support GNOME Keyring so AnyConnect won’t able to use the certificate imported to the GNOME Keyring.
Please make sure there are no related certificates in Linux OS certificate store and Firefox (NSS) certificate store before importing a new user certificate.
Ensure that your files meet the following requirements:
- All certificate files must end with the extension .pem.
- All private key files must end with the extension .key.
- A client certificate and its corresponding private key must have the same filename. For example: client.pem and client.key.
For a clean start, please consider the following approach:
- Linux OS (PEM) certificate store:
A. Remove unnecessary PEM files under “/opt/.cisco/certificates”, but keep the “/opt/.cisco/certificates/ca/VeriSignClass3PublicPrimaryCertificationAuthority-G5.pem” certificate intact. This is the CA certificate AnyConnect relies on to perform the code signing verification.
B. Remove the user certificates that are not required from the path
Use firefox settings to inspect and delete related certificates imported by user or AnyConnect itself.
Configure
Network Diagram
Configurations
Linux Client Setup
Step 1. Download the Anyconnect package, extract the contents and install the Anyconnect application on the Linux client.
Step 2. Create a certificate signing request for the identity certificate on Linux client using OpenSSL.
Step 3. The CSR generated above can be used to request CA to issue a user identity certificate.
Step 4. Once the certificate is issued by CA, copy the certificate to the Linux client.
ASA CLI Configuration
This section provides the CLI configuration for the Cisco AnyConnect Secure Mobility Client for reference purposes.
Verify
Use this section in order to confirm that your configuration works properly.
Note: The Output Interpreter Tool (registered customers only) supports certain show commands. Use the Output Interpreter Tool in order to view an analysis of show command output.
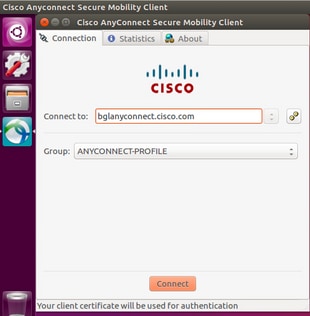
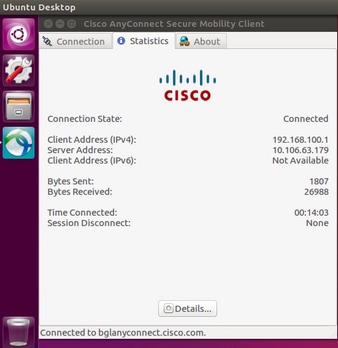
- On an Ubuntu OS 16.04.1 LTS, connect Anyconnect via GUI
If you wish to connect Anyconnect via command line on a Linux client, navigate to the following path:
Verify the Anyconnect client is able to establish connection:
Note: If Anyconnect GUI client is already opened and you try to connect Anyconnect via CLI, you get this error.
In this case, close the Anyconnect GUI client and then connect via Anyconnect CLI.
Once successfully connected, Anyconnect client details can be verified by navigating to Statistics tab in the Anyconnect GUI client
This command is used to confirm the CA and Identity certificates present on the Adaptive Security Appliance (ASA).
These show commands can be executed to confirm the status of AnyConnect client and its statistics.
In order to confirm if the Linux client has the certificate in the correct format (Base64 encoding with .pem extension), browse to the given path and use the following command:
If you get the following error it means that you are trying to view a DER-encoded certificate and it is not a PEM encoded certificate
Troubleshoot
This section provides the information you can use in order to troubleshoot your configuration.
Note: Refer to Important Information on Debug Commands before you use debug commands.
Caution: On the ASA, you can set various debug levels; by default, level 1 is used. If you change the debug level, the verbosity of the debugs might increase. Do this with caution, especially in production environments.
To troubleshoot an incoming AnyConnect client connection from Linux OS client, you can use the following:
- For AnyConnect process on an ASA
debug webvpn anyconnect 255
Here is a sample debug taken on an ASA from a working scenario:
- For client certificate authentication on an ASA
debug crypto ca 255
debug crypto ca messages 255
debug crypto ca transactions 255
Here is a sample debug taken for a successful client certificate authentication on an ASA:
- For the AnyConnect process on a Linux client
On a Linux device, Anyconnect logs can be found in the file named «syslog» at path:/var/log/
Here is a sample of working logs taken from a Linux client. The below command can be run to gather live logs for an Anyconnect client connection.
- DART(Diagnostic and Reporting Tool) on Linux Client
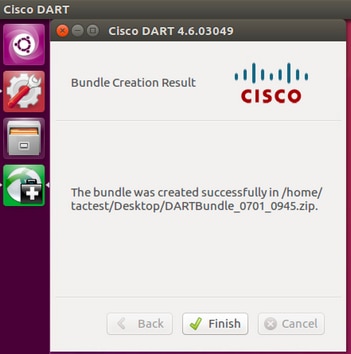
Similar to Windows and MAC, Linux client also has DART functionality. This can be used either using GUI and CLI.
Please note that DART needs to be run as an admin user in order to collect complete logs on a Linux client.
Step 1. DART can be executed from the command line by navigating to the following path:
Step 2. To execute DART from GUI, search for «anyconnect» on Linux GUI and click on Cisco DART and follow the instructions. The collected DART bundle is stored on the desktop.
Step 3. To copy dart bundle from the Linux client to your workstation, use the command
scp username@10.106.44.166:/home/ /Desktop/DARTBundle_0701_0945.zip /Users/dmoudgil/Desktop/Ubuntu/
Here is a document for reference to DART on different OS: https://community.cisco.com/t5/security-documents/how-to-collect-the-dart-bundle-for-anyconnect/ta-p/3156025
Источник