- Install Hashcat On Windows
- Hashcat Install
- Testing a MD5 hash
- Hashcat Help file — Quick Reference
- Brute Force Attacking:
- Hashcat GUI
- Starting Hashcat GUI
- hashcat advanced password recovery
- Navigation
- Download
- GPU Driver requirements:
- Features
- Screenshot
- Algorithms
- Supported OpenCL runtimes
- Supported OpenCL device types
- Download older version(s)
Install Hashcat On Windows
This is a guide to installing hashcat on a windows 10 build. Hashcat allows for the use of GPUs to crack hashes which is significantly faster then within a VM and/or using a CPU alone.
Legal Usage: The information provided by executeatwill and this website is to be used for educational purposes only. The website creator and/or editor is in no way responsible for any misuse of the information provided. All the information on this website is meant to help the reader develop penetration testing and vulnerability aptitude to prevent attacks discussed. In no way should you use the information to cause any kind of damage directly or indirectly. Information provided by this website is to be regarded from an “ethical hacker” standpoint. Only preform testing on systems you OWN and/or have expressed written permission. Use information at your own risk.
By continued reading, you acknowledge the aforementioned user risk/responsibilities.
Keep in mind by using your GPU the faster the clock speed the faster it will crack hashes. Understand with increased speed comes increased heat. Our goal should be to ensure we control the heat being generated from large password lists to which I recommend MSI Afterburner.
(recommended) — MSI Afterburner can be used to monitor temps/fans/overclock GPUs and is found at:
Hashcat Install
First head over to: https://hashcat.net/hashcat/
download the hashcat binaries — link
inside the directory create x2 text files:
within the hash.txt — add hashes you would like to crack. within the cracked.txt — you should have cracked hashes append here.
Testing a MD5 hash
create a quick MD5 hash at: http://www.miraclesalad.com/webtools/md5.php
Place the newly generated hash into the hash.txt file and save
Open command prompt as Administrator
change directory and navigate to hashcat directory.
Hashcat Help file — Quick Reference
Brute Force Attacking:
-m0 = MD5 hashes -a5 = Attack type: Brute forcing -o = output file
in my case I have x1 GTX 1070 for cracking.
After a few seconds MD5 is cracked
In this example it took 10s to crack this MD5 hash using brute force with x1 GTX 1070.
Hashcat GUI
For a bit easier user experience I recommend checking out Hashcat GUI.
Setup: Start by downloading the HashcatGUI_1.1beta0.zip from above website.
We are going to need to extract the zip and copy all the contents from the orginal hashcat into GUI directory.
files from hashcat folder were pasted into GUI folder.
inside same GUI folder create a new folder called wordlists
where are you going to find wordlists you ask? Lets checkout SecLists on github: https://github.com/danielmiessler/SecLists
hashkiller download section also has an frequently updated password list: https://hashkiller.co.uk/downloads.aspx
Starting Hashcat GUI
Locate and run HashcatGUI.exe
add wordlists under Wordlist tab
configure the input file to the hash.txt and the output file to the cracked.txt. untick “Disabled Pot File” untick “CPU only” change Format: Plain change Hashcat Path
configured in my case to crack MD5 hashes.
hashcat
advanced password recovery
Navigation
Download
| Name | Version | Date | Download | Signature |
|---|---|---|---|---|
| hashcat binaries | v6.1.1 | 2020.07.29 | Download | PGP |
| hashcat sources | v6.1.1 | 2020.07.29 | Download | PGP |
Signing key on PGP keyservers: RSA, 2048-bit. Key ID: 2048R/8A16544F. Fingerprint: A708 3322 9D04 0B41 99CC 0052 3C17 DA8B 8A16 544F
Check out our GitHub Repository for the latest development version
GPU Driver requirements:
- AMD GPUs on Linux require «RadeonOpenCompute (ROCm)» Software Platform (3.1 or later)
- AMD GPUs on Windows require «AMD Radeon Adrenalin 2020 Edition» (20.2.2 or later)
- Intel CPUs require «OpenCL Runtime for Intel Core and Intel Xeon Processors» (16.1.1 or later)
- NVIDIA GPUs require «NVIDIA Driver» (440.64 or later) and «CUDA Toolkit» (9.0 or later)
Features
- World’s fastest password cracker
- World’s first and only in-kernel rule engine
- Free
- Open-Source (MIT License)
- Multi-OS (Linux, Windows and macOS)
- Multi-Platform (CPU, GPU, APU, etc., everything that comes with an OpenCL runtime)
- Multi-Hash (Cracking multiple hashes at the same time)
- Multi-Devices (Utilizing multiple devices in same system)
- Multi-Device-Types (Utilizing mixed device types in same system)
- Supports password candidate brain functionality
- Supports distributed cracking networks (using overlay)
- Supports interactive pause / resume
- Supports sessions
- Supports restore
- Supports reading password candidates from file and stdin
- Supports hex-salt and hex-charset
- Supports automatic performance tuning
- Supports automatic keyspace ordering markov-chains
- Built-in benchmarking system
- Integrated thermal watchdog
- 300+ Hash-types implemented with performance in mind
- . and much more
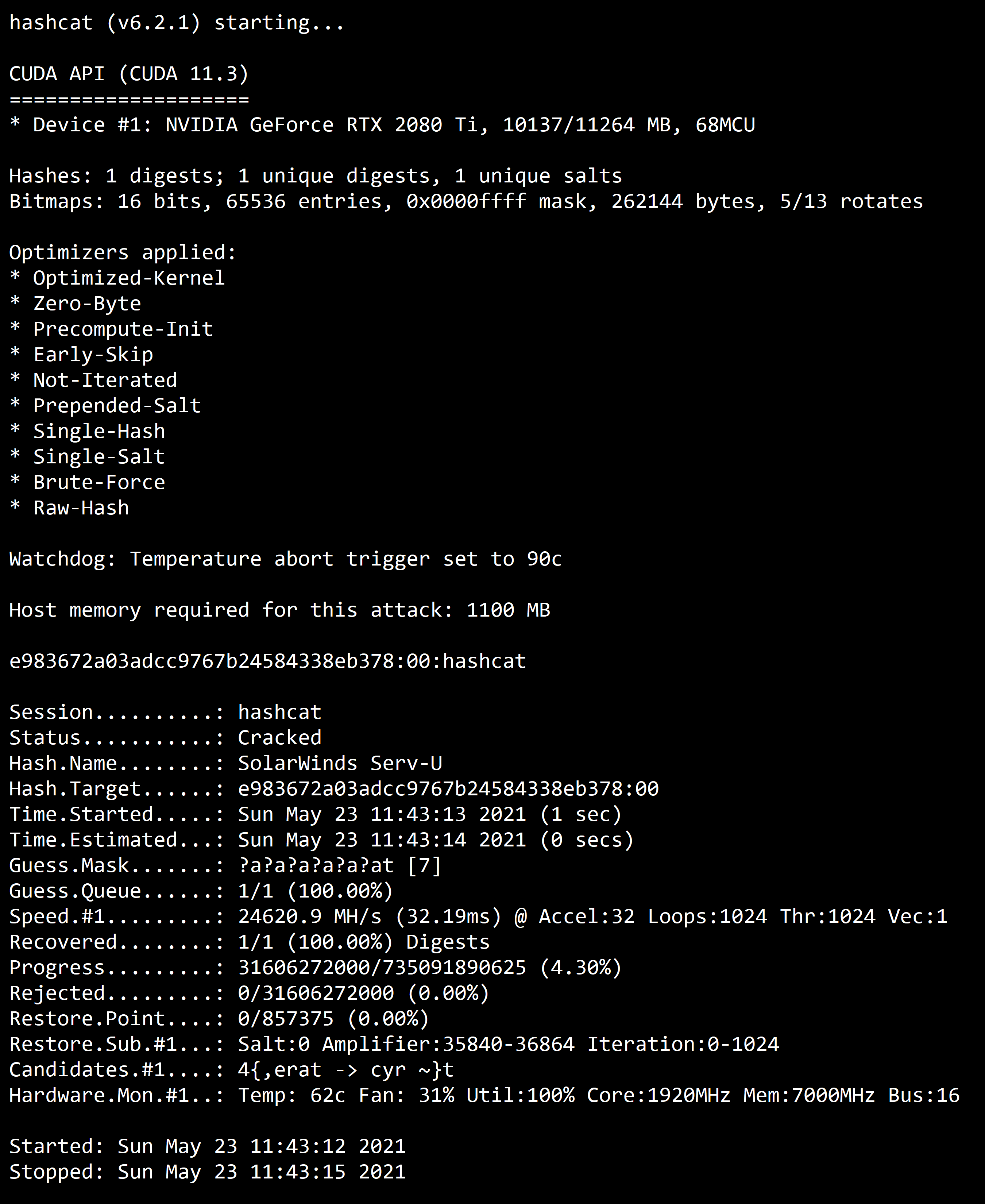
Screenshot
Algorithms
- MD4
- MD5
- SHA1
- SHA2-224
- SHA2-256
- SHA2-384
- SHA2-512
- SHA3-224
- SHA3-256
- SHA3-384
- SHA3-512
- RIPEMD-160
- BLAKE2b-512
- GOST R 34.11-2012 (Streebog) 256-bit, big-endian
- GOST R 34.11-2012 (Streebog) 512-bit, big-endian
- GOST R 34.11-94
- Half MD5
- Java Object hashCode()
- Keccak-224
- Keccak-256
- Keccak-384
- Keccak-512
- Whirlpool
- SipHash
- BitShares v0.x — sha512(sha512_bin(pass))
- md5($pass.$salt)
- md5($salt.$pass)
- md5($salt.$pass.$salt)
- md5($salt.md5($pass))
- md5($salt.md5($pass.$salt))
- md5($salt.md5($salt.$pass))
- md5($salt.sha1($salt.$pass))
- md5($salt.utf16le($pass))
- md5(md5($pass))
- md5(md5($pass).md5($salt))
- md5(sha1($pass))
- md5(sha1($pass).md5($pass).sha1($pass))
- md5(sha1($salt).md5($pass))
- md5(strtoupper(md5($pass)))
- md5(utf16le($pass).$salt)
- sha1($pass.$salt)
- sha1($salt.$pass)
- sha1($salt.$pass.$salt)
- sha1($salt.sha1($pass))
- sha1($salt.utf16le($pass))
- sha1($salt1.$pass.$salt2)
- sha1(CX)
- sha1(md5($pass))
- sha1(md5($pass).$salt)
- sha1(md5($pass.$salt))
- sha1(md5(md5($pass)))
- sha1(sha1($pass))
- sha1(utf16le($pass).$salt)
- sha256($pass.$salt)
- sha256($salt.$pass)
- sha256($salt.$pass.$salt)
- sha256($salt.utf16le($pass))
- sha256(md5($pass))
- sha256(sha256($pass).$salt)
- sha256(sha256_bin($pass))
- sha256(utf16le($pass).$salt)
- sha512($pass.$salt)
- sha512($salt.$pass)
- sha512($salt.utf16le($pass))
- sha512(utf16le($pass).$salt)
- Ruby on Rails Restful-Authentication
- HMAC-MD5 (key = $pass)
- HMAC-MD5 (key = $salt)
- HMAC-SHA1 (key = $pass)
- HMAC-SHA1 (key = $salt)
- HMAC-SHA256 (key = $pass)
- HMAC-SHA256 (key = $salt)
- HMAC-SHA512 (key = $pass)
- HMAC-SHA512 (key = $salt)
- HMAC-Streebog-256 (key = $pass), big-endian
- HMAC-Streebog-256 (key = $salt), big-endian
- HMAC-Streebog-512 (key = $pass), big-endian
- HMAC-Streebog-512 (key = $salt), big-endian
- CRC32
- 3DES (PT = $salt, key = $pass)
- DES (PT = $salt, key = $pass)
- ChaCha20
- Skip32 (PT = $salt, key = $pass)
- PBKDF2-HMAC-MD5
- PBKDF2-HMAC-SHA1
- PBKDF2-HMAC-SHA256
- PBKDF2-HMAC-SHA512
- scrypt
- phpass
- Ansible Vault
- Atlassian (PBKDF2-HMAC-SHA1)
- Python passlib pbkdf2-sha512
- Python passlib pbkdf2-sha256
- Python passlib pbkdf2-sha1
- TACACS+
- SIP digest authentication (MD5)
- IKE-PSK MD5
- IKE-PSK SHA1
- WPA-PBKDF2-PMKID+EAPOL
- WPA-PMK-PMKID+EAPOL
- IPMI2 RAKP HMAC-SHA1
- CRAM-MD5
- iSCSI CHAP authentication, MD5(CHAP)
- JWT (JSON Web Token)
- Kerberos 5, etype 23, AS-REQ Pre-Auth
- Kerberos 5, etype 23, TGS-REP
- Kerberos 5, etype 23, AS-REP
- Kerberos 5, etype 17, TGS-REP
- Kerberos 5, etype 18, TGS-REP
- Kerberos 5, etype 17, Pre-Auth
- Kerberos 5, etype 18, Pre-Auth
- NetNTLMv1 / NetNTLMv1+ESS
- NetNTLMv2
- Skype
- Telegram Desktop App Passcode (PBKDF2-HMAC-SHA1)
- Telegram Mobile App Passcode (SHA256)
- PostgreSQL CRAM (MD5)
- MySQL CRAM (SHA1)
- XMPP SCRAM
- RACF
- AIX
- AIX
- AIX
- AIX
- LM
- QNX /etc/shadow (MD5)
- QNX /etc/shadow (SHA256)
- QNX /etc/shadow (SHA512)
- DPAPI masterkey file v1
- DPAPI masterkey file v2
- GRUB 2
- MS-AzureSync PBKDF2-HMAC-SHA256
- BSDi Crypt, Extended DES
- NTLM
- macOS v10.4, macOS v10.5, MacOS v10.6
- macOS v10.7
- macOS v10.8+ (PBKDF2-SHA512)
- Radmin2
- Samsung Android Password/PIN
- bcrypt $2*$, Blowfish (Unix)
- md5crypt, MD5 (Unix), Cisco-IOS $1$ (MD5)
- descrypt, DES (Unix), Traditional DES
- sha256crypt $5$, SHA256 (Unix)
- sha512crypt $6$, SHA512 (Unix)
- Windows Phone 8+ PIN/password
- Cisco-ASA MD5
- Cisco-IOS $8$ (PBKDF2-SHA256)
- Cisco-IOS $9$ (scrypt)
- Cisco-IOS type 4 (SHA256)
- Cisco-PIX MD5
- Citrix NetScaler (SHA1)
- Citrix NetScaler (SHA512)
- Domain Cached Credentials (DCC), MS Cache
- Domain Cached Credentials 2 (DCC2), MS Cache 2
- FortiGate (FortiOS)
- ArubaOS
- Juniper IVE
- Juniper NetScreen/SSG (ScreenOS)
- Juniper/NetBSD sha1crypt
- MSSQL (2000)
- MSSQL (2005)
- MSSQL (2012, 2014)
- PostgreSQL
- Oracle H: Type (Oracle 7+)
- Oracle S: Type (Oracle 11+)
- Oracle T: Type (Oracle 12+)
- MySQL323
- MySQL4.1/MySQL5
- MySQL $A$ (sha256crypt)
- Sybase ASE
- hMailServer
- DNSSEC (NSEC3)
- CRAM-MD5 Dovecot
- SSHA-256(Base64), LDAP
- SSHA-512(Base64), LDAP
- RedHat 389-DS LDAP (PBKDF2-HMAC-SHA256)
- FileZilla Server >= 0.9.55
- ColdFusion 10+
- Apache $apr1$ MD5, md5apr1, MD5 (APR)
- Episerver 6.x = .NET 4
- nsldap, SHA-1(Base64), Netscape LDAP SHA
- nsldaps, SSHA-1(Base64), Netscape LDAP SSHA
- SAP CODVN B (BCODE)
- SAP CODVN B (BCODE) from RFC_READ_TABLE
- SAP CODVN F/G (PASSCODE)
- SAP CODVN F/G (PASSCODE) from RFC_READ_TABLE
- SAP CODVN H (PWDSALTEDHASH) iSSHA-1
- PeopleSoft
- PeopleSoft PS_TOKEN
- SolarWinds Orion
- Lotus Notes/Domino 5
- Lotus Notes/Domino 6
- Lotus Notes/Domino 8
- Oracle Transportation Management (SHA256)
- Huawei sha1(md5($pass).$salt)
- AuthMe sha256
- AES Crypt (SHA256)
- BitLocker
- eCryptfs
- LUKS
- VeraCrypt
- FileVault 2
- DiskCryptor
- Android FDE (Samsung DEK)
- Android FDE = 10.0
- WinZip
- Android Backup
- AxCrypt
- AxCrypt in-memory SHA1
- WBB3 (Woltlab Burning Board)
- vBulletin = v3.8.5
- PHPS
- SMF (Simple Machines Forum) > v1.1
- MediaWiki B type
- Redmine
- Joomla *
- Combination
- Brute-force
- Hybrid dict + mask
- Hybrid mask + dict
Supported OpenCL runtimes
- AMD
- Apple
- Intel
- NVidia
- POCL
- ROCm
Supported OpenCL device types
A detailed description of all commandline parameters is available by using --help. Next to that, the 7zip-package contains extensive documentation. Look for examples.txt. If you encounter a Bug, report it in the Forums where Fixes and Beta versions are announced as well.
If you still think you need help by a real human come to #hashcat on freenode IRC.
Download older version(s)
This is a list of older hashcat versions, it’s not always bad to grab the latest version.