- How to download linux kali linux
- System Requirements
- Installation Prerequisites
- Preparing for the Installation
- Kali Linux Installation Procedure
- Language
- Network
- User Accounts
- Clock
- Encrypted LVM
- Proxy Information
- Metapackages
- Boot Information
- Reboot
- Post Installation
- How to download linux kali linux
- Where to Get Official Kali Linux Images
- Verifying Your Downloaded Kali Image
- How Do I Verify My Downloaded Image?
How to download linux kali linux
Installing Kali Linux (single boot) on your computer is an easy process. This guide will cover the basic install (which can be done on bare metal or guest VM), with the option of encrypting the partition. At times, you may have sensitive data you would prefer to encrypt using Full Disk Encryption (FDE). During the setup process you can initiate an LVM encrypted install on either Hard Disk or USB drives.
First, you’ll need compatible computer hardware. Kali Linux is supported on amd64 (x86_64/64-Bit) and i386 (x86/32-Bit) platforms. Where possible, we would recommend using the amd64 images. The hardware requirements are minimal as listed in the section below, although better hardware will naturally provide better performance. You should be able to use Kali Linux on newer hardware with UEFI and older systems with BIOS.
Our i386 images, by default use a PAE kernel, so you can run them on systems with over 4 GB of RAM.
In our example, we will be installing Kali Linux in a fresh guest VM, without any existing operating systems pre-installed. We will explain other possible scenarios throughout the guide.
System Requirements
The installation requirements for Kali Linux will vary depending on what you would like to install and your setup. For system requirements:
- On the low end, you can set up Kali Linux as a basic Secure Shell (SSH) server with no desktop, using as little as 128 MB of RAM (512 MB recommended) and 2 GB of disk space.
- On the higher end, if you opt to install the default Xfce4 desktop and the kali-linux-default metapackage, you should really aim for at least 2 GB of RAM and 20 GB of disk space.
- When using resource-intensive applications, such as Burp Suite, they recommend at least 8 GB of RAM(and even more if it large web application!) or using simultaneous programs at the same time.
Installation Prerequisites
This guide will make also the following assumptions when installing Kali Linux:
- Using the amd64 installer image.
- CD/DVD drive / USB boot support.
- Single disk to install to.
- Connected to a network (with DHCP & DNS enabled) which has outbound Internet access.
We will be wiping any existing data on the hard disk, so please backup any important information on the device to an external media.
Preparing for the Installation
Download Kali Linux (We recommend the image marked Installer).
Burn The Kali Linux ISO to DVD or image Kali Linux Live to USB drive. (If you cannot, check out the Kali Linux Network Install).
Backup any important information on the device to an external media.
Ensure that your computer is set to boot from CD/DVD/USB in your BIOS/UEFI.
Kali Linux Installation Procedure
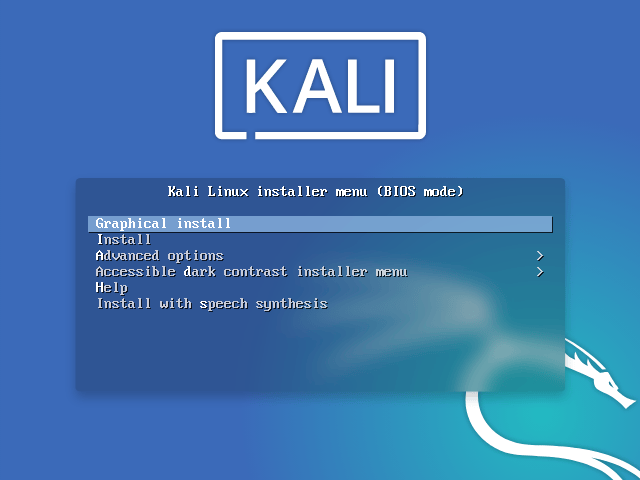
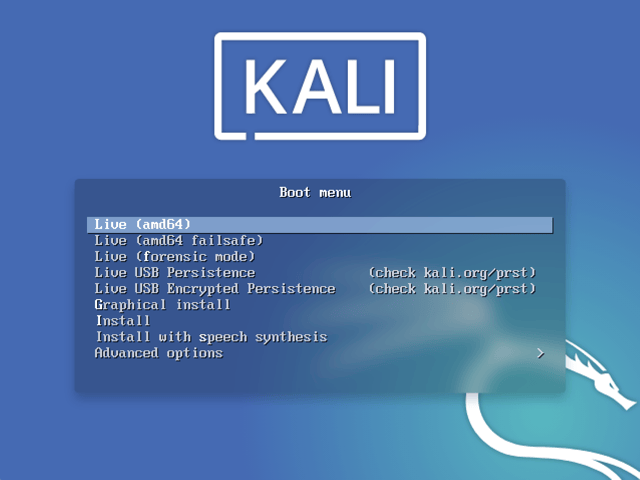
- To start your installation, boot with your chosen installation medium. You should be greeted with the Kali Linux Boot screen. Choose either Graphical install or Install (Text-Mode). In this example, we chose the Graphical install.
If you’re using the live image instead, you will see another mode, Live, which is also the default boot option.
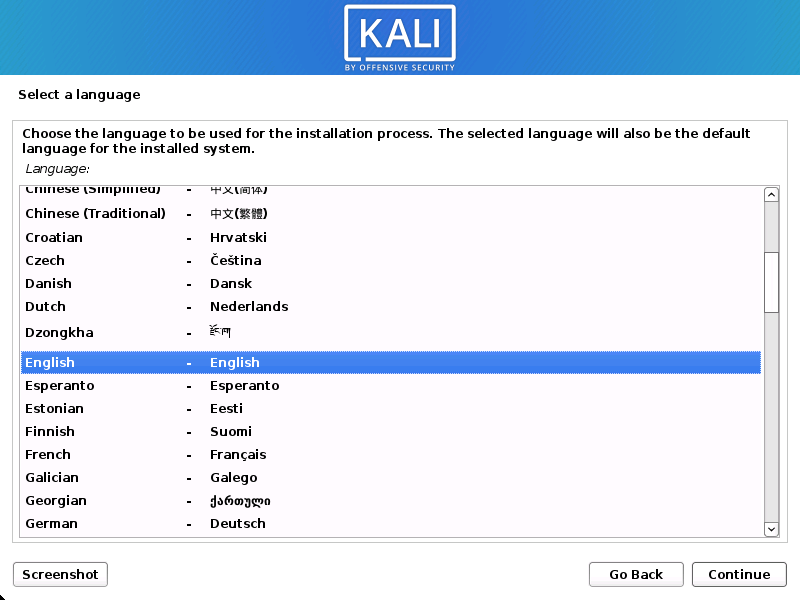
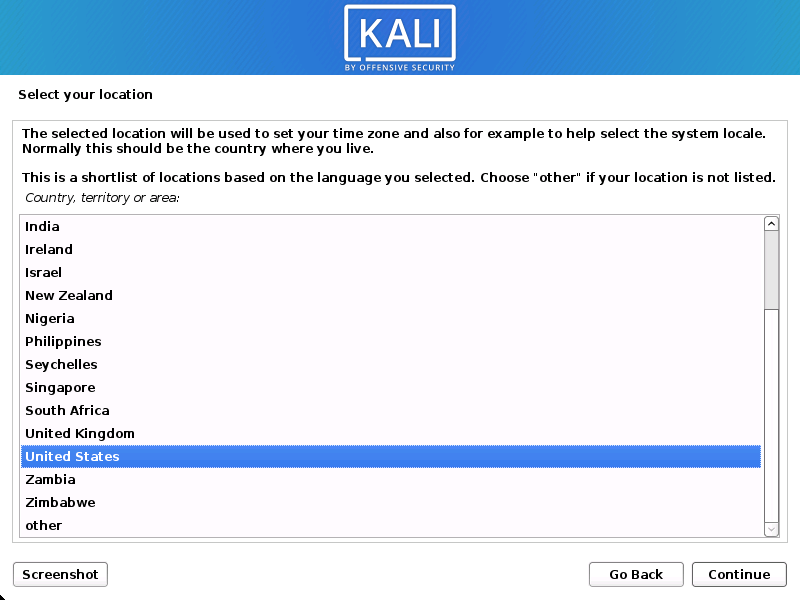
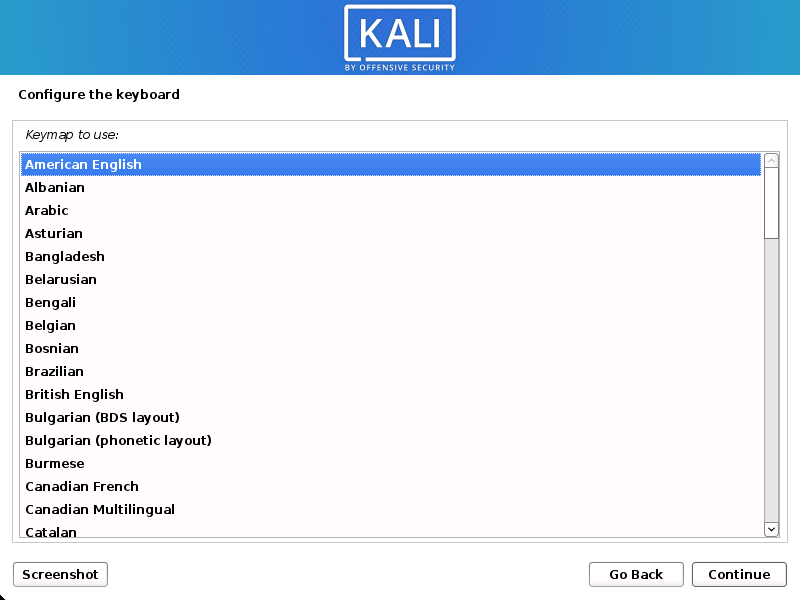
Language
- Select your preferred language. This will be used for both the setup process and once you are using Kali Linux.
- Specify your geographic location.
- Select your keyboard layout.
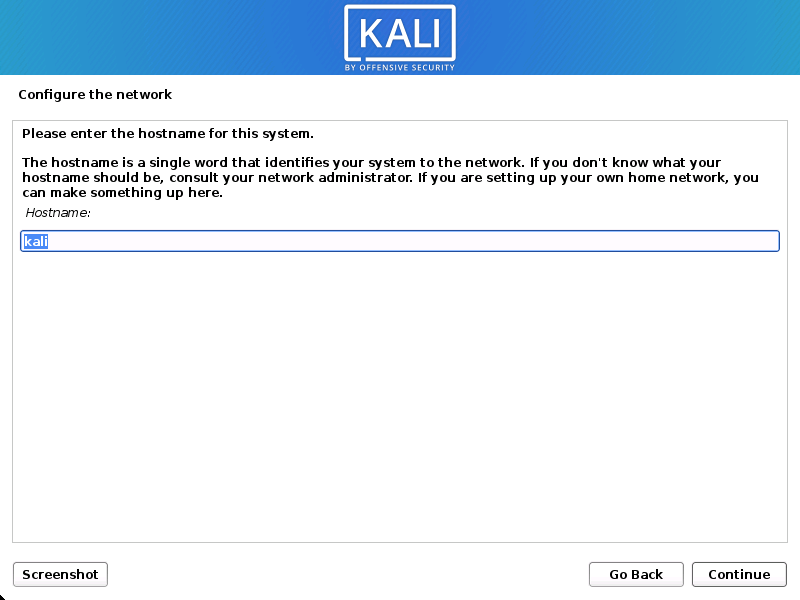
Network
- The setup will now probe your network interfaces, looks for a DHCP service, and then prompt you to enter a hostname for your system. In the example below, we’ve entered kali as our hostname.
If there is no network access with DHCP service detected, you may need to manually configure the network information or do not configure the network at this time.
- If there isn’t a DHCP service running on the network, it will ask you to manually enter the network information after probing for network interfaces, or you can skip.
- If Kali Linux doesn’t detect your NIC, you either need to include the drivers for it when prompted, or generate a custom Kali Linux ISO with them pre-included.
- If the setup detects multiple NICs, it may prompt you which one to use for the install.
- If the chosen NIC is 802.11 based, you will be asked for your wireless network information before being prompted for a hostname.
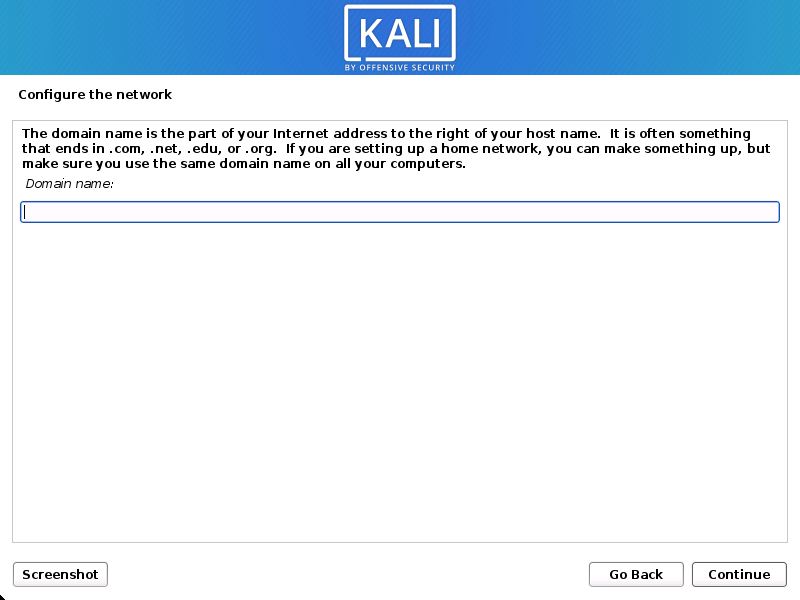
- You may optionally provide a default domain name for this system to use (values may be pulled in from DHCP or if there is an existing operating systems pre-existing).
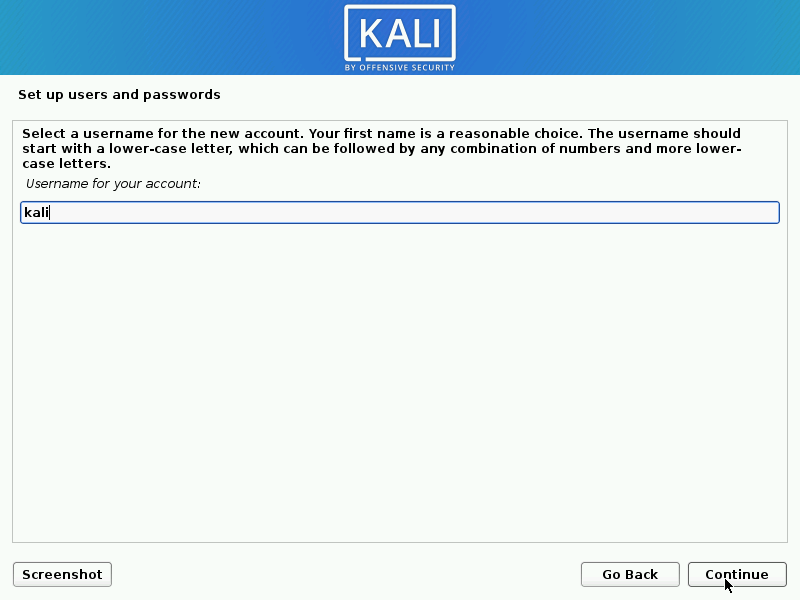
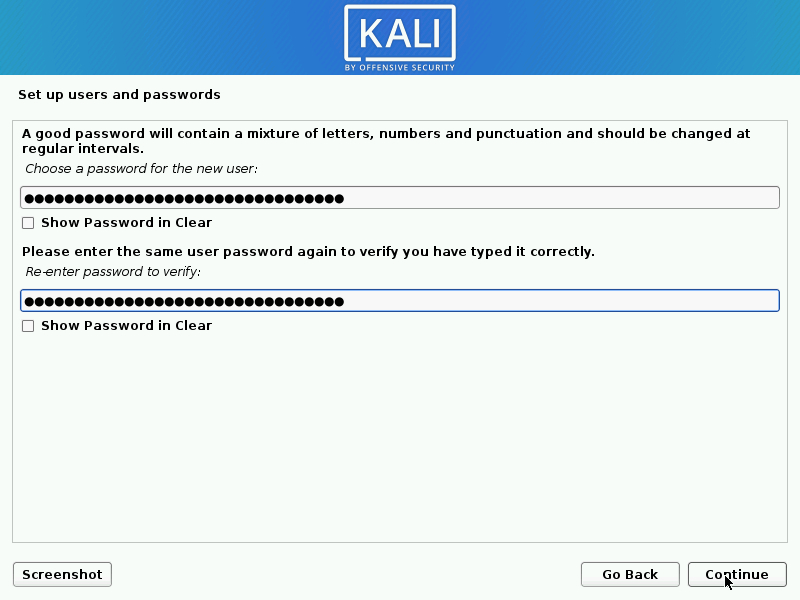
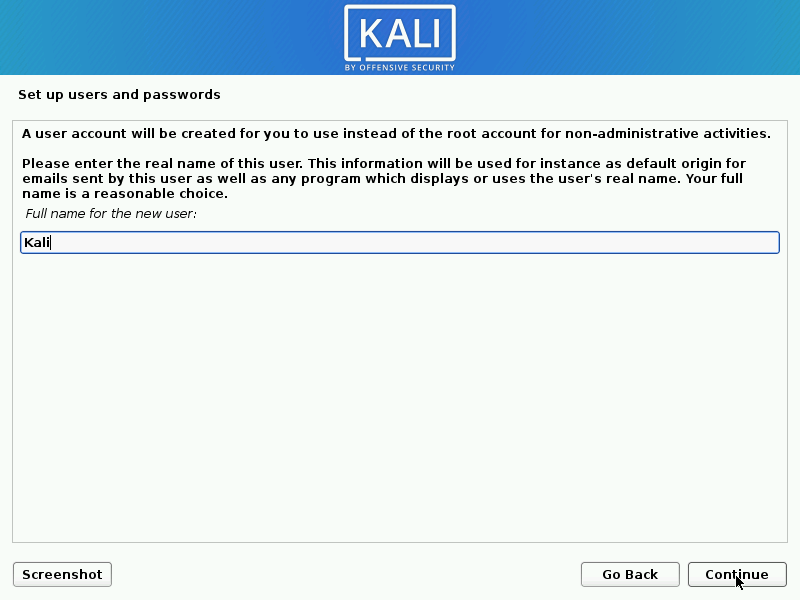
User Accounts
- Next, create the user account for the system (Full name, username and a strong password).
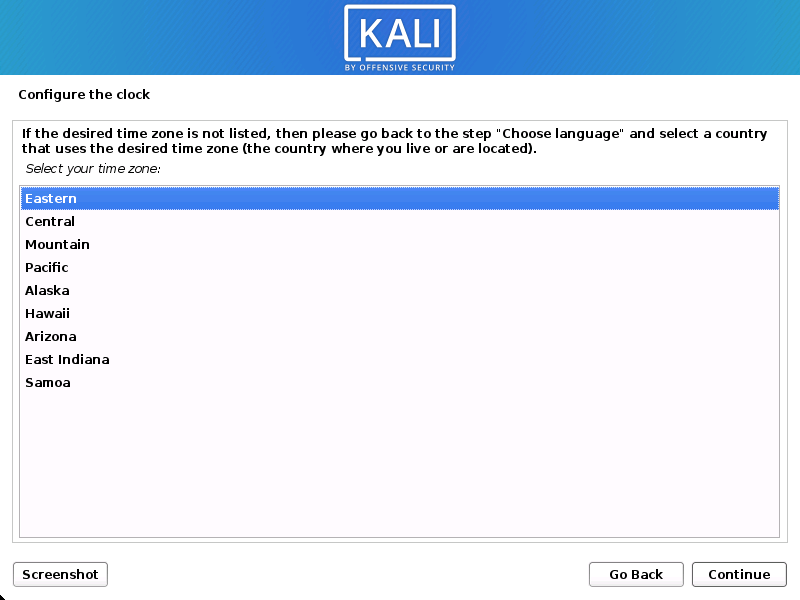
Clock
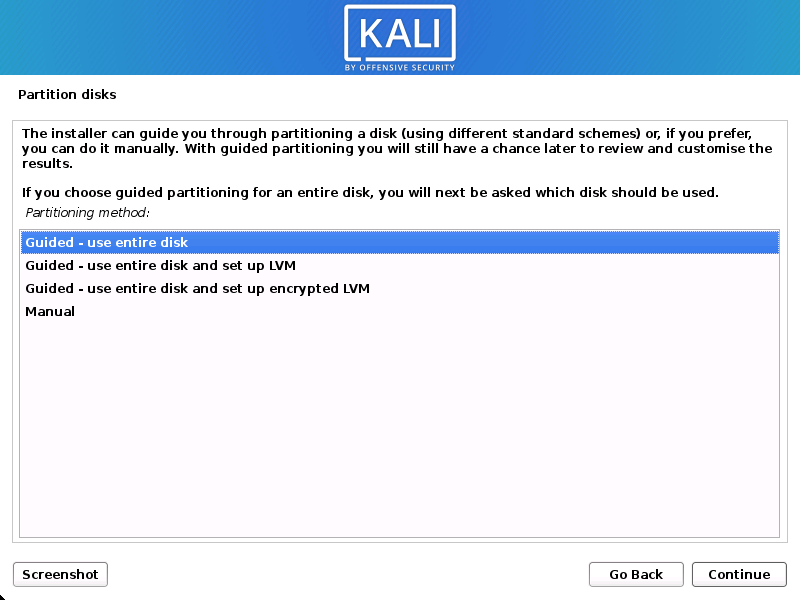
- The installer will now probe your disks and offer you various choices, depending on the setup.
In our guide, we are using a clean disk, so we have four options to pick from. We will select Guided — the entire disk, as this is the single boot installation for Kali Linux, so we do not want any other operating systems installed, so we are happy to wipe the disk.
If there is an pre-existing data on the disk, you will have have an extra option (Guided — use the largest continuous free space) than the example below. This would instruct the setup not to alter any existing data, which is perfect for for dual-booting into another operating system. As this is not the case in this example, it is not visible.
Experienced users can use the “Manual” partitioning method for more granular configuration options, which is covered more in our BTRFS guide.
If you want to encrypt Kali Linux, you can enable Full Disk Encryption (FDE), by selecting Guided — used entire disk and setup encrypted LVM. When selected, later on in the setup (not in this guide) prompt you to enter a password (twice). You will have to enter this password every time you start up Kali Linux.
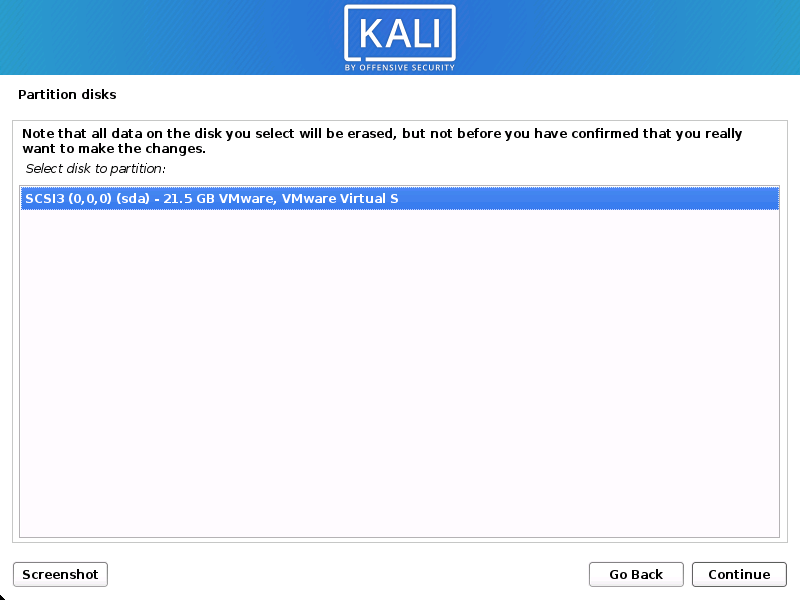
- Select the disk to be partitioned.
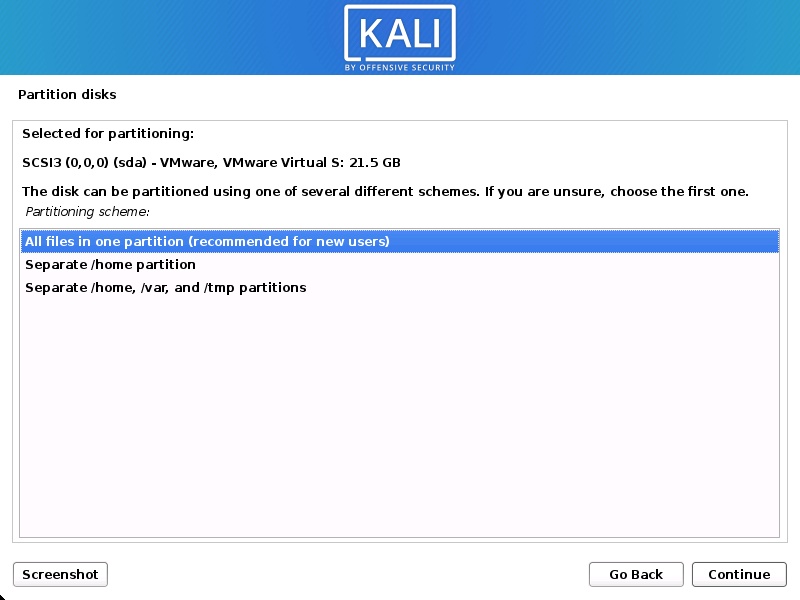
- Depending on your needs, you can choose to keep all your files in a single partition — the default — or to have separate partitions for one or more of the top-level directories.
If you’re not sure which you want, you want “All files in one partition”.
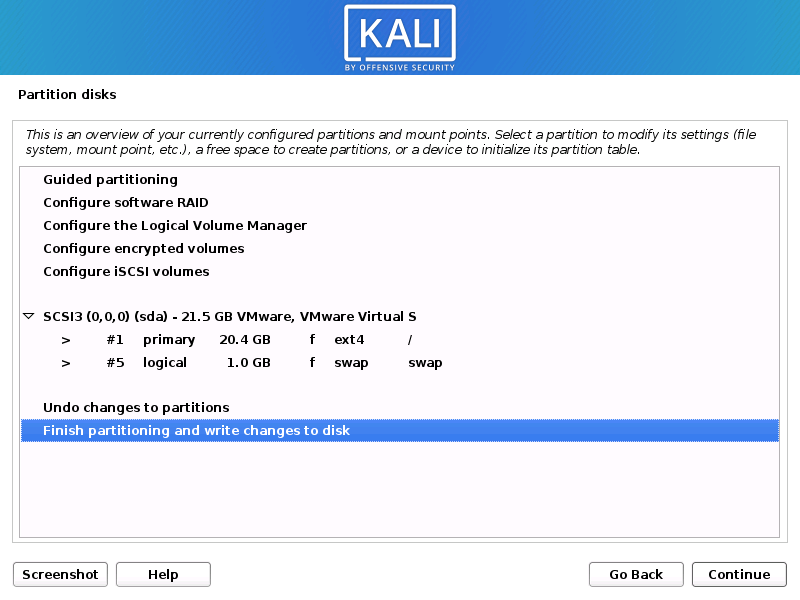
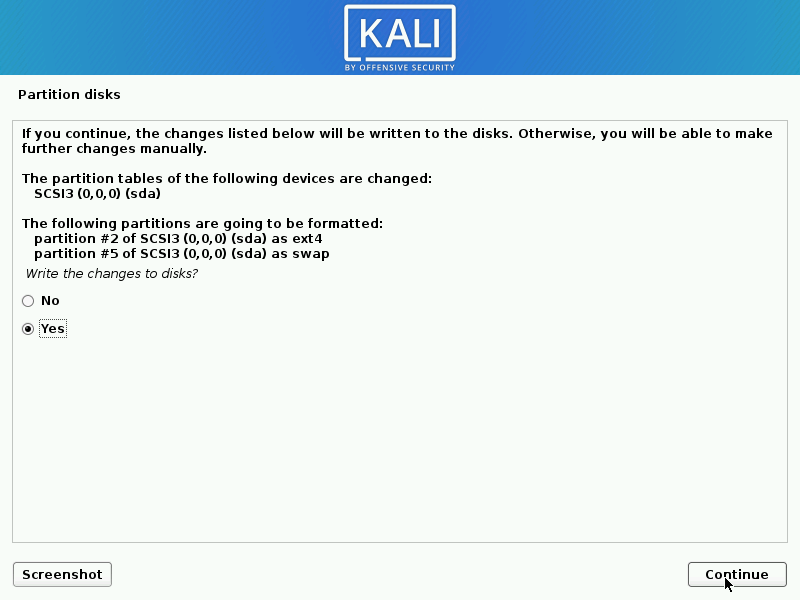
- Next, you’ll have one last chance to review your disk configuration before the installer makes irreversible changes. After you click Continue, the installer will go to work and you’ll have an almost finished installation.
Encrypted LVM
If enabled in the previous step, Kali Linux will now start to perform a secure wipe of the hard disk, before asking you for a LVM password.
Please sure a strong password, else you will have to agree to the warning about a weak passphrase.
This wipe may take “a while” (hours) depending on the size and speed of the drive.
If you wish to risk it, you can skip it.
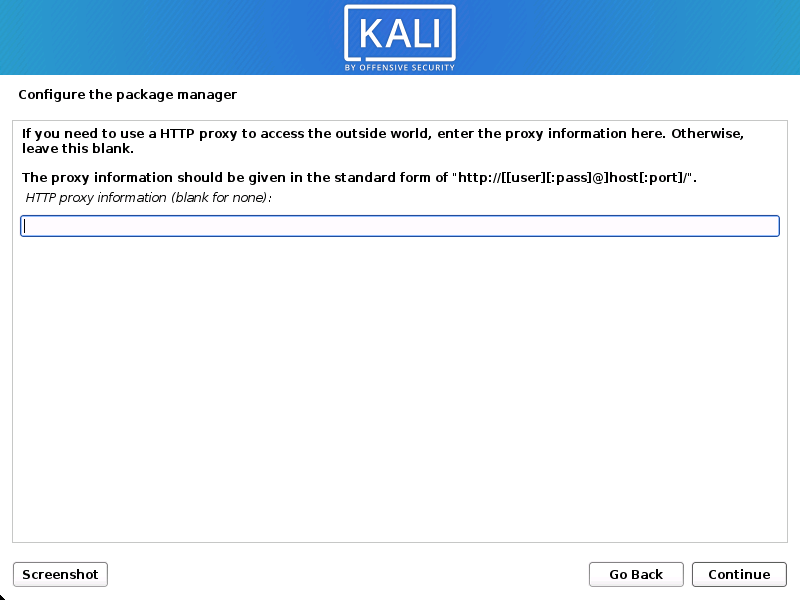
Proxy Information
- Kali Linux uses a central repository to distribute applications. You’ll need to enter any appropriate proxy information as needed.
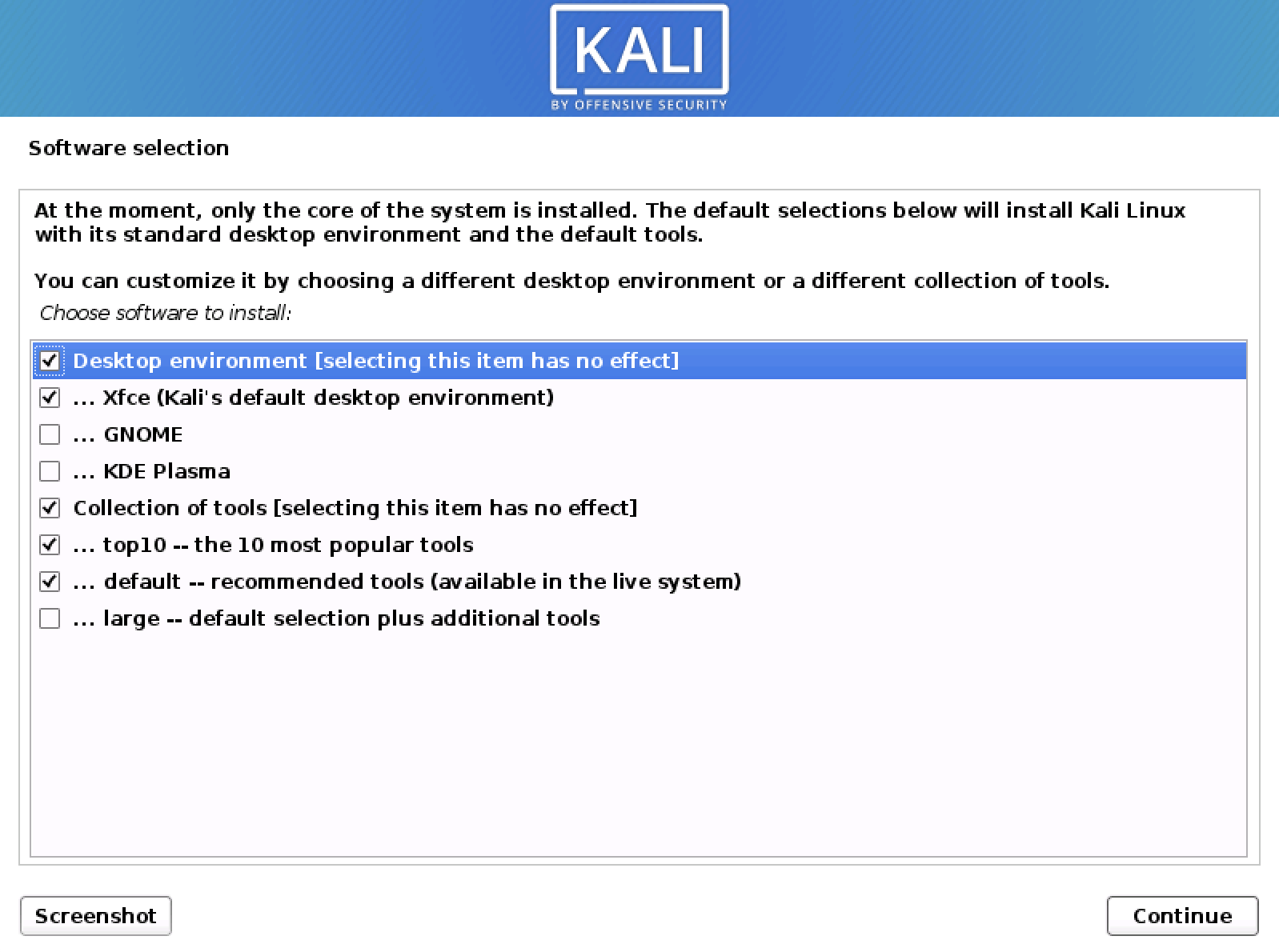
Metapackages
If network access was not setup, you will want to continue with setup when prompt.
If you are using the Live image, you will not have the following stage.
- Next you can select which metapackages you would like to install. The default selections will install a standard Kali Linux system and you don’t really have to change anything here.
Please refer to this guide if you prefer to change the default selections.
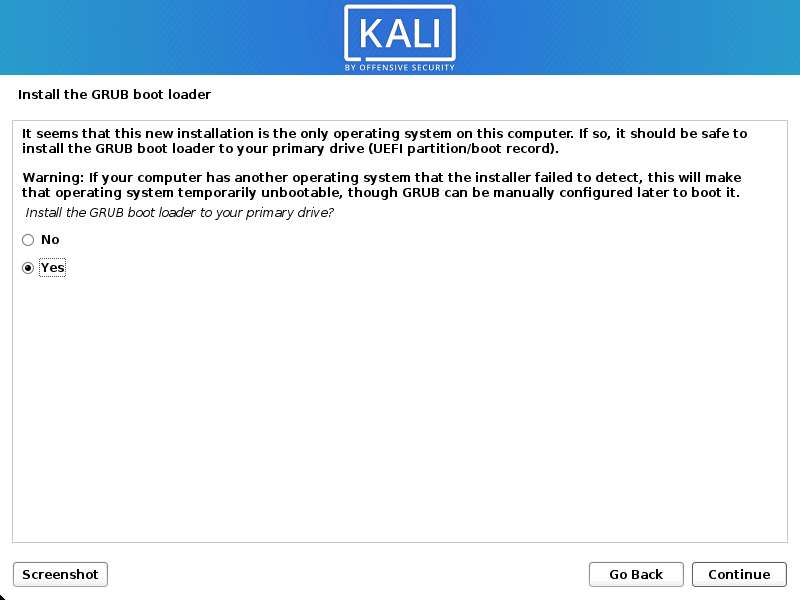
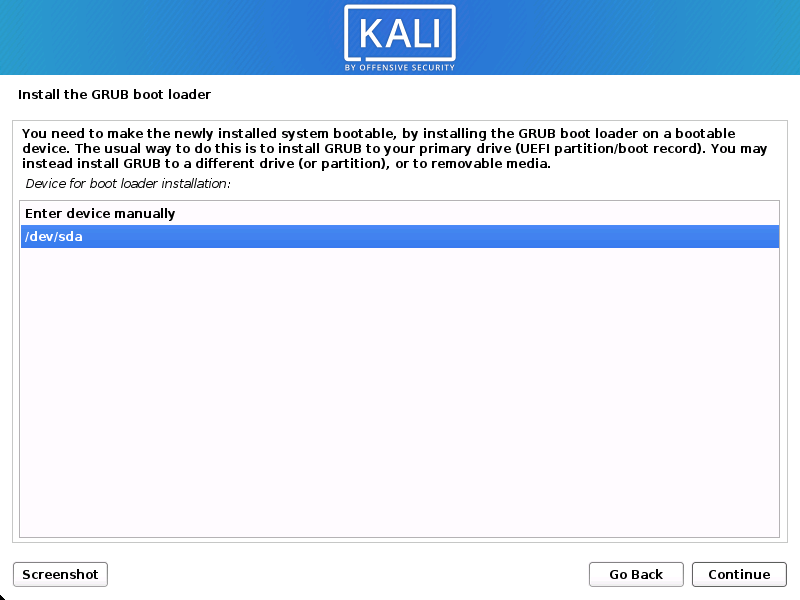
Boot Information
- Next confirm to install the GRUB boot loader.
- Select the hard drive to install the GRUB bootloader in (it does not by default select any drive).
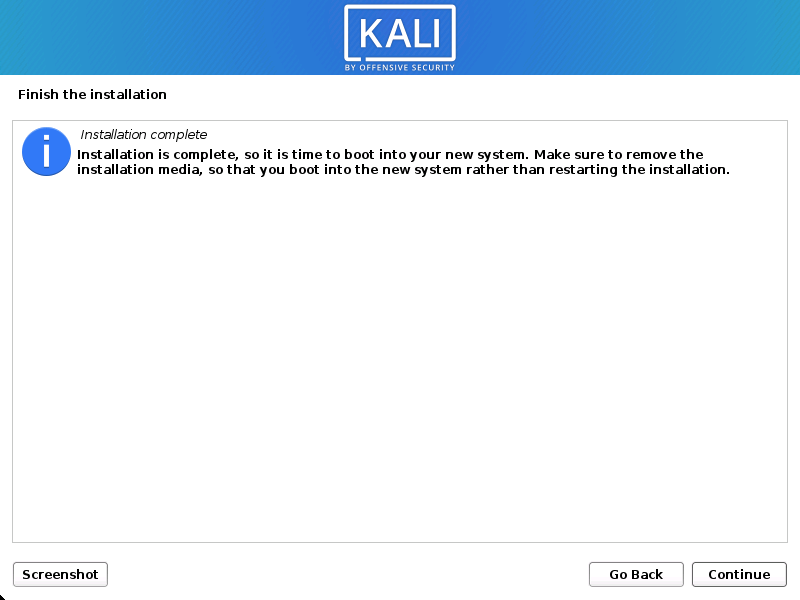
Reboot
- Finally, click Continue to reboot into your new Kali Linux installation.
Post Installation
Now that you’ve completed installing Kali Linux, it’s time to customize your system.
The General Use section has more information and you can also find tips on how to get the most out of Kali Linux in our User Forums.
Updated on: 2021-Sep-27
Author: gamb1t
Источник
How to download linux kali linux
IMPORTANT! Never download Kali Linux images from anywhere other than the official sources.
Always be sure to verify the SHA256 checksums of the file you’ve downloaded against our official values.
It would be easy for a malicious entity to modify a Kali installation to contain exploits or malware and host it unofficially.
Where to Get Official Kali Linux Images
ISO Files for Intel-based PCs
In order to run Kali “Live” from a USB drive on standard Windows and Apple PCs, you’ll need a Kali Linux bootable ISO image, in either 32-bit or 64-bit format.
If you’re not sure of the architecture of the system you want to run Kali on, on Linux or macOS, you can run the command uname -m at the command line. If you get the response, “x86_64”, use the 64-bit ISO image (the one containing “amd64” in the file name); if you get “i386”, use the 32-bit image (the one containing “i386” in the file name). If you’re on a Windows system, the procedure for determining whether your architecture is detailed on Microsoft’s website.
The Kali Linux images are available both as directly downloadable “.iso/.img” files or via “.torrent” files.
Building your own Kali Linux ISO, standard or customized, is a very simple process.
Virtual Machines Images
If you want to run Kali Linux as a “guest” under VMware or VirtualBox, Kali Linux is available as a pre-built virtual machines with any guest tools already installed. These image are available in a 64-bit (amd64), and 32-bit PAE (i*86) formats.
ARM Images
The hardware architectures of ARM-based devices vary considerably, so it is not possible to have a single image that will work across all of them. Pre-built Kali Linux images for the ARM architecture are available for a wide range of devices.
Scripts for building your own ARM images locally are also available on GitLab. For more details, see the articles on setting up an ARM cross-compilation environment and building a custom Kali Linux ARM chroot.
Verifying Your Downloaded Kali Image
Why do I need to do this?
Before you run Kali Linux Live, or install it to your hard disk, you want to be very sure that what you’ve got actually is Kali Linux, and not an imposter. Kali Linux is a professional penetration testing and forensics toolkit. As a professional penetration tester, having absolute confidence in the integrity of your tools is critical: if your tools are not trustworthy, your investigations will not be trustworthy, either.
Moreover, as the leading penetration testing distribution, Kali’s strengths mean that a bogus version of Kali Linux could do a tremendous amount of damage if it were deployed unwittingly. There are plenty of people with plenty of reason to want to stick very sketchy stuff into something that looks like Kali, and you absolutely do not want to find yourself running something like that.
Avoiding this is simple:
- Only download Kali Linux via the official download pages at kali.org/downloads/ or offensive-security.com/kali-linux-vmware-arm-image-download/ — you will not be able to browse to these pages without SSL; encrypting the connection makes it much harder for an attacker to use a “man-in-the-middle” attack to modify your download. There are a few potential weaknesses to even these sources — see the sections on verifying the download with the SHA256SUMS file and its signature against the official Kali Development team private key for something much closer to absolute assurance.
- Once you’ve downloaded an image, and before you run it, always validate that it really is what it’s supposed to be by verifying its checksum using one of the procedures detailed below.
There are several methods for verifying your download. Each provides a certain level of assurance, and involves a corresponding level of effort on your part.
- You can download an ISO image from an official Kali Linux “Downloads” mirror, calculate the ISO’s SHA256 hash and compare it by inspection with the value listed on the Kali Linux site. This is quick and easy, but potentially susceptible to subversion via a DNS poisoning: it assumes that the site to which, for example, the domain “kali.org” resolves is in fact the actual Kali Linux site. If it somehow were not, an attacker could present a “loaded” image and a matching SHA256 signature on the fake web page. See the section “Manually Verify the Signature on the ISO (Direct Download)”, below.
- You can download an ISO image through the torrents, and it will also pull down a file — unsigned — containing the calculated SHA256 signature. You can then use the shasum command (on Linux and macOS) or a utility (on Windows) to automatically verify that the file’s computed signature matches the signature in the secondary file. This is even easier than the “manual” method, but suffers from the same weakness: if the torrent you pulled down is not really Kali Linux, it could still have a good signature. See the section “Verify the Signature on the ISO Using the Included Signature File (Torrent Download)”, below.
- To be as close to absolutely certain as possible that the Kali Linux download you’ve obtained is the real thing, you can download both a cleartext signature file and and version of the same file that has been signed with the official Kali Linux private key and use GNU Privacy Guard (GPG) to first, verify that the computed SHA256 signature and the signature in the cleartext file match and second, verify that the signed version of the file containing the SHA256 hash has been correctly signed with the official key.
If you use this more complicated process and successfully validate your downloaded ISO, you can proceed with pretty complete assurance that what you’ve got is the official image and that it has not been tampered with in any way. This method, while the most complex, has the advantage of providing independent assurance of the integrity of the image. The only way this method can fail is if the official Kali Linux private key is not only subverted by an attacker, but also not subsequently revoked by the Kali Linux development team. For this method, see the section on verification using the SHA256SUMS file.
What do I need to do this?
If you’re running on Linux, you probably already have GPG (GNU Privacy Guard) installed. If you’re on Windows or macOS, you’ll need to install the appropriate version for your platform.
- If you’re on a PC running Windows, download and install GPG4Win from here. Certain versions of Windows do not have the native ability to calculate SHA256 checksums. To check this, you can open the command prompt and run certutil -? . If you do have this installed, you can run certutil -hashfile kali-linux-2021.3-live-amd64.iso sha256 to verify your download. If you do not have certutil installed, you will also need a utility such as Microsoft File Checksum Integrity Verifier or Hashtab to verify your download.
- If you’re on a Macintosh running macOS, download and install GPGTools from here. Alternatively, if you have Homebrew installed, just run brew install gnupg
Once you’ve installed GPG, you’ll need to download and import a copy of the Kali Linux official key. Do this with the following command:
Your output should look like this:
Verify that the key is properly installed with the command:
The output will look like this:
You’re now set up to validate your Kali Linux download.
How Do I Verify My Downloaded Image?
Manually Verify the Signature on the ISO (Direct Download)
If you downloaded the ISO directly from the downloads page, verify it using the following procedure.
On Linux, or macOS, you can generate the SHA256 checksum from the ISO image you’ve downloaded with the following command (assuming that the ISO image is named “kali-linux-2021.3-live-amd64.iso”, and is in your current directory):
The output should look like this:
The resulting SHA256 signature, “e316b27025922e9f6bca0cacee6dde83dbfd4a549ad18026526f5824af639fc1”, can be seen to match the signature displayed in the “sha256sum” column on the official download page for the 64-bit Intel architecture Kali Linux 2021.3 ISO image:
Verify the Signature on the ISO Using the Included Signature File (Torrent Download)
If you downloaded your copy of the Kali Linux ISO image via the torrents, in addition to the ISO file (e.g. kali-linux-2021.3-live-amd64.iso), there will be a second file containing the computed SHA256 signature for the ISO, with the extension “.txt.sha256sum” (e.g. kali-linux-2021.3-live-amd64.txt.sha256sum). You can use this file to verify the authenticity of your download on Linux or macOS with the following command:
If the image is successfully authenticated, the response will look like this:
IMPORTANT! If you are unable to verify the authenticity of the Kali Linux image you have downloaded as described in the preceding section, do NOT use it! Using it could endanger not only your own system, but any network you connect to as well as the other systems on that network. Stop, and ensure that you have downloaded the images from a legitimate Kali Linux mirror.
Verify the ISO Using the SHA256SUMS File
This is a more complex procedure, but offers a much higher level of validation: it does not rely on the integrity of the web site you downloaded the image from, only the official Kali Linux development team key that you install independently. To verify your image this way for an Intel architecture version of Kali, you will need to download three files from the Kali “Live CD Image” site for the current release (v2021.3, as of this writing):
- The ISO image itself (e.g. kali-linux-2021.3-live-amd64.iso)
- The file containing the calculated SHA256 hash for the ISO, SHA256SUMS
- The signed version of that file, SHA256SUMS.gpg
Before verifying the checksums of the image, you must ensure that the SHA256SUMS file is the one generated by Kali Linux. That’s why the file is signed by Kali’s official key with a detached signature in SHA256SUMS.gpg. If you have not already done so, Kali’s official key can be downloaded and imported into your keychain with this command:
or this command
Your output should look like this:
You should verify that the key is properly installed with the command:
The output will look like this:
Once you have downloaded both SHA256SUMS and SHA256SUMS.gpg, you can verify the signature as follows:
If you do not get that “Good signature” message or if the key ID does not match, then you should stop and review whether you downloaded the images from a legitimate Kali Linux mirror. The failed verification strongly suggests that the image you have may have been tampered with.
If you did get the “Good signature” response, you can now be assured that the checksum in the SHA256SUMS file was actually provided by the Kali Linux development team. All that remains to be done to complete the verification is to validate that the signature you compute from the ISO you’ve downloaded matches the one in the SHA256SUMS file. You can do that on Linux or macOS with the following command (assuming that the ISO is named “kali-linux-2021.3-live-amd64.iso” and is in your working directory):
If the image is successfully authenticated, the response will look like this:
If you do not get “OK” in response, then stop and review what’s happened: the Kali image you have has apparently been tampered with. Do NOT use it.
Once you’ve downloaded and verified your image, you can proceed to create a bootable “Kali Linux Live” USB drive.
Updated on: 2021-Sep-27
Authors: g0tmi1k , gamb1t
Источник