Событие с ИДЕНТИФИКАТОРом 4625 регистрируется каждые 5 минут при использовании пакета управления Exchange 2010 в Operations Manager
В этой статье описывается поведение по проекту с ИДЕНТИФИКАТОРом 4625 каждые 5 минут при использовании пакета управления Microsoft Exchange 2010 в System Center Operations Manager.
Исходная версия продукта: System Center 2012 Operations Manager
Исходный номер статьи базы знаний: 2591305
Симптомы
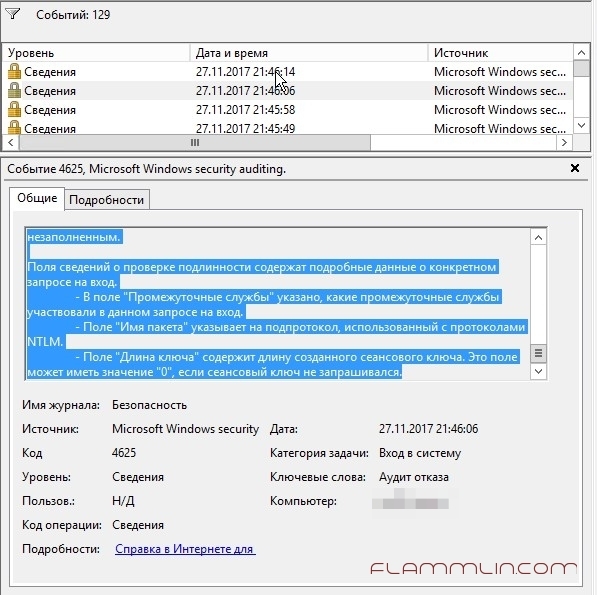
При использовании пакета управления Exchange 2010 в System Center Operations Manager можно получить событие ошибки аудита безопасности в журнале событий безопасности каждые 5 минут. Ниже приведен пример события.
Имя журнала: Security
Источник: Microsoft $ Windows — безопасность — аудит
Будущ
Идентификатор события: 4625
Категория задачи: вход в систему
Уровень: сведения
Ключевые слова: сбой аудита
Пользователь: N/A
Компьютер: имя_компьютера
Описание:
Не удалось выполнить вход в учетную запись.
Тема:
Идентификатор безопасности: NULL SID
Имя учетной записи: —
Домен учетной записи: —
Идентификатор входа: 0x0
Учетная запись, для которой не удалось выполнить вход:
Идентификатор безопасности: NULL SID
Имя учетной записи: Aextest_
Домен учетной записи:
Сведения об ошибке:
Причина ошибки: неизвестное имя пользователя или неверный пароль.
Состояние: 0xC000006D
Дочернее состояние: 0xC0000064
Сведения о процессе:
Идентификатор процесса звонящего: 0x0
Имя процесса вызывающего абонента: —
Сведения о сети:
Имя рабочей станции: воркстатионнаме
Сетевой адрес источника: саурценетворкаддресс
Исходный порт: 30956
Подробные сведения о проверке подлинности:
Процесс входа: NtLmSsp
Пакет проверки подлинности: NTLM
Транзитные службы: —
Имя пакета (только NTLM):-
Длина ключа: 0
Имя учетной записи будет иметь формат Aextest_ .
Причина
Используемая учетная запись почтовых ящиков Exchange extest_ . Этот дополнительный метод A передается таким образом, чтобы тестовая учетная запись не блокировалась.
Решение
Это событие можно игнорировать по мере его создания.
Событие 4625
Уже с год наблюдаю ошибку в логах 4625, ошибка связанная с попыткой входа по RDP. Но к сожалению в логах увидеть кто и откуда не представляется возможным.
В логах постоянно вот такая штука появлялась:
Учетной записи не удалось выполнить вход в систему. Субъект: ИД безопасности: NULL SID Имя учетной записи: — Домен учетной записи: — Код входа: 0x0 Тип входа: 3 Учетная запись, которой не удалось выполнить вход: ИД безопасности: NULL SID Имя учетной записи: АДМИНИСТРАТОР Домен учетной записи: Сведения об ошибке: Причина ошибки: Неизвестное имя пользователя или неверный пароль. Состояние: 0xC000006D Подсостояние: 0xC000006A Сведения о процессе: Идентификатор процесса вызывающей стороны: 0x0 Имя процесса вызывающей стороны: — Сведения о сети: Имя рабочей станции: — Сетевой адрес источника: — Порт источника: — Сведения о проверке подлинности: Процесс входа: NtLmSsp Пакет проверки подлинности: NTLM Промежуточные службы: — Имя пакета (только NTLM): — Длина ключа: 0 Данное событие возникает при неудачной попытке входа. Оно регистрируется на компьютере, попытка доступа к которому была выполнена. Поля «Субъект» указывают на учетную запись локальной системы, запросившую вход. Обычно это служба, например, служба «Сервер», или локальный процесс, такой как Winlogon.exe или Services.exe. В поле «Тип входа» указан тип выполненного входа. Наиболее распространенными являются типы 2 (интерактивный) и 3 (сетевой). В полях «Сведения о процессе» указано, какая учетная запись и процесс в системе выполнили запрос на вход. Поля «Сведения о сети» указывают на источник запроса на удаленный вход. Имя рабочей станции доступно не всегда, и в некоторых случаях это поле может оставаться незаполненным. Поля сведений о проверке подлинности содержат подробные данные о конкретном запросе на вход. — В поле «Промежуточные службы» указано, какие промежуточные службы участвовали в данном запросе на вход. — Поле «Имя пакета» указывает на подпротокол, использованный с протоколами NTLM. — Поле «Длина ключа» содержит длину созданного сеансового ключа. Это поле может иметь значение «0», если сеансовый ключ не запрашивался.
Периодичность таких ошибок ничем не связана. Может за раз появиться только один раз, может наоборот под 200 штук набежать. По началу думал, что проблема в сети, мол клиент какой то лезет, но проверив методом исключений, я понял. Клиент был и был он снаружи, а это значит что мы имеем самый настоящий bruteforce.
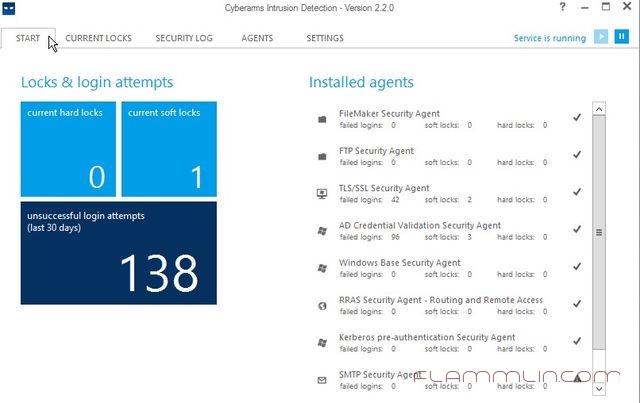
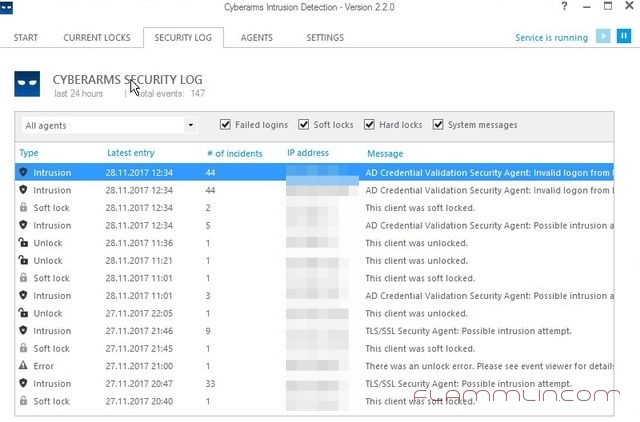
Помогла утилита Cyberarms IDDS, которая прекрасно смогла отобразить ip адрес недоброжелателя и окончательно понять, что он снаружи ломится на сервак.
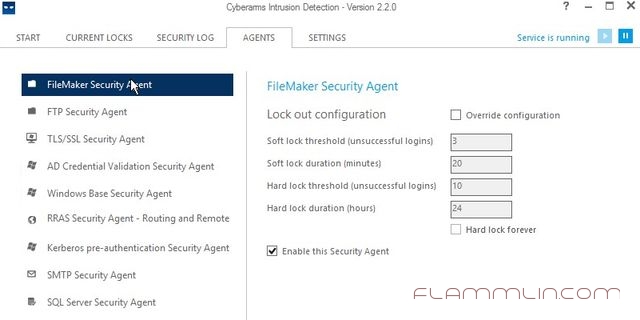
Программа достаточна проста в настройке и дополнительных знаний не требует. Необходимо сразу произвести настройку мониторинга присутствующих агентов и просто закрыть, так как программа работает как служба.
Не забываем проставлять напротив интересующих нас «служб» галочку Enable и жать кнопку Save.
В итоге работы получил вот такой отчет:
Cyberarms IDDS работает с правилами Windows FireWall и нежелательные лица добавляет туда.
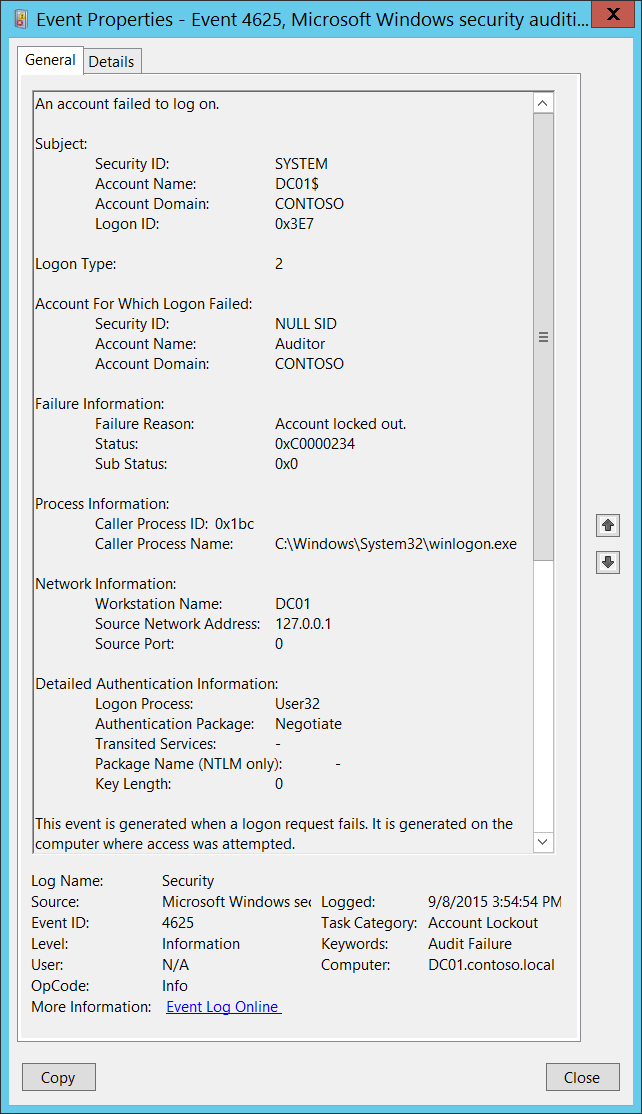
4625(F): An account failed to log on.
Applies to
- Windows 10
- Windows Server 2016
Event Description:
This event generates if an account logon attempt failed when the account was already locked out. It also generates for a logon attempt after which the account was locked out.
It generates on the computer where logon attempt was made, for example, if logon attempt was made on user’s workstation, then event will be logged on this workstation.
This event generates on domain controllers, member servers, and workstations.
For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
Required Server Roles: None.
Minimum OS Version: Windows Server 2008, Windows Vista.
Event Versions: 0.
Field Descriptions:
Subject:
Security ID [Type = SID]: SID of account that reported information about logon failure. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account that reported information about logon failure.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Here are some examples of formats:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon Type [Type = UInt32]: the type of logon that was performed. “Table 11. Windows Logon Types” contains the list of possible values for this field.
Table 11: Windows Logon Types
| Logon Type | Logon Title | Description |
|---|---|---|
| 2 | Interactive | A user logged on to this computer. |
| 3 | Network | A user or computer logged on to this computer from the network. |
| 4 | Batch | Batch logon type is used by batch servers, where processes may be executing on behalf of a user without their direct intervention. |
| 5 | Service | A service was started by the Service Control Manager. |
| 7 | Unlock | This workstation was unlocked. |
| 8 | NetworkCleartext | A user logged on to this computer from the network. The user’s password was passed to the authentication package in its unhashed form. The built-in authentication packages all hash credentials before sending them across the network. The credentials do not traverse the network in plaintext (also called cleartext). |
| 9 | NewCredentials | A caller cloned its current token and specified new credentials for outbound connections. The new logon session has the same local identity, but uses different credentials for other network connections. |
| 10 | RemoteInteractive | A user logged on to this computer remotely using Terminal Services or Remote Desktop. |
| 11 | CachedInteractive | A user logged on to this computer with network credentials that were stored locally on the computer. The domain controller was not contacted to verify the credentials. |
Account For Which Logon Failed:
Security ID [Type = SID]: SID of the account that was specified in the logon attempt. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account that was specified in the logon attempt.
Account Domain [Type = UnicodeString]: domain or computer name. Here are some examples of formats:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4624: An account was successfully logged on.”
Failure Information:
Failure Reason [Type = UnicodeString]: textual explanation of Status field value. For this event, it typically has “Account locked out” value.
Status [Type = HexInt32]: the reason why logon failed. For this event, it typically has “0xC0000234” value. The most common status codes are listed in Table 12. Windows logon status codes.
Table 12: Windows logon status codes.
| Status\Sub-Status Code | Description |
|---|---|
| 0XC000005E | There are currently no logon servers available to service the logon request. |
| 0xC0000064 | User logon with misspelled or bad user account |
| 0xC000006A | User logon with misspelled or bad password |
| 0XC000006D | The cause is either a bad username or authentication information |
| 0XC000006E | Indicates a referenced user name and authentication information are valid, but some user account restriction has prevented successful authentication (such as time-of-day restrictions). |
| 0xC000006F | User logon outside authorized hours |
| 0xC0000070 | User logon from unauthorized workstation |
| 0xC0000071 | User logon with expired password |
| 0xC0000072 | User logon to account disabled by administrator |
| 0XC00000DC | Indicates the Sam Server was in the wrong state to perform the desired operation. |
| 0XC0000133 | Clocks between DC and other computer too far out of sync |
| 0XC000015B | The user has not been granted the requested logon type (also called the logon right) at this machine |
| 0XC000018C | The logon request failed because the trust relationship between the primary domain and the trusted domain failed. |
| 0XC0000192 | An attempt was made to logon, but the Netlogon service was not started. |
| 0xC0000193 | User logon with expired account |
| 0XC0000224 | User is required to change password at next logon |
| 0XC0000225 | Evidently a bug in Windows and not a risk |
| 0xC0000234 | User logon with account locked |
| 0XC00002EE | Failure Reason: An Error occurred during Logon |
| 0XC0000413 | Logon Failure: The machine you are logging on to is protected by an authentication firewall. The specified account is not allowed to authenticate to the machine. |
| 0x0 | Status OK. |
To see the meaning of other status or substatus codes, you might also check for status code in the Window header file ntstatus.h in Windows SDK.
- Sub Status [Type = HexInt32]: additional information about logon failure. The most common substatus codes listed in the “Table 12. Windows logon status codes.”.
Process Information:
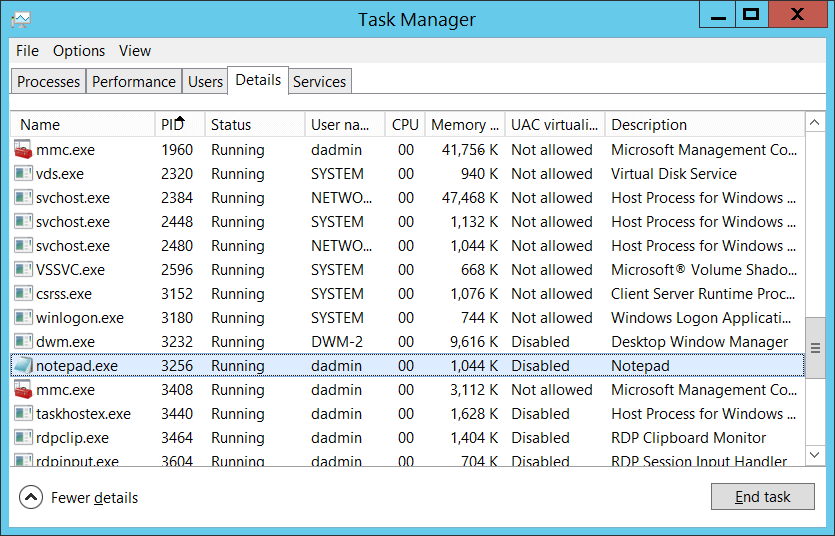
Caller Process ID [Type = Pointer]: hexadecimal Process ID of the process that attempted the logon. Process ID (PID) is a number used by the operating system to uniquely identify an active process. To see the PID for a specific process you can, for example, use Task Manager (Details tab, PID column):
If you convert the hexadecimal value to decimal, you can compare it to the values in Task Manager.
You can also correlate this process ID with a process ID in other events, for example, “4688: A new process has been created” Process Information\New Process ID.
Caller Process Name [Type = UnicodeString]: full path and the name of the executable for the process.
Network Information:
Workstation Name [Type = UnicodeString]: machine name from which logon attempt was performed.
Source Network Address [Type = UnicodeString]: IP address of machine from which logon attempt was performed.
IPv6 address or ::ffff:IPv4 address of a client.
::1 or 127.0.0.1 means localhost.
Source Port [Type = UnicodeString]: source port that was used for logon attempt from remote machine.
Detailed Authentication Information:
Logon Process [Type = UnicodeString]: the name of the trusted logon process that was used for the logon attempt. See event “4611: A trusted logon process has been registered with the Local Security Authority” description for more information.
Authentication Package [Type = UnicodeString]: The name of the authentication package that was used for the logon authentication process. Default packages loaded on LSA startup are located in “HKLM\SYSTEM\CurrentControlSet\Control\Lsa\OSConfig” registry key. Other packages can be loaded at runtime. When a new package is loaded a “4610: An authentication package has been loaded by the Local Security Authority” (typically for NTLM) or “4622: A security package has been loaded by the Local Security Authority” (typically for Kerberos) event is logged to indicate that a new package has been loaded along with the package name. The most common authentication packages are:
NTLM – NTLM-family Authentication
Kerberos – Kerberos authentication.
Negotiate – the Negotiate security package selects between Kerberos and NTLM protocols. Negotiate selects Kerberos unless it cannot be used by one of the systems involved in the authentication or the calling application did not provide sufficient information to use Kerberos.
Transited Services [Type = UnicodeString] [Kerberos-only]: the list of transmitted services. Transmitted services are populated if the logon was a result of a S4U (Service For User) logon process. S4U is a Microsoft extension to the Kerberos Protocol to allow an application service to obtain a Kerberos service ticket on behalf of a user – most commonly done by a front-end website to access an internal resource on behalf of a user. For more information about S4U, see https://msdn.microsoft.com/library/cc246072.aspx
Package Name (NTLM only) [Type = UnicodeString]: The name of the LAN Manager subpackage (NTLM-family protocol name) that was used during the logon attempt. Possible values are:
Only populated if “Authentication Package” = “NTLM”.
Key Length [Type = UInt32]: the length of NTLM Session Security key. Typically, it has a length of 128 bits or 56 bits. This parameter is always 0 if «Authentication Package» = «Kerberos», because it is not applicable for Kerberos protocol. This field will also have “0” value if Kerberos was negotiated using Negotiate authentication package.
Security Monitoring Recommendations
For 4625(F): An account failed to log on.
If you have a pre-defined “Process Name” for the process reported in this event, monitor all events with “Process Name” not equal to your defined value.
You can monitor to see if “Process Name” is not in a standard folder (for example, not in System32 or Program Files) or is in a restricted folder (for example, Temporary Internet Files).
If you have a pre-defined list of restricted substrings or words in process names (for example, “mimikatz” or “cain.exe”), check for these substrings in “Process Name.”
If Subject\Account Name is a name of service account or user account, it may be useful to investigate whether that account is allowed (or expected) to request logon for Account For Which Logon Failed\Security ID.
To monitor for a mismatch between the logon type and the account that uses it (for example, if Logon Type 4-Batch or 5-Service is used by a member of a domain administrative group), monitor Logon Type in this event.
If you have a high-value domain or local account for which you need to monitor every lockout, monitor all 4625 events with the “Subject\Security ID” that corresponds to the account.
We recommend monitoring all 4625 events for local accounts, because these accounts typically should not be locked out. Monitoring is especially relevant for critical servers, administrative workstations, and other high-value assets.
We recommend monitoring all 4625 events for service accounts, because these accounts should not be locked out or prevented from functioning. Monitoring is especially relevant for critical servers, administrative workstations, and other high value assets.
If your organization restricts logons in the following ways, you can use this event to monitor accordingly:
If the “Account For Which Logon Failed \Security ID” should never be used to log on from the specific Network Information\Workstation Name.
If a specific account, such as a service account, should only be used from your internal IP address list (or some other list of IP addresses). In this case, you can monitor for Network Information\Source Network Address and compare the network address with your list of IP addresses.
If a particular version of NTLM is always used in your organization. In this case, you can use this event to monitor Package Name (NTLM only), for example, to find events where Package Name (NTLM only) does not equal NTLM V2.
If NTLM is not used in your organization, or should not be used by a specific account (New Logon\Security ID). In this case, monitor for all events where Authentication Package is NTLM.
If the Authentication Package is NTLM. In this case, monitor for Key Length not equal to 128, because all Windows operating systems starting with Windows 2000 support 128-bit Key Length.
If Logon Process is not from a trusted logon processes list.
Monitor for all events with the fields and values in the following table: