- How to run a .NET Core console app as a service using Systemd on Linux (RHEL)
- .NET Core console application #
- .NET Core worker template #
- Adding .NET Core Systemd integration #
- Summary #
- How to run ASP.NET Core Web Application as a service on Linux without reverse proxy, no NGINX or Apache
- Run ASP.NET Core using Systemd #
- Add Systemd integration package #
- Make ASP.NET Core accessible externally #
- Serve ASP.NET Core over port 80 & 443 #
- Use a Reverse Proxy #
- Grant CAP_NET_BIND_SERVICE capability #
- Summary #
- Niels Swimberghe
How to run a .NET Core console app as a service using Systemd on Linux (RHEL)
Niels Swimberghe — 1/31/2020 — .NET
This article walks us through running a .NET Core console application on systemd. After running a simple console app as a service, we’ll upgrade to the worker template which is designed for long running services/ daemons . Lastly, we’ll add the systemd package for increased integration with systemd.
To learn how to run ASP.NET Core services (web stuff) on Linux, check out «How to run ASP.NET Core as a service on Linux without reverse proxy, no NGINX or Apache».
- Red Hat Enterprise Linux (or a compatible Unix based OS)
- .NET Core 3.1 installed (Get started instructions from Red Hat)
- Sudo privileges
This walkthrough should work for most .NET Core supported Linux distributions, not just RHEL.
.NET Core console application #
Let’s start by making a new console application using the dotnet CLI:
Verify that the console app works by running ` dotnet run `. The output should be «Hello World!».
If the application works, we can publish it somewhere logical such as ‘/srv/HelloWorld’:
The published result contains an executable called ‘HelloWorld’ which will run the application. Let’s verify we can also run the published application:
To run services on Linux, Systemd uses ‘ service unit configuration ‘ files to configure services.
Let’s create the file ‘HelloWorld.service’ inside our project so we can store it in source control along with our code. Add the following content to the file:
Make sure to update the ‘User’ to your username. Refer to the comments in the file for a basic explanation. For more in depth information, read the freedesktop manual page or the Red Hat documentation.
Systemd expects all configuration files to be put under ‘/etc/systemd/system/’. Copy the service configuration file to ‘/etc/systemd/system/HelloWorld.service‘. Then tell systemd to reload the configuration files, and start the service.
Using the ` systemctl status ` command we can view the status of the service:
In addition to the status command, we can use the ‘journalctl’ command to read everything our service is printing to the console. Using the unit-flag (-u), we can filter down to our HelloWorld service.
The console app only logs «Hello world!» to the console and then exits. When querying the status, systemd reports the service is inactive (dead). That’s because the console app starts, runs, and immediately exits. That’s not very useful, so let’s add some code that will let the app run until told to stop. Update Program.cs with the following content:
Let’s publish the app again:
Now we have a minimal application that is continuously running until told to stop.
If the application stops due to a crash, systemd will not automatically restart the service unless we configure that. Add the ‘Restart’ & ‘RestartSec’ options to HelloWorld.service:
Copy the service file, reload, and restart the service:
Now the service will automatically restart in case of a crash. But when the OS reboots, the application will not automatically start. To enable automatic startup of the service on boot, run the following command:
This console app works fine, but Microsoft has provided the worker template which is a more robust solution for long running services/daemons. Let’s upgrade to using the worker template next.
.NET Core worker template #
Let’s create a new empty directory and create the worker using the dotnet CLI:
Verify the worker is functional using the command ` dotnet run `.
If the application works, publish it somewhere logical such as ‘/srv/Worker’:
Let’s verify we can also run the published application:
Create a s ervice unit configuration file called «Worker.service» inside our project:
Copy the service configuration file to ‘ /etc/systemd/system/Worker.service ‘ and tell systemd to reload the configuration files:
Using ‘journalctl’, we can verify that the application is contentiously running successfully. The following ‘journalctl’ command will follow the output of the application. Use Ctrl-C to exit the command.
The .NET Core worker now runs as a systemd service, but the integration between .NET Core and systemd can bi improved on by installing the systemd-integration.
Adding .NET Core Systemd integration #
Microsoft recently added a package to better integrate with systemd. The .NET Core application will notify systemd when it’s ready and when it’s stopping. Additionally, systemd will now understand the different log levels when the .NET Core application logs to output.
Using the dotnet CLI, add the ‘Microsoft.Extensions.Hosting.Systemd’ ( nuget ) package:
Next, we’ll need to add one line to the ‘Program.cs’, ` .UseSystemd() `:
Lastly, we need to update our service unit configuration file to specify ‘type=Notify’:
Let’s publish, reload, and restart the service:
With the Systemd integration in place, we can now use the priority-flag (-p) on ‘journalctl’ to filter the output according to the log levels below:
| LogLevel | Syslog level | systemd name |
| Trace/Debug | 7 | debug |
| Information | 6 | info |
| Warning | 4 | warning |
| Error | 3 | err |
| Critical | 2 | crit |
For example, the following command will only print output with log level 4 and below:
We won’t see much because there’s nothing being logged as a warning, error, or critical.
Update the ‘Worker.cs’ file to include ‘LogWarning’, ‘LogError’, ‘LogCritical’ and republish:
Republish and restart the service:
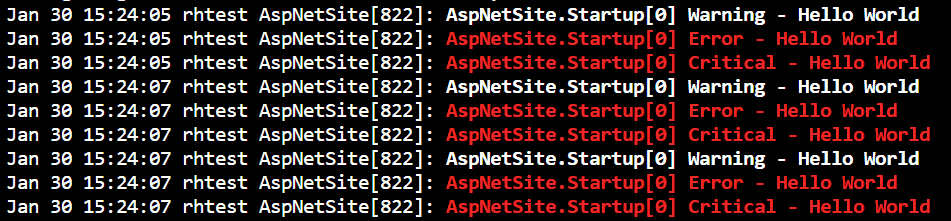
When we run the same ‘journalctl’ command, we can now see the warning output as bold white text, the error and critical output as red bold text.
The ‘UseSystemd’ function will not do anything when run outside of a systemd service.
The implementation checks if the OS is a Unix system and whether the parent process is systemd.
If not, the systemd integration is skipped.
Summary #
.NET Core has good support for running services on Linux. Using the worker template, we can create a long running service/daemon that integrates well with systemd. Using the systemd hosting integration, systemd is notified when the .NET Core application is ready & also understand the different log levels in .NET.
Источник
How to run ASP.NET Core Web Application as a service on Linux without reverse proxy, no NGINX or Apache
Niels Swimberghe — 2/10/2020 — .NET
This article walks us through running a ASP.NET Core web application on Linux (RHEL) using systemd. Here’s what we’ll cover:
- Running ASP.NET Core using systemd
- Adding Systemd integration package
- Making ASP.NET Core accessible externally (Kestrel only, no reverse proxy)
- Serving ASP.NET Core over port 80 & 443 (Kestrel only, no reverse proxy)
The end goal is to serve ASP.NET Core directly via the built-in Kestrel webserver over port 80/443.
No reverse proxy, no NGINX and no Apache. Reverse proxies are great and still recommended but there’s enough of documentation on that already.
To learn how to run .NET Core services (non web stuff) on Linux, check out «How to run a .NET Core as a service using Systemd on Linux»
- Red Hat Enterprise Linux (or a compatible Unix based OS)
- .NET Core 3.1 installed (Get started instructions from Red Hat)
- Sudo privileges
This walkthrough should work for most .NET Core supported Linux distributions, not just RHEL.
Run ASP.NET Core using Systemd #
Let’s start by creating a new ASP.NET Core application using the web-template:
We’ll be using this application throughout the walkthrough. Let’s verify that the web application works:
Open a separate shell (leave the other shell running) and use the curl HTTP-client to send an HTTP request to the application:
If the application works, we can publish it somewhere logical such as ‘/srv/AspNetSite’:
The published result contains an executable called ‘AspNetSite’ which will run the application. Let’s verify we can also run the published application:
Make sure to return to the original directory by running ` cd
/AspNetSite `. To run services on Linux, Systemd uses ‘service unit configuration‘ files to describe how to run services. Let’s create the file ‘AspNetSite.service‘ inside our project so we can store it in source control along with our code. Add the following content to ‘AspNetSite.service’:
Make sure to update the ‘User’ to your username. Refer to the comments for an explanation of the specified options. For more information on the service unit configuration file, read the freedesktop manual page or the Red Hat documentation.
Systemd expects all configuration files to be put under ‘/etc/systemd/system/’. Copy the service configuration file to ‘/etc/systemd/system/AspNetSite.service’ and tell systemd to reload the configuration files.
Now systemd is aware of the new ‘AspNetSite’ service. Using ` systemctl start AspNetSite ` we can start the service.
Using ` systemctl status AspNetSite ` we can query the status of the service. Let’s start the service and check its status:
Due to the ` Restart=always ` option, systemd will restart our service in case it crashed. But it will not automatically start the service when the machine reboots. To enable automatic startup, use the following command:
If everything is working correctly, we should be able to curl the application via localhost:5000:
The website is now running as a systemd service. There’s a systemd-package provided by Microsoft to improve the integration with systemd. Let’s set that up next.
Add Systemd integration package #
Microsoft recently added a package to better integrate with systemd. When the integration is installed, the application will notify systemd when it’s ready and when it’s stopping. Additionally, systemd will understand the different log levels that the application logs.
Using the dotnet CLI, add the ‘Microsoft.Extensions.Hosting.Systemd’ (nuget) package:
Next, we’ll need to add one line to the ‘Program.cs’, ` .UseSystemd() `:
For demonstration purposes of the logging integration, update the ‘Program.cs’ file with the following:
Lastly, we need to update the file ‘AspNetSite.service’ to specify ‘type=Notify’:
Let’s deploy all our changes. We’ll need to publish the .NET app and stop/reload/start the systemd service:
The application logs are being captured by systemd. We can query the logs using ‘journalctl’, here are some examples:
The unit-flag (-u) allows us to filter by ‘SyslogIdentifier’ which we specified in ‘AspNetSite.service’.
We can verify that the .NET Core logging integrates correctly by using the priority-flag (-p) on ‘journalctl’. This will filter the output according the log levels below:
| LogLevel | Syslog level | systemd name |
| Trace/Debug | 7 | debug |
| Information | 6 | info |
| Warning | 4 | warning |
| Error | 3 | err |
| Critical | 2 | crit |
For example, the following command will only print output with log level 4 and below meaning warning, error, and critical:
Let’s first make a couple of HTTP request to the application using curl and then run the ‘journalctl’ query:
The ‘journalctl’ command should now return the different log statements we wrote 3 times.
The ‘UseSystemd’ function will not do anything when run outside of a systemd service. The implementation checks if the OS is a Unix system and whether the parent process is systemd.
If not, the systemd integration is skipped.
We now have our systemd-integration ready, but the application is still not accessible outside of the machine. Let’s make the application accessible externally.
Make ASP.NET Core accessible externally #
As demonstrated below, the application is only accessible via localhost on the machine and not via the machine’s IP-address.
Out of the box, the application is configured to listen to http://localhost:5000 & https://localhost:5001. This works great for development, but we want to expose our application to other machines in the network or even to the internet. In ASP.NET Core there are many ways to configure the URL’s. We can configure it through code, appsettings.json, environment variables, or command line arguments.
Let’s go with environment variables. Add the ‘ASPNETCORE_URLS’ environment variable to the ‘AspNetSite.service’ file:
Instead of specifying localhost or an IP-address, the asterisk (*) will act as a wildcard. The application will now listen to localhost and all IP-addresses assigned to the machine.
Let’s copy the updated configuration file and reload/restart the systemd service:
Instead of http://localhost:5000, we can now see http://[::]:5000. Now that the application is bound to the machine’s IP-address, we should be able to curl it via IP from within the machine:
Does this mean the website is accessible from outside the machine now?
Almost, Red Hat comes with a built-in firewall which will block the traffic. Using the ‘firewall-cmd’ utility, we can update the firewall configuration to allow TCP traffic over port 5000 & 5001:
Now the website will be accessible from other machines within the network.
In case you’re running this RHEL machine in the cloud, you will also have to ensure whatever security is provided by the cloud also allow TCP over port 5000 & 5001.
Once that’s done, the website should be accessible to the internet.
Serve ASP.NET Core over port 80 & 443 #
By default, Linux machines won’t allow processes to use well known ports (ports lower than 1024).
If we try to run the application using port 80 and/or 443, we’ll get a permission error:
There are many ways to work around this restriction.
Use a Reverse Proxy #
We can setup a reverse proxy to listen to port 80 & 443 and have it forward traffic to the ASP.NET Core application. This process is well documented by Microsoft:
This is a great option for many reasons, but we’re not going to do this since our goal for this walkthrough is to stick to the built-in Kestrel server exclusively.
Grant CAP_NET_BIND_SERVICE capability #
Using the following command, we can give the AspNetSite executable the ‘CAP_NET_BIND_SERVICE’ capability. This capability will allow the process to bind to well known ports.
Every time the executable is updated the ‘CAP_NET_BIND_SERVICE’ capability will be lost. We could make this command as part of a deployment script, but the systemd service unit configuration files has an option called ‘AmbientCapabilities’.
When configuring this option to ‘CAP_NET_BIND_SERVICE’, systemd will grant the capability to the service for us. Let’s update the ‘AspNetSite.service’ file to update the ports and add the capability to bind to well known ports.
For the last time, copy the ‘AspNetSite.service’ file and reload/restart the AspNetSite service.
The web application is now listening to port 80 & 443, but the built-in firewall will still block traffic coming in over those ports. Update the built-in firewall and any other network security to allow traffic over port 80 & 443:
Visiting the website over port 80 using the browser should now return «Hello World!».
Summary #
We now have a public facing ASP.NET Core application served by the built-in Kestrel web server by taking the following steps:
- deploy ASP.NET Core to RHEL under /srv/AspNetSite
- configure systemd to run the application as a service
- add systemd .NET Core integration to the application
- configure the application to listen to all IP’s and different ports using environment variables
- update the built-in firewall to allow TCP traffic over 5000, 5001, 80, and 443
- grant ‘CAP_NET_BIND_SERVICE’ capability to the service to allow the application to bind to well known ports such as 80 & 443
Niels Swimberghe
Niels Swimberghe is a Belgian Full Stack Developer solving problems and delivering value to customers using .NET technologies for back-end systems, and modern JavaScript technologies for the front-end.
Found this article useful? Follow me on Twitter, buy me a coffee, add this blog to your feed reader!
Источник