- Ethical hacking and penetration testing
- InfoSec, IT, Kali Linux, BlackArch
- How to reset a forgotten login password in Linux
- How to change a Linux user password
- What to do if forgot Linux login password
- Resetting the password in Linux Mint, Ubuntu, Debian, Kali Linux (should also work for other Debian derivatives)
- How to reset the password in Arch Linux, BlackArch (and also in other Arch Linux derivatives)
- Reset your password in RHEL/CentOS 7
- In GRUB 2 one cannot change the password in single user mode?
- Как сбросить пароль в Linux
- Когда можно использовать GRUB
- Когда нет возможности использовать GRUB
- 9 Linux account password policies explained
- 1. Password Max days
- 2. Password min days
- 3. Password warning days
- 4. Password history depth
- 5. Password minimum length
- 6. Minimum upper case characters
- 7. Minimum lower case characters
- 8. Minimum digits in password
- 9. Wrong password retry
Ethical hacking and penetration testing
InfoSec, IT, Kali Linux, BlackArch
How to reset a forgotten login password in Linux
If you cannot log in to the Linux system because you forgot your user account password, it is possible to solve the problem! Although this password cannot be recovered (by simple methods), but it can be reset and replaced with a new one, this guide will tell you what to do if forgot the user’s password in Linux.
How to change a Linux user password
Any users from the group of administrators (whose account is in the group wheel) can change the password for any other user, both for unprivileged accounts, and for other administrators, including root. Therefore, if you forgot the root password, but remember the password of the user who has the right to execute commands with sudo, then the password can be restored with the passwd command. To change the root password, run:

To change the password of any user:
Where instead of username you need to substitute the name of the Linux user account.
What to do if forgot Linux login password
If you do not have other administrative accounts and if you forgot the Linux account password, you cannot enter the operating system, then to reset the password we need a single-user mode.
In single-user mode, credentials are not asked (login, password), while the logged user has superuser permissions. In this mode, using the familiar passwd command, it is possible to set a new password.
The algorithm in all Linux distributions is similar:
- Interrupting the GRUB boot loader
- Add the boot option that enable single-user mode
- Resume booting
- Change password with passwd command
- Restart in normal mode
Note that the changes made in the second step (changing the download options) are temporary — they affect only one subsequent booting. Therefore, when you reboot at the fifth step, you do not need to do anything — the system will operate in normal mode.
To move to the end of the line and to the beginning of the line (in the second step), use the keyboard shortcuts Ctrl+a and Ctrl+e.
Although the root password reset algorithm is similar, but there may be some nuances in different distributions, let us take a closer look at them.
Note for UEFI: If you use UEFI instead of GRUB, then also see this article, it tells you how to change kernel boot parameters in this case.
By the way: if you want to protect the system from changing the password as described in this article, see the article “How to protect GRUB bootloader with password”.
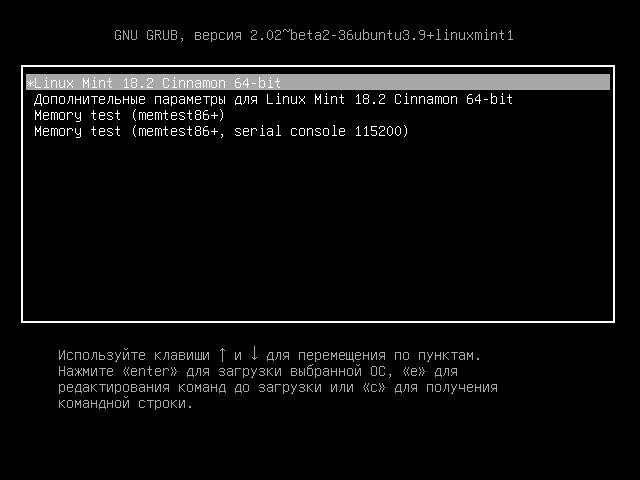
Resetting the password in Linux Mint, Ubuntu, Debian, Kali Linux (should also work for other Debian derivatives)
To interrupt the loading of GRUB (the first step) during startup of the computer, press and hold the SHIFT key — it works always, even on Linux Mint, where by default the GRUB menu display is disabled.
Stop the booting by holding the SHIFT key while starting the computer, you will see:
Press the «e» key and you will proceed to edit the boot settings:
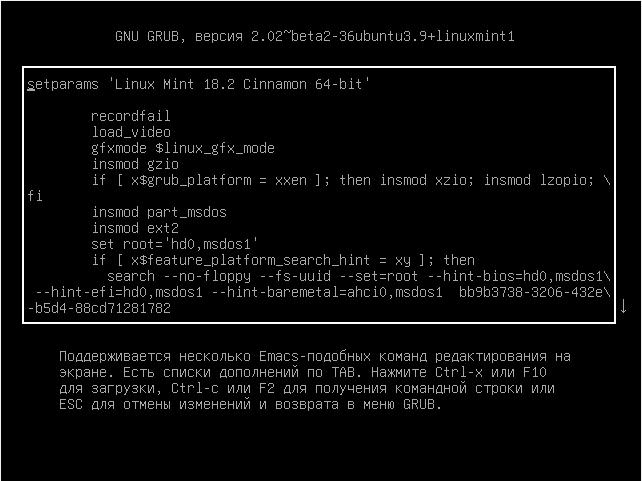
On the screen there is no necessary line for us, swipe the cursor keys down and find the line starting with linux:
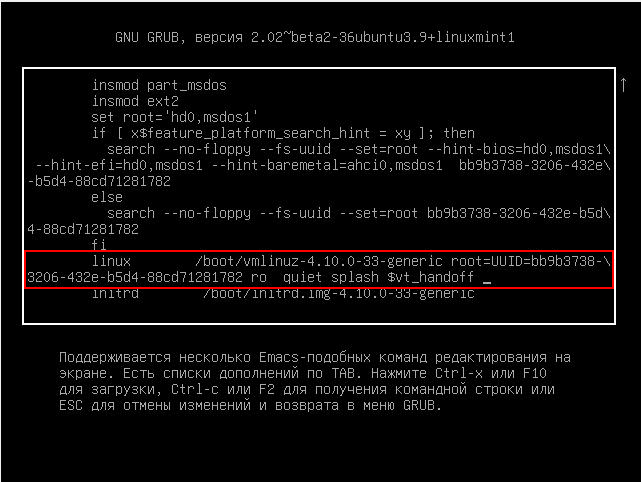
Go to the end of this line, type a space and add:
It should look something like this (the kernel number may differ):
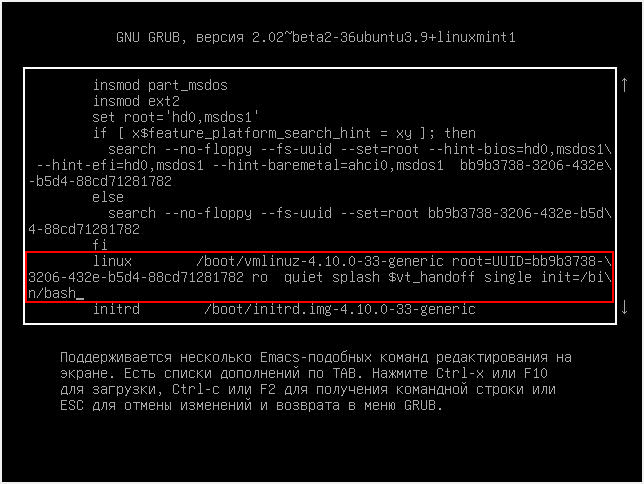
When everything is ready, press Ctrl+x or F10 to continue booting with the set options.
You will see a shell prompt, also note that we are logged in as root, i.e. we have superuser privileges, including the use of the passwd command:

With the passwd command we change the password, as you can see, the passwd command failed:
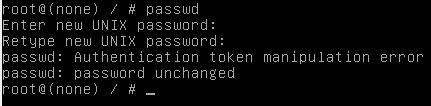
To understand the cause of the error, enter the command:

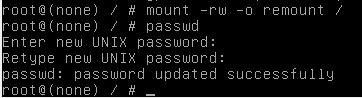
The letters ro indicate that the file system is mounted read-only and for this reason the made changes cannot be saved. Let us remount the file system:
As you can see, after that the password change was successful:
To turn off your computer run:
Or restart your computer with the command:
How to reset the password in Arch Linux, BlackArch (and also in other Arch Linux derivatives)
When the GRUB menu appears, press the «a» key to stop the booting:
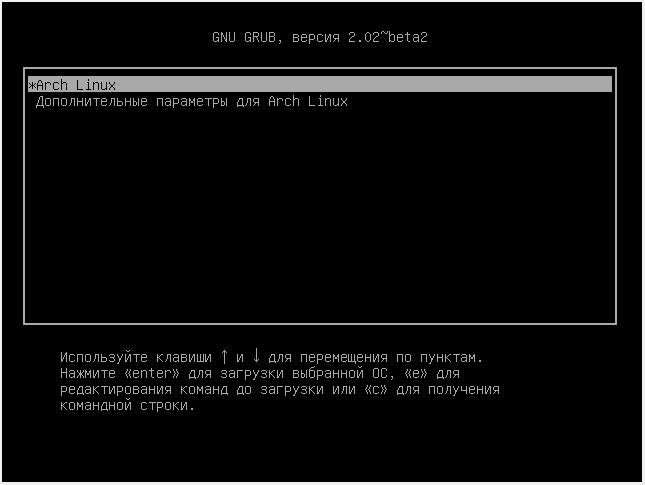
Then press «e» to edit the boot parameters:
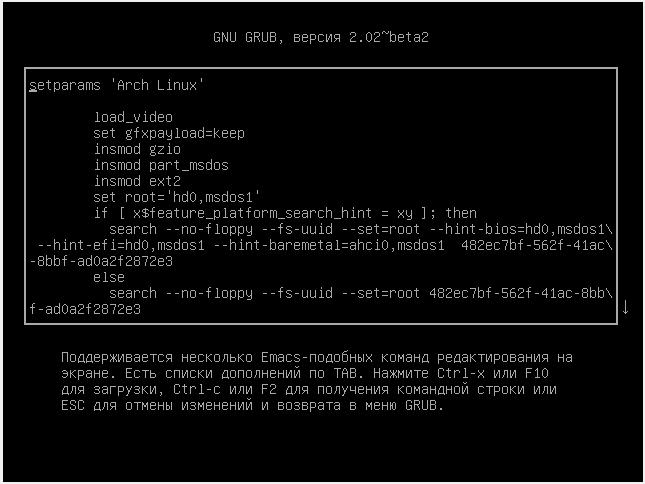
On the screen there is no interesting line for us, swipe the cursor keys down and find the line starting with linux.
Go to the end of this line, type a space and add:
It should look something like this:
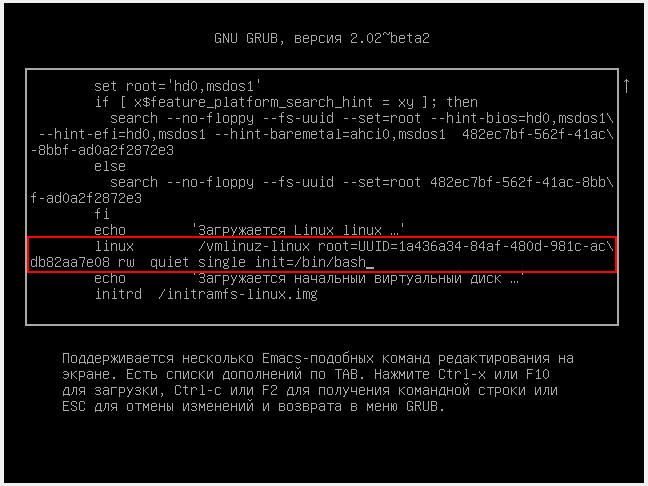
When everything is ready, press Ctrl+x or F10 to continue booting with the set options.
In Arch Linux, the file system is mounted with write permissions by default. Therefore, you can immediately change the password using the command
To turn off your computer run:
Or restart your computer with the command:
Reset your password in RHEL/CentOS 7
In addition to having to mount a file system for save changes, RHEL/CentOS 7 also has a nuance related to the presence of SELinux.
When the GRUB menu appears, press the «a» key to stop the booting:
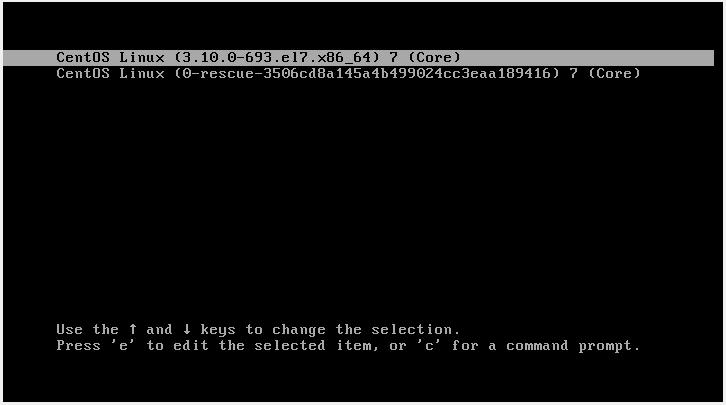
Then press «e» to edit the boot parameters:

On the screen is missing the line we need, swipe the cursor keys down and find the line starting with linux16:
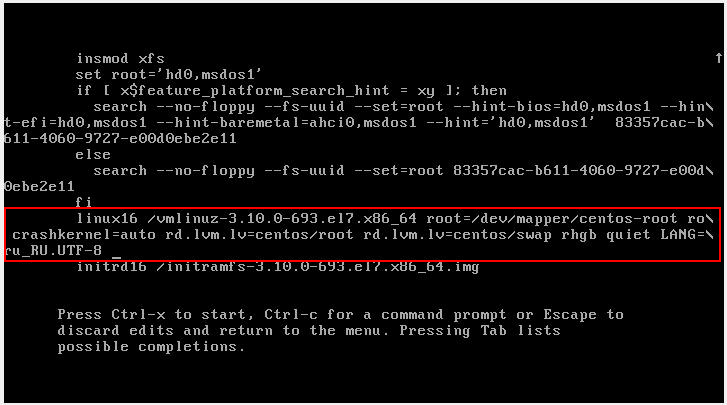
Find the part of the string
and replace with
It should look something like this:

When everything is ready, press Ctrl+x or F10 to continue booting with the set options.
Let us check write permissions:
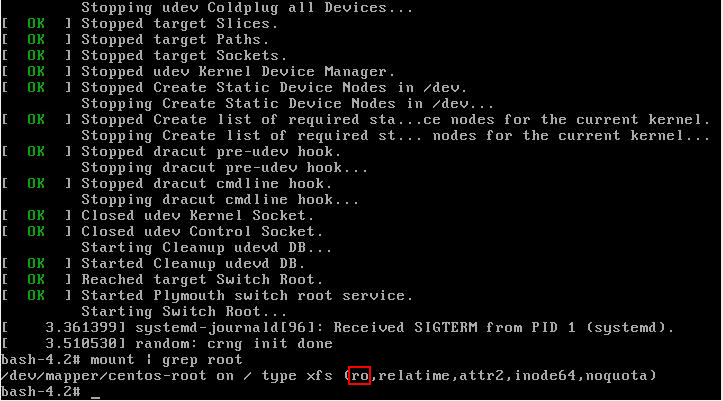
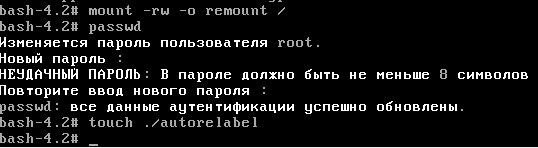
As you can see, there are no write permissions. We will remount the file system with write permissions:
The password has been changed, but it is not over yet. We need to relabel the SELinux context. If we do not relabel the whole SELinux context, we will not be able to use the new password. To do that:
To turn off your computer run:
Or restart your computer with the command:
In GRUB 2 one cannot change the password in single user mode?
In Red Hat official documentation, I found the statement that GRUB 2 no longer performs password reset in single-user mode, as it was in GRUB. And now for the operation in single-user mode, as well as in emergency mode, the root password is required. Perhaps this applies only to the latest versions of Red Hat Enterprise Linux, because, as you can see from this instruction and screenshots, in GRUB 2 you can change the password in single-user mode. The documentation describes two ways to reset the root password in Red Hat Enterprise Linux in case the described here method does not work.
Источник
Как сбросить пароль в Linux

Давайте рассмотрим несколько способов сбрасывания системного пароля в Linux. Вы наверное знаете, что у пользователя root есть права на изменение пароля любого пользователя в системе. А что если вы забыли пароль от рута? Вот об этом и пойдет речь в статье.
При восстановления пароля (рута или любого другого пользователя) встречаются две различные ситуации, требующие разного подхода.
Когда можно использовать GRUB
- После этого вы либо увидите приглашение для рута, либо восстанавливающее меню, где нужно выбрать строку с рутом. Используйте passwd для того чтобы изменить пароль у любого пользователя
Также следует заметить что некоторые дистрибутивы создают режим восстановления во время установки. Если в вашем меню GRUB есть такой пункт, вам не нужно производить все вышеперечисленные действия, просто выберите режим восстановления, а затем приглашение для рута, в последующем диалоговом окне.
Когда нет возможности использовать GRUB
Если вы не используете GRUB по каким-то причинам, вы можете восстановить пароль с помощью live CD (Я буду использовать Ubuntu live CD, вы можете взять любой другой). Просто следуйте дальнейшим инструкциям:
- Загрузитесь с live CD
- Выберите «Попробовать Ubuntu без изменений на вашем компьютере» (Try Ubuntu without any changes to your computer)
Далее нам нужно монтировать линукс-раздел. Для этого создайте папку, в качестве точки для монтирования, используя команду: sudo mkdir /media/linx_part
Примонтируйте линукс-раздел командой sudo mount /dev/sda1 /media/linx_part
Источник
9 Linux account password policies explained
Published: December 29, 2016 | Modified: June 20, 2020
Learn 9 different account password policies in Linux. Understand how to view them, how to change them and what is their impact on user management.
User management is one of the important aspects of Linux system administration. Restricting unauthorized access to systems can be prohibited by implementing strong password policies on accounts. That’s why this is a mandatory task in system hardening.
In this post, we will be seeing below nine different password policies that can be implemented in Linux.
- Password Max days
- Password Min days
- Password warning days
- Password history depth
- Password minimum length
- Minimum upper case characters
- Minimum lower case characters
- Minimum digits in password
- Wrong password retry
In the above list first 3 parameters are password aging-related whereas rest decides password strength.
1. Password Max days
This parameter decides how many days the maximum a password can be used. Once account password ages for these many days, it’s mandatory for the user to change his/her account password. This forbids users from using the same password for a long duration. In short, this is a maximum number of days password is valid on the system. This value can be set under file /etc/login.defs against parameter PASS_MAX_DAYS as shown below:
File parameter values affect only newly created accounts after the file has been edited. But for existing accounts, you need to change this value manually by using chage command with -M option. You can check the current set value by using -l option.
Observe in the above example, max days for an existing account have been changed from 30 to 45 days using chage command.
2. Password min days
These attributes control a minimum number of days before a password can be changed. This forbids users from changing passwords too frequently. For example, if this parameter is set to 7 days & user changed password today. Then he will be able to change it again only after 7 days from now. This value can be set under file /etc/login.defs against parameter PASS_MIN_DAYS as shown below:
File parameter values affect only newly created accounts after the file has been edited. But for existing accounts, you need to change this value manually by using chage command with -M option.
3. Password warning days
This attribute controls a number of days before the password expires, the user starts seeing a warning about password change after login. This gives sysadmins a chance to educate and made aware of their system users about password expiry. So that users can change their password well before its expiry time. This is not really adding any security to the system but helping users to avoid unwanted service impacts due to password expiry. Its value can be defined under /etc/login.defs file against PASS_WARN_AGE parameter.
Same as the last two parameters, this file parameter values affect only newly created accounts after the file has been edited. But for existing accounts, you need to change this value manually by using chage command with -W option.
4. Password history depth
When the user sets a new password, it will be checked against historical passwords. If the user tries to set the same old password then the system will forbid the user to use that password. This password history depth is defined by this attribute. If it is set to 3 then the user won’t be able to use any password which matches his last 3 passwords used.
This depth can be set in /etc/pam.d/system-auth file against the remember parameter.
In the above example, the last 2 passwords will be kept in history to check against the new one since remember is set to 2.
5. Password minimum length
Minimum characters needed in the password are defined by this attribute. This ensures the enforcement of strong passwords to be used by users. It can be defined in /etc/pam.d/system-auth file against minlen parameter.
This will be used whenever a new password is being set.
6. Minimum upper case characters
Another password strengthening attribute like the previous one. This ensures the enforcement of the use of uppercase characters in the password. It can be defined in /etc/pam.d/system-auth file against ucredit parameter.
Example in point 5.
7. Minimum lower case characters
This ensures the enforcement of the use of lowercase characters in the password. It can be defined in /etc/pam.d/system-auth file against lcredit parameter.
Example in point 5.
8. Minimum digits in password
This ensures the enforcement of the use of digits in passwords. It can be defined in /etc/pam.d/system-auth file against dcredit parameter.
Example in point 5.
9. Wrong password retry
This is a number of tries users get to try passwords without locking the account. As universally accepted, this is always set to be 3. Its value can be defined in retry parameter in /etc/pam.d/system-auth file.
Example in point 5.
Please make a note that all the above configurations files are taken into account from the RHEL flavor. If you have any questions, queries, suggestions, corrections please let us know in comments.
Источник