- Configure browsers to use Windows Integrated Authentication (WIA) with AD FS
- View WIASupportedUserAgent settings
- Change WIASupportedUserAgent settings
- Встроенная проверка подлинности Windows Integrated Windows Authentication
- Windows Authentication
- Overview
- New in IIS 7.5
- Compatibility
- Setup
- Windows Server 2012 or Windows Server 2012 R2
- Windows 8 or Windows 8.1
- Windows Server 2008 or Windows Server 2008 R2
- Windows Vista or Windows 7
- How To
- How to enable Windows authentication for a Web site, Web application, or Web service
- How to enable Extended Protection for Windows authentication
- Configuration
- Attributes
- Child Elements
- Configuration Sample
- Sample Code
Configure browsers to use Windows Integrated Authentication (WIA) with AD FS
By default, Windows Integrated Authentication (WIA) is enabled in Active Directory Federation Services (AD FS) in Windows Server 2012 R2 for authentication requests that occur within the organization’s internal network (intranet) for any application that uses a browser for its authentication.
AD FS 2016 now has an improved default setting that enables the Edge browser to do WIA while not also (incorrectly) catching Windows Phone as well:
The above means you no longer have to configure individual user agent strings to support common Edge scenarios, even though they are updated quite often.
For other browsers, configure the AD FS property WiaSupportedUserAgents to add the required values based on the browsers you are using. You can use the procedures below.
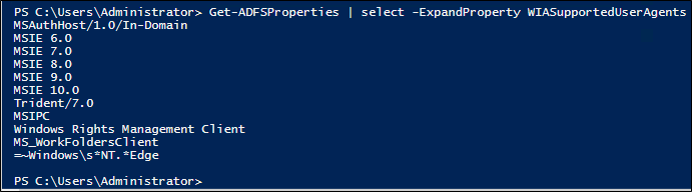
View WIASupportedUserAgent settings
The WIASupportedUserAgents defines the user agents which support WIA. AD FS analyzes the user agent string when performing logins in a browser or browser control.
You can view the current settings using the following PowerShell example:
Change WIASupportedUserAgent settings
By default, a new AD FS installation has a set of user agent string matches created. However, these may be out of date based on changes to browsers and devices. Particularly, Windows devices have similar user agent strings with minor variations in the tokens. The following Windows PowerShell example provides the best guidance for the current set of devices that are on the market today that support seamless WIA:
If you have AD FS on Windows Server 2012 R2 or earlier:
If you have AD FS on Windows Server 2016 or later:
The command above will ensure that AD FS only covers the following use cases for WIA:
Встроенная проверка подлинности Windows Integrated Windows Authentication
Встроенная проверка подлинности Windows позволяет пользователям выполнять вход с использованием учетных данных Windows, используя Kerberos или NTLM. Integrated Windows authentication enables users to log in with their Windows credentials, using Kerberos or NTLM. Клиент отправляет учетные данные в заголовке авторизации. The client sends credentials in the Authorization header. Проверка подлинности Windows наилучшим образом подходит для среды интрасети. Windows authentication is best suited for an intranet environment. Дополнительные сведения: Проверка подлинности Windows. For more information, see Windows Authentication.
| Преимущества Advantages | Недостатки Disadvantages |
|---|---|
| Встроенные в IIS. Built into IIS. | Не рекомендуется для Интернет приложений. Not recommended for Internet applications. |
| Не отправляет учетные данные пользователя в запросе. Does not send the user credentials in the request. | Требует поддержки Kerberos или NTLM в клиенте. Requires Kerberos or NTLM support in the client. |
| Если клиентский компьютер принадлежит к домену (например, к приложению интрасети), пользователю не нужно вводить учетные данные. If the client computer belongs to the domain (for example, intranet application), the user does not need to enter credentials. | Клиент должен находиться в домене Active Directory. Client must be in the Active Directory domain. |
Если ваше приложение размещено в Azure и имеется локальный домен Active Directory, рассмотрите возможность Федерации локального AD с Azure Active Directory. If your application is hosted on Azure and you have an on-premise Active Directory domain, consider federating your on-premise AD with Azure Active Directory. Таким образом пользователи смогут входить с использованием локальных учетных данных, но проверка подлинности выполняется Azure AD. That way, users can log in with their on-premise credentials, but the authentication is performed by Azure AD. Дополнительные сведения см. в статье Проверка подлинности Azure. For more information, see Azure Authentication.
Чтобы создать приложение, использующее встроенную проверку подлинности Windows, выберите шаблон «приложение интрасети» в мастере проектов MVC 4. To create an application that uses Integrated Windows authentication, select the «Intranet Application» template in the MVC 4 project wizard. Этот шаблон проекта помещает в файл Web.config следующий параметр: This project template puts the following setting in the Web.config file:
На стороне клиента встроенная проверка подлинности Windows работает с любым браузером, поддерживающим схему проверки подлинности Negotiate , которая включает большинство основных браузеров. On the client side, Integrated Windows authentication works with any browser that supports the Negotiate authentication scheme, which includes most major browsers. Для клиентских приложений .NET класс HttpClient поддерживает проверку подлинности Windows: For .NET client applications, the HttpClient class supports Windows authentication:
Проверка подлинности Windows уязвима для атак с подделкой межсайтовых запросов (CSRF). Windows authentication is vulnerable to cross-site request forgery (CSRF) attacks. См. раздел предотвращение атак с подделкой межсайтовых запросов (CSRF). See Preventing Cross-Site Request Forgery (CSRF) Attacks.
Windows Authentication
Overview
The element defines configuration settings for the Internet Information Services (IIS) 7 Windows authentication module. You can use Windows authentication when your IIS 7 server runs on a corporate network that is using Microsoft Active Directory service domain identities or other Windows accounts to identify users. Because of this, you can use Windows authentication whether or not your server is a member of an Active Directory domain.
Windows authentication (formerly named NTLM, and also referred to as Windows NT Challenge/Response authentication) is a secure form of authentication because the user name and password are hashed before being sent across the network. When you enable Windows authentication, the client browser sends a strongly hashed version of the password in a cryptographic exchange with your Web server.
Windows authentication supports two authentication protocols, Kerberos and NTLM, which are defined in the
element. When you install and enable Windows authentication on IIS 7, the default protocol is Kerberos. The element can also contain a useKernelMode attribute that configures whether to use the kernel mode authentication feature that is new to Windows Server 2008.
Windows authentication is best suited for an intranet environment for the following reasons:
- Client computers and Web servers are in the same domain.
- Administrators can make sure that every client browser is Internet Explorer 2.0 or later.
- HTTP proxy connections, which are not supported by NTLM, are not required.
- Kerberos version 5 requires a connection to Active Directory, which is not feasible in an Internet environment.
New in IIS 7.5
The element was introduced in IIS 7.5, which allows you to configure the settings for the new extended protection features that have been integrated into Windows authentication.
Compatibility
| Version | Notes |
|---|---|
| IIS 10.0 | The element was not modified in IIS 10.0. |
| IIS 8.5 | The element was not modified in IIS 8.5. |
| IIS 8.0 | The element was not modified in IIS 8.0. |
| IIS 7.5 | The element was added in IIS 7.5. |
| IIS 7.0 | The element was introduced in IIS 7.0. |
| IIS 6.0 | The element replaces portions of the IIS 6.0 AuthType and AuthFlags metabase properties. |
Setup
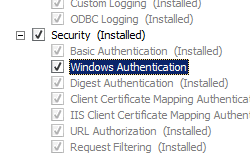
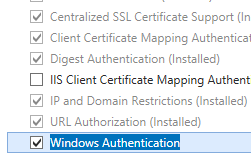
The default installation of IIS 7 and later does not include the Windows authentication role service. To use Windows authentication on IIS, you must install the role service, disable Anonymous authentication for your Web site or application, and then enable Windows authentication for the site or application.
After you install the role service, IIS 7 commits the following configuration settings to the ApplicationHost.config file.
Windows Server 2012 or Windows Server 2012 R2
- On the taskbar, click Server Manager.
- In Server Manager, click the Manage menu, and then click Add Roles and Features.
- In the Add Roles and Features wizard, click Next. Select the installation type and click Next. Select the destination server and click Next.
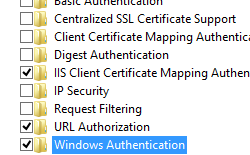
- On the Server Roles page, expand Web Server (IIS), expand Web Server, expand Security, and then select Windows Authentication. Click Next.
.
- On the Select features page, click Next.
- On the Confirm installation selections page, click Install.
- On the Results page, click Close.
Windows 8 or Windows 8.1
- On the Start screen, move the pointer all the way to the lower left corner, right-click the Start button, and then click Control Panel.
- In Control Panel, click Programs and Features, and then click Turn Windows features on or off.
- Expand Internet Information Services, expand World Wide Web Services, expand Security, and then select Windows Authentication.
- Click OK.
- Click Close.
Windows Server 2008 or Windows Server 2008 R2
- On the taskbar, click Start, point to Administrative Tools, and then click Server Manager.
- In the Server Manager hierarchy pane, expand Roles, and then click Web Server (IIS).
- In the Web Server (IIS) pane, scroll to the Role Services section, and then click Add Role Services.
- On the Select Role Services page of the Add Role Services Wizard, select Windows Authentication, and then click Next.
- On the Confirm Installation Selections page, click Install.
- On the Results page, click Close.
Windows Vista or Windows 7
- On the taskbar, click Start, and then click Control Panel.
- In Control Panel, click Programs and Features, and then click Turn Windows Features on or off.
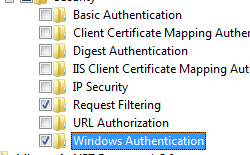
- Expand Internet Information Services, then World Wide Web Services, then Security.
- Select Windows Authentication, and then click OK.
How To
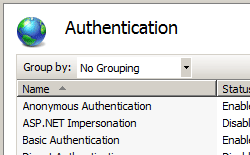
How to enable Windows authentication for a Web site, Web application, or Web service
Open Internet Information Services (IIS) Manager:
If you are using Windows Server 2012 or Windows Server 2012 R2:
- On the taskbar, click Server Manager, click Tools, and then click Internet Information Services (IIS) Manager.
If you are using Windows 8 or Windows 8.1:
- Hold down the Windows key, press the letter X, and then click Control Panel.
- Click Administrative Tools, and then double-click Internet Information Services (IIS) Manager.
If you are using Windows Server 2008 or Windows Server 2008 R2:
- On the taskbar, click Start, point to Administrative Tools, and then click Internet Information Services (IIS) Manager.
If you are using Windows Vista or Windows 7:
- On the taskbar, click Start, and then click Control Panel.
- Double-click Administrative Tools, and then double-click Internet Information Services (IIS) Manager.
In the Connections pane, expand the server name, expand Sites, and then the site, application, or Web service for which you want to enable Windows authentication.
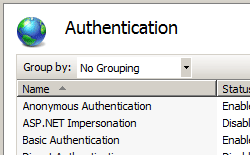
Scroll to the Security section in the Home pane, and then double-click Authentication.
In the Authentication pane, select Windows Authentication, and then click Enable in the Actions pane.
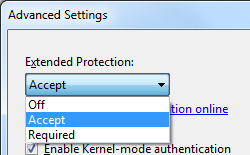
How to enable Extended Protection for Windows authentication
Open Internet Information Services (IIS) Manager:
If you are using Windows Server 2012 or Windows Server 2012 R2:
- On the taskbar, click Server Manager, click Tools, and then click Internet Information Services (IIS) Manager.
If you are using Windows 8 or Windows 8.1:
- Hold down the Windows key, press the letter X, and then click Control Panel.
- Click Administrative Tools, and then double-click Internet Information Services (IIS) Manager.
If you are using Windows Server 2008 or Windows Server 2008 R2:
- On the taskbar, click Start, point to Administrative Tools, and then click Internet Information Services (IIS) Manager.
If you are using Windows Vista or Windows 7:
- On the taskbar, click Start, and then click Control Panel.
- Double-click Administrative Tools, and then double-click Internet Information Services (IIS) Manager.
In the Connections pane, expand the server name, expand Sites, and then the site, application, or Web service for which you want to enable Extended Protection for Windows authentication.
Scroll to the Security section in the Home pane, and then double-click Authentication.
In the Authentication pane, select Windows Authentication.
Click Enable in the Actions pane.
Click Advanced Settings in the Actions pane.
When the Advanced Settings dialog box appears, select one of the following options in the Extended Protection drop-down menu:
- Select Accept if you want to enable extended protection while providing down-level support for clients that do not support extended protection.
- Select Required if you want to enable extended protection without providing down-level support.
Click OK to close the Advanced Settings dialog box.
Configuration
The element is configurable at the site, application, or virtual directory level in the ApplicationHost.config file.
Attributes
| Attribute | Description |
|---|---|
| authPersistNonNTLM | Optional Boolean attribute. |
Specifies whether IIS automatically reauthenticates every non-NTLM (for example, Kerberos) request, even those on the same connection. False enables multiple authentications for the same connections.
Note: A setting of true means that the client will be authenticated only once on the same connection. IIS will cache a token or ticket on the server for a TCP session that stays established.
The default is false .
Setting this flag to true specifies that authentication persists only for a single request on a connection. IIS resets the authentication at the end of each request, and forces reauthentication on the next request of the session.
The default value is false .
Specifies whether Windows authentication is enabled.
The default value is false .
Specifies whether Windows authentication is done in kernel mode. True specifies that Windows authentication uses kernel mode.
Kernel-mode authentication may improve authentication performance and prevent authentication problems with application pools that are configured to use a custom identity.
As a best practice, do not disable this setting if you use Kerberos authentication and have a custom identity on the application pool.
The default is true .
Child Elements
| Element | Description |
|---|---|
| extendedProtection | Optional element. |
Specifies extended protection options for Windows authentication.
Note: This element was added in IIS 7.5.
Specifies security support providers used for Windows authentication.
Configuration Sample
The following default element is configured at the root ApplicationHost.config file in IIS 7.0, and disables Windows authentication by default. It also defines the two Windows authentication providers for IIS 7.0.
The following example enables Windows authentication and disables Anonymous authentication for a Web site named Contoso.
Sample Code
The following examples disable Anonymous authentication for a site named Contoso, then enable Windows authentication for the site.
 .
.