4627(S): Group membership information.
Applies to
- Windows 10
- Windows Server 2016
Event Description:
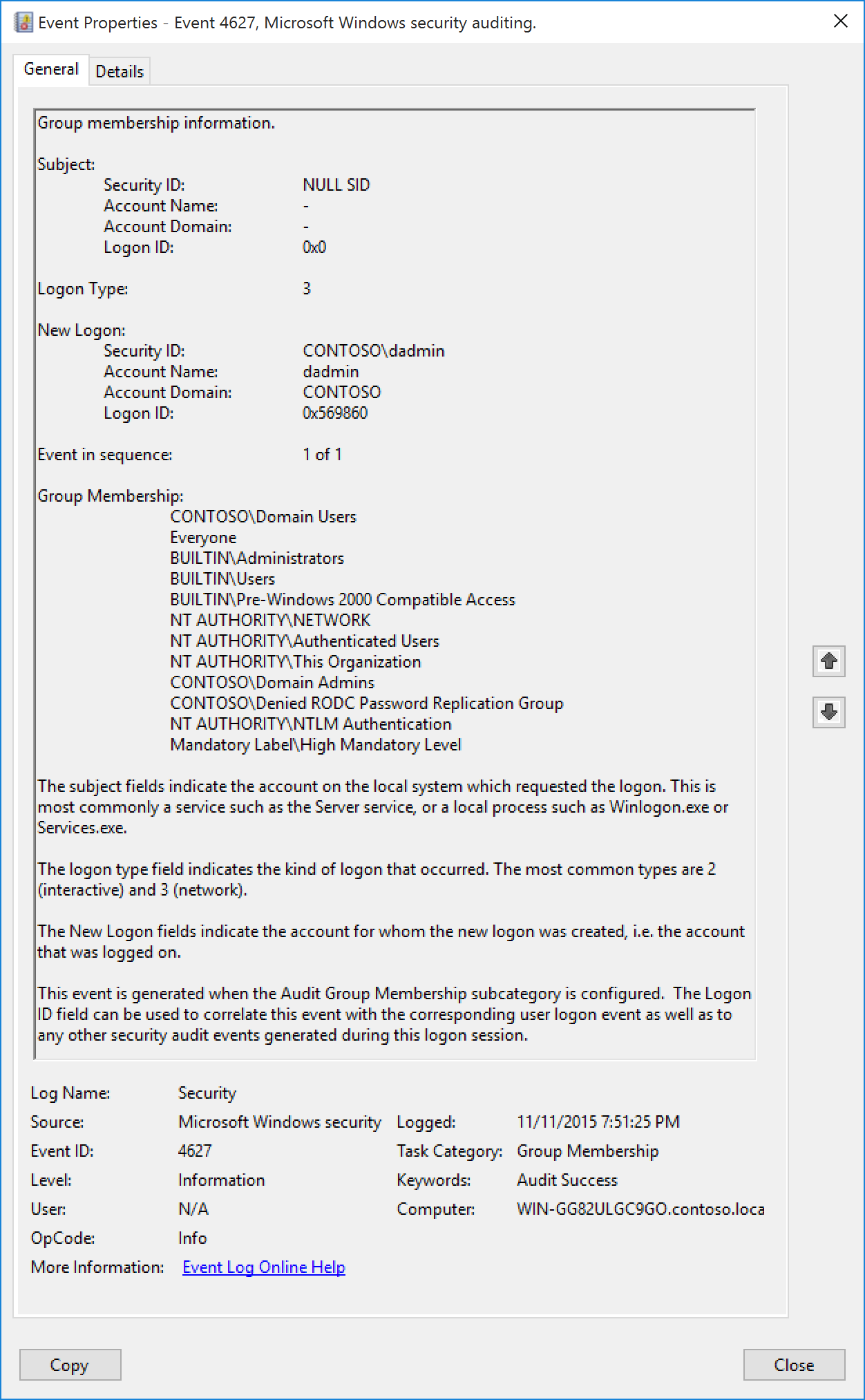
This event generates with “4624(S): An account was successfully logged on” and shows the list of groups that the logged-on account belongs to.
You must also enable the Success audit for Audit Logon subcategory to get this event.
Multiple events are generated if the group membership information cannot fit in a single security audit event.
NoteВ В For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
Required Server Roles: None.
Minimum OS Version: Windows Server 2016, Windows 10.
Event Versions: 0.
Field Descriptions:
Subject:
- Security ID [Type = SID]: SID of account that reported information about successful logon or invokes it. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
NoteВ В A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account that reported information about successful logon or invokes it.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4672(S): Special privileges assigned to new logon.”
Logon Type [Type = UInt32]: the type of logon which was performed. The table below contains the list of possible values for this field:
| Logon Type | Logon Title | Description |
|---|---|---|
| 2 | Interactive | A user logged on to this computer. |
| 3 | Network | A user or computer logged on to this computer from the network. |
| 4 | Batch | Batch logon type is used by batch servers, where processes may be executing on behalf of a user without their direct intervention. |
| 5 | Service | A service was started by the Service Control Manager. |
| 7 | Unlock | This workstation was unlocked. |
| 8 | NetworkCleartext | A user logged on to this computer from the network. The user’s password was passed to the authentication package in its unhashed form. The built-in authentication packages all hash credentials before sending them across the network. The credentials do not traverse the network in plaintext (also called cleartext). |
| 9 | NewCredentials | A caller cloned its current token and specified new credentials for outbound connections. The new logon session has the same local identity, but uses different credentials for other network connections. |
| 10 | RemoteInteractive | A user logged on to this computer remotely using Terminal Services or Remote Desktop. |
| 11 | CachedInteractive | A user logged on to this computer with network credentials that were stored locally on the computer. The domain controller was not contacted to verify the credentials. |
New Logon:
- Security ID [Type = SID]: SID of account for which logon was performed. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
NoteВ В A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account for which logon was performed.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4672(S): Special privileges assigned to new logon.”
Event in sequence [Type = UInt32]: If is there is not enough space in one event to put all groups, you will see “1 of N” in this field and additional events will be generated. Typically this field has “1 of 1” value.
Group Membership [Type = UnicodeString]: the list of group SIDs which logged account belongs to (member of). Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
4647(S): пользователь инициировал выйдите из сети. 4647(S): User initiated logoff.
Область применения Applies to
- Windows 10 Windows 10
- Windows Server2016 Windows Server 2016
* Описание события: Event Description: *
Это событие создается при инициировании выйдите из нее. This event is generated when a logoff is initiated. Дальнейшие действия, инициированные пользователем, не могут быть инициированы пользователем. No further user-initiated activity can occur. Это событие можно интерпретировать как событие выйдите из систему. This event can be interpreted as a logoff event.
Основное различие между»4634(S): учетная запись была отключена». The main difference with “4634(S): An account was logged off.” событие 4647 создается при инициации процедуры выйдите из системы определенной учетной записью с помощью функции выйдите из системы, а событие 4634 показывает, что сеанс был завершен и больше не существует. event is that 4647 event is generated when logoff procedure was initiated by specific account using logoff function, and 4634 event shows that session was terminated and no longer exists.
4647 является более типичным для типов входа _Interactive* и RemoteInteractive, когда пользователь вышел из системы с помощью стандартных методов. 4647 is more typical for _Interactive* and RemoteInteractive logon types when user was logged off using standard methods. Как правило, события 4647 и 4634 можно увидеть, процедура выхода инициирована пользователем. You will typically see both 4647 and 4634 events when logoff procedure was initiated by user.
Это может быть однозначно связано с событием «4624: учетная запись успешно выполнила вход в систему.» It may be positively correlated with a “4624: An account was successfully logged on.” с помощью значения ID входа. event using the Logon ID value. Идентификаторы входа являются уникальными только между перезагрузками одного компьютера. Logon IDs are only unique between reboots on the same computer.
Примечание. Рекомендации приведены в разделе Рекомендации по мониторингу безопасности для этого события. Note For recommendations, see Security Monitoring Recommendations for this event.
*Обязательные роли сервера:* нет. Required Server Roles: None.
*Минимальная версия ОС:* Windows Server 2008, Windows Vista. Minimum OS Version: Windows Server 2008, Windows Vista.
* Описания полей: Field Descriptions: *
- Security ID [Type = SID]: SID учетной записи, запросив операцию «logoff». Security ID [Type = SID]: SID of account that requested the “logoff” operation. Средство просмотра событий автоматически пытается разрешить идентификатор безопасности SID и отобразить имя учетной записи. Event Viewer automatically tries to resolve SIDs and show the account name. Если идентификатор безопасности разрешить не удается, в событии будут отображены исходные данные. If the SID cannot be resolved, you will see the source data in the event.
Примечание. . Идентификатор безопасности (SID) представляет собой строковое значение переменной длины, которое используется для идентификации доверенного лица (субъекта безопасности). Note A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Каждая учетная запись имеет уникальный идентификатор безопасности, выданный центром сертификации, таким как контроллер домена Active Directory, который хранится в базе данных безопасности. Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Каждый раз, когда пользователь входит в систему, система получает идентификатор безопасности этого пользователя из базы данных и помещает ее в маркер доступа этого пользователя. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. Система использует идентификатор безопасности в маркере доступа для идентификации пользователя во всех последующих операциях с Безопасностью Windows. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. Если идентификатор SID использовался как уникальный идентификатор для пользователя или группы, он не может использоваться повторно для идентификации другого пользователя или группы. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. Дополнительные сведения о SID см. в разделе Идентификаторы безопасности. For more information about SIDs, see Security identifiers.
Имя учетной записи [Type = UnicodeString]— имя учетной записи, которая запросила операцию «logoff». Account Name [Type = UnicodeString]: the name of the account that requested the “logoff” operation.
Account Domain [Type = UnicodeString]: домен субъекта или имя компьютера. Account Domain [Type = UnicodeString]: subject’s domain or computer name. Форматы различаются и включают в себя следующее: Formats vary, and include the following:
Пример имени домена NETBIOS: CONTOSO Domain NETBIOS name example: CONTOSO
Полное имя домена в нижнем регистре: contoso.local Lowercase full domain name: contoso.local
Полное имя домена в верхнем регистре: CONTOSO.LOCAL Uppercase full domain name: CONTOSO.LOCAL
Для некоторых известных субъектов безопасности, таких как LOCAL SERVICE или ANONYMOUS LOGON, значение этого поля равно «NT AUTHORITY». For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
Для учетных записей локальных пользователей это поле будет содержать имя компьютера или устройства, к которым принадлежит эта учетная запись, например: «Win81». For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: шестнадцатеричное значение, которое может помочь сопоставить это событие с недавними событиями содержащими тот же идентификатор входа, например: “4624: Учетная запись успешно вошла в систему.” Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4624: An account was successfully logged on.”
Рекомендации по контролю безопасности Security Monitoring Recommendations
Для 4647 (S): пользователь инициировал вход. For 4647(S): User initiated logoff.