- Oracle linux iptables stop
- Linux Firewall (iptables, system-config-firewall)
- Installation
- system-config-firewall
- system-config-firewall-tui
- iptables
- Quick Database Setup
- IT Knowledge Base
- How to stop/start and disable/enable firewall on Oracle Linux 7.
- How To Start, Stop and Enable, Disable Iptables or Ufw In Ubuntu, Debian, Kali, Mint
- Ufw or Ubuntu Firewall
- Install Ufw
- Install Iptables
- Remove, Uninstall Iptables
- ufw Help
- List Iptables/Ufw Service Status
- Start Iptables/Ufw Service
- Stop Iptables/Ufw Service
- Enable Iptables/Ufw Service
- Disable Iptables/Ufw Service
- Allow Port Or Service with ufw
- Allow Port Range
- Deny Port
- List Rules
- Delete Rules
- Check ufw Status
- Reset All Rules In ufw
- 4 thoughts on “How To Start, Stop and Enable, Disable Iptables or Ufw In Ubuntu, Debian, Kali, Mint”
Oracle linux iptables stop
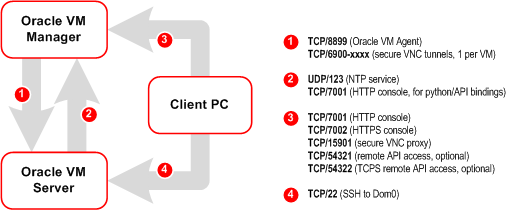
A default Oracle Linux install has the firewall enabled (iptables on). In order to use Oracle VM Manager on a system with iptables enabled you can either open all the ports used by Oracle VM Manager, or open all ports by disabling iptables.
The ports required for the web browser connection to Oracle VM Manager are: 7001, 7002 and 15901. The ports used by the Oracle VM Servers to connect to Oracle VM Manager are: 7001, 7002 and 54321. Oracle VM Manager, in turn, connects to the Oracle VM Servers through port 8899 for Oracle VM Agent communication, and port 6900 and up for secure VNC tunneling to virtual machines (one port per VM). Be sure to open the necessary ports on the different firewalls that may be installed between different parts of your network. Follow the guidelines of in the diagram below:
To disable iptables and open all ports, enter the following commands as the root user:
Alternatively, open the required ports by using the iptables command as the root user:
To remotely connect to the Oracle VM Manager core API, also enter the following command:
When all the ports have been opened, save the iptables configuration:
This does not require iptables to be restarted as the commands open the ports while iptables is running and the save ensures they are opened on reboot/restart in future.
To configure the firewall to open the required ports automatically, use the environment configuration script provided with the Oracle VM Manager installer. See Section 3.3.2.4, “Environment Configuration Script” for information on using this script.
| PrevВ | Up | В Next |
| 3.3.2.5.В Prerequisite PackagesВ | Home | В 3.3.2.7.В Installation Ports and Passwords |
Copyright В© 2011, 2012, Oracle and/or its affiliates. All rights reserved. Legal Notices
Источник
Linux Firewall (iptables, system-config-firewall)
This article covers basic Linux firewall management, with specific reference to the information needed for the RHCSA EX200 certification exam. Extra information is required for the RHCE EX300 certification exam, which will be supplied by another article.
Remember, the exams are hands-on, so it doesn’t matter which method you use to achieve the result, so long as the end product is correct.
Installation
Most installations will include the firewall functionality. If you need to manually install it, the following commands will install the IP4 and IP6 firewall functionality. In this article we will only consider the IP4 settings.
Make sure the service is started and will auto-start on reboot.
You can check the current status of the service using the following command.
To disable the firewall, run the following commands.
system-config-firewall
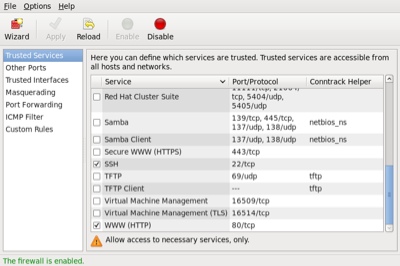
The GUI screen to control the firewall is available from the menu (System > Administration > Firewall) or can be started from the command line using the system-config-firewall command. If it is not already present, it can be installed using the following command.
Once started, the toolbar provides buttons to allow the firewall to be enabled/disabled. You can also configure basic trusted services, such as SSH, FTP and HTTP, by putting a tick in the appropriate checkbox and clicking the «Apply» button on the toolbar.
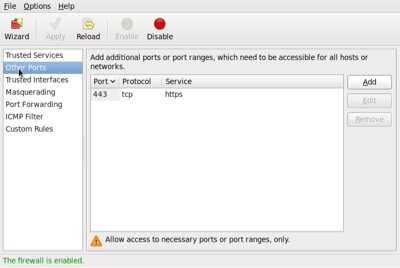
The «Other Ports» section allows you to open ports that are not covered in the «Trusted Services» section.
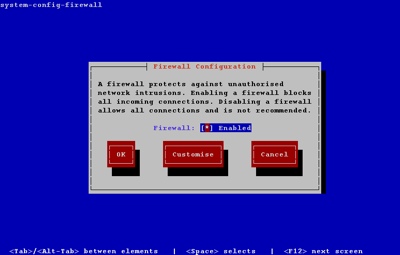
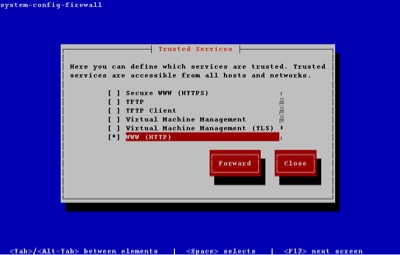
system-config-firewall-tui
The TUI utility is similar to the GUI utility shown above, but it feels incredibly clumsy in comparison. If it is not already present, it can be installed using the following command.
Running the system-config-firewall-tui command from the command line produces the top-level screen, allowing you to enable/disable the firewall. Use the space bar to toggle the setting, the tab key to navigate between buttons and the return key to click them.
To alter the Trusted Services, tab to the «Customize» button and press the return key. Amend the list using the arrow and space keys.
You can close out of the customization section at any point. The other sections of the GUI tool are available by clicking the «Forward» button on each successive screen.
iptables
In addition to the GUI and TUI interfaces, the firewall rules can be amended directly using the iptables command. There are vast number of parameters, so I will just focus on the elements necessary for the RHCSA exam.
The firewall consists of chains of rules that determine what action should be taken for packets processed by the system. By default, there are three chains defined:
- INPUT : Used to check all packets coming into the system.
- OUPUT : Used to check all packets leaving the system.
- FORWARD : Used to check all packets being routed by the system. Unless you are using your server as a router, this chain is unnecessary.
Each chain can contain multiple explicit rules that are checked in order. If a rule matches, the associated action ( ACCEPT and DROP being the most common) is taken. If no specific rule is found, the default policy is used to determine the action to take.
Since the default policy is a catch-all, one of two basic methods can be chosen for each chain.
- Set the default policy to ACCEPT and explicitly DROP things you don’t want.
- Set the default policy to DROP and explicitly ACCEPT things you do want.
The safest option is to set the default policy to DROP for the INPUT and FORWARD chains, so it is perhaps a little surprising that the GUI and TUI tools set the default policies to ACCEPT , then use an explicit REJECT as the last rule in these chains.
This works fine, but if you accidentally get rid of the last rule in the chain you are in trouble. For this reason, for the remainder of this section I will assume that the default policy for INPUT and FORWARD is DROP . For the OUTPUT chain I will assume any packets originating from the system are safe, so I will ACCEPT any outgoing packets.
The default policy for a chain is set using the «-P» flag. In the following example, assuming no specific rules were present, all communication to and from the server would be prevented.
Warning: If you are administering the firewall via SSH, having a default INPUT policy of DROP will cut your session off if you get rid of the explicit rules that accept SSH access. As a result, it makes sense to start any administration by setting the default policies to ACCEPT and only switch them back to DROP once the chains have been built to your satisfaction. The following example temporarily sets the default policies to ACCEPT .
The next thing we want to do if flush any existing rules, leaving just the default policies. This is done using the «-F» flag.
Now we need to define specific rules for the type of access we want the server to have. Focusing on the INPUT chain, we can grant access to packets in a number of ways.
Once the explicit rules are defined, we need to set the real default policies.
Rule and policy definitions take effect immediately.To make sure they persists beyond reboot the current configuration must be saved to the «/etc/sysconfig/iptables» file using the following command.
If you are using Fedora, you may need to use the following command instead.
As you can imagine, even in a simple configuration this process can get a bit long-winded, so it makes sense to combine all the elements of the firewall definition into a single file so it can be amended and run repeatedly. Create a file called «/root/firewall.sh» with the following contents. Think of this as your starting point for each server.
Make the file executable.
Run the file to set the required firewall rules.
The iptables command also allows you to insert (-I), delete (-D) and replace (-R) rules, but if you work using a file as described above, you never need to use these variations.
Quick Database Setup
If you are using the server as an Oracle database server, you will probably want to make sure the SSH and Oracle listener ports are accessible. You could lock these down to specific source IP addresses, but for a quick setup, you could just do the following, where «1521» is the port used for the listener.
Источник
IT Knowledge Base
How to stop/start and disable/enable firewall on Oracle Linux 7.
Fedora 18 introduced firewalld as a replacement for the previous iptables service. Since RHEL7 and Oracle Linux 7 are based on Fedora 19, the switch from iptables service to firewalld is now part of the Enterprise Linux distributions.
The firewall on Oracle Linux 7 system is enabled by default. Normally there should not be a need to disable firewall but it may be quite handy for testing purposes etc. The firewall runs as firewalld daemon. Bellow command can be used to check the firewall status:
From the above output we can see that the firewall is enabled, which means it will start automatically after reboot and that is also current active. Furthermore, you can even check all currently applied rules with:
You need to distinguish between the iptables service and the iptables command. Although firewalld is a replacement for the firewall management provided by iptables service, it still uses the iptables command for dynamic communication with the kernel packet filter (netfilter). So it is only the iptables service that is replaced, not the iptables command. That can be a confusing distinction at first.
The firewall on Oracle Linux 7 system can be stopped by a following command:
Stopped firewall will start again after system’s reboot. To start firewall use the following command:
In order to completely disable OL7 firewall, so it would not start after reboot, run:
Now the firewall would not start after system’s reboot. To enable the firewall again run:
Источник
How To Start, Stop and Enable, Disable Iptables or Ufw In Ubuntu, Debian, Kali, Mint
Ubuntu is popular Linux distribution used in different enterprise or personal IT environment. Security is important part of the today IT. We can use firewall services like iptables in order to tighten security of our Ubuntu system. In this tutorial we will look how to install, remove, enable, disable, start and stop Ubuntu iptables. This tutorial can be used for Kali, Debian, Mint distributions too.
Ufw or Ubuntu Firewall
Ubuntu rebranded iptables as ufw or Ubuntu firewall in its distrbution. So we will use ufw for different operations according to iptables in this tutorial.
Install Ufw
We can install ufw package for Ubuntu, Debian, Mint and Kali like below.
Install Iptables
Actually iptables package and related tools are installed by default for Ubuntu, Kali, Debian and Mint. But if they are removed accidentally or intentionally we may need to install iptables with the following command. Most of the operations like iptables installation examined in this tutorial will require root privileges.
Remove, Uninstall Iptables
Or we may want to uninstall iptables package and related tools. I generally uninstall iptables in my kali systems because use cases do nor requires iptables .
ufw Help
We can get help about ufw command with -h option. This will list most common commands provided by ufw .

As we can there are commands and their summary descriptions. There is also Applications profiles.
List Iptables/Ufw Service Status
Now in order to manage iptables we should list the status of the service. We will use systemctl status command with ufw for Ubuntu and iptables for other distributions. As default behaivour ufw is enable by default in Ubuntu.
Start Iptables/Ufw Service
We can start ufw or iptables service in Ubuntu and related distributions by using systemctl start command like below.
OR we can use ufw command to start the related service like below.
Stop Iptables/Ufw Service
We can stop with the same command systemctl and stop option.
OR we can use command ufw to start the related service like below.
Enable Iptables/Ufw Service
Services may be enabled inorder to start after a reboot or fresh start. We can enable iptables ufw with the following commands.
Disable Iptables/Ufw Service
If we do not want to remove iptables or ufw but we do not want to start related services automatically at the system start we can disable related services with the following command.
Allow Port Or Service with ufw
ufw provides simple way to manage ports. We may need to allow some ports. We will use allow option. In this example we will allow TCP port 22 which is SSH default port.
We need to provide the tcp as protocol too.

We can also allow just providing the service or protocol name. Following command will also allow SSH port like above command.
Allow Port Range
In some cases, some applications or services may use multiple ports in a range. We may need to allow a given port range. We can use : in order to specify the range. For example 2000:3000 can be used to specify ports between 2000 and 3000 .
In this example we will allow ports between 2000 and 3000 .
Deny Port
The default policy or setup of the ufw is denying all ports. This is more secure way to setup and manage firewalls. During the management of the firewall we may enable some ports. After some time we may need to disable these enabled ports. We can use deny option in order to prevent traffic for given port. In this example we will deny TCP port 22.

List Rules
Over time some rules will be added to the ufw. In order to check, remove or update this rules we need to list them. We can list existing firewall tules with the status verbose options. In order to work this command ufw should be enabled and running.

As we see there are rules we have been added previously.
Delete Rules
In order to remove previously defined rules we need to delete them . Like addding new rule we just need to change allow with delete . In this example we will delete the TCP 22 or ssh rule. We should provide the allow or deny of the rule.

As we can see we delete the rule deny 22/tcp
Check ufw Status
We can check the status of the ufw with status option. Event the ufw service is running ufw may be disabled.

As we can see the line Status:active shows that the ufw is actively working.
Reset All Rules In ufw
If we want to remove all rules deleting or removing them one by one is very tedious task. We can remove all added rules with a single option named reset . Keep in mind that this will remove all rules and revert back to default configuration.

As we can see from screenshot it will ask us wheter we are sureto remove. Event we remove the rules they are saved automatically to the /etc/ufw/ directory with rules category and date by ufw.
4 thoughts on “How To Start, Stop and Enable, Disable Iptables or Ufw In Ubuntu, Debian, Kali, Mint”
FYI:
In the “Stop Iptables/Ufw Service” section, the code given is “systemctl start ufw” and “systemctl start iptables”, which obviously doesn’t stop the services.
Thanks for your suggestion. I have corrected the commands.
Have a nice day
Thanks for the sentences “Ubuntu is popular Linux distribution used in different enterprise or personal IT environment. Security is important part of the today IT. ” Even though I googled Kali Firewall, i would have been completely lost had you not included those at the beginning.
ufw does not stand for “Ubuntu Firewall.” It stands for “Uncomplicated Firewall.”
Источник