- BitLocker: использование средства просмотра пароля восстановления BitLocker BitLocker: Use BitLocker Recovery Password Viewer
- Прежде чем начать Before you start
- How to Reset Windows Password on BitLocker Encrypted Drive
- How to Reset Windows Password on BitLocker Encrypted Drive
- BitLocker recovery guide
- What is BitLocker recovery?
- What causes BitLocker recovery?
- Testing recovery
- Planning your recovery process
- Self-recovery
- Recovery password retrieval
- Record the name of the user’s computer
- Verify the user’s identity
- Locate the recovery password in ADВ DS
- Multiple recovery passwords
- Gather information to determine why recovery occurred
- Give the user the recovery password
- Post-recovery analysis
- Determine the root cause of the recovery
- Resolve the root cause
- Unknown PIN
- Lost startup key
- Changes to boot files
- Windows RE and BitLocker Device Encryption
- BitLocker recovery screen
- Custom recovery message
- BitLocker recovery key hints
- Example 1 (single recovery key with single backup)
- Example 2 (single recovery key with single backup)
- Example 3 (single recovery key with multiple backups)
- Example 4 (multiple recovery passwords)
- Example 5 (multiple recovery passwords)
- Using additional recovery information
- BitLocker key package
- Resetting recovery passwords
- Retrieving the BitLocker key package
BitLocker: использование средства просмотра пароля восстановления BitLocker BitLocker: Use BitLocker Recovery Password Viewer
Область применения Applies to
В этой статье, предназначенной для ИТ-специалистов, рассказывается, как использовать средство просмотра пароля восстановления в BitLocker. This topic for the IT professional describes how to use the BitLocker Recovery Password Viewer.
Средство просмотра паролей восстановления BitLocker является необязательным средством, включенным в средства удаленного администрирования сервера (RSAT). The BitLocker Recovery Password Viewer tool is an optional tool included with the Remote Server Administration Tools (RSAT). Он позволяет находить и просматривать пароли восстановления BitLocker, хранимые в доменных службах Active Directory (AD DS). It lets you locate and view BitLocker recovery passwords that are stored in Active Directory Domain Services (AD DS). С помощью этого средства можно восстанавливать данные на диске, зашифрованном с помощью BitLocker. You can use this tool to help recover data that is stored on a drive that has been encrypted by using BitLocker. Средство просмотра паролей восстановления BitLocker Active Directory является расширением оснастки «Пользователи и компьютеры Active Directory» консоли управления (MMC). The BitLocker Active Directory Recovery Password Viewer tool is an extension for the Active Directory Users and Computers Microsoft Management Console (MMC) snap-in. С помощью этого средства можно просмотреть **** диалоговое окно свойств объекта компьютера, чтобы просмотреть соответствующие пароли восстановления BitLocker. Using this tool, you can examine a computer object’s Properties dialog box to view the corresponding BitLocker recovery passwords. Кроме того, вы можете щелкнуть контейнер домена правой кнопкой мыши, а затем искать пароль восстановления BitLocker на всех доменах в лесу Active Directory. Additionally, you can right-click a domain container and then search for a BitLocker recovery password across all the domains in the Active Directory forest. Вы также можете найти пароль по идентификатору (ID). You can also search for a password by password identifier (ID).
Прежде чем начать Before you start
Чтобы выполнить процедуры в этом сценарии: To complete the procedures in this scenario:
- У вас должны быть учетные данные администратора домена. You must have domain administrator credentials.
- Тестовые компьютеры должны быть соединены с доменом. Your test computers must be joined to the domain.
- На тестовых компьютерах BitLocker должен быть включен после присоединения к домену. On the test computers, BitLocker must have been turned on after joining the domain.
В следующих процедурах описаны наиболее распространенные задачи, выполняемые с помощью просмотра паролей восстановления BitLocker. The following procedures describe the most common tasks performed by using the BitLocker Recovery Password Viewer.
Просмотр паролей восстановления для компьютера To view the recovery passwords for a computer
- В области «Пользователи и компьютеры Active Directory» найдите и щелкните контейнер, в котором расположен компьютер. In Active Directory Users and Computers, locate and then click the container in which the computer is located.
- Щелкните правой кнопкой мыши объект компьютера и выберите «Свойства». Right-click the computer object, and then click Properties.
- В диалоговом окне «Свойства» перейдите на вкладку «Восстановление BitLocker», чтобы просмотреть пароли восстановления BitLocker, связанные с компьютером. In the Properties dialog box, click the BitLocker Recovery tab to view the BitLocker recovery passwords that are associated with the computer.
Копирование паролей восстановления для компьютера To copy the recovery passwords for a computer
- Выполните действия, которые вы выполните в предыдущей процедуре, чтобы просмотреть пароли восстановления BitLocker. Follow the steps in the previous procedure to view the BitLocker recovery passwords.
- На вкладке «Восстановление BitLocker» в диалоговом окне «Свойства» щелкните правой кнопкой мыши пароль восстановления BitLocker, который нужно скопировать, и выберите «Скопировать сведения». On the BitLocker Recovery tab of the Properties dialog box, right-click the BitLocker recovery password that you want to copy, and then click Copy Details.
- Нажмите CTRL+V, чтобы в paste the copied text to a destination location, such as a text file or spreadsheet. Press CTRL+V to paste the copied text to a destination location, such as a text file or spreadsheet.
Поиск пароля восстановления с помощью его ИД To locate a recovery password by using a password ID
- В области «Пользователи и компьютеры Active Directory» щелкните правой кнопкой мыши контейнер домена и выберите «Найти пароль восстановления BitLocker». In Active Directory Users and Computers, right-click the domain container, and then click Find BitLocker Recovery Password.
- В диалоговом окне «Поиск пароля восстановления BitLocker» введите первые восемь символов пароля восстановления в поле «Код пароля» (первые 8 символов), а затем нажмите кнопку «Поиск». In the Find BitLocker Recovery Password dialog box, type the first eight characters of the recovery password in the Password ID (first 8 characters) box, and then click Search. Выполив процедуры в этом сценарии, вы просмотрели и скопировали пароли восстановления для компьютера и использовали ИД пароля для поиска пароля восстановления. By completing the procedures in this scenario, you have viewed and copied the recovery passwords for a computer and used a password ID to locate a recovery password.
How to Reset Windows Password on BitLocker Encrypted Drive
Lost admin password on a Windows PC that uses BitLocker drive encryption? When BitLocker is enabled on your hard drive, all your files will be encrypted. As a result, you’re unable to access any system files even if you boot with a Live CD, not to mention resetting your forgotten Windows password.
The good news is that if you have your BitLocker recovery key, you can use PCUnlocker to decrypt your hard drive and then reset Windows password you’ve lost or forgotten.
How to Reset Windows Password on BitLocker Encrypted Drive
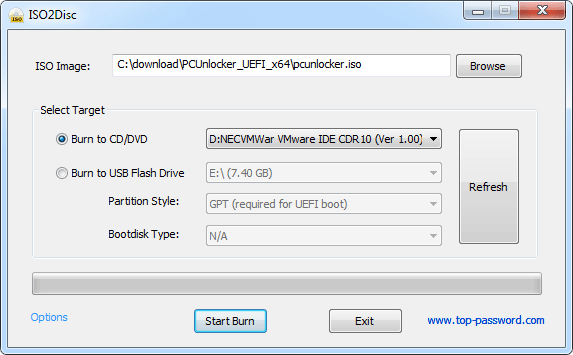
Download the ISO image of PCUnlocker Enterprise which adds BitLocker support, and then burn it to a CD or install it onto your USB flash drive using the third-party software ISO2Disc.
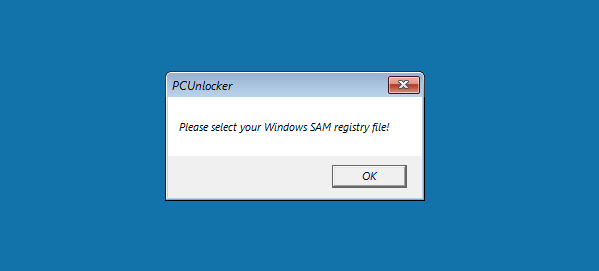
Next, insert the CD or USB into your BitLocker-protected computer. After booting from the CD/USB, you’ll see the message «Please select your Windows SAM registry file» on the screen as the system drive stays encrypted and inaccessible. Just click OK.
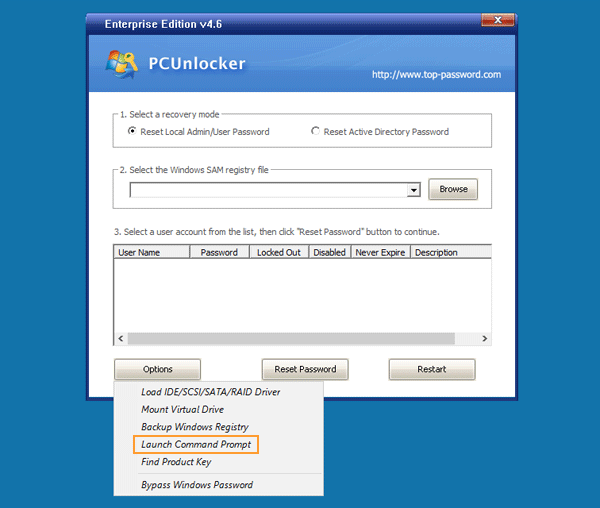
You’ll come to the main interface of PCUnlocker. Click the Options button and then choose «Launch Command Prompt» from the popup menu.
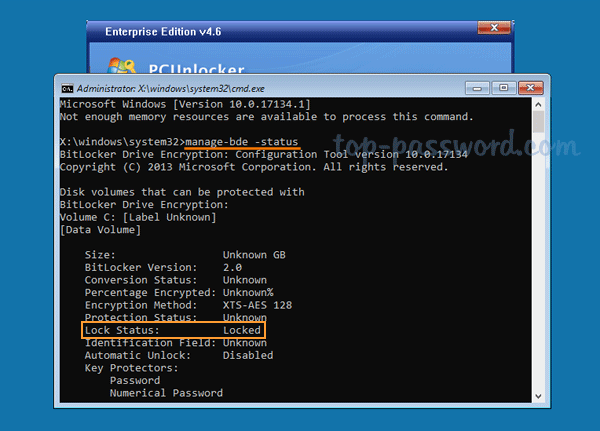
Run the following command to check the BitLocker status for all drives connected to your computer:
In the screenshot above, BitLocker has encrypted the system volume C: and it is currently locked.
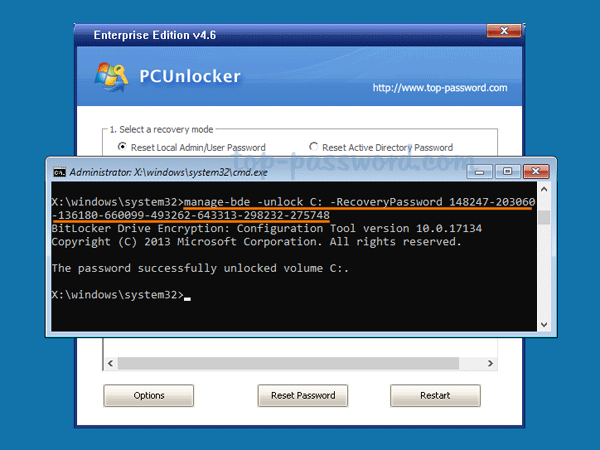
Now you need to use your BitLocker recovery key to unlock the encrypted system drive (usually C:). Type the following command:
Tip: You can open the BitLocker recovery key file with Notepad and paste the key on the command line.
If you can remember the password you set during BitLocker setup, type the following command. After pressing Enter, you have to enter your Bitlocker user password.
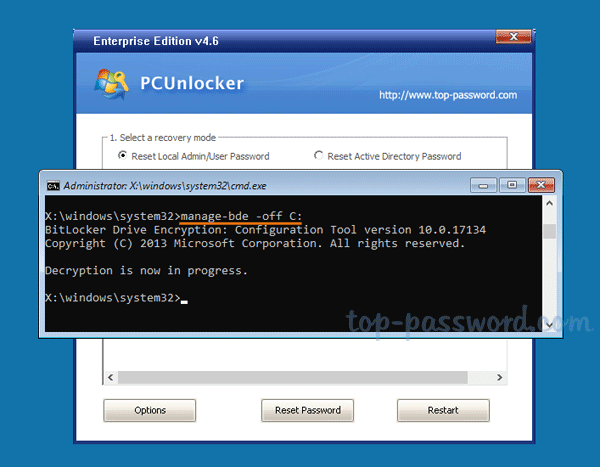
Next, execute the following command to decrypt your system drive. Depending on the size of the drive, this could take a while.
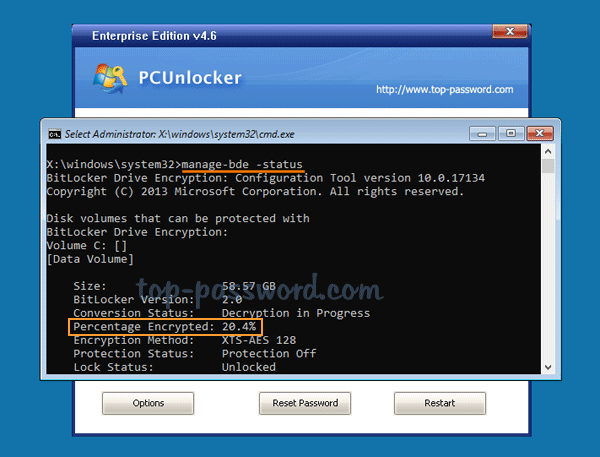
You can repeatedly type the following command to check the decryption progress. Look for «Percentage Encrypted» and wait for it to reach 0.0% (fully decrypted).
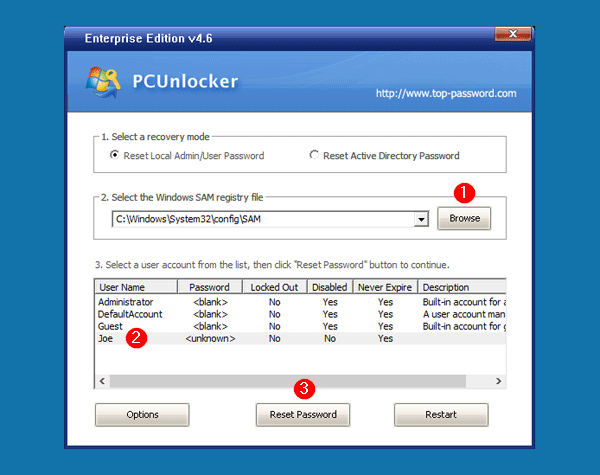
After turning off BitLocker, close the Command Prompt. At this point, you can click the Browse button to select the SAM registry hive on your system drive. Choose your regular account and click on Reset Password button to remove the password.
BitLocker recovery guide
Applies to:
This article for IT professionals describes how to recover BitLocker keys from AD DS.
Organizations can use BitLocker recovery information saved in Active Directory Domain Services (ADВ DS) to access BitLocker-protected data. Creating a recovery model for BitLocker while you are planning your BitLocker deployment is recommended.
This article assumes that you understand how to set up ADВ DS to back up BitLocker recovery information automatically, and what types of recovery information are saved to ADВ DS.
This article does not detail how to configure ADВ DS to store the BitLocker recovery information.
What is BitLocker recovery?
BitLocker recovery is the process by which you can restore access to a BitLocker-protected drive in the event that you cannot unlock the drive normally. In a recovery scenario, you have the following options to restore access to the drive:
- The user can supply the recovery password. If your organization allows users to print or store recovery passwords, the user can type in the 48-digit recovery password that they printed or stored on a USB drive or with your Microsoft Account online. (Saving a recovery password with your Microsoft Account online is only allowed when BitLocker is used on a PC that is not a member of a domain).
- A data recovery agent can use their credentials to unlock the drive. If the drive is an operating system drive, the drive must be mounted as a data drive on another computer for the data recovery agent to unlock it.
- A domain administrator can obtain the recovery password from AD DS and use it to unlock the drive. Storing recovery passwords in AD DS is recommended to provide a way for IT professionals to be able to obtain recovery passwords for drives in their organization if needed. This method requires that you have enabled this recovery method in the BitLocker Group Policy setting Choose how BitLocker-protected operating system drives can be recovered located at Computer Configuration\Administrative Templates\Windows Components\BitLocker Drive Encryption\Operating System Drives in the Local Group Policy Editor. For more information, see BitLocker Group Policy settings.
What causes BitLocker recovery?
The following list provides examples of specific events that will cause BitLocker to enter recovery mode when attempting to start the operating system drive:
On PCs that use BitLocker Drive Encryption, or on devices such as tablets or phones that use BitLocker Device Encryption only, when an attack is detected, the device will immediately reboot and enter into BitLocker recovery mode. To take advantage of this functionality, administrators can set the Interactive logon: Machine account lockout threshold Group Policy setting located in \Computer Configuration\Windows Settings\Security Settings\Local Policies\Security Options in the Local Group Policy Editor. Or they can use the MaxFailedPasswordAttempts policy of Exchange ActiveSync (also configurable through Microsoft Intune), to limit the number of failed password attempts before the device goes into Device Lockout.
On devices with TPM 1.2, changing the BIOS or firmware boot device order causes BitLocker recovery. However, devices with TPM 2.0 do not start BitLocker recovery in this case. TPM 2.0 does not consider a firmware change of boot device order as a security threat because the OS Boot Loader is not compromised.
Having the CD or DVD drive before the hard drive in the BIOS boot order and then inserting or removing a CD or DVD.
Failing to boot from a network drive before booting from the hard drive.
Docking or undocking a portable computer. In some instances (depending on the computer manufacturer and the BIOS), the docking condition of the portable computer is part of the system measurement and must be consistent to validate the system status and unlock BitLocker. So if a portable computer is connected to its docking station when BitLocker is turned on, then it might also need to be connected to the docking station when it is unlocked. Conversely, if a portable computer is not connected to its docking station when BitLocker is turned on, then it might need to be disconnected from the docking station when it is unlocked.
Changes to the NTFS partition table on the disk including creating, deleting, or resizing a primary partition.
Entering the personal identification number (PIN) incorrectly too many times so that the anti-hammering logic of the TPM is activated. Anti-hammering logic is software or hardware methods that increase the difficulty and cost of a brute force attack on a PIN by not accepting PIN entries until after a certain amount of time has passed.
Turning off the support for reading the USB device in the pre-boot environment from the BIOS or UEFI firmware if you are using USB-based keys instead of a TPM.
Turning off, disabling, deactivating, or clearing the TPM.
Upgrading critical early startup components, such as a BIOS or UEFI firmware upgrade, causing the related boot measurements to change.
Forgetting the PIN when PIN authentication has been enabled.
Updating option ROM firmware.
Upgrading TPM firmware.
Adding or removing hardware; for example, inserting a new card in the computer, including some PCMIA wireless cards.
Removing, inserting, or completely depleting the charge on a smart battery on a portable computer.
Changes to the master boot record on the disk.
Changes to the boot manager on the disk.
Hiding the TPM from the operating system. Some BIOS or UEFI settings can be used to prevent the enumeration of the TPM to the operating system. When implemented, this option can make the TPM hidden from the operating system. When the TPM is hidden, BIOS and UEFI secure startup are disabled, and the TPM does not respond to commands from any software.
Using a different keyboard that does not correctly enter the PIN or whose keyboard map does not match the keyboard map assumed by the pre-boot environment. This problem can prevent the entry of enhanced PINs.
Modifying the Platform Configuration Registers (PCRs) used by the TPM validation profile. For example, including PCR[1] would result in BitLocker measuring most changes to BIOS settings, causing BitLocker to enter recovery mode even when non-boot critical BIOS settings change.
Some computers have BIOS settings that skip measurements to certain PCRs, such as PCR[2]. Changing this setting in the BIOS would cause BitLocker to enter recovery mode because the PCR measurement will be different.
Moving the BitLocker-protected drive into a new computer.
Upgrading the motherboard to a new one with a new TPM.
Losing the USB flash drive containing the startup key when startup key authentication has been enabled.
Failing the TPM self-test.
Having a BIOS, UEFI firmware, or an option ROM component that is not compliant with the relevant Trusted Computing Group standards for a client computer. For example, a non-compliant implementation may record volatile data (such as time) in the TPM measurements, causing different measurements on each startup and causing BitLocker to start in recovery mode.
Changing the usage authorization for the storage root key of the TPM to a non-zero value.
The BitLocker TPM initialization process sets the usage authorization value to zero, so another user or process must explicitly have changed this value.
Disabling the code integrity check or enabling test signing on Windows Boot Manager (Bootmgr).
Pressing the F8 or F10 key during the boot process.
Adding or removing add-in cards (such as video or network cards), or upgrading firmware on add-in cards.
Using a BIOS hot key during the boot process to change the boot order to something other than the hard drive.
Before you begin recovery, we recommend that you determine what caused recovery. This might help prevent the problem from occurring again in the future. For instance, if you determine that an attacker has modified your computer by obtaining physical access, you can create new security policies for tracking who has physical presence. After the recovery password has been used to recover access to the PC, BitLocker will reseal the encryption key to the current values of the measured components.
For planned scenarios, such as a known hardware or firmware upgrades, you can avoid initiating recovery by temporarily suspending BitLocker protection. Because suspending BitLocker leaves the drive fully encrypted, the administrator can quickly resume BitLocker protection after the planned task has been completed. Using suspend and resume also reseals the encryption key without requiring the entry of the recovery key.
If suspended BitLocker will automatically resume protection when the PC is rebooted, unless a reboot count is specified using the manage-bde command line tool.
If software maintenance requires the computer to be restarted and you are using two-factor authentication, you can enable BitLocker Network Unlock to provide the secondary authentication factor when the computers do not have an on-premises user to provide the additional authentication method.
Recovery has been described within the context of unplanned or undesired behavior, but you can also cause recovery as an intended production scenario, in order to manage access control. For example, when you redeploy desktop or laptop computers to other departments or employees in your enterprise, you can force BitLocker into recovery before the computer is given to a new user.
Testing recovery
Before you create a thorough BitLocker recovery process, we recommend that you test how the recovery process works for both end users (people who call your helpdesk for the recovery password) and administrators (people who help the end user get the recovery password). The -forcerecovery command of manage-bde is an easy way for you to step through the recovery process before your users encounter a recovery situation.
To force a recovery for the local computer:
- Select the Start button, type cmd in the Start Search box, right-click cmd.exe, and then select Run as administrator.
- At the command prompt, type the following command and then press Enter: manage-bde -forcerecovery
To force recovery for a remote computer:
On the Start screen, typeВ cmd.exe, and then select Run as administrator.
At the command prompt, type the following command and then press ENTER: manage-bde -ComputerName -forcerecovery
Recovery triggered by -forcerecovery persists for multiple restarts until a TPM protector is added or protection is suspended by the user. When using Modern Standby devices (such as Surface devices), the -forcerecovery option is not recommended because BitLocker will have to be unlocked and disabled manually from the WinRE environment before the OS can boot up again. For more information, see BitLocker Troubleshooting: Continuous reboot loop with BitLocker recovery on a slate device.
Planning your recovery process
When planning the BitLocker recovery process, first consult your organization’s current best practices for recovering sensitive information. For example: How does your enterprise handle lost Windows passwords? How does your organization perform smart card PIN resets? You can use these best practices and related resources (people and tools) to help formulate a BitLocker recovery model.
Organizations that rely on BitLocker Drive Encryption and BitLocker To Go to protect data on a large number of computers and removable drives running the WindowsВ 10, Windows 8, or Windows 7 operating systems and Windows to Go should consider using the Microsoft BitLocker Administration and Monitoring (MBAM) Tool version 2.0, which is included in the Microsoft Desktop Optimization Pack (MDOP) for Microsoft Software Assurance. MBAM makes BitLocker implementations easier to deploy and manage and allows administrators to provision and monitor encryption for operating system and fixed drives. MBAM prompts the user before encrypting fixed drives. MBAM also manages recovery keys for fixed and removable drives, making recovery easier to manage. MBAM can be used as part of a Microsoft System Center deployment or as a stand-alone solution. For more info, see Microsoft BitLocker Administration and Monitoring.
After a BitLocker recovery has been initiated, users can use a recovery password to unlock access to encrypted data. Consider both self-recovery and recovery password retrieval methods for your organization.
When you determine your recovery process, you should:
Become familiar with how you can retrieve the recovery password. See:
Determine a series of steps for post-recovery, including analyzing why the recovery occurred and resetting the recovery password. See:
Self-recovery
In some cases, users might have the recovery password in a printout or a USB flash drive and can perform self-recovery. We recommend that your organization create a policy for self-recovery. If self-recovery includes using a password or recovery key stored on a USB flash drive, the users should be warned not to store the USB flash drive in the same place as the PC, especially during travel, for example if both the PC and the recovery items are in the same bag, then it’s easy for an unauthorized user to access the PC. Another policy to consider is having users contact the Helpdesk before or after performing self-recovery so that the root cause can be identified.
Recovery password retrieval
If the user does not have a recovery password in a printout or on a USB flash drive, the user will need to be able to retrieve the recovery password from an online source. If the PC is a member of a domain, the recovery password can be backed up to AD DS. However, this does not happen by default. You must have configured the appropriate Group Policy settings before BitLocker was enabled on the PC. BitLocker Group Policy settings can be found in the Local Group Policy Editor or the Group Policy Management Console (GPMC) under Computer Configuration\Administrative Templates\Windows Components\BitLocker Drive Encryption. The following policy settings define the recovery methods that can be used to restore access to a BitLocker-protected drive if an authentication method fails or is unable to be used.
- Choose how BitLocker-protected operating system drives can be recovered
- Choose how BitLocker-protected fixed drives can be recovered
- Choose how BitLocker-protected removable drives can be recovered
In each of these policies, select Save BitLocker recovery information to Active Directory Domain Services and then choose which BitLocker recovery information to store in Active Directory Domain Services (ADВ DS). Select the Do not enable BitLocker until recovery information is stored in AD DS check box if you want to prevent users from enabling BitLocker unless the computer is connected to the domain and the backup of BitLocker recovery information for the drive to ADВ DS succeeds.
If the PCs are part of a workgroup, users should be advised to save their BitLocker recovery password with their Microsoft Account online. Having an online copy of your BitLocker recovery password is recommended to help ensure that you do not lose access to your data in the event that recovery is required.
The BitLocker Recovery Password Viewer for Active Directory Users and Computers tool allows domain administrators to view BitLocker recovery passwords for specific computer objects in Active Directory.
You can use the following list as a template for creating your own recovery process for recovery password retrieval. This sample process uses the BitLocker Recovery Password Viewer for Active Directory Users and Computers tool.
Record the name of the user’s computer
You can use the name of the user’s computer to locate the recovery password in ADВ DS. If the user does not know the name of the computer, ask the user to read the first word of the Drive Label in the BitLocker Drive Encryption Password Entry user interface. This is the computer name when BitLocker was enabled and is probably the current name of the computer.
Verify the user’s identity
Verify that the person that is asking for the recovery password is truly the authorized user of that computer. You might also want to verify that the computer with the name the user provided belongs to the user.
Locate the recovery password in ADВ DS
Locate the Computer object with the matching name in ADВ DS. Because Computer object names are listed in the ADВ DS global catalog, you should be able to locate the object even if you have a multi-domain forest.
Multiple recovery passwords
If multiple recovery passwords are stored under a computer object in ADВ DS, the name of the BitLocker recovery information object includes the date that the password was created.
If at any time you are unsure what password to provide, or if you think you might be providing the incorrect password, ask the user to read the eight character password ID that is displayed in the recovery console.
Since the password ID is a unique value that is associated with each recovery password stored in ADВ DS, running a query using this ID will find the correct password to unlock the encrypted volume.
Gather information to determine why recovery occurred
Before you give the user the recovery password, you should gather any information that will help determine why the recovery was needed, in order to analyze the root cause during the post-recovery analysis. For more info about post-recovery analysis, see Post-recovery analysis.
Give the user the recovery password
Because the recovery password is 48 digits long, the user might need to record the password by writing it down or typing it on a different computer. If you are using MBAM, the recovery password will be regenerated after it is recovered from the MBAM database to avoid the security risks associated with an uncontrolled password.
Because the 48-digit recovery password is long and contains a combination of digits, the user might mishear or mistype the password. The boot-time recovery console uses built-in checksum numbers to detect input errors in each 6-digit block of the 48-digit recovery password, and offers the user the opportunity to correct such errors.
Post-recovery analysis
When a volume is unlocked using a recovery password, an event is written to the event log and the platform validation measurements are reset in the TPM to match the current configuration. Unlocking the volume means that the encryption key has been released and is ready for on-the-fly encryption when data is written to the volume, and on-the-fly decryption when data is read from the volume. After the volume is unlocked, BitLocker behaves the same way, regardless of how the access was granted.
If you notice that a computer is having repeated recovery password unlocks, you might want to have an administrator perform post-recovery analysis to determine the root cause of the recovery and refresh BitLocker platform validation so that the user no longer needs to enter a recovery password each time that the computer starts up. See:
Determine the root cause of the recovery
If a user needed to recover the drive, it is important to determine the root cause that initiated the recovery as soon as possible. Properly analyzing the state of the computer and detecting tampering may reveal threats that have broader implications for enterprise security.
While an administrator can remotely investigate the cause of recovery in some cases, the end user might need to bring the computer that contains the recovered drive on site to analyze the root cause further.
Review and answer the following questions for your organization:
- What BitLocker protection mode is in effect (TPM, TPM + PIN, TPM + startup key, startup key only)? Which PCR profile is in use on the PC?
- Did the user merely forget the PIN or lose the startup key? If a token was lost, where might the token be?
- If TPM mode was in effect, was recovery caused by a boot file change?
- If recovery was caused by a boot file change, was the change an intended user action (for example, BIOS upgrade), or was it caused by malicious software?
- When was the user last able to start the computer successfully, and what might have happened to the computer since then?
- Might the user have encountered malicious software or left the computer unattended since the last successful startup?
To help you answer these questions, use the BitLocker command-line tool to view the current configuration and protection mode (for example, manage-bde -status). Scan the event log to find events that help indicate why recovery was initiated (for example, if the boot file changed). Both of these capabilities can be performed remotely.
Resolve the root cause
After you have identified what caused recovery, you can reset BitLocker protection and avoid recovery on every startup.
The details of this reset can vary according to the root cause of the recovery. If you cannot determine the root cause, or if malicious software or a rootkit might have infected the computer, Helpdesk should apply best-practice virus policies to react appropriately.
You can perform a BitLocker validation profile reset by suspending and resuming BitLocker.
Unknown PIN
If a user has forgotten the PIN, you must reset the PIN while you are logged on to the computer in order to prevent BitLocker from initiating recovery each time the computer is restarted.
To prevent continued recovery due to an unknown PIN
- Unlock the computer using the recovery password.
- Reset the PIN:
- Right-click the drive and then select Change PIN.
- In the BitLocker Drive Encryption dialog, select Reset a forgotten PIN. If you are not logged in with an administrator account, provide administrative credentials at this time.
- In the PIN reset dialog, provide and confirm the new PIN to use and then select Finish.
- You will use the new PIN the next time you unlock the drive.
Lost startup key
If you have lost the USB flash drive that contains the startup key, then you must unlock the drive by using the recovery key and then create a new startup key.
To prevent continued recovery due to a lost startup key
- Log on as an administrator to the computer that has the lost startup key.
- Open Manage BitLocker.
- Select Duplicate start up key, insert the clean USB drive on which you are going to write the key and then select Save.
Changes to boot files
This error might occur if you updated the firmware. As a best practice, you should suspend BitLocker before making changes to the firmware and then resume protection after the update has completed. This action prevents the computer from going into recovery mode. However if changes were made when BitLocker protection was on, then log on to the computer using the recovery password, and the platform validation profile will be updated so that recovery will not occur the next time.
Windows RE and BitLocker Device Encryption
Windows Recovery Environment (RE) can be used to recover access to a drive protected by BitLocker Device Encryption. If a PC is unable to boot after two failures, Startup Repair will automatically start. When Startup Repair is launched automatically due to boot failures, it will only execute operating system and driver file repairs, provided that the boot logs or any available crash dump point to a specific corrupted file. In Windows 8.1 and later, devices that include firmware to support specific TPM measurements for PCR[7] the TPM can validate that Windows RE is a trusted operating environment and will unlock any BitLocker-protected drives if Windows RE has not been modified. If the Windows RE environment has been modified, for example the TPM has been disabled, the drives will stay locked until the BitLocker recovery key is provided. If Startup Repair can’t run automatically from the PC and instead Windows RE is manually started from a repair disk, then the BitLocker recovery key must be provided to unlock the BitLocker–protected drives.
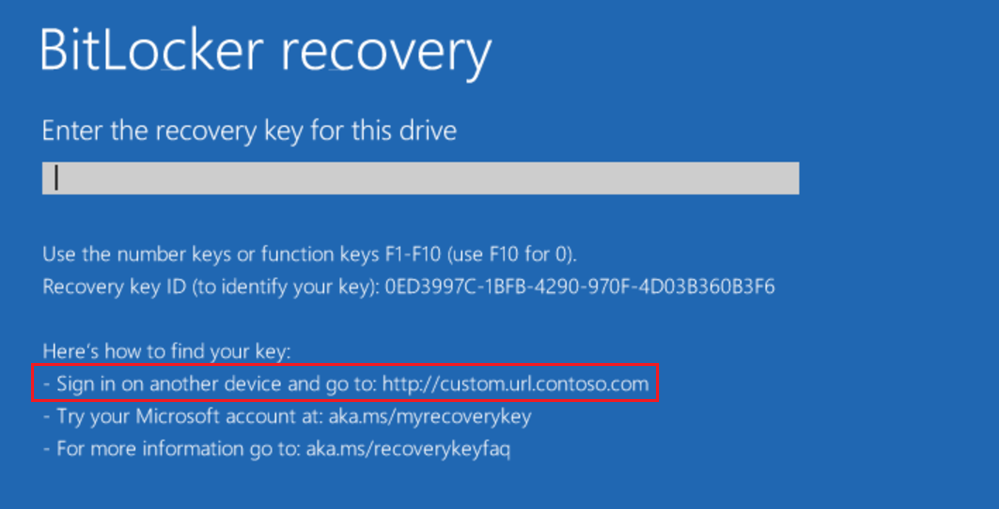
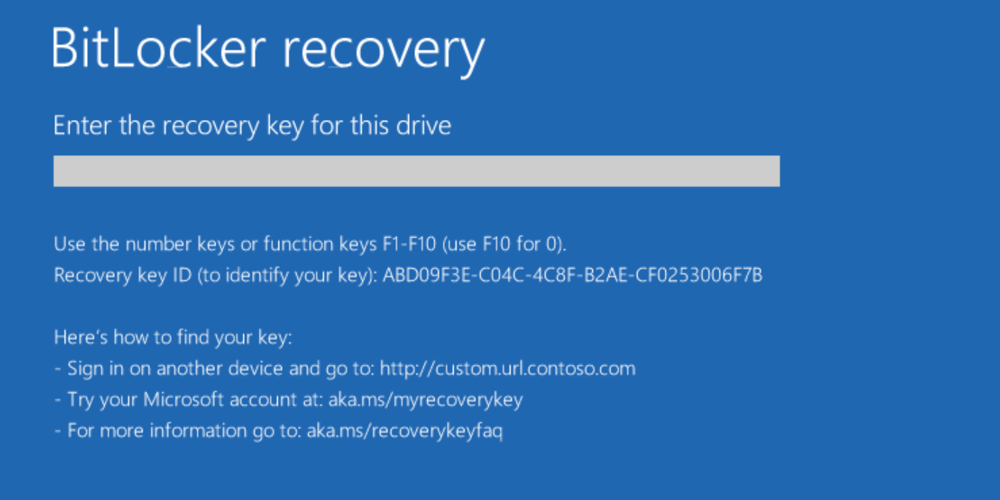
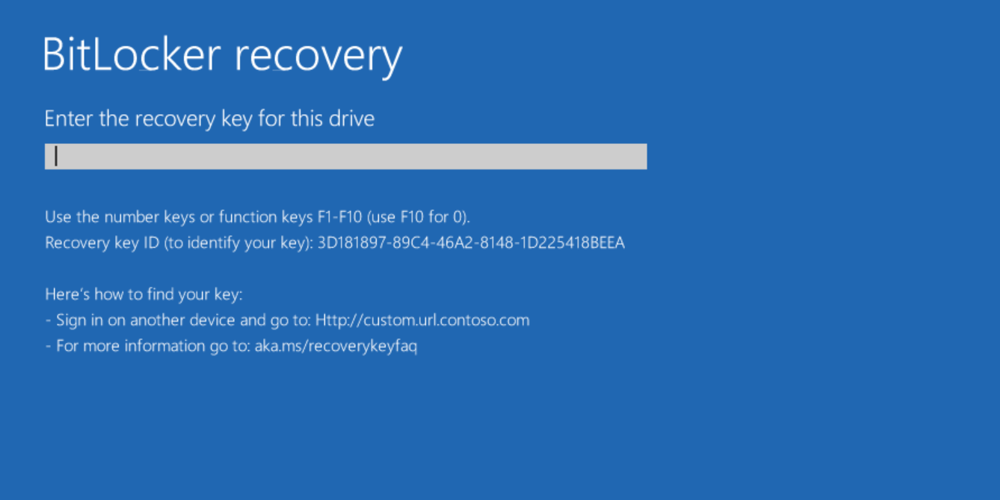
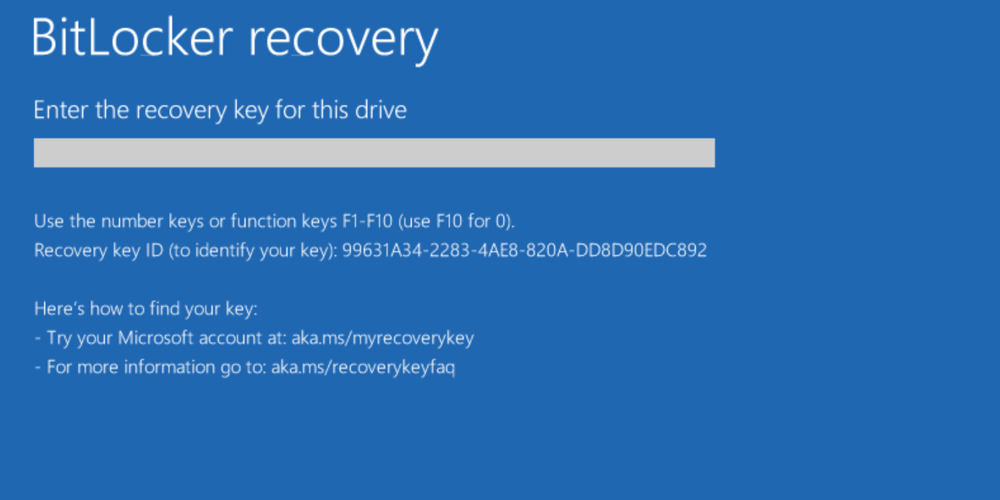
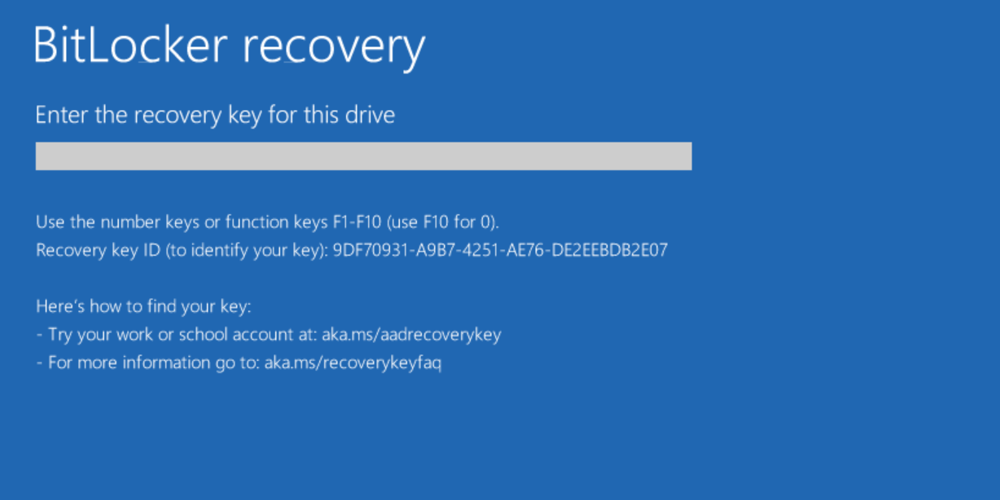
BitLocker recovery screen
During BitLocker recovery, Windows can display a custom recovery message and hints that identify where a key can be retrieved from. These improvements can help a user during BitLocker recovery.
Custom recovery message
BitLocker Group Policy settings in Windows 10, version 1511, let you configure a custom recovery message and URL on the BitLocker recovery screen, which can include the address of the BitLocker self-service recovery portal, the IT internal website, or a phone number for support.
This policy can be configured using GPO under Computer Configuration > Administrative Templates > Windows Components > BitLocker Drive Encryption > Operating System Drives > Configure pre-boot recovery message and URL.
It can also be configured using Intune mobile device management (MDM) in the BitLocker CSP: ./Device/Vendor/MSFT/BitLocker/SystemDrivesRecoveryMessage
Example of customized recovery screen:
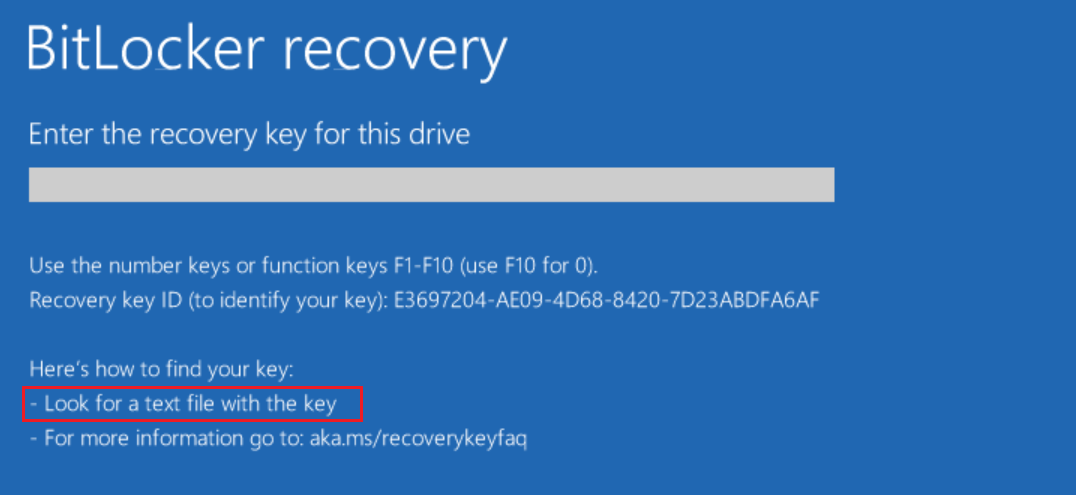
BitLocker recovery key hints
BitLocker metadata has been enhanced in Windows 10, version 1903 to include information about when and where the BitLocker recovery key was backed up. This information is not exposed through the UI or any public API. It is used solely by the BitLocker recovery screen in the form of hints to help a user locate a volume’s recovery key. Hints are displayed on the recovery screen and refer to the location where the key has been saved. Hints are displayed on both the modern (blue) and legacy (black) recovery screen. This applies to both the boot manager recovery screen and the WinRE unlock screen.
We don’t recommend printing recovery keys or saving them to a file. Instead, use Active Directory backup or a cloud-based backup. Cloud-based backup includes Azure Active Directory (Azure AD) and Microsoft Account.
There are rules governing which hint is shown during the recovery (in order of processing):
- Always display custom recovery message if it has been configured (using GPO or MDM).
- Always display generic hint: «For more information, go to https://aka.ms/recoverykeyfaq».
- If multiple recovery keys exist on the volume, prioritize the last created (and successfully backed up) recovery key.
- Prioritize keys with successful backup over keys that have never been backed up.
- Prioritize backup hints in the following order for remote backup locations: Microsoft Account > Azure AD > Active Directory.
- If a key has been printed and saved to file, display a combined hint, «Look for a printout or a text file with the key,» instead of two separate hints.
- If multiple backups of the same type (remove vs. local) have been performed for the same recovery key, prioritize backup info with latest backed up date.
- There is no specific hint for keys saved to an on-premises Active Directory. In this case, a custom message (if configured) or a generic message, «Contact your organization’s help desk,» will be displayed.
- If two recovery keys are present on the disk, but only one has been successfully backed up, the system will ask for a key that has been backed up, even if another key is newer.
Example 1 (single recovery key with single backup)
| Custom URL | Yes |
|---|---|
| Saved to Microsoft Account | Yes |
| Saved to Azure AD | No |
| Saved to Active Directory | No |
| Printed | No |
| Saved to file | No |
Result: The hint for the Microsoft Account and the custom URL are displayed.
Example 2 (single recovery key with single backup)
| Custom URL | Yes |
|---|---|
| Saved to Microsoft Account | No |
| Saved to Azure AD | No |
| Saved to Active Directory | Yes |
| Printed | No |
| Saved to file | No |
Result: Only the custom URL is displayed.
Example 3 (single recovery key with multiple backups)
| Custom URL | No |
|---|---|
| Saved to Microsoft Account | Yes |
| Saved to Azure AD | Yes |
| Saved to Active Directory | No |
| Printed | Yes |
| Saved to file | Yes |
Result: Only the Microsoft Account hint is displayed.
Example 4 (multiple recovery passwords)
| Custom URL | No |
|---|---|
| Saved to Microsoft Account | No |
| Saved to Azure AD | No |
| Saved to Active Directory | No |
| Printed | No |
| Saved to file | Yes |
| Creation time | 1PM |
| Key ID | A564F193 |
| Custom URL | No |
|---|---|
| Saved to Microsoft Account | No |
| Saved to Azure AD | No |
| Saved to Active Directory | No |
| Printed | No |
| Saved to file | No |
| Creation time | 3PM |
| Key ID | T4521ER5 |
Result: Only the hint for a successfully backed up key is displayed, even if it isn’t the most recent key.
Example 5 (multiple recovery passwords)
| Custom URL | No |
|---|---|
| Saved to Microsoft Account | Yes |
| Saved to Azure AD | Yes |
| Saved to Active Directory | No |
| Printed | No |
| Saved to file | No |
| Creation time | 1PM |
| Key ID | 99631A34 |
| Custom URL | No |
|---|---|
| Saved to Microsoft Account | No |
| Saved to Azure AD | Yes |
| Saved to Active Directory | No |
| Printed | No |
| Saved to file | No |
| Creation time | 3PM |
| Key ID | 9DF70931 |
Result: The hint for the most recent key is displayed.
Using additional recovery information
Besides the 48-digit BitLocker recovery password, other types of recovery information are stored in Active Directory. This section describes how this additional information can be used.
BitLocker key package
If the recovery methods discussed earlier in this document do not unlock the volume, you can use the BitLocker Repair tool to decrypt the volume at the block level. The tool uses the BitLocker key package to help recover encrypted data from severely damaged drives. You can then use this recovered data to salvage encrypted data, even after the correct recovery password has failed to unlock the damaged volume. We recommend that you still save the recovery password. A key package cannot be used without the corresponding recovery password.
You must use the BitLocker Repair tool repair-bde to use the BitLocker key package.
The BitLocker key package is not saved by default. To save the package along with the recovery password in AD DS, you must select the Backup recovery password and key package option in the Group Policy settings that control the recovery method. You can also export the key package from a working volume. For more details about how to export key packages, see Retrieving the BitLocker Key Package.
Resetting recovery passwords
Invalidate a recovery password after it has been provided and used. It should also be done when you intentionally want to invalidate an existing recovery password for any reason.
You can reset the recovery password in two ways:
- Use manage-bde: You can use manage-bde to remove the old recovery password and add a new recovery password. The procedure identifies the command and the syntax for this method.
- Run a script: You can run a script to reset the password without decrypting the volume. The sample script in the procedure illustrates this functionality. The sample script creates a new recovery password and invalidates all other passwords.
To reset a recovery password using manage-bde:
Remove the previous recovery password
Add the new recovery password
Get the ID of the new recovery password. From the screen, copy the ID of the recovery password.
Back up the new recovery password to AD DS.
You must include the braces in the ID string.
To run the sample recovery password script:
Save the following sample script in a VBScript file. For example: ResetPassword.vbs.
At the command prompt, type a command similar to the following sample script:
cscript ResetPassword.vbs
This sample script is configured to work only for the C volume. You must customize the script to match the volume where you want to test password reset.
To manage a remote computer, you can specify the remote computer name rather than the local computer name.
You can use the following sample script to create a VBScript file to reset the recovery passwords:
Retrieving the BitLocker key package
You can use two methods to retrieve the key package, as described in Using Additional Recovery Information:
- Export a previously saved key package from ADВ DS. You must have Read access to BitLocker recovery passwords that are stored in ADВ DS.
- Export a new key package from an unlocked, BitLocker-protected volume. You must have local administrator access to the working volume, before any damage has occurred.
The following sample script exports all previously saved key packages from ADВ DS.
To run the sample key package retrieval script:
Save the following sample script in a VBScript file. For example: GetBitLockerKeyPackageADDS.vbs.
At the command prompt, type a command similar to the following sample script:
cscript GetBitLockerKeyPackageADDS.vbs -?
You can use the following sample script to create a VBScript file to retrieve the BitLocker key package from ADВ DS:
The following sample script exports a new key package from an unlocked, encrypted volume.
To run the sample key package retrieval script:
Save the following sample script in a VBScript file. For example: GetBitLockerKeyPackage.vbs
Open an administrator command prompt, and then type a command similar to the following sample script: