- How to Reset Windows 10 Password with Ubuntu Live CD/USB
- How to Reset Windows 10 Password with Ubuntu Live CD/USB
- BootDev
- Страницы
- 2018-09-03
- SystemRescueCd: Cброс пароля Windows
- Содержание
- System Rescue CD
- Сброс Пароля
- Reset the password in Ubuntu / Linux Bash in Windows
- 6 Answers 6
- Windows: Как сбросить пароль Windows при помощи Linux
- How to reset a Windows password with Linux
- Lost your Windows login? The chntpw utility can save the day.
- Subscribe now
- passwordreset_login-pass.png
- passwordreset_boot.png
- passwordreset_try-fedora.png
- passwordreset_root.png
- passwordreset_install.png
- passwordreset_sfdisk.png
- mount-1.png
- passwordreset_mount-2.png
- passwordreset_mount-3.png
- passwordreset_username-1.png
- passwordreset_username-2.png
- passwordreset_clear-1.png
- passwordreset_clear-2.png
- passwordreset_nopass-1.png
- passwordreset_nopass-2.png
- Topics
- About the author
- Recommended reading
- 30 Comments, Register or Log in to post a comment.
How to Reset Windows 10 Password with Ubuntu Live CD/USB
Forgot administrator password of your Windows 10 PC? If you had not created a Windows 10 password reset disk earlier, then you’re left with an option to reinstall Windows, but that will erase all your files and settings. Well, do not worry. In this tutorial we will discuss how to reset Windows 10 password with Ubuntu Live CD or USB drive, when you forgot your computer password.
How to Reset Windows 10 Password with Ubuntu Live CD/USB
- To get started, just download Ubuntu Desktop free from Ubuntu official website (about 1.4 GB). Burn the ISO image to a CD (or USB flash drive) using the freeware ISO2Disc.
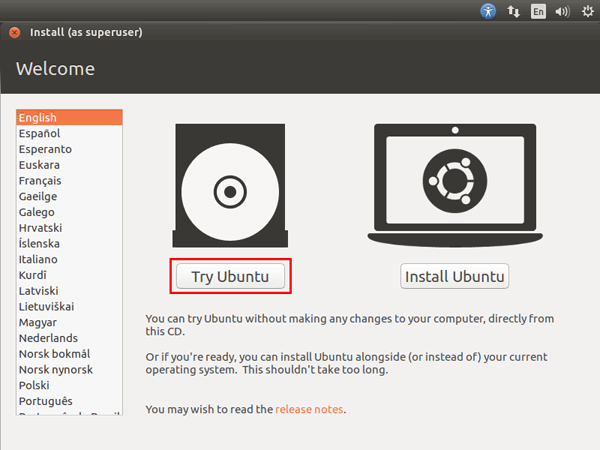
Insert the Ubuntu Live CD into the computer that you want to reset the password for, then you need to boot off the disc. Once booted to the Ubuntu Live welcome screen, choose Try Ubuntu.
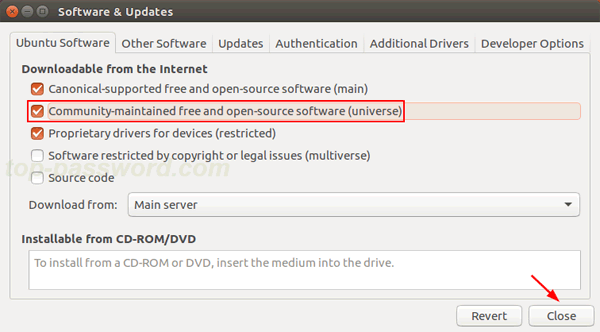
Open System Settings and then click on Software and Updates. In the window that appears, check the «Community-maintained free and open-source software» option and click Close.
A dialog will appear with the repository information is out of date. You have to Click the Reload button.
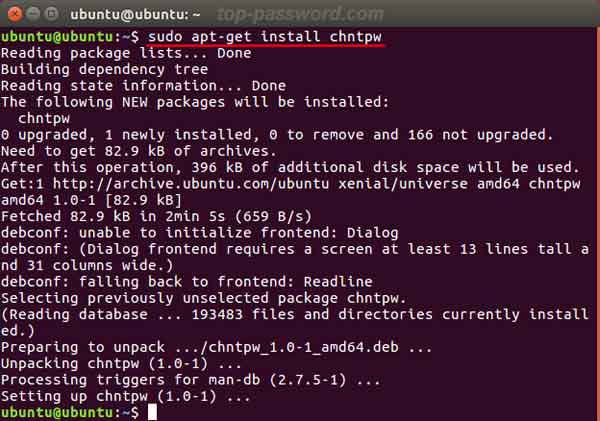
Open a terminal, then run the following command to install the password resetting utility you’ll need.
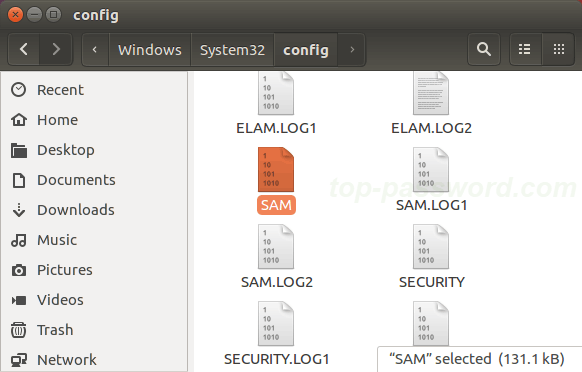
Now find your Windows partition and browse to the directory Windows\System32\Config. Right-click blank space and select Open in Terminal.
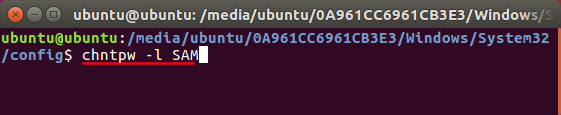
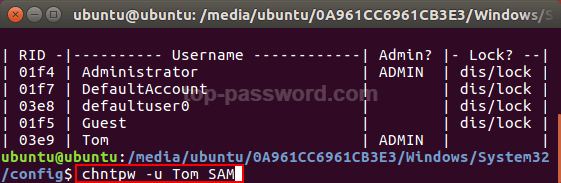
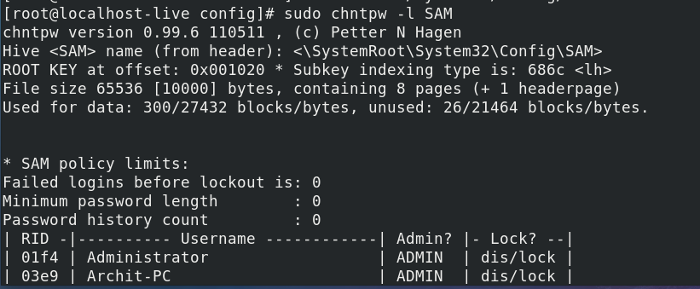
In the terminal, run the following command and it will list out all the user accounts that are contained on your Windows 10 system.
If you would like to reset lost password for a specific account, type the following command and press Enter.
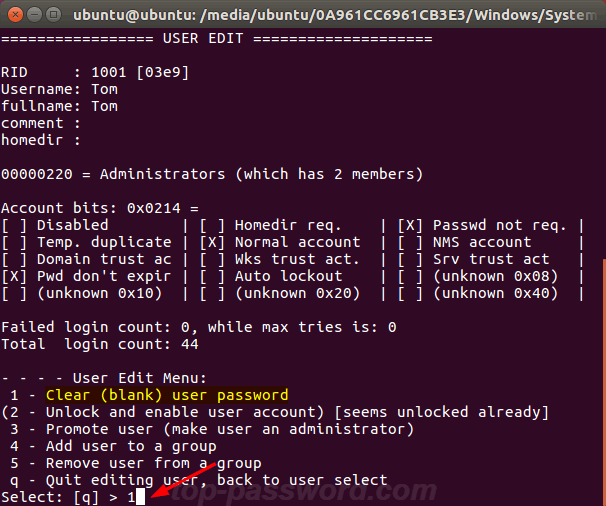
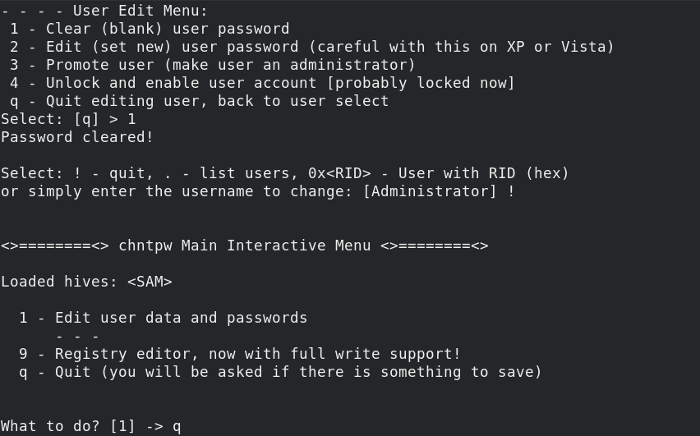
You’ll be presented with several options to reset the password, unlock / enable / promote user account. Type 1 and press Enter.
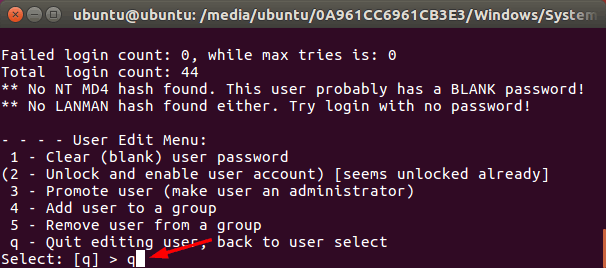
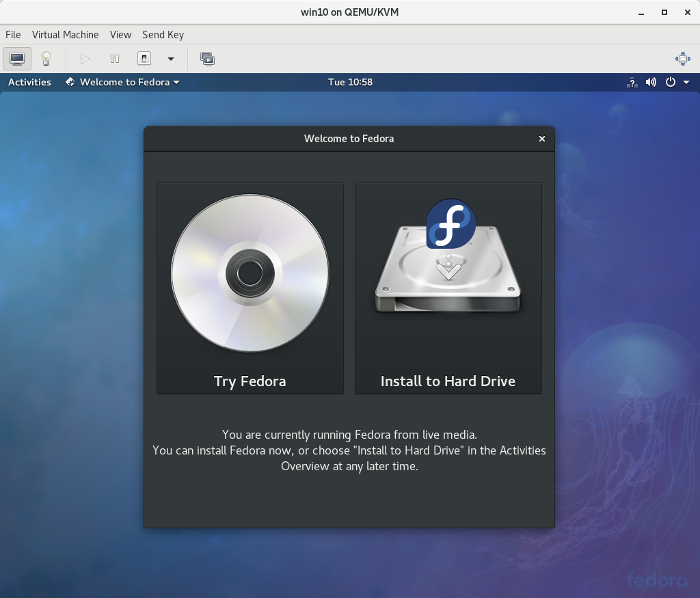
Type q and hit Enter at this point to quit the User Edit Menu.
Then type y to confirm and save the changes.
This method is easy to follow for Linux users to reset Windows 10 local user password. If you’re looking for a much easier yet professional live CD/USB to bypass Windows 10 Microsoft / local password, you can try PCUnlocker.
BootDev
Создание загрузочных дисков и прочие полезные мелочи
Страницы
2018-09-03
SystemRescueCd: Cброс пароля Windows
Содержание
System Rescue CD
Данный livecd предназначен для восстановления работоспособности операционных систем Linux и Windows. Скачать iso-образ данного можно по ссылке http://www.system-rescue-cd.org/Download/.
Сброс Пароля
Как и прежде, сброс пароля будет проводится на операционной системе Windows 10. Приступим.
Выведем информацию о диска системы, чтобы определить целевой, с установленной операционной системой Windows.
Из вывода, видно, что целевой диск /dev/sda, а необходимый раздел, с ОС Windows, /dev/sda2.
Смонтируем раздел /dev/sda2 для выполнения дальнейших манипуляций над ним.
mount /dev/sda2 /mnt/windows
Перейдем в папку /Windows/System32/config.
Проверяем наличие файла SAM.
Создаем резервную копию файла SAM. На всякий случай.
Выполняем вывод учетных записей файла SAM, чтобы определить необходимую.
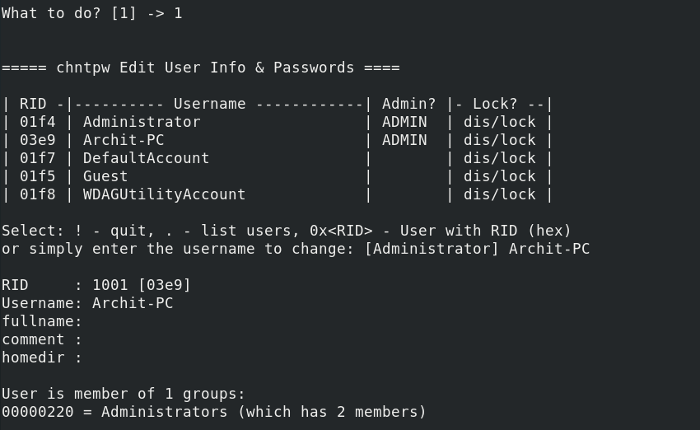
Узнав данные необходимой учетной записи (имя или RID), переходим к ее редактированию.
chntpw -u BootDevRU SAM
chntpw -u 0x3e9 SAM
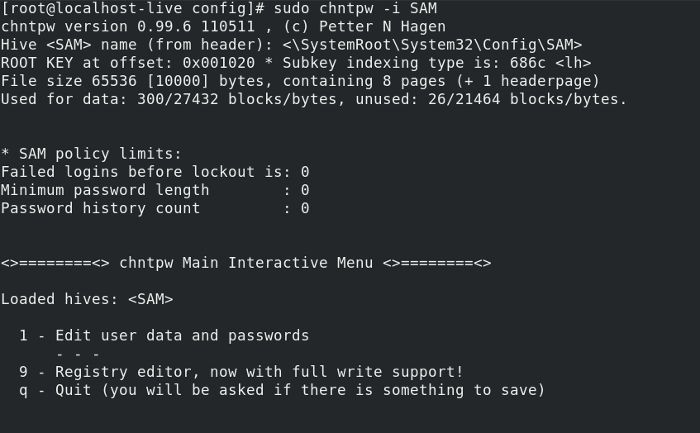
Откроется интерактивный режим. Перед нами будет меню из шести пунктов. Сброс пароля расположен под номером 1. Вводим данную цифру и нажимаем ENTER .
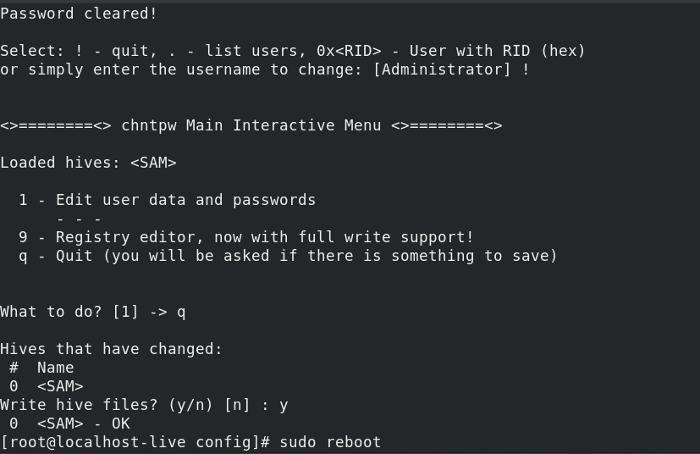
Программа выдаст сообщение что пароль успешно сброшен. Выполняем выход из интерактивного режима введя букву q. Соглашаемся с внесением изменений введя y.
Выполняем перезагрузку командой reboot , и загружаемся с жесткого диска компьютера.
Пароль успешно сброшен. Как и прежде, можно вернуть сброшенный пароль, восстановив бэкап файла SAM.
Итак. Мы выполнили сброс пароля учетной записи Windows через операционную систему Linux. Все что потребовалось, это скормить chntpw SAM файл целевой ОС.
Возможно также восстановить сброшенный пароль, так как была создана резервная копия файла SAM. Подробно данный процесс описан тут.
Reset the password in Ubuntu / Linux Bash in Windows
I have installed Linux Bash on Windows 10 (available from Microsoft), but I’ve forgotten my password.
I’ve searched for a solution but I only find suggestions that involve doing something before the system boots, like accessing recovery mode, but that will not work in this case as this Ubuntu is just an application within a Windows system and doesn’t have its own boot process.
How can I reset my password?
6 Answers 6
- Run bash and make a note of your Linux username (this need not match your Windows username), see How can I find out my user name?
- Close Bash on Ubuntu if it is running (or the next command will fail).
In Windows admin command prompt ( Super + X , A ) change the default user to root:
If you are using Ubuntu 18.04 in WSL, the command has changed to ubuntu1804 , so
- Now Bash on Ubuntu on Windows logs you in as root without asking password
Use passwd command in Bash to change the user password (the user whose password you want to reset):
Change the default user back to your normal user in Windows command prompt
If you are using Ubuntu 18.04 in WSL, the command has changed to ubuntu1804 , so
Watch Full Video to Recover your password Windows Subsystem Linux https://youtu.be/dTR232yvDCE
Note 1: The subsystem used in the video is not Ubuntu, but Kali Linux. Hence the difference in the command.
Note 2: If you are still using the original Ubuntu subsystem that came with the Anniversary Update, use the command lxrun. Upgrade to the subsystem version distributed via Microsoft Store is recommended.)
Windows: Как сбросить пароль Windows при помощи Linux
Бывают такие ситуации, когда вы забыли пароль к системе Windows или вам необходимо получить доступ, но вы не знайте пароль учетной записи с правами Администратора. При помощи Fedora Linux, можно быстро и просто сбросить пароль на любой версии Windows. Для этого понадобится сделать загрузочную флешку или записать диск с образом Linux. Записать образ на флешку, можно при помощи утилиты etcher, после чего подключить ее в ПК и следовать действиям описанным ниже. Для описания примера сброса пароля использовался Windows 10 и дистрибутив Linux — Fedora 27.
01. Подключаем загрузочную флешку и перезагружаем ПК.
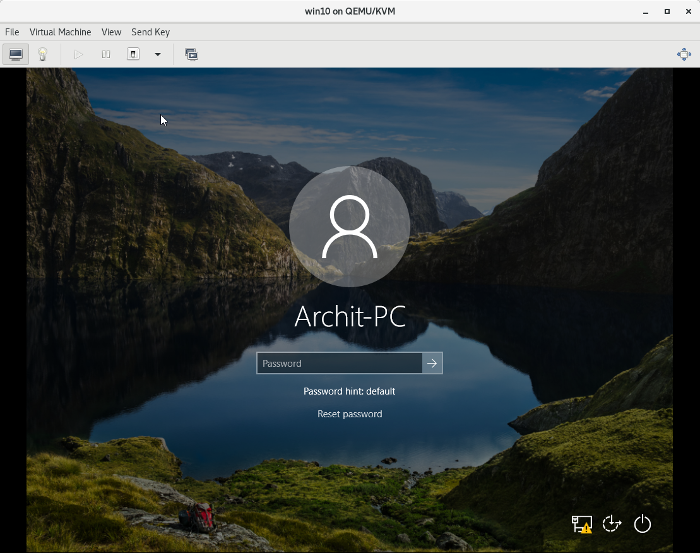
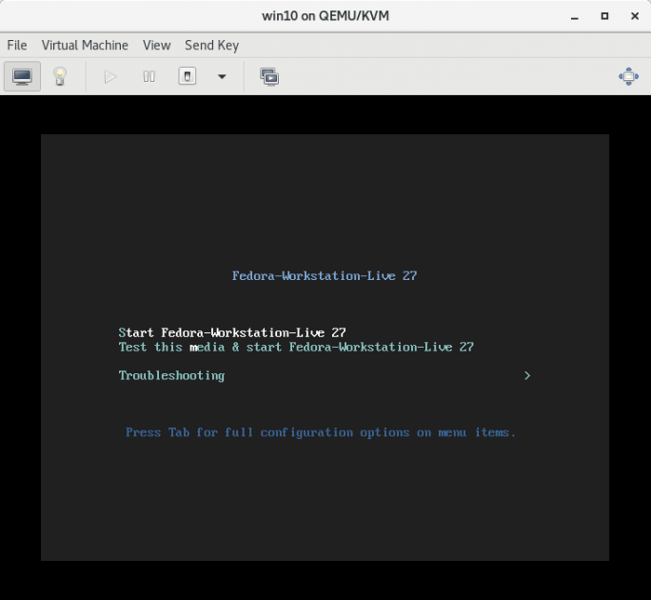
02. Загружаемся с флешки и выбираем «Start Fedora-Workstation-Live 27» и выбираем «Try Fedora«.
03. Запускаем Terminal.
04. Набираем следующие команды для установки chntpw:
05. Проверяем доступные области жесткого диска:
06. Монтируем раздел с Windows (/dev/sda2):
07. Переходим в директорию с SAM записями Windows и запускам chntpw:
08. Редактируем SAM записи:
09. Из списка предложных действий выбираем [1]
10. Вводим необходимое имя пользователя из предложенного списка (forbiddenaccess):
11. Далее выбираем опцию [1] для того, что бы сбросить пароль выбранной учетной записи.
12. Вводим !, затем q и сохраняем изменения в SAM — y
13. Перезагружаем ПК при помощи следующей команды:
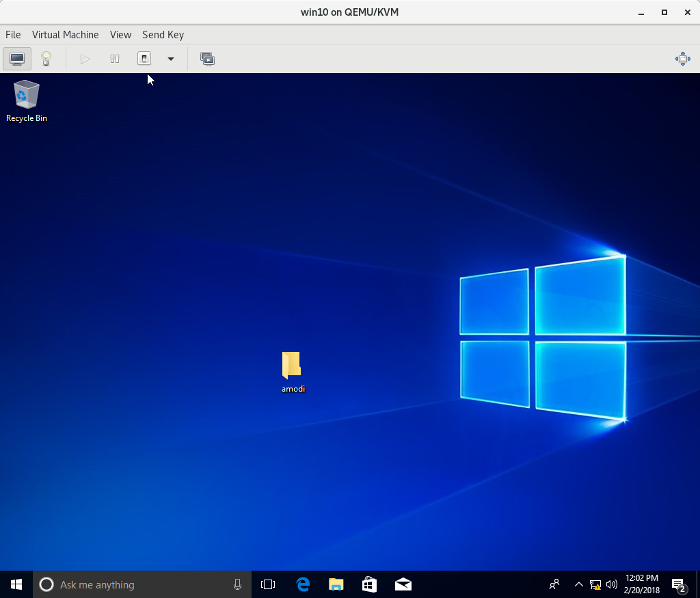
14. Система Windows загружается без запроса ввода пароля
How to reset a Windows password with Linux
Lost your Windows login? The chntpw utility can save the day.
Subscribe now
Get the highlights in your inbox every week.
If you (or someone you know) ever forget your Windows password, you’ll be glad to know about chntpw , a neat Linux utility that you can use to reset a Windows password. For this how-to, I created a Windows virtual machine and set the password to pass123 on my user account, Archit -PC . I also created a Live USB with Fedora 27 using the Fedora Media Writer application.
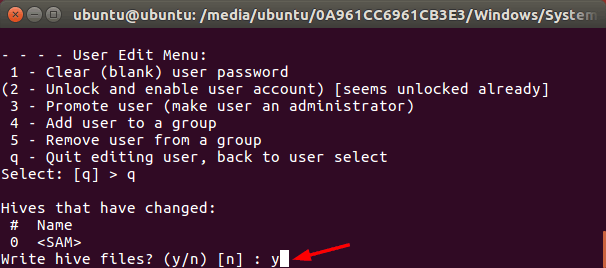
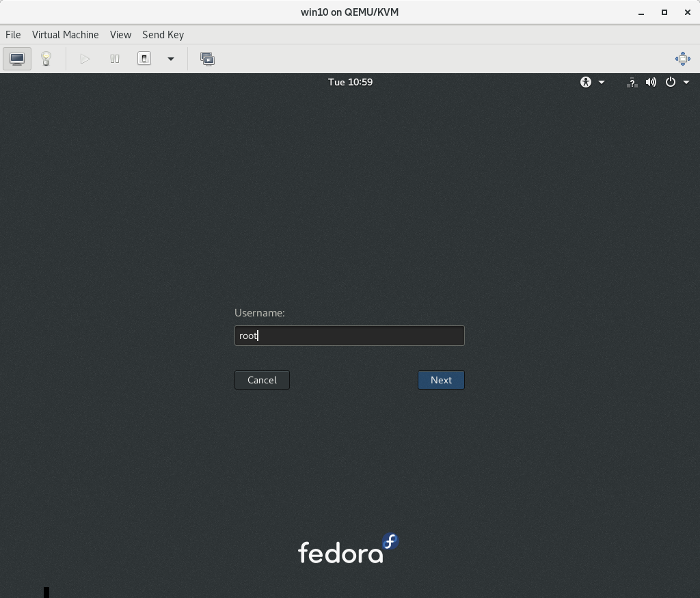
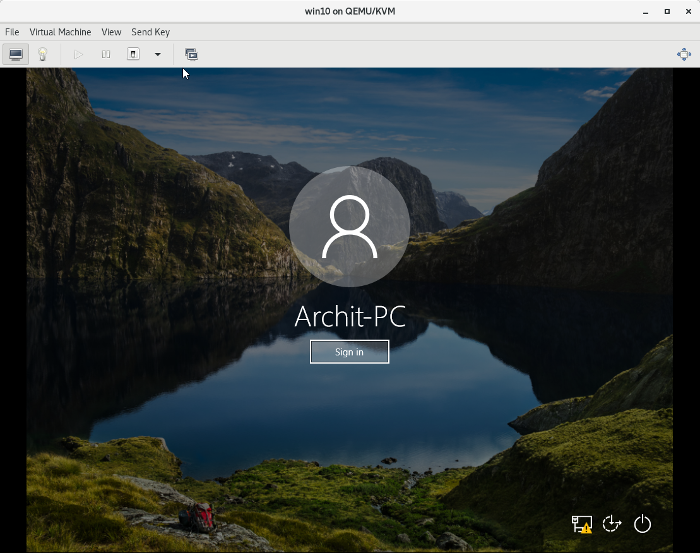
1. Attach the Live USB to your PC and restart from the login screen, as shown below:
passwordreset_login-pass.png
2. Boot from the Live USB and click on Try Fedora:
passwordreset_boot.png
passwordreset_try-fedora.png
3. Log out from live-user and log into root . This step is not necessary, but I prefer to use the root user to bypass any permission issues:
passwordreset_root.png
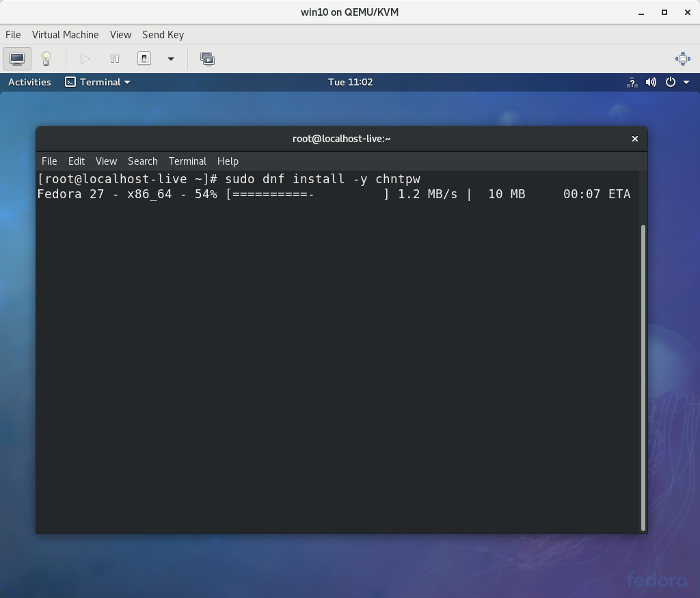
4. Install the chntpw utility with the following command (you’ll need a live internet connection for this):
passwordreset_install.png
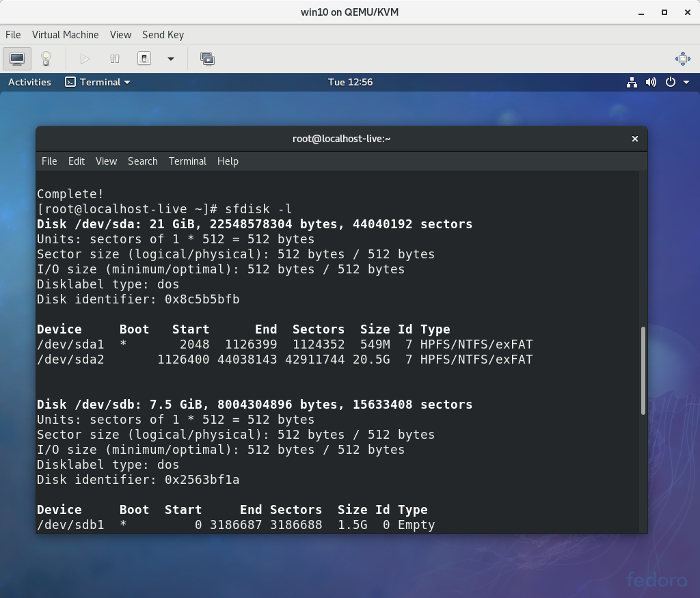
5. Check which partition should be mounted by sfdisk -l .
passwordreset_sfdisk.png
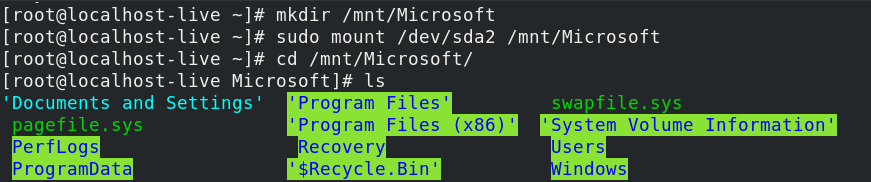
and mount that partition (e.g., /dev/sda2 ) with the following command:
mount-1.png
Change the current directory to the config directory:
passwordreset_mount-2.png
Also, check the user records in the Security Account Manager (SAM) database:
passwordreset_mount-3.png
6. Edit the SAM database with the command:
Then type 1 (for Edit user data and passwords ):
passwordreset_username-1.png
And type your user account name (i.e., Archit-PC in this example) for the username:
passwordreset_username-2.png
7. Type 1 to clear the user password or 2 to set a new password for the Archit-PC user, then quit and save the changes:
passwordreset_clear-1.png
passwordreset_clear-2.png
8. Reboot to Windows. If you selected 1 above, you’ll see there’s no password required to log in. Just click Sign in and you will be logged in:
passwordreset_nopass-1.png
passwordreset_nopass-2.png
That’s all there is to it! I hope this will be helpful if you ever need to reset a Windows password.
Topics
About the author
Recommended reading
30 Comments, Register or Log in to post a comment.
It really worked
Glad to hear that!
Spotted a small glitch. Looks like the screenshot that supposed to illustrate the execution of a mounting command, sudo mount /dev/sda2 /mnt/Microsoft/, is wrong. For me it shows the result of the execution of a chntpw command, sudo chntpw -i SAM.
Oh that’s correct, thanks for finding it!! 🙂
Archit, If you send over a revised screenshot, I can swap it out.
Thanks a lot Rikki, i’ve sent the revision 🙂
While I love Fedora clonezillia has chntpw already there.
I have clonezilla on my pxe boot arsenal.
Great, I got to give it a try!
This is great! Thanks for sharing. I have used Linux to rescue a number of crashed/trashed Windows computers. This is the most complete description I have ever seen of how to use chntpw.
Glad to hear that!! :-)😊
Superb beginning of the day 🙂 thanks for this post :+1
«3. Log out from live-user and log into root. This step is not necessary, but I prefer to use the root user to bypass any permission issues:
passwordreset_root.png
Logging in as root
4. Install the chntpw utility with the following command (you’ll need a live internet connection for this):
sudo dnf install -y chntpw»
You are saying log in as root. You don’t need sudo if you are already root.
Thanks John, that’s correct. I used this command so that a person using live-user can also execute it without any modifications, hope this makes sense. 🙂
Thanks for sharing! I have used chntpw for years. This utility can also run from Ubuntu Live CD.
There are also other free alternatives that can break a lost windows password. For instance, using Ophcrack or a Windows install disk:
http://ophcrack.sourceforge.net/
https://www.top-password.com/blog/reset-windows-10-password-with-sticky-.
Oh cool, thanks for sharing, will definitely try these out! 🙂
Thanks for the tip, might come handy! BTW you don’t need to use sudo if you’re already working as root.
Wow! Didn’t know about this. Nice article!
Thanks for the great tutorial. More grease to your elbows.
This only works if your Windows drive is not encrypted. If you have encrypted it using the storage option of Windows, you won’t even be able to mount the volume correctly and edit its content from an external tool to clear the password stored in the SAM registry file, you first need the password.
It may also not work if the encryption password comes from the TPE module which won’t allow you to boot from the external drive which was not first allowed to run as it was not signed.
But anyway it’s good to signal users that their Windwos password is not a real protection for their data, and that it can be easily cleared in most cases: suppose your PC is stolen (or seized by the police/justice. ), they know what they can do easily to enter your drive and get access to all the contents.
Also clearing a password this way may invalidate all access tokens that allow you to use some remote sites or storage that will need a new authorization, because the SAM database will no longer have the necessary access tokens.Your PC will then be «disconnected» from a secure corporate domain and you’ll need to contact the domain admin to reauthorize your PC (and fbefore they accept to reconnect you they’ll want to inspect your PC, and may force you to resintall it completely).
So don’t do that to bypass the protections that have been set in a corporate domain against such personal use of a PC you don’t really own and have no right to adminsiter yourself.
Wow, thanks for the very useful info!! Totally agree about the disk encryption and thanks for sharing about TPE, didnt know it! :))
I thought we can just rename cmd to sethc and press ctrl alt del when reboot windows.
I havent tried this yet, but the article specifies how to reset it with Linux, so keeping the scope limited to Linux 🙂
Why using sudo, when you are with root?
nice review, and very crystal clear steps! Great JOB!
I guess i was looking to provide universal steps irrespective of user, so sudo would be useful for non-root users. Thanks :))