- SOLVED: Windows 10 Won’t Install or Download Updates
- Repair Corrupt System Files
- Solution 1: Run the Windows Update Troubleshooter
- Solution 2: Ensure that all services related to Windows Update are running
- Solution 3: Using a Registry Tweak to reset Windows Update
- Solution 4: Fix the issue via an elevated Command Prompt
- Solution 5: Turn OFF Metered Connection
- 2019 SHA-2 Code Signing Support requirement for Windows and WSUS
- Summary
- Background details
- Product update schedule
- Current status
- Windows 7 SP1 and Windows Server 2008 R2 SP1
- Windows Server 2008 SP2
- Frequently Ask Questions
- General information, planning and issue prevention
- Issue recovery
SOLVED: Windows 10 Won’t Install or Download Updates
While Windows 10 is the latest and greatest iteration of the Windows Operating System in existence, it is far from perfect. That being the case, Microsoft periodically rolls out tons of updates for both Windows 10 and the programs and applications that it contains. Unlike with older versions of Windows, however, all updates rolled out to Windows 10 computers via Windows Update are mandatory and are automatically downloaded and installed at one time or another. Regardless of the important status of an update and regardless of whether or not you want to install it, it will eventually be downloaded and installed, although you do have the power to delay the occurrence slightly.
Some Windows 10 users, unfortunately, have been and continue to be affected by an issue where their computers accumulate tons of pending updates, some of which are marked as waiting to be downloaded, some marked as waiting to be installed, but none actually being downloaded or installed no matter how many times affected users try to download and install them. When users affected by this issue go into Windows Update, they see a list of all of the updates available for their computer but are unable to download and/or install any of them even though some are marked as waiting to be downloaded and some waiting to be installed.
Thankfully, though, this problem is not a dead-end problem and can be fixed by pretty simple means. The following are the three most effective solutions that you can use to try and fix this problem:
Repair Corrupt System Files
Download and run Restoro to scan for corrupt files from here, if files are found to be corrupt and missing repair them and then check if it fixes the issue, if not then proceed with Solutions listed below.
Before you Proceed: Make sure to leave the process for at least an hour or two to make sure that Windows isn’t just initializing updates.
Solution 1: Run the Windows Update Troubleshooter
If a Windows 10 component is not working or behaving the way it is supposed to, what you need to do is simply run Windows 10’s built-in Troubleshooting utility, but run it specifically for the component that is malfunctioning. The same applies to Windows Update – since Windows Update is behaving strangely, the first solution you should try out is running the Windows Update Troubleshooter. To do so, you need to:
- Open the Control Panel.
- Switch to Icons
- Click on Troubleshooting.
- Click on View all in the left pane.
- Click on Windows Update.
- Click on Next, and then proceed with the troubleshooter all the way through to the end, following the on-screen instructions along the way.
The Troubleshooter will try to identify any and all problems with Windows Update and fix any problems that it finds. Once you have successfully run the Troubleshooter, you should restart your computer and try downloading and installing Windows Updates once it boots up to see whether or not the issue still persists.
Solution 2: Ensure that all services related to Windows Update are running
You may be facing this Windows Update issue if one or more of the services pertaining to Windows Update is either not enabled or are not running on your computer. If that is the case, this issue can be easily remedied by making sure that all Windows Update-related services are enabled and running.
- Hold down the Windows Logo key, and while doing so, press R to open a Run
- Type services.msc into the Run dialog and press Enter.
- Locate and right-click on the Windows Update service, and click on Properties.
- Set the service’s Startup type to Automatic, if the service is stopped, click on Start to start it, click on Apply and then click on OK.
- Locate and right-click on the Background Intelligent Transfer Service (BITS), and click on Properties.
- Repeat step 4.
- Locate and right-click on the Cryptographic Service, and click on Properties.
- Repeat step 4.
Close the utility, restart your computer and check to see whether or not the problem has been fixed once it boots up.
Solution 3: Using a Registry Tweak to reset Windows Update
If the solutions provided above doesn’t fix your problem there is a possibility that registry keys are corrupted or modified there is a Registry Tweak that you can try, basically it will reset the Windows Update‘s registry keys and set them to default which can potentially fix the issue you are having.
- Click hereto download the Registry Tweak.
- Wait for the Registry Tweak to be downloaded.
- Navigate to where the Tweak was downloaded to and double-click on it to run it.
- There will be a pop-up asking “Are you sure you want to continue?” Press “Yes”
- Now press ok.
- Restart your Computer then check to see if the issue still persists.
Solution 4: Fix the issue via an elevated Command Prompt
If none of the solutions listed and described above have worked for you, you may just be able to fix this issue through an elevated Command Prompt. In order to do so, you need to:
- Right-click on the Start Menu button to open the WinX Menu.
- Click on Command Prompt (Admin).
- One by one, type the following commands into the elevated Command Prompt, pressing Enter after typing in each one and waiting for one command to be executed fully before typing in the next:
Once all of the commands listed above have been fully executed, close the Command Prompt and restart your computer.
Check whether or not you are now able to download and install updates via Windows Update once your computer boots up.
Solution 5: Turn OFF Metered Connection
In some cases, the internet connection that you are using might be set up as a metered connection due to which the download restriction might be implemented on it. Therefore, in this step, we will be turning this metered connection OFF and then check to see if the issue still persists. For that:
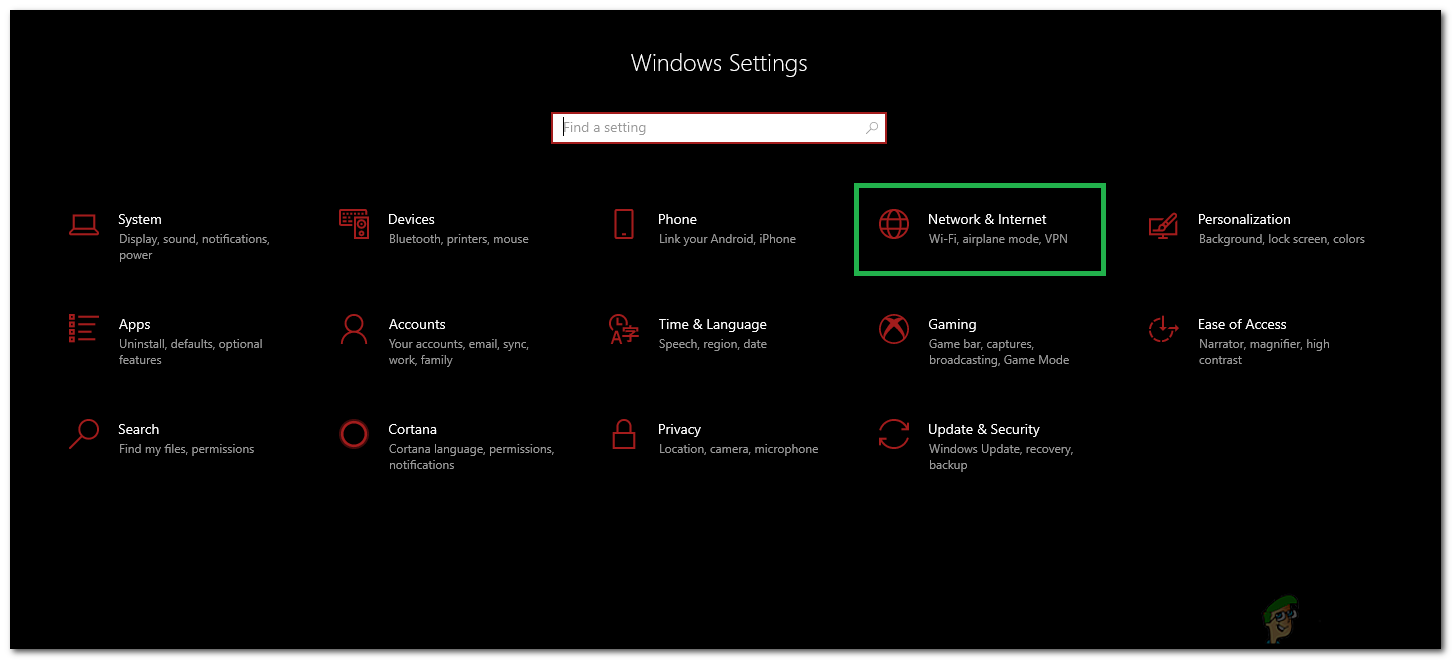
- Press “Windows” + “I” to open settings.
- Click on the “Networkand Internet” option.
Selecting “Network and Internet” Options
- Click on the “Wifi” option on the left pane and select “Manage known Networks” in the next window.
Accessing the Manage known networks menu
- Click on the Wifi name in the next window and select “Properties”.
- Click on the “Toggle” for “Set as Metered Connection” to turn it off.
- Check to see if the issue persists.
2019 SHA-2 Code Signing Support requirement for Windows and WSUS
Summary
To help protect the security of the Windows operating system, updates were previously signed (using both the SHA-1 and SHA-2 hash algorithms). The signatures are used to authenticate that the updates come directly from Microsoft and were not tampered with during delivery. Because of weaknesses in the SHA-1 algorithm and to align to industry standards, we have changed the signing of Windows updates to use the more secure SHA-2 algorithm exclusively. This change was done in phases starting in April 2019 through September 2019 to allow for smooth migration (see the «Product update schedule» section for more details on the changes).
Customers who run legacy OS versions (Windows 7 SP1, Windows Server 2008 R2 SP1 and Windows Server 2008 SP2) are required to have SHA-2 code signing support installed on their devices to install updates released on or after July 2019. Any devices without SHA-2 support will not be able to install Windows updates on or after July 2019. To help prepare you for this change, we released support for SHA-2 signing in starting March 2019 and have made incremental improvements. Windows Server Update Services (WSUS) 3.0 SP2 will receive SHA-2 support to securely deliver SHA-2 signed updates. Please see the «Product update schedule» section for the SHA-2 only migration timeline.
Background details
The Secure Hash Algorithm 1 (SHA-1) was developed as an irreversible hashing function and is widely used as a part of code-signing. Unfortunately, the security of the SHA-1 hash algorithm has become less secure over time because of the weaknesses found in the algorithm, increased processor performance, and the advent of cloud computing. Stronger alternatives such as the Secure Hash Algorithm 2 (SHA-2) are now strongly preferred as they do not experience the same issues. For more information about of the deprecation of SHA-1, see Hash and Signature Algorithms.
Product update schedule
Starting in early 2019, the migration process to SHA-2 support began in stages, and support will be delivered in standalone updates. Microsoft is targeting the following schedule to offer SHA-2 support. Please note that the following timeline is subject to change. We will continue to update this page as needed.
Stand Alone security updates KB4474419 and KB4490628 released to introduce SHA-2 code sign support.
Windows 7 SP1
Windows Server 2008 R2 SP1
Stand Alone update, KB4484071 is available on Windows Update Catalog for WSUS 3.0 SP2 that supports delivering SHA-2 signed updates. For those customers using WSUS 3.0 SP2, this update should be manually installed no later than June 18, 2019.
Stand Alone update, KB4493730 that introduce SHA-2 code sign support for the servicing stack (SSU) was released as a security update.
Windows Server 2008 SP2
Stand Alone security update KB4474419 released to introduce SHA-2 code sign support.
Windows Server 2008 SP2
Stand Alone security update KB4474419re-released to add missing MSI SHA-2 code sign support.
Windows Server 2008 SP2
Windows 10 updates signatures changed from dual signed (SHA-1/SHA-2) to SHA-2 only. No customer action required.
Windows 10, version 1709
Windows 10, version 1803
Windows 10, version 1809
Windows Server 2019
Required: For those customers using WSUS 3.0 SP2, KB4484071 must be manually installed by this date to support SHA-2 updates.
Required: Updates for legacy Windows versions will require that SHA-2 code signing support be installed. The support released in April and May (KB4493730 and KB4474419) will be required in order to continue to receive updates on these versions of Windows.
All legacy Windows updates signatures changed from SHA1 and dual signed (SHA-1/SHA-2) to SHA-2 only at this time.
Windows Server 2008 SP2
Windows 10 updates signatures changed from dual signed (SHA-1/SHA-2) to SHA-2 only. No customer action required.
Windows 10, version 1507
Windows 10, version 1607
Windows Server 2016
Windows 10, version 1703
Required: Updates for legacy Windows versions will require that SHA-2 code signing support be installed. The support released in March (KB4474419 and KB4490628) will be required in order to continue to receive updates on these versions of Windows. If you have a device or VM using EFI boot, please see the FAQ section for additional steps to prevent an issue in which your device may not start.
All legacy Windows updates signatures changed from SHA-1 and dual signed (SHA-1/SHA-2) to SHA-2 only at this time.
Windows 7 SP1
Windows Server 2008 R2 SP1
September 10, 2019
Legacy Windows update signatures changed from dual-signed (SHA-1/SHA-2) to SHA-2 only. No customer action required.
Windows Server 2012
Windows 8.1
Windows Server 2012 R2
September 10, 2019
Stand Alone security update KB4474419 was re-released to add missing EFI boot mangers. Please make sure that this version is installed.
Windows 7 SP1
Windows Server 2008 R2 SP1
Windows Server 2008 SP2
January 28, 2020
Signatures on the Certificate Trust Lists (CTLs) for the Microsoft Trusted Root Program changed from dual-signed (SHA-1/SHA-2) to SHA-2 only. No customer action required.
All supported Windows platforms
Windows Update SHA-1 based service endpoints are discontinued. This only impacts older Windows devices which have not updated with appropriate security updates. For more information, see KB4569557.
Windows 7
Windows 7 SP1
Windows Server 2008
Windows Server 2008 SP2
Windows Server 2008 R2
Windows Server 2008 R2 SP1
Microsoft retired content that is Windows-signed for Secure Hash Algorithm 1 (SHA-1) from the Microsoft Download Center. For more information, see the Windows IT pro blog SHA-1 Windows content to be retired August 3, 2020.
Windows Server 2000
Windows XP
Windows Server 2003
Windows Vista
Windows Server 2008
Windows 7
Windows Server 2008 R2
Windows 8
Windows Server 2012
Windows 8.1
Windows Server 2012 R2
Windows 10
Windows 10 Server
Current status
Windows 7 SP1 and Windows Server 2008 R2 SP1
The following required updates must be installed and then the device restarted before installing any update released August 13, 2019 or later. The required updates can be installed in any order and do not need to be reinstalled, unless there is a new version of the required update.
Servicing stack update (SSU) (KB4490628). If you use Windows Update, the required SSU will be offered to you automatically.
SHA-2 update (KB4474419) released September 10, 2019. If you use Windows Update, the required SHA-2 update will be offered to you automatically.
Important You must restart your device after installing all the required updates, before installing any Monthly Rollup, Security-only update, Preview of Monthly Rollup, or standalone update.
Windows Server 2008 SP2
The following updates must be installed and then the device restarted before installing any Rollup released September 10, 2019 or later. The required updates can be installed in any order and do not need to be reinstalled, unless there is a new version of the required update.
Servicing stack update (SSU) (KB4493730). If you use Windows Update, the required SSU update will be offered to you automatically.
The latest SHA-2 update (KB4474419) released September 10, 2019. If you use Windows Update, the required SHA-2 update will be offered to you automatically.
Important You must restart your device after installing all the required updates, before installing any Monthly Rollup, Security-only update, Preview of Monthly Rollup, or standalone update.
Frequently Ask Questions
General information, planning and issue prevention
The SHA-2 code-signing support was shipped early to ensure that most customers would have the support well in advance of Microsoft’s change to SHA-2 signing for updates to these systems. The stand-alone updates include some additional fixes and are being made available to ensure that all of the SHA-2 updates are in a small number of easily identifiable updates. Microsoft recommends that customers that maintain system images for these OSes to apply these updates to the images.
Starting with WSUS 4.0 on Windows Server 2012, WSUS already supports SHA-2-signed updates, and no customer action is needed for these versions.
Only WSUS 3.0 SP2 needs KB4484071installed to support SHA2 only signed updates.
Assume you run Windows Server 2008 SP2. If you dual-boot with Windows Server 2008 R2 SP1/Windows 7 SP1, the boot manager for this type of system is from the Windows Server 2008 R2/Windows 7 system. In order to successfully update both of these systems to use SHA-2 support, you must first update the Windows Server 2008 R2/Windows 7 system so that the boot manager is updated to the version that supports SHA-2. Then, update the Windows Server 2008 SP2 system with SHA-2 support.
Similar to the dual-boot scenario, the Windows 7 PE environment must be updated to SHA-2 support. Then, the Windows Server 2008 SP2 system must be updated to SHA-2 support.
Run Windows setup to completion and boot into Windows prior to installing August 13, 2019 or later updates
Open an administrator command prompt window, run bcdboot.exe. This copies the boot files from the Windows directory and sets up the boot environment. See BCDBoot Command-Line Options for more details.
Before installing any additional updates, install the August 13, 2019 re-release of KB4474419 and KB4490628 for Windows 7 SP1 and Windows Server 2008 R2 SP1.
Restart the operating system. This restart is required
Install any remaining updates.
Install the image on the disk and boot into Windows.
At the command prompt, run bcdboot.exe. This copies the boot files from the Windows directory and sets up the boot environment. See BCDBoot Command-Line Options for more details.
Before installing any additional updates, install the September 23, 2019 re-release of KB4474419 and KB4490628 for Windows 7 SP1 and Windows Server 2008 R2 SP1.
Restart the operating system. This restart is required
Install any remaining updates.
Yes, you will need to install the required updates before proceeding: SSU (KB4490628) and SHA-2 update (KB4474419). Also, you are required to restart your device after installing the required updates before installing any further updates.
Windows 10, version 1903 supports SHA-2 since it’s release and all updates are already SHA-2 only signed. There is no action needed for this version of Windows.
Windows 7 SP1 and Windows Server 2008 R2 SP1
Boot into Windows prior to installing any August 13, 2019 or later updates.
Before installing any additional updates, install the September 23, 2019 re-release of KB4474419 and KB4490628for Windows 7 SP1 and Windows Server 2008 R2 SP1.
Restart the operating system. This restart is required
Install any remaining updates.
Windows Server 2008 SP2
Boot into Windows prior to installing any July 9, 2019 or later updates.
Before installing any additional updates, install the September 23, 2019 re-release of KB4474419 and KB4493730 for Windows Server 2008 SP2.
Restart the operating system. This restart is required
Install any remaining updates.
Issue recovery
If you are seeing error 0xc0000428 with the message “Windows cannot verify the digital signature for this file. A recent hardware or software change might have installed a file that is signed incorrectly or damaged, or that might be malicious software from an unknown source.” please follow these steps to recover.
Start the operating system using recovery media.
Before installing any additional updates, install update KB4474419 that is dated September 23, 2019 or a later date using Deployment Image Servicing and Management (DISM) for Windows 7 SP1 and Windows Server 2008 R2 SP1.
At the command prompt, run bcdboot.exe. This copies the boot files from the Windows directory and sets up the boot environment. See BCDBoot Command-Line Options for more details.
Restart the operating system.
Halt deployment to other devices and do not restart any devices or VMs that have not already restarted.
Identify devices and VMs in restart pending state with updates released August 13, 2019 or later and open an elevated command prompt
Find the package identity for the update you want to remove by using the following command using the KB number for that update (replace 4512506 with the KB number you are targeting, if it is not the Monthly rollup released August 13, 2019): dism /online /get-packages | findstr 4512506
Use the following command to remove the update, replacing
with what was found in the previous command: Dism.exe /online /remove-package /packagename:
You will now need to install the required updates listed in the How to get this update section of the update you are trying to install, or the required updates listed above in the Current status section of this article.
Note Any device or VM you are currently receiving an error 0xc0000428 or that is starting into the recovery environment, you will need to follow the steps in the FAQ question for error 0xc0000428.
If you encounter these errors, you need to install the required updates listed in the How to get this update section of the update you are trying to install, or the required updates listed above in the Current status section of this article.
If you are seeing error 0xc0000428 with the message “Windows cannot verify the digital signature for this file. A recent hardware or software change might have installed a file that is signed incorrectly or damaged, or that might be malicious software from an unknown source.” please follow these steps to recover.
Start the operating system using recovery media.
Install the latest SHA-2 update (KB4474419) released on or after August 13, 2019, using Deployment Image Servicing and Management (DISM) for Windows 7 SP1 and Windows Server 2008 R2 SP1.
Reboot into the recovery media. This restart is required
At the command prompt, run bcdboot.exe. This copies the boot files from the Windows directory and sets up the boot environment. See BCDBoot Command-Line Options for more details.
Restart the operating system.
If you encounter this issue, you can mitigate this issue by opening a command prompt window and run the following command to install the update (replace the placeholder with the actual location and file name of the update):
This issue is resolved in KB4474419 released October 8, 2019. This update will install automatically from Windows Update and Windows Server Update Services (WSUS). If you need to install this update manually, you will need to use the workaround above.
Note If you previously installed KB4474419 released September 23, 2019, then you already have the latest version of this update and do not need to reinstall.

 Selecting “Network and Internet” Options
Selecting “Network and Internet” Options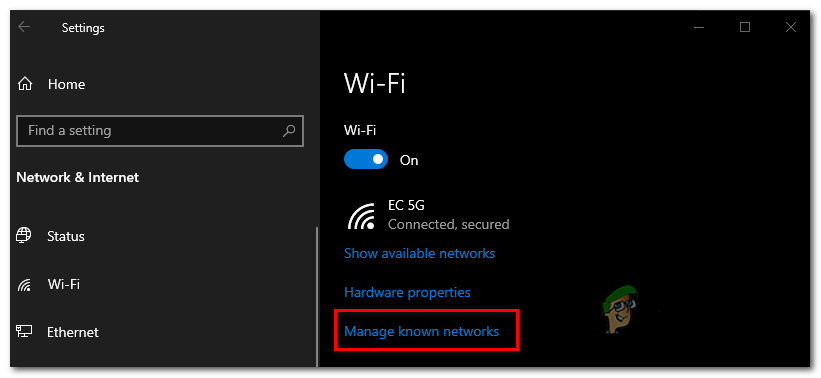 Accessing the Manage known networks menu
Accessing the Manage known networks menu


