- Tor browser linux 32bit
- Tor Browser
- Expert Bundle
- Tor Browser
- Tor Browser
- Tor (standalone)
- Android Bundle
- Source Tarball
- Want Tor to really work?
- Tor browser linux 32bit
- Tor Browser for Windows
- Tor Browser for Mac
- Tor Browser for Linux (64-Bit)
- Tor Browser for Linux (32-Bit)
- Running Tor on OpenBSD
- Orbot — Tor for Android
- Want Tor to really work?
- Where else can I get Tor?
- Tor Browser для Linux
- Руководство
- Шаг №1: Инсталляция
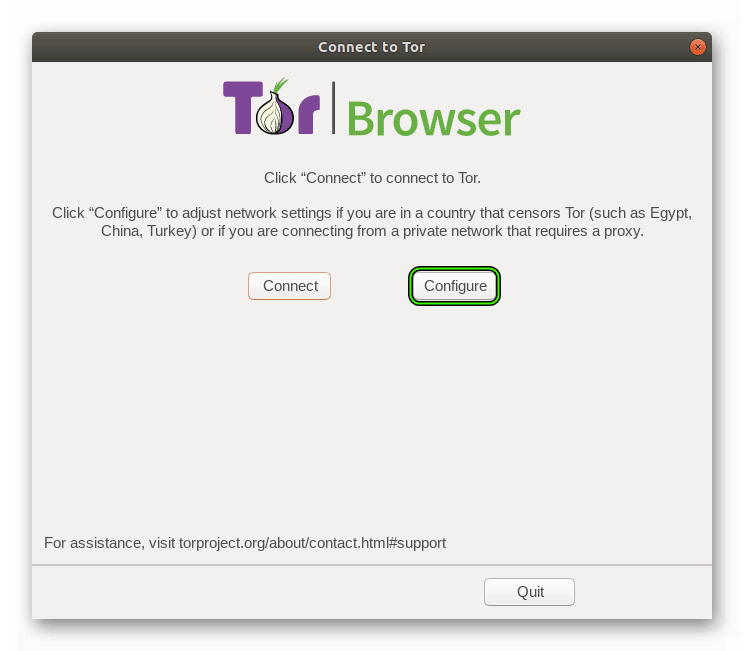
- Шаг №2: Первый запуск и настройка
- Tor browser linux 32bit
- Download Tor Browser
Tor browser linux 32bit
You need to change some of your habits, as some things won’t work exactly as you are used to. Please read the full list of warnings for details.
Tor Browser
Everything you need to safely browse the Internet. Learn more »
Expert Bundle
Contains just Tor and nothing else. You’ll need to configure Tor and all of your applications manually. This installer must be run as Administrator.
Tor Browser
Everything you need to safely browse the Internet. This package requires no installation. Just extract it and run. Learn more »
Tor Browser
Everything you need to safely browse the Internet. This package requires no installation. Just extract it and run. Learn more »
Tor (standalone)
Install the Tor components yourself, run a relay, create custom configurations. All an apt-get or yum install away.
Android Bundle
Our software is available for Android-based phones, tablets, and computers from the Guardian Project in their F-Droid Repository or the Google Play Store.
Source Tarball
Configure with: ./configure && make && src/or/tor
The current stable version of Tor is 0.3.3.7. Its release notes are available.
The current unstable/alpha version of Tor is 0.3.4.3-alpha. Its Changelog is available.
Want Tor to really work?
You need to change some of your habits, as some things won’t work exactly as you are used to.
Tor does not protect all of your computer’s Internet traffic when you run it. Tor only protects your applications that are properly configured to send their Internet traffic through Tor. To avoid problems with Tor configuration, we strongly recommend you use the Tor Browser. It is pre-configured to protect your privacy and anonymity on the web as long as you’re browsing with Tor Browser itself. Almost any other web browser configuration is likely to be unsafe to use with Tor.
Don’t torrent over Tor
Torrent file-sharing applications have been observed to ignore proxy settings and make direct connections even when they are told to use Tor. Even if your torrent application connects only through Tor, you will often send out your real IP address in the tracker GET request, because that’s how torrents work. Not only do you deanonymize your torrent traffic and your other simultaneous Tor web traffic this way, you also slow down the entire Tor network for everyone else.
Don’t enable or install browser plugins
Tor Browser will block browser plugins such as Flash, RealPlayer, Quicktime, and others: they can be manipulated into revealing your IP address. Similarly, we do not recommend installing additional addons or plugins into Tor Browser, as these may bypass Tor or otherwise harm your anonymity and privacy.
Use HTTPS versions of websites
Tor will encrypt your traffic to and within the Tor network, but the encryption of your traffic to the final destination website depends upon on that website. To help ensure private encryption to websites, Tor Browser includes HTTPS Everywhere to force the use of HTTPS encryption with major websites that support it. However, you should still watch the browser URL bar to ensure that websites you provide sensitive information to display a blue or green URL bar button, include https:// in the URL, and display the proper expected name for the website. Also see EFF’s interactive page explaining how Tor and HTTPS relate.
Don’t open documents downloaded through Tor while online
Tor Browser will warn you before automatically opening documents that are handled by external applications. DO NOT IGNORE THIS WARNING. You should be very careful when downloading documents via Tor (especially DOC and PDF files, unless you use the PDF viewer that’s built into Tor Browser) as these documents can contain Internet resources that will be downloaded outside of Tor by the application that opens them. This will reveal your non-Tor IP address. If you must work with DOC and/or PDF files, we strongly recommend either using a disconnected computer, downloading the free VirtualBox and using it with a virtual machine image with networking disabled, or using Tails. Under no circumstances is it safe to use BitTorrent and Tor together, however.
Use bridges and/or find company
Tor tries to prevent attackers from learning what destination websites you connect to. However, by default, it does not prevent somebody watching your Internet traffic from learning that you’re using Tor. If this matters to you, you can reduce this risk by configuring Tor to use a Tor bridge relay rather than connecting directly to the public Tor network. Ultimately the best protection is a social approach: the more Tor users there are near you and the more diverse their interests, the less dangerous it will be that you are one of them. Convince other people to use Tor, too!
Be smart and learn more. Understand what Tor does and does not offer. This list of pitfalls isn’t complete, and we need your help identifying and documenting all the issues.
Источник
Tor browser linux 32bit
You need to change some of your habits, as some things won’t work exactly as you are used to. Please read the full list of warnings for details.
Tor Browser for Windows
Everything you need to safely browse the Internet.
Learn more »
Not Using Windows?
Download for Mac or Linux
Tor Browser for Mac
Everything you need to safely browse the Internet.
Learn more »
Not Using Mac? Download for Windows or Linux
Tor Browser for Linux (64-Bit)
Everything you need to safely browse the Internet. This package requires no installation. Just extract it and run.
Learn more »
Not Using Linux? Download for Mac or Windows
Tor Browser for Linux (32-Bit)
Everything you need to safely browse the Internet. This package requires no installation. Just extract it and run.
Learn more »
Not Using Linux? Download for Mac or Windows
Running Tor on OpenBSD
These are installation instructions for running Tor Browser in a OpenBSD environment.
To install from OpenBSD’s packages, run:
Sometimes the most recent version of Tor Browser on OpenBSD is behind the current release. The available version of TB on OpenBSD should be checked with:
If provided version is not the current Tor Browser version, it is not recommended.
To install the Tor Browser port from an updated ports tree, run:
Orbot — Tor for Android
Our software is available for Android-based phones, tablets, and computers from the Guardian Project in their F-Droid Repository or the Google Play Store. Learn more »
Looking For Something Else? View All Downloads
Want Tor to really work?
You need to change some of your habits, as some things won’t work exactly as you are used to.
Tor does not protect all of your computer’s Internet traffic when you run it. Tor only protects your applications that are properly configured to send their Internet traffic through Tor. To avoid problems with Tor configuration, we strongly recommend you use the Tor Browser. It is pre-configured to protect your privacy and anonymity on the web as long as you’re browsing with Tor Browser itself. Almost any other web browser configuration is likely to be unsafe to use with Tor.
Don’t torrent over Tor
Torrent file-sharing applications have been observed to ignore proxy settings and make direct connections even when they are told to use Tor. Even if your torrent application connects only through Tor, you will often send out your real IP address in the tracker GET request, because that’s how torrents work. Not only do you deanonymize your torrent traffic and your other simultaneous Tor web traffic this way, you also slow down the entire Tor network for everyone else.
Don’t enable or install browser plugins
Tor Browser will block browser plugins such as Flash, RealPlayer, Quicktime, and others: they can be manipulated into revealing your IP address. Similarly, we do not recommend installing additional addons or plugins into Tor Browser, as these may bypass Tor or otherwise harm your anonymity and privacy.
Use HTTPS versions of websites
Tor will encrypt your traffic to and within the Tor network, but the encryption of your traffic to the final destination website depends upon on that website. To help ensure private encryption to websites, Tor Browser includes HTTPS Everywhere to force the use of HTTPS encryption with major websites that support it. However, you should still watch the browser URL bar to ensure that websites you provide sensitive information to display a blue or green URL bar button, include https:// in the URL, and display the proper expected name for the website. Also see EFF’s interactive page explaining how Tor and HTTPS relate.
Don’t open documents downloaded through Tor while online
Tor Browser will warn you before automatically opening documents that are handled by external applications. DO NOT IGNORE THIS WARNING. You should be very careful when downloading documents via Tor (especially DOC and PDF files, unless you use the PDF viewer that’s built into Tor Browser) as these documents can contain Internet resources that will be downloaded outside of Tor by the application that opens them. This will reveal your non-Tor IP address. If you must work with DOC and/or PDF files, we strongly recommend either using a disconnected computer, downloading the free VirtualBox and using it with a virtual machine image with networking disabled, or using Tails. Under no circumstances is it safe to use BitTorrent and Tor together, however.
Use bridges and/or find company
Tor tries to prevent attackers from learning what destination websites you connect to. However, by default, it does not prevent somebody watching your Internet traffic from learning that you’re using Tor. If this matters to you, you can reduce this risk by configuring Tor to use a Tor bridge relay rather than connecting directly to the public Tor network. Ultimately the best protection is a social approach: the more Tor users there are near you and the more diverse their interests, the less dangerous it will be that you are one of them. Convince other people to use Tor, too!
Be smart and learn more. Understand what Tor does and does not offer. This list of pitfalls isn’t complete, and we need your help identifying and documenting all the issues.
Where else can I get Tor?
In some countries the Tor Project website is blocked or censored and it is not possible to download Tor directly. The Tor Project hosts a Tor Browser mirror on Github.
Using the GetTor service is another way to download Tor Browser when the Project website and mirrors are blocked.
Источник
Tor Browser для Linux
Тор чрезвычайно ценится среди пользователей, заинтересованных в сохранении анонимности и личных данных в ходе веб-серфинга. Связано это с тем, что разработчики интернет-обозревателя сделали основной акцент на защищенности. И вполне логично, что он был в кратчайшее время портирован для операционной системы Линукс. Ведь она тоже славится своей безопасностью, при правильной эксплуатации, разумеется. Tor Browser для Linux предельно прост в инсталляции, настройке и использовании, если знать порядок действий. Специально для вашего удобства мы подготовили понятную инструкцию.
Руководство
Мы решили разбить статью на две основных части. В первой пойдет речь непосредственно о процедуре инсталляции, применимой к большинству сборок Линукс (Ubuntu, Debian и многие другие). А во второй будет рассмотрен первый запуск приложения и его настройка для правильного подключения.
Шаг №1: Инсталляция
И начнем мы именно с процедуры установки Tor Browser на Linux. Распишем ее в пошаговом варианте:
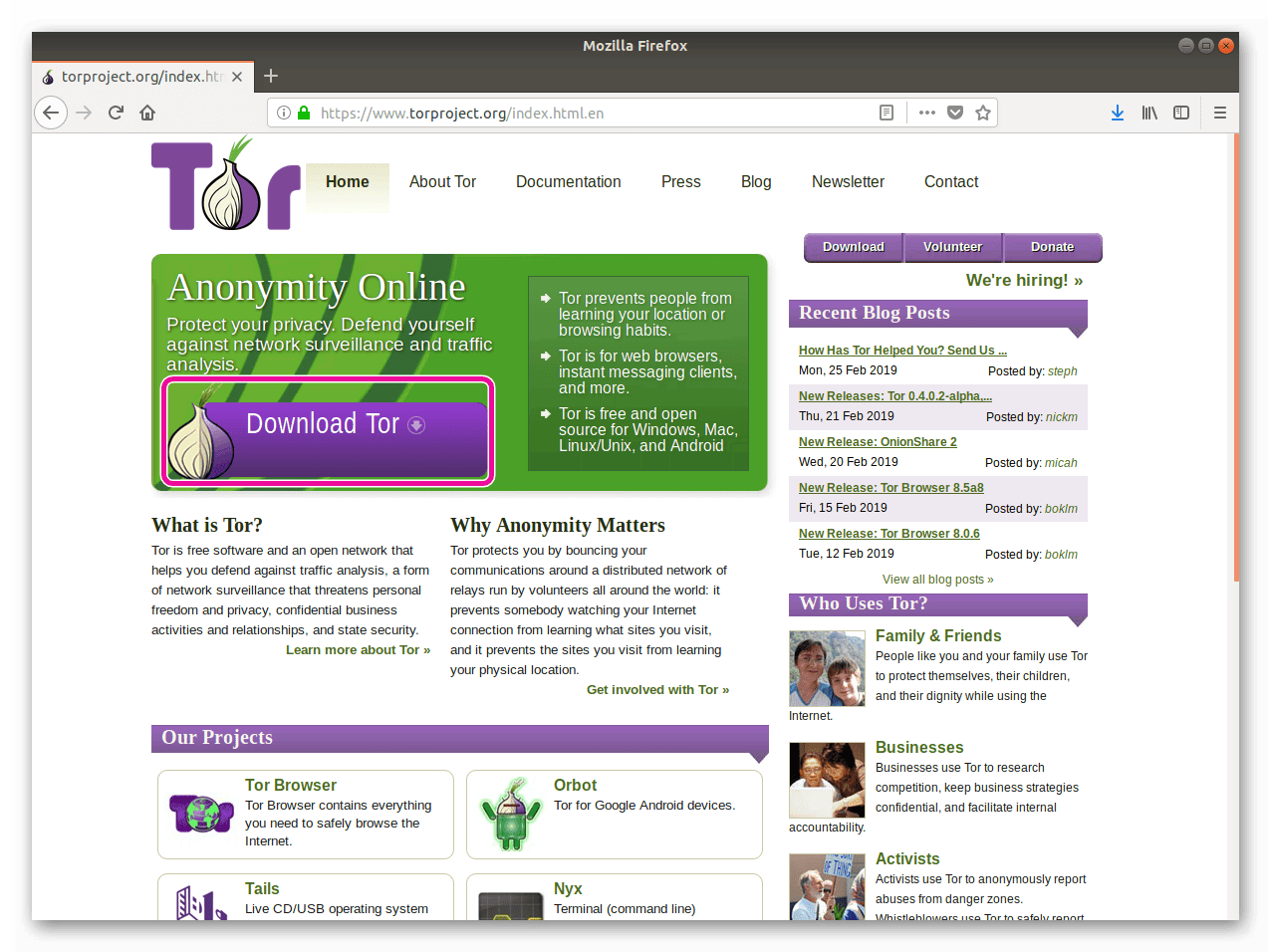
- Перейдите на официальный сайт проекта, открыв ссылку из конца статьи.
- Здесь нажмите на внушительных размеров кнопку DownloadTor.
- На новой странице загрузите подходящую версию приложения, в зависимости от разрядности операционной системы (64bit – 64-разрядная, 32bit – 32-разрядная).
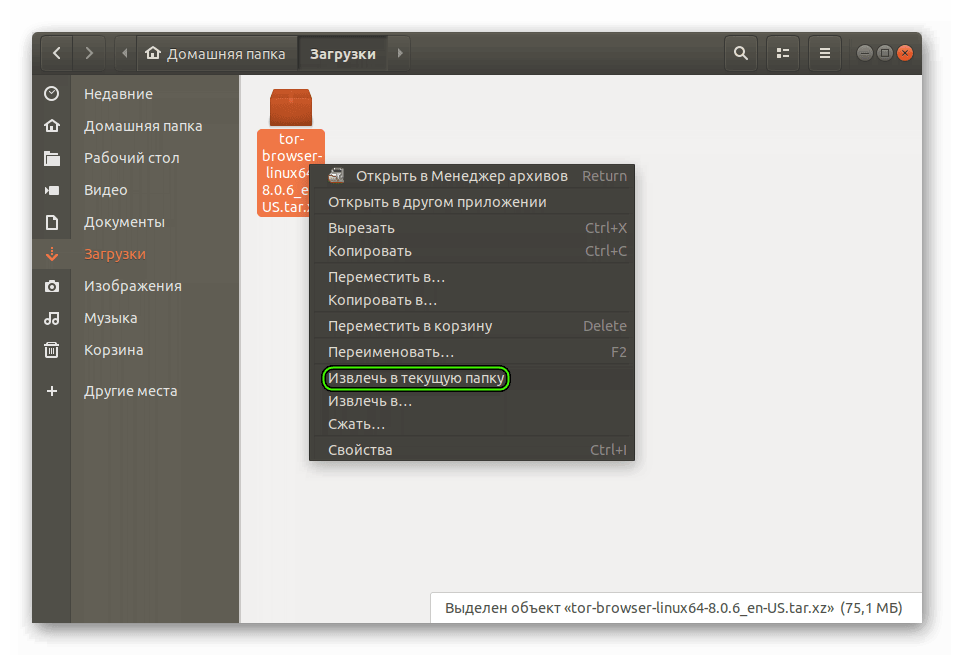
- Перейдите в каталог, куда был сохранен архив с расширением .tar.xz.
- Щелкните по нему ЛКМ и выберите опцию извлечения в текущее место.
- Дождитесь окончания распаковки.
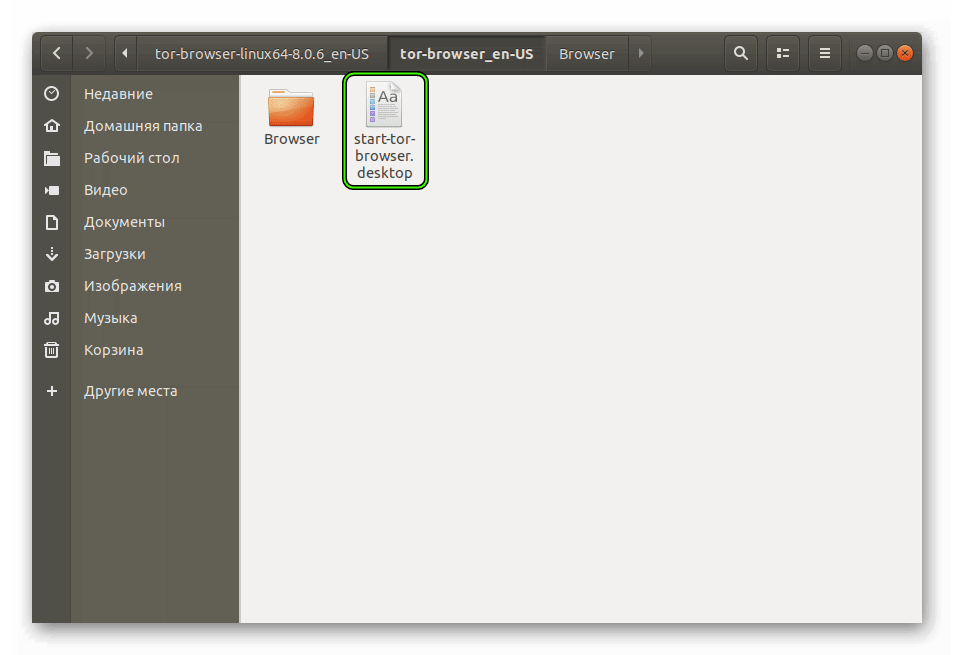
- Теперь откройте папку с названием исходного архива.
- Из нее перейдите в tor—browser—xx, где xx – исходный язык приложения (если там стоит en-US, то русский язык все равно присутствует).
- Откройте файл start-tor-browser.desktop.
- Если появится предупреждение о безопасности, то согласитесь на запуск приложения.
- Название файла сменится на TorBrowser, а его иконкой станет зелено-фиолетово-серый глобус. Вместе с тем и откроется сам интернет-обозреватель.
Шаг №2: Первый запуск и настройка
При первом запуске пользователю нужно выполнить настройку Tor для Linux. Кнопка Connect применит стандартные параметры подключения, а спустя некоторое время откроется сам интернет-обозреватель.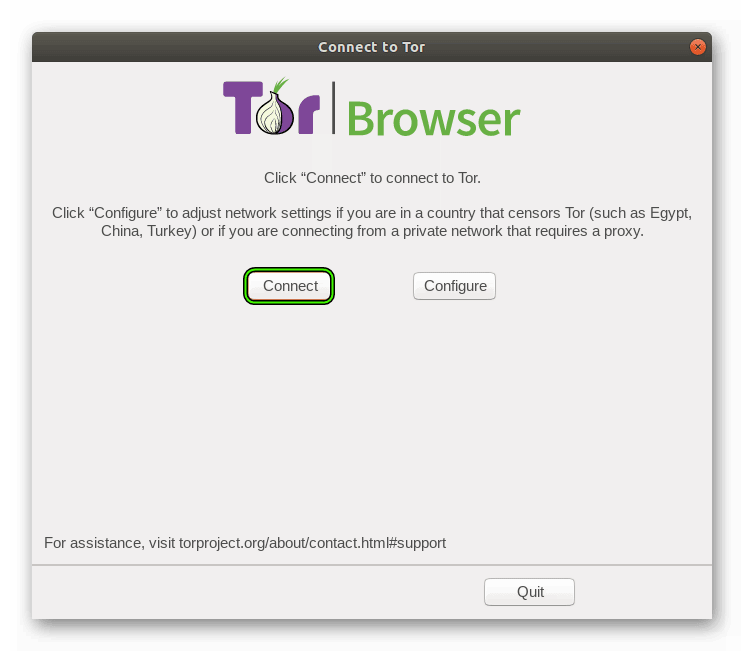
Скачать браузер Тор для Линукс на официальном сайте проекта 32-bit (sig) / 64-bit (sig)
Источник
Tor browser linux 32bit
We want everyone to be able to enjoy Tor Browser in their own language. Tor Browser is now available in 36 different languages, and we are working to add more. Want to help us translate? See here
| Language | Windows | macOS | GNU/Linux |
|---|---|---|---|
| English (en) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Ш№Ш±ШЁЩЉШ© (ar) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| CatalГ (ca) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| ДЌesky (cs) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Dansk (da) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Deutsch (de) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| О•О»О»О·ОЅО№ОєО¬ (el) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| EspaГ±ol (es) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| EspaГ±ol Arg. (es-AR) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| ЩЃШ§Ш±ШіЫЊ (fa) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Français (fr) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Gaeilge (ga-IE) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| ЧўЧ‘ЧЁЧ™ЧЄ (he) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Magyar nyelv (hu) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Indonesia (id) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Islenska (is) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Italiano (it) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| ж—Ґжњ¬иЄћ (ja) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| ქართულრენა (ka) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| н•њкµм–ґ (ko) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| lietuviЕі kalba (lt) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| македонски (mk) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| ШЁЩ‡Ш§Ші Щ…Щ„Ш§ЩЉЩ€ (ms) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| бЂ™бЂјбЂ”бЂєбЂ™бЂ¬бЂ…бЂ¬ (my) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Norsk BokmГҐl (nb-NO) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Nederlands (nl) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Polszczyzna (pl) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| PortuguГЄs Brasil(pt-BR) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| RomГўnДѓ (ro) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Р СѓСЃСЃРєРёР№ (ru) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Svenska (sv-SE) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| ภาษาไทย (th) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Türkçe (tr) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| Tiếng Việt (vi) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| з®ЂдЅ“дёж–‡ (zh-CN) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
| жЈй«”е— (zh-TW) | 32-bit (sig) / 64-bit (sig) | 64-bit (sig) | 32-bit (sig) / 64-bit (sig) |
Download Tor Browser
Download Tor Browser to experience real private browsing without tracking, surveillance, or censorship.
Our mission:
To advance human rights and freedoms by creating and deploying free and open source anonymity and privacy technologies, supporting their unrestricted availability and use, and furthering their scientific and popular understanding.
Donate Now
Subscribe to our Newsletter
Get monthly updates and opportunities from the Tor Project:
Источник