- NetworkService Account
- Учетная запись NetworkService
- Local Accounts
- About local user accounts
- Default local user accounts
- Administrator account
- Guest account
- HelpAssistant account (installed with a Remote Assistance session)
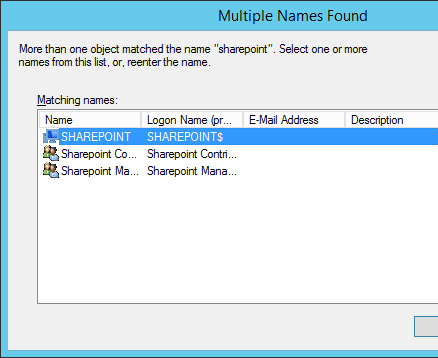
- Доступ к сетевой папке под NT AUTHORITY\NetworkService
- Как разрешить доступ к другому компьютеры под учеткой NetworkService
- А что с другими локальными аккаунтами?
NetworkService Account
The NetworkService account is a predefined local account used by the service control manager. This account is not recognized by the security subsystem, so you cannot specify its name in a call to the LookupAccountName function. It has minimum privileges on the local computer and acts as the computer on the network.
This account can be specified in a call to the CreateService and ChangeServiceConfig functions. Note that this account does not have a password, so any password information that you provide in this call is ignored. While the security subsystem localizes this account name, the SCM does not support localized names. Therefore, you will receive a localized name for this account from the LookupAccountSid function, but the name of the account must be NTВ AUTHORITY\NetworkService when you call CreateService or ChangeServiceConfig, regardless of the locale, or unexpected results can occur.
A service that runs in the context of the NetworkService account presents the computer’s credentials to remote servers. By default, the remote token contains SIDs for the Everyone and Authenticated Users groups. The user SID is created from the SECURITY_NETWORK_SERVICE_RID value.
The NetworkService account has its own subkey under the HKEY_USERS registry key. Therefore, the HKEY_CURRENT_USER registry key is associated with the NetworkService account.
The NetworkService account has the following privileges:
- SE_ASSIGNPRIMARYTOKEN_NAME (disabled)
- SE_AUDIT_NAME (disabled)
- SE_CHANGE_NOTIFY_NAME (enabled)
- SE_CREATE_GLOBAL_NAME (enabled)
- SE_IMPERSONATE_NAME (enabled)
- SE_INCREASE_QUOTA_NAME (disabled)
- SE_SHUTDOWN_NAME (disabled)
- SE_UNDOCK_NAME (disabled)
- Any privileges assigned to users and authenticated users
Учетная запись NetworkService
Учетная запись NetworkService представляет собой стандартную локальную учетную запись, используемую диспетчером управления службами. Эта учетная запись не распознается подсистемой безопасности, поэтому нельзя указать ее имя в вызове функции LookupAccountName . Он имеет минимальные права на локальном компьютере и действует как компьютер в сети.
Эту учетную запись можно указать в вызове функций CreateService и чанжесервицеконфиг . Обратите внимание, что эта учетная запись не имеет пароля, поэтому любые сведения о пароле, предоставленные в этом вызове, игнорируются. Пока подсистема безопасности локализуется таким именем учетной записи, SCM не поддерживает локализованные имена. Поэтому вы получите локализованное имя для этой учетной записи из функции LookupAccountSid , но при вызове CreateService или чанжесервицеконфиг имя учетной записи должно быть «NT Authority \ NetworkService «, независимо от языкового стандарта или непредвиденных результатов.
Служба, которая выполняется в контексте учетной записи NetworkService, представляет учетные данные компьютера удаленным серверам. По умолчанию удаленный токен содержит идентификаторы безопасности для групп «все» и «пользователи, прошедшие проверку». Идентификатор безопасности пользователя создается на основе значения _ RID сетевой _ службы _ безопасности .
Учетная запись NetworkService имеет собственный подраздел в разделе реестра hKey _ Users . Таким образом, раздел реестра hKey _ текущий _ пользователь связан с учетной записью NetworkService.
Учетная запись NetworkService имеет следующие права:
- SE _ _Имя ассигнпримаритокен (отключено)
- SE _ _Имя аудита (отключено)
- SE _ ИЗМЕНИТЬ _ _ имя уведомления (включено)
- SE _ СОЗДАТЬ _ глобальное _ имя (включено)
- SE _ _Имя олицетворения (включено)
- SE _ УВЕЛИЧИТЬ _ _ имя квоты (отключено)
- SE _ _Имя завершения работы (отключено)
- SE _ Открепить _ имя (отключено)
- Все привилегии, назначенные пользователям и прошедшим проверку пользователям
Дополнительные сведения см. в разделе Безопасность службы и права доступа.
Local Accounts
Applies to
- Windows 10
- Windows Server 2019
- Windows Server 2016
This reference topic for IT professionals describes the default local user accounts for servers, including how to manage these built-in accounts on a member or standalone server.
About local user accounts
Local user accounts are stored locally on the server. These accounts can be assigned rights and permissions on a particular server, but on that server only. Local user accounts are security principals that are used to secure and manage access to the resources on a standalone or member server for services or users.
This topic describes the following:
For information about security principals, see Security Principals.
Default local user accounts
The default local user accounts are built-in accounts that are created automatically when you install Windows.
After Windows is installed, the default local user accounts cannot be removed or deleted. In addition, default local user accounts do not provide access to network resources.
Default local user accounts are used to manage access to the local server’s resources based on the rights and permissions that are assigned to the account. The default local user accounts, and the local user accounts that you create, are located in the Users folder. The Users folder is located in the Local Users and Groups folder in the local Computer Management Microsoft Management Console (MMC). Computer Management is a collection of administrative tools that you can use to manage a single local or remote computer. For more information, see How to manage local accounts later in this topic.
Default local user accounts are described in the following sections.
Administrator account
The default local Administrator account is a user account for the system administrator. Every computer has an Administrator account (SID S-1-5-domain-500, display name Administrator). The Administrator account is the first account that is created during the Windows installation.
The Administrator account has full control of the files, directories, services, and other resources on the local computer. The Administrator account can create other local users, assign user rights, and assign permissions. The Administrator account can take control of local resources at any time simply by changing the user rights and permissions.
The default Administrator account cannot be deleted or locked out, but it can be renamed or disabled.
In Windows 10 and Windows Server 2016, Windows setup disables the built-in Administrator account and creates another local account that is a member of the Administrators group. Members of the Administrators groups can run apps with elevated permissions without using the Run as Administrator option. Fast User Switching is more secure than using Runas or different-user elevation.
Account group membership
By default, the Administrator account is installed as a member of the Administrators group on the server. It is a best practice to limit the number of users in the Administrators group because members of the Administrators group on a local server have Full Control permissions on that computer.
The Administrator account cannot be deleted or removed from the Administrators group, but it can be renamed.
Security considerations
Because the Administrator account is known to exist on many versions of the Windows operating system, it is a best practice to disable the Administrator account when possible to make it more difficult for malicious users to gain access to the server or client computer.
You can rename the Administrator account. However, a renamed Administrator account continues to use the same automatically assigned security identifier (SID), which can be discovered by malicious users. For more information about how to rename or disable a user account, see Disable or activate a local user account and Rename a local user account.
As a security best practice, use your local (non-Administrator) account to sign in and then use Run as administrator to accomplish tasks that require a higher level of rights than a standard user account. Do not use the Administrator account to sign in to your computer unless it is entirely necessary. For more information, see Run a program with administrative credentials.
In comparison, on the Windows client operating system, a user with a local user account that has Administrator rights is considered the system administrator of the client computer. The first local user account that is created during installation is placed in the local Administrators group. However, when multiple users run as local administrators, the IT staff has no control over these users or their client computers.
In this case, Group Policy can be used to enable secure settings that can control the use of the local Administrators group automatically on every server or client computer. For more information about Group Policy, see Group Policy Overview.
NoteВ В Blank passwords are not allowed in the versions designated in the Applies To list at the beginning of this topic.
ImportantВ В Even when the Administrator account has been disabled, it can still be used to gain access to a computer by using safe mode. In the Recovery Console or in safe mode, the Administrator account is automatically enabled. When normal operations are resumed, it is disabled.
Guest account
The Guest account is disabled by default on installation. The Guest account lets occasional or one-time users, who do not have an account on the computer, temporarily sign in to the local server or client computer with limited user rights. By default, the Guest account has a blank password. Because the Guest account can provide anonymous access, it is a security risk. For this reason, it is a best practice to leave the Guest account disabled, unless its use is entirely necessary.
Account group membership
By default, the Guest account is the only member of the default Guests group (SID S-1-5-32-546), which lets a user sign in to a server. On occasion, an administrator who is a member of the Administrators group can set up a user with a Guest account on one or more computers.
Security considerations
When enabling the Guest account, only grant limited rights and permissions. For security reasons, the Guest account should not be used over the network and made accessible to other computers.
In addition, the guest user in the Guest account should not be able to view the event logs. After the Guest account is enabled, it is a best practice to monitor the Guest account frequently to ensure that other users cannot use services and other resources, such as resources that were unintentionally left available by a previous user.
HelpAssistant account (installed with a Remote Assistance session)
The HelpAssistant account is a default local account that is enabled when a Remote Assistance session is run. This account is automatically disabled when no Remote Assistance requests are pending.
HelpAssistant is the primary account that is used to establish a Remote Assistance session. The Remote Assistance session is used to connect to another computer running the Windows operating system, and it is initiated by invitation. For solicited remote assistance, a user sends an invitation from their computer, through e-mail or as a file, to a person who can provide assistance. After the user’s invitation for a Remote Assistance session is accepted, the default HelpAssistant account is automatically created to give the person who provides assistance limited access to the computer. The HelpAssistant account is managed by the Remote Desktop Help Session Manager service.
Security considerations
The SIDs that pertain to the default HelpAssistant account include:
SID: S-1-5- -13, display name Terminal Server User. This group includes all users who sign in to a server with Remote Desktop Services enabled. Note that, in Windows Server 2008, Remote Desktop Services are called Terminal Services.
SID: S-1-5- -14, display name Remote Interactive Logon. This group includes all users who connect to the computer by using a remote desktop connection. This group is a subset of the Interactive group. Access tokens that contain the Remote Interactive Logon SID also contain the Interactive SID.
For the Windows Server operating system, Remote Assistance is an optional component that is not installed by default. You must install Remote Assistance before it can be used.
For details about the HelpAssistant account attributes, see the following table.
HelpAssistant account attributes
| Attribute | Value |
|---|---|