- What is a driver?
- Expanding the definition
- Software drivers
- Additional notes
- Device driver
- What devices need drivers?
- What devices may not need drivers
- What happens if a driver is not installed?
- Can a driver make my computer do more?
- What’s new in driver development
- What’s new in Windows 10, version 2004 (latest)
- Windows Drivers
- Windows Hardware Error Architecture (WHEA)
- Display and Graphics Drivers
- Storage Drivers
- Windows Debugger
- WinDbg Preview
- Stop Codes
- Driver Security
- Related Topics
- Deprecated features
- Device Drivers
- Adding Drivers
- Add drivers before deployment on an offline Windows image by using DISM
- Add drivers during an automated deployment by using WindowsВ Setup and an answer file
- Add drivers after deployment on a running operating system by using PnPUtil or an answer file
- Drivers for Windows 10 S
- Managing Driver Folders
- Understanding Driver Ranking
- Understanding Digital Signature Requirements
- Additional Resources
What is a driver?
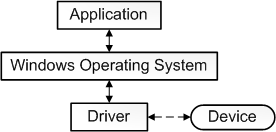
It is challenging to give a single precise definition for the term driver. In the most fundamental sense, a driver is a software component that lets the operating system and a device communicate with each other. For example, suppose an application needs to read some data from a device. The application calls a function implemented by the operating system, and the operating system calls a function implemented by the driver. The driver, which was written by the same company that designed and manufactured the device, knows how to communicate with the device hardware to get the data. After the driver gets the data from the device, it returns the data to the operating system, which returns it to the application.
Expanding the definition
Our explanation so far is oversimplified in several ways:
Not all drivers have to be written by the company that designed the device. In many cases, a device is designed according to a published hardware standard. This means that the driver can be written by Microsoft, and the device designer does not have to provide a driver.
Not all drivers communicate directly with a device. For a given I/O request (like reading data from a device), there are often several drivers, layered in a stack, that participate in the request. The conventional way to visualize the stack is with the first participant at the top and the last participant at the bottom, as shown in this diagram. Some of the drivers in the stack might participate by transforming the request from one format to another. These drivers do not communicate directly with the device; they just manipulate the request and pass the request along to drivers that are lower in the stack.
The one driver in the stack that communicates directly with the device is called the function driver; the drivers that perform auxiliary processing are called filter drivers.
Some filter drivers observe and record information about I/O requests but do not actively participate in them. For example, certain filter drivers act as verifiers to make sure the other drivers in the stack are handling the I/O request correctly.
We could expand our definition of driver by saying that a driver is any software component that observes or participates in the communication between the operating system and a device.
Software drivers
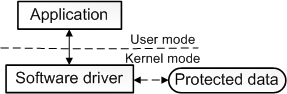
Our expanded definition is reasonably accurate but is still incomplete because some drivers are not associated with any hardware device at all. For example, suppose you need to write a tool that has access to core operating system data structures, which can be accessed only by code running in kernel mode. You can do that by splitting the tool into two components. The first component runs in user mode and presents the user interface. The second component runs in kernel mode and has access to the core operating system data. The component that runs in user mode is called an application, and the component that runs in kernel mode is called a software driver. A software driver is not associated with a hardware device. For more information about processor modes, see User Mode and Kernel Mode.
This diagram illustrates a user-mode application communicating with a kernel-mode software driver.
Additional notes
Software drivers always run in kernel mode. The main reason for writing a software driver is to gain access to protected data that is available only in kernel mode. But device drivers do not always need access to kernel-mode data and resources. So some device drivers run in user mode.
There is a category of driver we have not mentioned yet, the bus driver. To understand bus drivers, you need to understand device nodes and the device tree. For information about device trees, device nodes, and bus drivers, see Device Nodes and Device Stacks.
Our explanation so far over simplifies the definition of function driver. We said that the function driver for a device is the one driver in the stack that communicates directly with the device. This is true for a device that connects directly to the Peripheral Component Interconnect (PCI) bus. The function driver for a PCI device obtains addresses that are mapped to port and memory resources on the device. The function driver communicates directly with the device by writing to those addresses. However in many cases, a device does not connect directly to the PCI bus. Instead the device connects to a host bus adapter that is connected to the PCI bus. For example, a USB toaster connects to a host bus adapter (called a USB host controller), which is connected to the PCI bus. The USB toaster has a function driver, and the USB host controller also has a function driver. The function driver for the toaster communicates indirectly with the toaster by sending a request to the function driver for the USB host controller. The function driver for the USB host controller then communicates directly with the USB host controller hardware, which communicates with the toaster.
Device driver
More commonly known as a driver, a device driver or hardware driver is a group of files that enable one or more hardware devices to communicate with the computer’s operating system. Without drivers, the computer would not be able to send and receive data correctly to hardware devices, such as a printer.
What devices need drivers?
Hardware devices that are unknown by the operating system or that have features that are unknown by the operating system all require drivers. Below is a list of hardware devices and peripherals that require drivers.
What devices may not need drivers
Today’s operating systems have a lot of generic drivers that allow hardware to work at a basic level without needing drivers or software. However, if that device has features unknown to the operating system, it will not work without drivers. For example, you could plug any keyboard into a computer and expect it to work. However, if that keyboard has any special keys or features, they will not work until the drivers are installed.
The operating systems generic driver may not be updated as often as the drivers from a hardware manufacturer or computer manufacturer.
What happens if a driver is not installed?
If the appropriate driver is not installed, the device may not function properly, if at all. With some devices, the device may work, but all of its features may not work. For example, a computer mouse usually works without drivers, but if it has more buttons than the traditional mouse, those extra buttons will not work until the drivers are installed.
For Microsoft Windows users, missing drivers may cause a driver conflict or an error that is shown in the Device Manager. If problems or conflicts are encountered with drivers, the computer manufacturer or hardware manufacturer releases a driver update to fix the problems. If updated drivers are available, those drivers need to be installed to replace the existing driver code.
Can a driver make my computer do more?
Installing a driver only makes the hardware installed in the computer function properly. If the correct driver is not installed, installing the latest driver for the hardware can take full advantage of the device. However, you cannot install a driver for hardware not installed in the computer and expect it to make your computer faster or more capable. In other words, installing video card drivers for a video card that’s not installed in the computer does not give your computer all the capabilities of that video card. In this example, you’d need the video card hardware and the video card drivers to be installed.
What’s new in driver development
This section provides information about the new features and updates to Windows driver development in Windows 10.
What’s new in Windows 10, version 2004 (latest)
This section describes new features and updates for driver development in Windows 10, version 2004 (Windows 10 May 2020 Update).
Windows Drivers
Windows 10, version 2004 is a transition release for universal drivers. In this release, universal drivers still exist, but are being replaced by Windows Drivers. A Windows Driver is a universal driver with a few additional requirements.
Windows Drivers are distinguished from Windows Desktop Drivers. While Windows Drivers run on Windows 10X and Windows 10 Desktop editions, Windows Desktop Drivers run only on Windows 10 Desktop editions.
No changes are required to universal drivers for the version 2004 release, but documentation is available now so that you can plan ahead for upcoming changes.
For information about how to build, install, deploy, and debug a Windows Driver, see Getting Started with Windows Drivers.
Windows Hardware Error Architecture (WHEA)
WHEA includes a new interface (v2). For info about how to register as an error source and report errors, see Using WHEA on Windows 10.
Display and Graphics Drivers
Several new and enhanced display and graphics driver features are available in Windows 10, version 2004, including D3D12 mesh shader support, sampler support, raytracing extensions, video motion estimation, and video protected resources support. See What’s New for Windows 10 Display and Graphics Drivers for more details about these new features.
Storage Drivers
A storage miniport driver can now get and set more information about a device’s internal state, including the ability to reset a device. See IOCTL_STORAGE_GET_DEVICE_INTERNAL_LOG and StorPortHardwareReset as good starting points.
Windows Debugger
WinDbg Preview
Updates to WinDbg Preview to cover new features such as WinDbg Preview — Timelines. Time travel timelines allows for the visualization of time travel code execution traces.
Stop Codes
Driver Security
Updates to the Driver security checklist to use the BinSkim tool.
Related Topics
For information on what was new for drivers in past Windows releases, see the following pages:
Deprecated features
The following table describes Windows driver development features that have been removed in Windows 10.
Device Drivers
You can add device drivers to a Windows image before, during, or after you deploy the image. When planning how to add drivers to your Windows deployment, it’s important to understand how driver folders are added to the image, how driver ranking affects deployment, and the digital signature requirements for drivers.
Adding Drivers
You can add device drivers to a Windows image:
Add drivers before deployment on an offline Windows image by using DISM
Offline servicing occurs when you modify a Windows image entirely offline without booting the operating system. You can add, remove, and enumerate drivers on an offline Windows image by using the DISM command-line tool. DISM is installed with Windows and is also distributed in the Windows Assessment and Deployment Kit (WindowsВ ADK). For more information about DISM, see the DISM — Deployment Image Servicing and Management Technical Reference for Windows.
When you add a driver to an offline image, it’s either staged or reflected in the image:
Boot-critical drivers are reflected. In other words, the files are copied into the image according to what’s specified in the .inf file. The PC completes installation tasks during the initial boot, including updating the Critical Devices Database (CDDB) and the registry.
Drivers that aren’t boot critical are staged. In other words, they’re added to the driver store. After Windows starts, PnP detects the device and installs the matching driver from the driver store.
You can use DISM commands to add or remove drivers on a mounted or applied Windows or Windows Preinstallation Environment (WindowsВ PE) image.
NoteВ В You can’t use DISM to remove inbox drivers (drivers that are installed on Windows by default). You can use it only to remove third-party or out-of-box drivers.
You can also use DISM commands to apply an unattended answer file to a mounted or applied Windows image.
If you’re using DISM, you can add only .inf drivers to an offline Windows image. Drivers that display the Designed for Windows logo are provided as .cab files. You must expand the .cab file before you install the .inf file if you’re using DISM for the installation. You must install a driver that’s packaged as a .exe file or another file type on a running Windows operating system. To run a .exe or Windows Installer (.msi) driver package, you can add a custom command to an answer file to install the driver package. For more information, see Add a Custom Command to an Answer File.
Add drivers during an automated deployment by using WindowsВ Setup and an answer file
You can use an unattended answer file to add drivers to an image when you use WindowsВ Setup for deployment. In this answer file, you can specify the path of a device driver on a network share (or a local path). You accomplish this by adding the Microsoft-Windows-PnpCustomizationWinPE or Microsoft-Windows-PnpCustomizationNonWinPE components and specifying the configuration passes where you want to install them. When you run WindowsВ Setup and specify the name of the answer file, out-of-box drivers are staged (added to the driver store on the image), and boot-critical drivers are reflected (added to the image so that they’ll be used when the computer boots). Setup uses the answer file. By adding device drivers during the windowsPE or offlineServicing configuration passes, you can add out-of-box device drivers to the Windows image before the computer starts. You can also use this method to add boot-critical device drivers to a Windows image. For more information, see Add Device Drivers to Windows During Windows Setup. For more information about how WindowsВ Setup works, see the Windows Setup Technical Reference.
If you want to add boot-critical drivers to WindowsВ PE, use the windowsPE configuration pass to reflect the drivers before the WindowsВ PE image is booted. The difference between adding boot-critical drivers during the windowsPE configuration pass and adding them during the offlineServicing configuration pass is that during the windowsPE configuration pass, boot-critical drivers are reflected for WindowsВ PE to use. During the offlineServicing configuration pass, the drivers are staged to the driver store on the Windows image.
Methods for adding device drivers by using WindowsВ Setup include these:
Using an answer file to add drivers during the offlineServicing configuration pass of Setup.
Using an answer file to add drivers during the windowsPE configuration pass of Setup.
For Windows Server, placing drivers in the $WinPEDriver$ directory to be installed automatically during the windowsPE configuration pass of Setup. All drive letters with a value of C or greater are scanned for a $WinPEDriver$ directory. The drive must be accessible to the hard disk during Setup. Make sure that the drive does not require a storage driver to be loaded before it can be accessed.
For more information about these and other configuration passes, see Windows Setup Configuration Passes.
When you’re using Windows Deployment Services for deployment in Windows Server, you can add device drivers to your server and configure them to be deployed to clients as part of a network-based installation. You configure this functionality by creating a driver group on the server, adding packages to it, and then adding filters to define which clients will install those drivers. You can configure drivers to be installed based on the client’s hardware (for example, manufacturer or BIOS vendor) and the edition of the Windows image that’s selected during the installation. You can also configure whether clients install all packages in a driver group or only the drivers that match the installed hardware on the client. For more information about how to implement this functionality, see the Windows Deployment Services documentation.
Add drivers after deployment on a running operating system by using PnPUtil or an answer file
You can use the PnPUtil tool to add or remove drivers on a running operating system. Alternatively, you can use an answer file to automate the installation of the drivers when the computer is booted in audit mode. These methods can be helpful if you want to maintain a simple Windows image, and then add only the drivers that are required for a specific hardware configuration. For more information about how to use audit mode, see Boot Windows to Audit Mode or OOBE.
Methods for adding device drivers online to a running operating system include these:
Using PnPUtil to add or remove PnP drivers. For more information, see Use PnPUtil at a command line to install a Plug and Play device.
Using an answer file to automate the installation of PnP drivers when the computer is booted in audit mode. For more information, see Add a Driver Online in Audit Mode.
Drivers for Windows 10 S
Drivers in Windows 10 S must meet certain requirements. See Windows 10 S driver requirements to learn about the types of drivers you can add to Windows 10 S.
Managing Driver Folders
If you’re adding multiple drivers, you should create separate folders for each driver or driver category. This makes sure that there are no conflicts when you add drivers that have the same file name. After the driver is installed on the operating system, it’s renamed to Oem*.inf to ensure unique file names in the operating system. For example, the staged drivers named MyDriver1.inf and MyDriver2.inf are renamed to Oem0.inf and Oem1.inf after they’re installed.
When you specify a device-driver path in an answer file, all .inf drivers in the specified directory and subdirectories are added to the driver store of the Windows image, %SystemRoot%\System32\DriverStore\FileRepository. For example, if you want all of the drivers in the C:\MyDrivers\Networking, C:\MyDrivers\Video, and C:\MyDrivers\Audio directories to be available in your Windows image, specify the device-driver path, C:\MyDrivers, in your answer file. If you’re not using an answer file, you can use the /recurse command in DISM. For more information about the /recurse command, see DISM Driver Servicing Command-Line Options. This command makes sure that all drivers in each subdirectory will be added to the driver store in your Windows image.
If all drivers in the specified directory and subdirectories are added to the image, you should manage the answer file or your DISM commands and these directories carefully. Do your best to address concerns about increasing the size of the image through unnecessary driver packages.
If it isn’t practical to manage your driver shares so that only the required drivers are added to your image, you can use the Driver Package Installer (DPInst) tool to add drivers that aren’t boot critical online. DPInst selectively installs drivers that aren’t boot critical only if the hardware is present or if the driver package is a better match for the device.
Understanding Driver Ranking
One of the most common issues in deploying drivers happens when a driver is successfully imported into the driver store but, after the system is online, PnP finds a higher-ranking driver and installs that driver instead.
The WindowsВ PnP manager ranks these driver package properties in order of importance:
For example, if a device has a better PnP ID match but is unsigned, a signed driver that has a compatible ID match takes precedence. An older driver can outrank a newer driver if the older driver has a better PnP ID match or signature.
For more information about driver ranking, see How Windows Ranks Drivers.
Understanding Digital Signature Requirements
Signed device drivers are a key security feature in Windows. Drivers that are installed on x64-based computers must have a digital signature. Although it isn’t required, we recommend making sure that drivers are signed before you install them on x86-based computers.
All boot-critical drivers must contain embedded signatures. A digital signature isn’t required for Plug and Play (PnP) drivers. But when an unsigned PnP driver is installed on a running operating system, administrator credentials are required, and you can’t install such drivers on 64-bit operating systems.
There are two ways that a driver can be signed:
Kernel mode and boot-critical drivers are digitally signed via a method called embedded signing. By using embedded signatures, every binary in the driver package is signed. Embedded signatures improve boot loading performance. For drivers that are not PnP, signatures should be embedded so that they’re not lost during an upgrade of the operating system.
Digitally signed PnP drivers contain a catalog (.cat) file that’s digitally signed. The catalog file contains a hash of all the files in the driver’s .inf file for installation. A signed catalog file is all that’s required to correctly install most PnP drivers.
Either of these sources can sign drivers:
WindowsВ Hardware Quality Labs (WHQL), which makes sure that your drivers qualify for the Windows Hardware Certification Program. WHQL creates a signed driver catalog. For boot-critical drivers, you should add embedded signatures instead of relying on the catalog. Embedded signatures in boot-critical driver image files optimize boot performance of the operating system by eliminating the requirement to locate the appropriate catalog file when the operating system loader verifies the driver signature.
A certification authority (CA), by using a Software Publishing Certificate (SPC). For boot-critical and x64-based kernel drivers, Microsoft provides an additional certificate that can be used to cross-sign the drivers. Drivers that aren’t boot critical don’t have to be cross-signed by Microsoft or embedded. You can use the WindowsВ Kernel Mode Code Signing process if you need the flexibility of signing the drivers yourself. For information about digital signatures for kernel modules on x64-based systems, see 64-Bit Driver Guidelines.
For testing, you can also use test certificates.
If you have received an unsigned driver from a vendor for testing, you can use a test signature to validate the driver and to test the installation. Test signing is the act of digitally signing an application by using a private key and a corresponding code-signing certificate that’s trusted only in the confines of a test environment.
These are the primary ways to generate such test-signing certificates:
Developers can generate their own self-signed certificates.
A CA can issue certificates.
For either option, test-signing certificates must be clearly identified as appropriate only for testing. For example, the word «test» can be included in the certificate subject name, and additional legal disclaimers can be included in the certificate. Production certificates that are issued by commercial CAs must be reserved for signing only public beta releases and public final releases of software and internal line-of-business software.
When you’re adding test-signed driver packages to Windows, consider these points:
You must install the test certificates on a running operating system. You can’t install them offline.
The certificate of the CA that issued the test certificate must be inserted in the Trusted Root Certification Authorities certificate store.
Note  If the test certificate is self-signed—for example, by using the Certificate Creation Tool (MakeCert)—the test certificate must be inserted in the Trusted Root Certification Authorities certificate store.
The test certificate that’s used to sign the driver package must be inserted in the Trusted Publishers certificate store.
You must add test certificates online (to a booted instance of the Windows image) before you can use the Deployment Image Servicing and Management (DISM) command-line tool to add test-signed drivers offline.
DISM validates WHQL certifications only for boot-critical drivers. But, a DISM command-line option can override this behavior. For more information, see DISM Driver Servicing Command-Line Options.
To install and verify test-signed drivers on 64-bit operating systems, set the Windows boot configuration to test mode by using the BCDedit tool on the destination computer. Test mode verifies that the driver image is signed, but certificate path validation doesn’t require the issuer to be configured as a trusted root authority. For the PnP driver installation and ranking logic to treat the driver correctly, the test certificate must be stored in the trusted certificate store of the operating system image. For information about test mode during development, see 64-Bit Driver Guidelines.
CautionВ В If an unsigned or invalid boot-critical device driver is installed on an x64-based computer, the computer will not boot. The unsigned or invalid boot-critical device driver will cause a Stop error. You should remove the driver from either the critical device database (CDDB) or its reflected location in the image. If you’re performing an upgrade, make sure that unsigned drivers and their associated applications, services, or devices are removed or updated with a signed driver.
If you don’t enable test mode by using BCDedit, and you have a test-signed driver installed, your computer will not boot. If you use DISM to remove the driver, all instances of the reflected driver package might not be removed. So, we recommend that you don’t deploy images that have test-signed drivers installed.
Additional Resources
These websites provide more information about device-driver requirements:
For more information about PnP driver deployment, see PnP Device Installation Signing Requirements.
For more information about digital signatures and developing drivers, see the relevant page on the Windows Hardware Developer Central website.