- Linux find out which port is open using the command line
- Linux find out which port is open using the command line
- Linux find port open command
- How to find out and list of all open TCP/UDP ports in Linux
- fuser command examples to find out which port is open
- How to use lsof command to display open port on Linux
- Conclusion
- Как узнать, какой номер порта используется процессом в Linux?
- Метод-1: Использование команды ss
- Способ-2: Использование команды netstat
- Метод-3: использование команды lsof
- Метод-4: Использование команды fuser
- Метод-5: Использование команды nmap
- Метод-6: Использование команды systemctl
- Important Port numbers for the Linux system administrator
- Linux Port numbers
- Q. What is a port?
- Q. What is hardware port?
- Q. What is a socket?
- Q. What is the range of ports or how many ports are there?
- Q. Why port numbers are just 65536?
- Q. What are the well-known ports or assigned ports or default ports?
- Q. What do you mean by default port?
- Q. Can we change default port for a service(example Apache, squid)?
- Q. What are the protocol numbers for TCP and UDP?
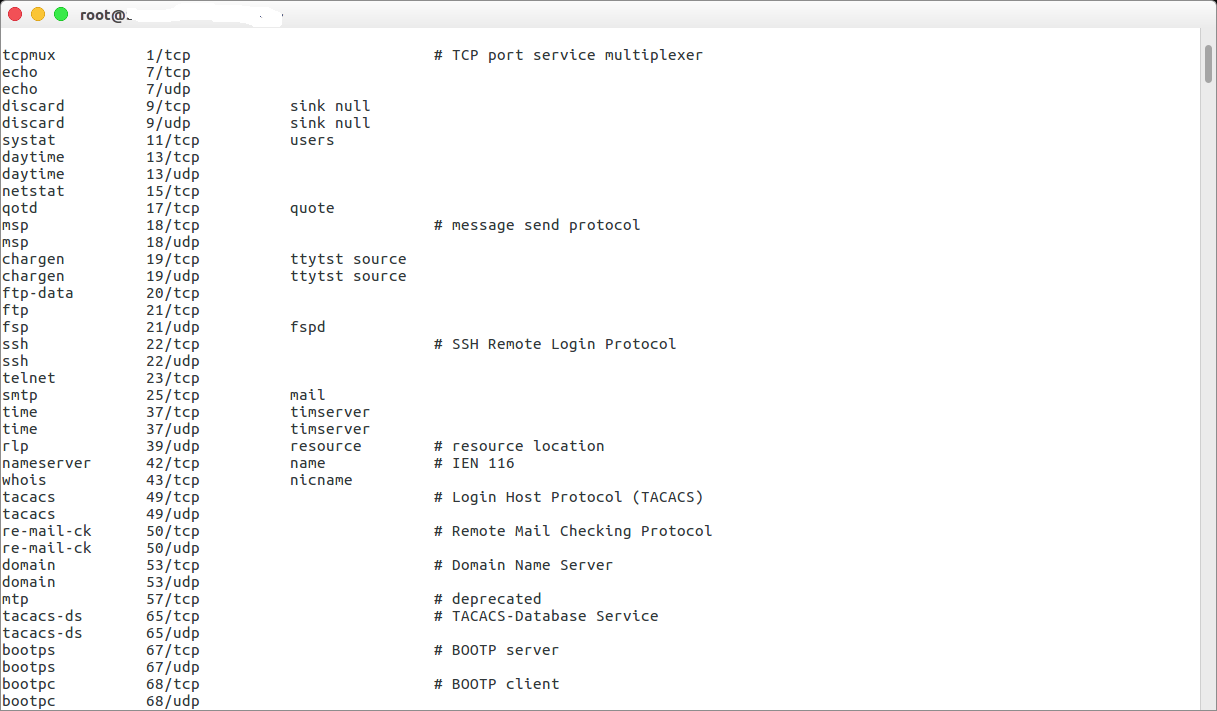
- Q. Is there any way I can see all the port information in Linux?
- Q. How can I see open ports in Linux?
- Well known ports
- Easy Steps to List All Open Linux Ports
- Linux System Ports
- Linux User Ports
- Linux Private Ports
- The netstat or network statistics command
- Retrieving a list of all TCP and UDP ports which are currently listening
- To list all the connections that are listening
- Display ports that are open, alongside current TCP connections
- A list of open UDP ports
- Get a list of your Linux services which are listening on TCP and UDP, a list of the open ports on your machine which are free, alongside the name and the PID of the service or program
- nmap – the Network Mapper command
- Scanning for open ports on a domain
- List of ports that are listening for connections via TCP
- List of ports that are listening for connections via UDP
- Look at a specific port (instead of all ports)
- Scan every open port on both TCP and UDP
- The lsof (List Open Files) command
- Listing all active network connections
- Find a process that is using a specified port
- Get a list of all the UDP and TCP connections
Linux find out which port is open using the command line
Linux find out which port is open using the command line
The procedure to list open ports in Linux is as follows:
- Open the terminal application
- Use command netstat -tulpn to open ports
- Another option is to run ss -tulpn to open ports on modern Linux distros
Let us see all commands in details.
Linux find port open command
One can use the netstat command or ss command find out which process is listing upon a port:
$ sudo netstat -tulpn
$ sudo netstat -tulpn | more
$ sudo netstat -tulpn | grep ‘:port’
$ sudo netstat -tulpn | grep ‘:22’
OR
$ sudo ss -tulpn
$ sudo ss -tulpn | more
$ sudo ss -tulpn | grep ‘:port’
$ sudo ss -tulpn | grep ‘:22’
Click to enlarge image
How to find out and list of all open TCP/UDP ports in Linux
Other commands that you can use are as follows.
fuser command examples to find out which port is open
One can list the processes PID that opened tcp port 22, enter:
$ sudo fuser 22/tcp
Sample outputs:
Let us see process name associated with PID # 1462, execute:
$ sudo ls -l /proc/1462/exe
Outputs:
/usr/sbin/sshd has opened tcp port 22. But, what is sshd? Let us find out:
$ whatis sshd
Example outputs:
How to use lsof command to display open port on Linux
$ sudo lsof -i :portNumber
$ sudo lsof -i tcp:portNumber
$ sudo lsof -i udp:portNumber
$ sudo lsof -i :22
$ sudo lsof -i :22 | grep LISTEN
Click to enlarge file
- No ads and tracking
- In-depth guides for developers and sysadmins at Opensourceflare✨
- Join my Patreon to support independent content creators and start reading latest guides:
- How to set up Redis sentinel cluster on Ubuntu or Debian Linux
- How To Set Up SSH Keys With YubiKey as two-factor authentication (U2F/FIDO2)
- How to set up Mariadb Galera cluster on Ubuntu or Debian Linux
- A podman tutorial for beginners – part I (run Linux containers without Docker and in daemonless mode)
- How to protect Linux against rogue USB devices using USBGuard
Join Patreon ➔
Conclusion
You just learned how to list open ports on a Linux based system. For more info see man pages.
🐧 Get the latest tutorials on Linux, Open Source & DevOps via
Источник
Как узнать, какой номер порта используется процессом в Linux?
Как администратор Linux, вы должны знать, является ли соответствующая служба обязательной / прослушивающей с правильным портом или нет.
Это поможет вам легко устранить проблему, когда вы столкнулись с проблемами, связанными с портами.
Порт – это логическое соединение, которое идентифицирует конкретный процесс в Linux.
Доступны два вида порта: физическое и программное обеспечение.
Поскольку операционная система Linux является программным обеспечением, мы собираемся обсудить порт программного обеспечения.
Программный порт всегда связан с IP-адресом хоста и соответствующим типом протокола для связи. Порт используется для распознования приложения.
Большинство служб, связанных с сетью, должны открыть сокет для прослушивания входящих сетевых запросов.
Socket уникален для каждого сервиса.
Сокет – это комбинация IP-адреса, программного порта и протокола.
Область номеров портов доступна для протокола TCP и UDP.
Протокол управления передачей (TCP) и протокол пользовательских дейтаграмм (UDP) используют номера портов для связи.
Это значение от 0 до 65535.
Ниже приведены категории присвоений портов.
- 0-1023: Хорошо известные порты или системные порты
- 1024-49151: Зарегистрированные порты для приложений
- 49152-65535: Динамические порты или частные порты
Вы можете проверить детали зарезервированных портов в файле /etc/services в Linux.
Это может быть достигнуто с использованием шести методов.
- ss: ss используется для вывода статистики сокетов.
- netstat: netstat отображает список открытых сокетов.
- lsof: lsof – список открытых файлов.
- fuser: идентификаторы процессов в списке терминов всех процессов, которые открывают один или несколько файлов
- nmap: nmap – Инструмент сетевого исследования и сканер безопасности / портов
- systemctl: systemctl – Управление системой systemd и менеджером сервисов
Метод-1: Использование команды ss
ss используется для вывода статистики сокетов.
Он позволяет отображать информацию, аналогичную netstat.
Он может отображать больше информации о TCP и его состоянии, чем другие инструменты.
Он может отображать статистику для всех типов сокетов, таких как PACKET, TCP, UDP, DCCP, RAW, домен Unix и т. д.
В качестве альтернативы вы также можете проверить это с помощью номера порта.
Способ-2: Использование команды netstat
netstat – вывод сетевых подключений, таблиц маршрутизации, статистики интерфейсов, соединений маскарада и многоадресной рассылки.
По умолчанию netstat отображает список открытых сокетов.
Если вы не укажете каких-либо семейств адресов, будут выведены активные сокеты всех сконфигурированных семейств адресов.
Эта программа устарела. Замена для netstat – ss.
В качестве альтернативы вы также можете проверить это с помощью номера порта.
Метод-3: использование команды lsof
lsof – список открытых файлов.
Команда lsof Linux выводит информацию о файлах, открытых для процессов, запущенных в системе.
В качестве альтернативы вы также можете проверить это с помощью номера порта.
Метод-4: Использование команды fuser
Утилита fuser должна записывать на стандартный вывод идентификаторы процессов, запущенных в локальной системе, которые открывают один или несколько именованных файлов.
Метод-5: Использование команды nmap
Nmap («Network Mapper») – это инструмент с открытым исходным кодом для проверки сети и проверки безопасности.
Он был разработан для быстрого сканирования больших сетей, хотя он отлично работает с одиночными хостами.
Nmap использует необработанные IP-пакеты в новых способах определения того, какие хосты доступны в сети, какие службы (имя и версия приложения) эти хосты предлагают, какие операционные системы (и версии ОС) они запускают, какие типы фильтров пакетов / брандмауэры используются, и десятки других характеристик
Метод-6: Использование команды systemctl
systemctl – Управление системой systemd и менеджером сервисов.
Это замена старого системного управления SysV, и большинство современных операционных систем Linux были адаптированы под systemd.
Вышеприведенный пример будет показывать фактический порт прослушивания службы SSH при запуске службы SSHD в последнее время.
В большинстве случаев вышеприведенный вывод не показывает фактический номер порта процесса. в этом случае я предлагаю вам проверить детали, используя приведенную ниже команду из файла журнала
Источник
Important Port numbers for the Linux system administrator
Linux Port numbers
This is bit important post on understanding the ports, their details and numbers.
Some FAQ related PORTS
Q. What is a port?
A port is piece of software which is used as docking point in your machine, where remote application can communicate. This is analogy to the physical ports for entering in to a country from different sea ports.
Q. What is hardware port?
This is a physical peripheral connecting point to a machine from a physical device.
Q. What is a socket?
Socket is combination of software Port and IP address.
Q. What is the range of ports or how many ports are there?
Port numbers can vary from 0 to 65535, so total we can get 65536 ports
Q. Why port numbers are just 65536?
This is because limitation in TCP/IP stack where the port number field is just 16bit size. So we get only 2^16(2 to the power of 16) ports which are equal to 65536 available ports
Q. What are the well-known ports or assigned ports or default ports?
Well known ports are from 0 to 1023(total 2^10=1024 ports)
Q. What do you mean by default port?
Default port is a designated port for particular well-known service such as web server, mail server, ftp server etc. By default FTP uses 21 port, DNS uses 53 and Apache uses 80 port.
Q. Can we change default port for a service(example Apache, squid)?
Yes, we can change. In Apache and DNS we can change this using listen configuration entry in httpd.conf and named.conf. Squid have port entry in it’s squid.conf file to mention port number.
Q. What are the protocol numbers for TCP and UDP?
Do not confuse this one with port numbers. TCP and UDP have their own numbers in TCP/IP stack.
TCP protocol number: 6
UDP protocol number: 17
Q. Is there any way I can see all the port information in Linux?
Yes, you can get that from /etc/services files.
Q. How can I see open ports in Linux?
Well known ports
20 – FTP Data (For transferring FTP data)
21 – FTP Control (For starting FTP connection)
22 – SSH (For secure remote administration which uses SSL to encrypt the transmission)
23 – Telnet (For insecure remote administration)
25 – SMTP (Mail Transfer Agent for e-mail server such as SEND mail)
53 – DNS (Special service which uses both TCP and UDP)
67 – Bootp
68 – DHCP
69 – TFTP (Trivial file transfer protocol uses udp protocol for connection less transmission of data)
80 – HTTP/WWW(Apache)
88 – Kerberos
110 – POP3 (Mail delivery Agent)
123 – NTP (Network time protocol used for time syncing uses UDP protocol)
137 – NetBIOS (nmbd)
139 – SMB-Samba (smbd)
143 – IMAP
161 – SNMP (For network monitoring)
389 – LDAP (For centralized administration)
443 – HTTPS (HTTP+SSL for secure web access)
514 – Syslogd (udp port)
636 – ldaps (both ctp and udp)
873 – rsync
989 – FTPS-data
990 – FTPS
995 – POP3s
2049 – NFS (nfsd, rpc.nfsd, rpc, portmap)
2401 – CVS server
3306 – MySql
6000-6063-X11
Note 1: If protocol(TCP or UDP) is not mention then the above port are solely for TCP. Some service use UDP as mention in above list.
Note 2: X11 use 6000 to 6063.. ports for connecting X11 from remote server.
Источник
Easy Steps to List All Open Linux Ports
If you wanted to know what you need to do to list all of the open ports in a Linux instance you’ve come to the right place. But, what is a port and why would you want to have a list of all the open ports?
In short, a port is an access point that an operating system makes available so that it can facilitate network traffic with other devices or servers, while also differentiating the traffic in order to understand what service or app the traffic is being sent to.
There are two common protocols when it comes to ports: TCP, or the transmission control protocol; and of course, UDP – the user datagram protocol. Each of these protocols have a range of port numbers which is commonly classified into three groups:
Linux System Ports
Also known as “well-known” ports. These are port numbers from 0 to 1023 which are considered important for typical system use, commonly these ports are considered quite critical for ensuring ongoing communications services.
Linux User Ports
Also know as “registered ports” which range from 1024 to 49151. It is possible to send a request to the Internet Assigned Numbers Authority (IANA) to request retention of one of these ports for your application.
Linux Private Ports
Also known as “dynamic ports” range from 49152 to 65535. These ports are open for whatever use case you deem privately necessary and so are dynamic in nature – they are not fixed to specific applications.
Now, even though many ports have specific uses, it is important to keep an eye on ports which are “open” without the need for that port to be open. This is because ports that are unnecessarily left open can be a security risk – and also a sign that an intrusion is actively occurring.
Understanding which ports are open and “listening” for communications is therefore absolutely crucial to ensuring that you block efforts to break into your systems. Of course, some common ports need to be left open in order to facilitate ordinary internet communications. For example:
- FTP (the file transfer protocol) uses port 20 for data transfers
- Likewise, FTP uses port 21 to issue commands and to control the FTP session
- Port 22 is dedicated to SSH, or secure shell login
- Telnet uses port 23 to facilitate remote logins but this port entails unencrypted messaging which is not secure so it’s not really recommended for use
- E-mail routing via SMTP (the simple mail transfer protocol) is achieved on port 25
- Port 43 is dedicated to the WHOIS system which can check who owns a domain
- The domain name service (DNS) makes use of port 53
- DHCP uses port 67 as the server port, and port 68 as the client port
- HTTP, the hypertext transfer protocol, uses port 80 to deliver web pages
- POP3, the e-mail centric “post office protocol” uses port 110
- Port 119 is used by the news transfer protocol, NNTP
- The network time protocol, NTP, uses port 123
- IMAP, another email protocol, makes use of port 143 to retrieve email messages
- SNP or the simple network management protocol uses port 161
- Port 194 is dedicated to IRC, the internet relay chat app
- Port 443 is dedicated to HTTPS, the secure version of HTTP delivered over TLS/SSL
- SMTP, the simple mail transfer protocol, uses port 587 to submit emails
It is often possible to configure a specific service to use a port which is not the standard port, but this configuration needs to be made on both the sender and recipient side – in other words, on both client and server. Otherwise if only one side uses a non-standard port configuration communication won’t be possible.
How do you get a simple list of common ports that are open? Use this command:
Alternatively, you can modify the size of the list you get by adding “less” to your command
$ cat /etc/services | less
However, you can use a range of other commands on a Linux machine which will give you all the TCP and the UDP ports which are open and ready to receive communication from other machines. We will cover three in the following section – Isof, netstat and nmap.
The netstat or network statistics command
Most Linux distributions will include netstat by default, in their installations. It’s a really capable tool which can display all the TCP/IDP network connections that are active – both for incoming connections, and outgoing connections. It also displays routing tables plus the number of the network interface alongside comprehensive statistics for network protocols.
So, you can use netstat to troubleshoot and to measure the performance of your network. While basic, it is a useful and essential too for finding faults in network services. It clearly tells you which ports are open, and where a program or service is listening on a specific port. We will now give you some examples on how to make use of netstat.
Retrieving a list of all TCP and UDP ports which are currently listening
It’s simple really, just use the -a flag alongside a pipe that specifies less, this will give you TCP and UDP ports which are currently listening
$ netstat -a | less
To list all the connections that are listening
Make use of the -l flag in the netstat command to get a list of every port connection which is actively listening
Display ports that are open, alongside current TCP connections
Here, we combine a couple of flags in order to show a list of ports which are open and the established (TCP) connections.
A list of open UDP ports
You might only want to see the UDP ports which are open, excluding the open TCP ports. The command you need is this:
Get a list of your Linux services which are listening on TCP and UDP, a list of the open ports on your machine which are free, alongside the name and the PID of the service or program
This command gives you all the services and apps which listen on either TCP or UDP. It also gives you the open ports on your Linux instance which are free, plus the program name and process ID that is associated with every open socket.
So you can see how the different commands you can use with netstat makes it very versatile, allowing you to see what the status quo is on your Linux machine. But what exactly does these individual flags mean? It’s simple really:
- -a will show all sockets that are listening and all non-listening sockets too
- -l only shows ports which are actively listening
- -v means “verbose” and tells netstat to include additional information about any address families that are not currently configured
- -t restricts the listing to TCP connections only
- -u restricts the listing to UDP connections only
- -n tells netstat to display the numerical addresses too
- -p adds the process ID (PID) as well as the name of the program
Keep in mind that the seven flags we’ve shown above are just a couple of the many flags you can specify for netstat. Check out the help file by triggering
You’ll get a full listing of all the options and features you can make use of with netstat.
nmap – the Network Mapper command
An open source tool, nmap is great for exploring your network, scanning it for security vulnerabilities and to audit your network. That said, new users might find nmap challenging to use because it is so feature-rich: nmap comes with so many options that you might find it difficult to figure out, even if it does mean it is a very robust tool.
It’s worth remembering that nmap will deliver very extensive information about the network that it is scanning. So, do not use nmap on a network unless you have permission to examine it – permission to scan it, basically. You need to have a reason to use nmap, in other words, and the permission of the network owner.
We will now give you a basic overview of nmap including typical usage of the map command. To start off with, here is the instructions you need to install nmap if you have Ubuntu or Debian server:
$ sudo apt-get install nmap
The command is slightly different if you’re using RHEL or CentOS:
$ sudo yum install nmap
There’s a file you can view for a wider picture of ports and services. Use this command:
It’s an example of exactly how extensive the details are when you use nmap as a tool. If you want to experiment with nmap you could try to check out your own virtual private server, but you could also give nmap a go on the official nmap test server – located at scanme.nmap.org.
In order to try out some basic nmap commands we will make use of sudo privileges to ensure that the queries give complete results – not partial results. Remember, some nmap commands will take a little bit longer to execute.
Throughout these examples we will make use of mywebsite.com as the example domain; replace your actual domain in place of mywebsite.com when you run this command.
Scanning for open ports on a domain
$ sudo nmap -vv mywebsite.com
Here you can see we have used the -vv flag, which has a specific function. When you use -vv it means “verbose”, in other words it will show you extensive output, including the process as nmap scans for open ports. Leave out the -vv flag and you will quickly see the difference.
List of ports that are listening for connections via TCP
$ sudo nmap -sT mywebsite.com
You’ll note the -sT flag, this is usually what you’d specify to scan for TCP connections when a SYN scan cannot be performed.
List of ports that are listening for connections via UDP
$ sudo nmap -sU mywebsite.com
So, -sU is what you use to get a UDP scan. However you can scan for both UDP and TCP connections by using another flag, -sS. You’ll get a list covering both UDP and TCP.
Look at a specific port (instead of all ports)
$ sudo nmap -p port_number mywebsite.com
In this case, -p means that you only look at the port number specified in place of “port_number”.
Scan every open port on both TCP and UDP
$ sudo nmap -n -Pn -sT -sU -p- mywebsite.com
We use two flags here: first -n which specified to nmap that it must not make a reverse domain resolution for an active IP address, where it finds one. -Pn disables pinging, treating all of the hosts as if they are online.
It’s just a few examples but nmap is a really fantastic tool than can help you a lot. Remember, typing $ man nmap will give you a full list of all the tools at your disposal; many of these are very useful for exploring the security of your network and to find potentially vulnerable points.
The lsof (List Open Files) command
It’s easy to remember what lsof means – the list open files command – just take ls as “list” and of as “open files” and you’ll clearly see why lsof means “list open files”.
Listing all active network connections
Use the -i flag with lsof in order to get a full list of every network connection which is both listening and established.
Find a process that is using a specified port
As an example, for all processes which are currently operating on port 22, you’ll run this command:
$ sudo lsof -i TCP:22
Get a list of all the UDP and TCP connections
To list every single UDP and TCP connection just use this command:
$ sudo lsof -i tcp; sudo lsof -i udp;
Just like with nmap, you can check the manual for lsof in order to get a full view of all the options you have when you are using lsof.
So, to wrap up, Linux fans must understand at least a little bit about ports – particularly if they plan on managing Linux servers. We’ve given three examples of great tools – nmap, lsof and netstat – which will help you on the way to understanding which ports are open on your machine, and which services are active on your server.
We suggest that you take a look at the man pages for each of these commands so that you can get a better idea of what they do. While these tools are great for checking the exposure on your own network, never abuse any of these tools by scanning networks that do not belong to you.
Источник