- Command line process auditing
- Overview
- Configuration
- You must have Audit Process Creation auditing enabled to see event ID 4688.
- In order to see the additions to event ID 4688, you must enable the new policy setting: Include command line in process creation events
- To ensure that Advanced Audit Policy Configuration settings are not overwritten
- Additional Resources
- Try This: Explore command line process auditing
- 4688(S): A new process has been created.
- Security Monitoring Recommendations
Command line process auditing
Applies To: Windows Server 2016, Windows Server 2012 R2
Author: Justin Turner, Senior Support Escalation Engineer with the Windows group
This content is written by a Microsoft customer support engineer, and is intended for experienced administrators and systems architects who are looking for deeper technical explanations of features and solutions in Windows Server 2012 R2 than topics on TechNet usually provide. However, it has not undergone the same editing passes, so some of the language may seem less polished than what is typically found on TechNet.
Overview
The pre-existing process creation audit event ID 4688 will now include audit information for command line processes.
It will also log SHA1/2 hash of the executable in the Applocker event log
- Application and Services Logs\Microsoft\Windows\AppLocker
You enable via GPO, but it is disabled by default
- «Include command line in process creation events»
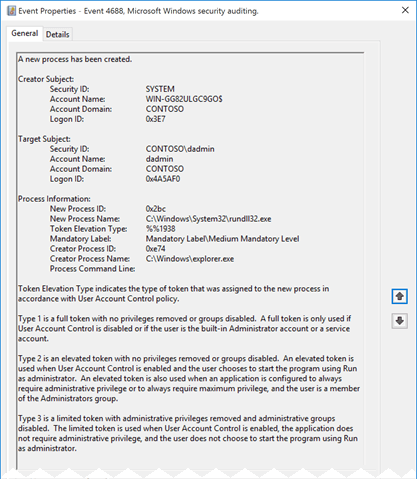
Figure SEQ Figure \* ARABIC 16 Event 4688
Review the updated event ID 4688 in REF _Ref366427278 \h Figure 16. Prior to this update none of the information for Process Command Line gets logged. Because of this additional logging we can now see that not only was the wscript.exe process started, but that it was also used to execute a VB script.
Configuration
To see the effects of this update, you will need to enable two policy settings.
You must have Audit Process Creation auditing enabled to see event ID 4688.
To enable the Audit Process Creation policy, edit the following group policy:
Policy location: Computer Configuration > Policies > Windows Settings > Security Settings > Advanced Audit Configuration > Detailed Tracking
Policy Name: Audit Process Creation
Supported on: Windows 7 and above
Description/Help:
This security policy setting determines whether the operating system generates audit events when a process is created (starts) and the name of the program or user that created it.
These audit events can help you understand how a computer is being used and to track user activity.
Event volume: Low to medium, depending on system usage
Default: Not configured
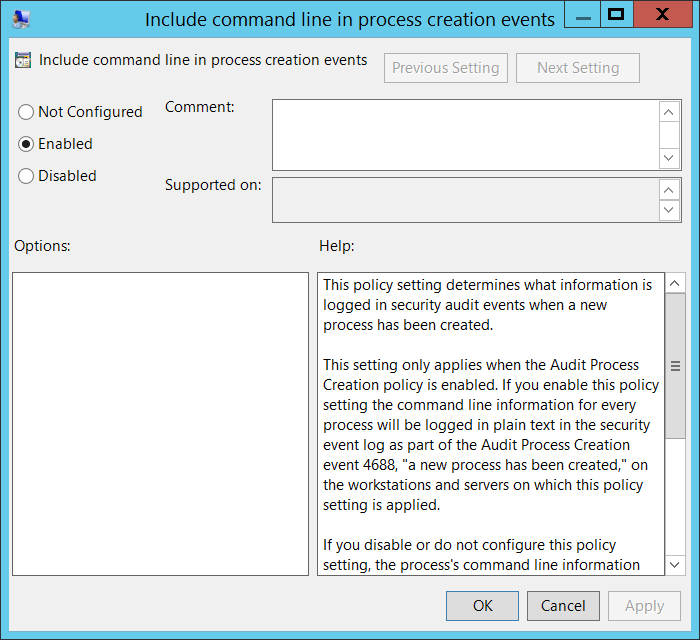
In order to see the additions to event ID 4688, you must enable the new policy setting: Include command line in process creation events
Table SEQ Table \* ARABIC 19 Command line process policy setting
| Policy Configuration | Details |
|---|---|
| Path | Administrative Templates\System\Audit Process Creation |
| Setting | Include command line in process creation events |
| Default setting | Not Configured (not enabled) |
| Supported on: | ? |
| Description | This policy setting determines what information is logged in security audit events when a new process has been created. This setting only applies when the Audit Process Creation policy is enabled. If you enable this policy setting the command line information for every process will be logged in plain text in the security event log as part of the Audit Process Creation event 4688, «a new process has been created,» on the workstations and servers on which this policy setting is applied. If you disable or do not configure this policy setting, the process’s command line information will not be included in Audit Process Creation events. Default: Not configured Note: When this policy setting is enabled, any user with access to read the security events will be able to read the command line arguments for any successfully created process. Command line arguments can contain sensitive or private information such as passwords or user data. |
When you use Advanced Audit Policy Configuration settings, you need to confirm that these settings are not overwritten by basic audit policy settings. Event 4719 is logged when the settings are overwritten.
The following procedure shows how to prevent conflicts by blocking the application of any basic audit policy settings.
To ensure that Advanced Audit Policy Configuration settings are not overwritten
Open the Group Policy Management console
Right-click Default Domain Policy, and then click Edit.
Double-click Computer Configuration, double-click Policies, and then double-click Windows Settings.
Double-click Security Settings, double-click Local Policies, and then click Security Options.
Double-click Audit: Force audit policy subcategory settings (Windows Vista or later) to override audit policy category settings, and then click Define this policy setting.
Click Enabled, and then click OK.
Additional Resources
Try This: Explore command line process auditing
Enable Audit Process Creation events and ensure the Advance Audit Policy configuration is not overwritten
Create a script that will generate some events of interest and execute the script. Observe the events. The script used to generate the event in the lesson looked like this:
Enable the command line process auditing
Execute the same script as before and observe the events
4688(S): A new process has been created.
Applies to
- Windows 10
- Windows Server 2016
Event Description:
This event generates every time a new process starts.
NoteВ В For recommendations, see Security Monitoring Recommendations for this event.
Event XML:
Required Server Roles: None.
Minimum OS Version: Windows Server 2008, Windows Vista.
Event Versions:
0 — Windows Server 2008, Windows Vista.
1 — Windows Server 2012 R2, Windows 8.1.
- Added «Process Command Line» field.
Subject renamed to Creator Subject.
Added «Target Subject» section.
Added «Mandatory Label» field.
Added «Creator Process Name» field.
Field Descriptions:
Creator Subject [Value for versions 0 and 1 – Subject]:
- Security ID [Type = SID]: SID of account that requested the «create process» operation. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
NoteВ В A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account that requested the «create process» operation.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is «NT AUTHORITY».
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: «Win81».
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, «4624: An account was successfully logged on.»
Target Subject [Version 2]:
NoteВ В This event includes the principal of the process creator, but this is not always sufficient if the target context is different from the creator context. In that situation, the subject specified in the process termination event does not match the subject in the process creation event even though both events refer to the same process ID. Therefore, in addition to including the creator of the process, we will also include the target principal when the creator and target do not share the same logon.
- Security ID [Type = SID] [Version 2]: SID of target account. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
NoteВ В A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString] [Version 2]: the name of the target account.
Account Domain [Type = UnicodeString] [Version 2]: target account’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is «NT AUTHORITY».
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: «Win81».
Logon ID [Type = HexInt64] [Version 2]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, «4624: An account was successfully logged on.»
Process Information:
New Process ID [Type = Pointer]: hexadecimal Process ID of the new process. Process ID (PID) is a number used by the operating system to uniquely identify an active process. To see the PID for a specific process you can, for example, use Task Manager (Details tab, PID column):
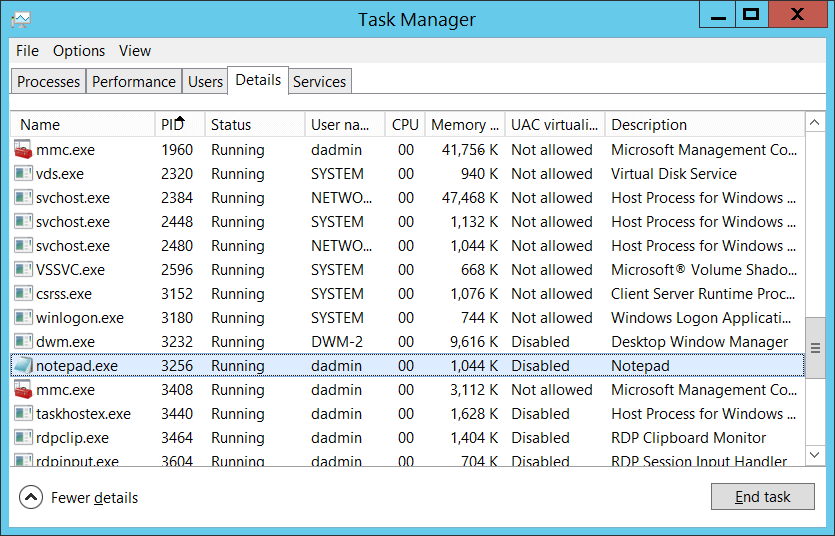
If you convert the hexadecimal value to decimal, you can compare it to the values in Task Manager.
New Process Name [Type = UnicodeString]: full path and the name of the executable for the new process.
Token Elevation Type [Type = UnicodeString]:
TokenElevationTypeDefault (1): Type 1 is a full token with no privileges removed or groups disabled. A full token is only used if User Account Control is disabled or if the user is the built-in Administrator account (for which UAC disabled by default), service account or local system account.
TokenElevationTypeFull (2): Type 2 is an elevated token with no privileges removed or groups disabled. An elevated token is used when User Account Control is enabled and the user chooses to start the program using Run as administrator. An elevated token is also used when an application is configured to always require administrative privilege or to always require maximum privilege, and the user is a member of the Administrators group.
TokenElevationTypeLimited (3): Type 3 is a limited token with administrative privileges removed and administrative groups disabled. The limited token is used when User Account Control is enabled, the application does not require administrative privilege, and the user does not choose to start the program using Run as administrator.
Mandatory Label [Version 2] [Type = SID]: SID of integrity label which was assigned to the new process. Can have one of the following values:
| SID | RID | RID label | Meaning |
|---|---|---|---|
| S-1-16-0 | 0x00000000 | SECURITY_MANDATORY_UNTRUSTED_RID | Untrusted. |
| S-1-16-4096 | 0x00001000 | SECURITY_MANDATORY_LOW_RID | Low integrity. |
| S-1-16-8192 | 0x00002000 | SECURITY_MANDATORY_MEDIUM_RID | Medium integrity. |
| S-1-16-8448 | 0x00002100 | SECURITY_MANDATORY_MEDIUM_PLUS_RID | Medium high integrity. |
| S-1-16-12288 | 0X00003000 | SECURITY_MANDATORY_HIGH_RID | High integrity. |
| S-1-16-16384 | 0x00004000 | SECURITY_MANDATORY_SYSTEM_RID | System integrity. |
| S-1-16-20480 | 0x00005000 | SECURITY_MANDATORY_PROTECTED_PROCESS_RID | Protected process. |
- Creator Process ID [Type = Pointer]: hexadecimal Process ID of the process which ran the new process. If you convert the hexadecimal value to decimal, you can compare it to the values in Task Manager.
You can also correlate this process ID with a process ID in other events, for example, «4688: A new process has been created» Process Information\New Process ID.
Creator Process Name [Version 2] [Type = UnicodeString]: full path and the name of the executable for the process.
Process Command Line [Version 1, 2] [Type = UnicodeString]: contains the name of executable and arguments which were passed to it. You must enable «Administrative Templates\System\Audit Process Creation\Include command line in process creation events» group policy to include command line in process creation events:
By default Process Command Line field is empty.
Security Monitoring Recommendations
For 4688(S): A new process has been created.
| Type of monitoring required | Recommendation |
|---|---|
| High-value accounts: You might have high-value domain or local accounts for which you need to monitor each action. Examples of high-value accounts are database administrators, built-in local administrator account, domain administrators, service accounts, domain controller accounts and so on. | Monitor all events with the «Creator Subject\Security ID» or «Target Subject\Security ID» that corresponds to the high-value account or accounts. |
| Anomalies or malicious actions: You might have specific requirements for detecting anomalies or monitoring potential malicious actions. For example, you might need to monitor for use of an account outside of working hours. | When you monitor for anomalies or malicious actions, use the «Creator Subject\Security ID» or «Target Subject\Security ID» (with other information) to monitor how or when a particular account is being used. |
| Non-active accounts: You might have non-active, disabled, or guest accounts, or other accounts that should never be used. | Monitor all events with the «Creator Subject\Security ID» or «Target Subject\Security ID» that corresponds to the accounts that should never be used. |
| Account whitelist: You might have a specific allow list of accounts that are the only ones allowed to perform actions corresponding to particular events. | If this event corresponds to a «whitelist-only» action, review the «Creator Subject\Security ID» and «Target Subject\Security ID» for accounts that are outside the allow list. |
| Accounts of different types: You might want to ensure that certain actions are performed only by certain account types, for example, local or domain account, machine or user account, vendor or employee account, and so on. | If this event corresponds to an action you want to monitor for certain account types, review the «Creator Subject\Security ID» or «Target Subject\Security ID» to see whether the account type is as expected. |
| External accounts: You might be monitoring accounts from another domain, or «external» accounts that are not allowed to perform certain actions (represented by certain specific events). | Monitor the specific events for the «Creator Subject\Security ID» or «Target Subject\Security ID» corresponding to accounts from another domain or «external» accounts. |
| Restricted-use computers or devices: You might have certain computers, machines, or devices on which certain people (accounts) should not typically perform any actions. | Monitor the target Computer: (or other target device) for actions performed by the «Creator Subject\Security ID» or «Target Subject\Security ID» that you are concerned about. |
| Account naming conventions: Your organization might have specific naming conventions for account names. | Monitor «Creator Subject\Security ID» or «Target Subject\Security ID» for names that don’t comply with naming conventions. |
If you have a pre-defined «New Process Name» or «Creator Process Name» for the process reported in this event, monitor all events with «New Process Name» or «Creator Process Name» not equal to your defined value.
You can monitor to see if «New Process Name» or «Creator Process Name» is not in a standard folder (for example, not in System32 or Program Files) or is in a restricted folder (for example, Temporary Internet Files).
If you have a pre-defined list of restricted substrings or words in process names (for example «mimikatz» or «cain.exe«), check for these substrings in «New Process Name» or «Creator Process Name.»
It can be unusual for a process to run using a local account in either Creator Subject\Security ID or in Target Subject\Security ID.
Monitor for Token Elevation Type with value TokenElevationTypeDefault (1) when Subject\Security ID lists a real user account, for example when Account Name doesn’t contain the $ symbol. Typically this means that UAC is disabled for this account for some reason.
Monitor for Token Elevation Type with value TokenElevationTypeDefault (2) on standard workstations, when Subject\Security ID lists a real user account, for example when Account Name doesn’t contain the $ symbol. This means that a user ran a program using administrative privileges.
You can also monitor for Token Elevation Type with value TokenElevationTypeDefault (2) on standard workstations, when a computer object was used to run the process, but that computer object is not the same computer where the event occurs.
If you need to monitor all new processes with a specific Mandatory Label, for example S-1-16-20480 (Protected process), check the «Mandatory Label» in this event.