- Catalog Files and Digital Signatures
- Guidelines for Catalog Files
- Digital Signatures
- Digital Signatures
- Add or remove a digital signature in Office files
- In this article
- What is a digital signature?
- Signing certificate and certificate authority
- What does a digital signature guarantee?
- Signature lines in Word and Excel
- Create a signature line in Word or Excel
- Sign the signature line in Word or Excel
- Remove digital signatures from Word or Excel
- Invisible digital signatures in Word, Excel, or PowerPoint
- Add invisible digital signatures in Word, Excel, or PowerPoint
- Remove invisible digital signatures from Word, Excel, or PowerPoint
Catalog Files and Digital Signatures
A digitally-signed catalog file (.cat) can be used as a digital signature for an arbitrary collection of files. A catalog file contains a collection of cryptographic hashes, or thumbprints. Each thumbprint corresponds to a file that is included in the collection.
Plug and Play (PnP) device installation recognizes the signed catalog file of a driver package as the digital signature for the driver package, where each thumbprint in the catalog file corresponds to a file that is installed by the driver package. Regardless of the intended operating system, cryptographic technology is used to digitally-sign the catalog file.
PnP device installation considers the digital signature of a driver package to be invalid if any file in the driver package is altered after the driver package was signed. Such files include the INF file, the catalog file, and all files that are copied by INF CopyFiles directives. For example, even a single-byte change to correct a misspelling invalidates the digital signature. If the digital signature is invalid, you must either resubmit the driver package to the Windows Hardware Quality Labs (WHQL) for a new signature or generate a new Authenticode signature for the driver package.
Similarly, changes to a device’s hardware or firmware require a revised device ID value so that the system can detect the updated device and install the correct driver. Because the revised device ID value must appear in the INF file, you must either resubmit the package to WHQL for a new signature or generate a new Authenticode signature for the driver package. You must do this even if the driver binaries do not change.
The CatalogFile directive in the INF Version section of the driver’s INF file specifies the name of the catalog file for the driver package. During driver installation, the operating system uses the CatalogFile directive to identify and validate the catalog file. The system copies the catalog file to the %SystemRoot%\CatRoot directory and the INF file to the %SystemRoot%\Inf directory.
Guidelines for Catalog Files
Starting with Windows 2000, if the driver package installs the same binaries on all versions of Windows, the INF file can contain a single, undecorated CatalogFile directive. However, if the package installs different binaries for different versions of Windows, the INF file should contain decorated CatalogFile directives. For more information about the CatalogFile directive, see INF Version Section.
If you have more than one driver package, you should create a separate catalog file for each driver package and give each catalog file a unique file name. Two unrelated driver packages cannot share a single catalog file. However, a single driver package that serves multiple devices requires only one catalog file.
Digital Signatures
Digital signatures are based on Microsoft public key infrastructure technology, which is based on Microsoft Authenticode combined with an infrastructure of trusted certification authorities (CAs). Authenticode, which is based on industry standards, allows vendors, or software publishers, to sign either a file or a collection of files (such as a driver package) by using a code-signing digital certificate that is issued by a CA.
Windows uses a valid digital signature to verify the following:
The file, or the collection of files, is signed.
The signer is trusted.
The certification authority that authenticated the signer is trusted.
The collection of files was not altered after it was published.
For example, this signing process for a driver package involves the following:
A publisher obtains an X.509 digital certificate from a CA. An Authenticode certificate is also referred to as a signing certificate. A signing certificate is a set of data that identifies a publisher, and is issued by a CA only after the CA has verified the identity of the publisher. A CA can be a Microsoft CA, a third-party commercial CA, or an Enterprise CA.
The signing certificate is used to sign the catalog file of a driver package or to embed a signature in a driver file. Certificates that identify trusted publishers and trusted CAs are installed in certificate stores that are maintained by Windows.
The signing certificate includes a private key and a public key, which is known as the key pair. The private key is used to sign the catalog file of a driver package or to embed a signature in a driver file. The public key is used to verify the signature of a driver package’s catalog file or a signature that is embedded in a driver file.
To sign a catalog file or to embed a signature in a file, the signing process first generates a cryptographic hash, or thumbprint, of the file. The signing process then encrypts the file thumbprint with a private key and adds the thumbprint to the file.
The signing process also adds information about the publisher and the CA that issued the signing certificate. The digital signature is added to the file in a section of the file that is not processed when the file thumbprint is generated.
To verify the digital signature of a file, Windows extracts the information about the publisher and the CA and uses the public key to decrypt the encrypted file thumbprint.
Windows accepts the integrity of the file and the authenticity of the publisher only if the following are true:
- The decrypted thumbprint matches the thumbprint of the file.
- The certificate of the publisher is installed in the Trusted Publishers certificate store.
- The root certificate of the CA that issued the publisher’s certificate is installed in the Trusted Root Certification Authorities certificate store.
For more information about how the Plug and Play (PnP) device installation uses the digital signature of a driver package’sВ catalog file, see Digital Signatures and PnP Device Installation.
For more information about Microsoft public key infrastructure technology, code signing, and digital signatures, see Introduction to Code Signing and Code Signing Best Practices.
Digital Signatures
Digital signatures can be used to distribute a message in plaintext form when the recipients must identify and verify the message sender. Signing a message does not alter the message; it simply generates a digital signature string you can either bundle with the message or transmit separately. A digital signature is a short piece of data that is encrypted with the sender’s private key. Decrypting the signature data using the sender’s public key proves that the data was encrypted by the sender or by someone who had access to the sender’s private key.
Digital signatures are generated by using public key signature algorithms. A private key generates the signature, and the corresponding public key must be used to validate the signature. This process is shown in the following illustration.
There are two steps involved in creating a digital signature from a message. The first step involves creating a hash value (also known as a message digest) from the message. This hash value is then signed, using the signer’s private key. The following is an illustration of the steps involved in creating a digital signature.
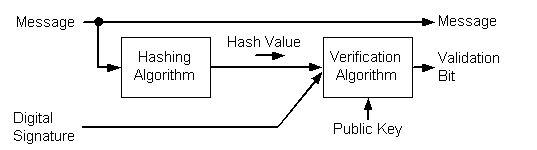
To verify a signature, both the message and the signature are required. First, a hash value must be created from the message in the same way the signature was created. This hash value is then verified against the signature by using the public key of the signer. If the hash value and the signature match, you can be confident that the message is indeed the one the signer originally signed and that it has not been tampered with. The following diagram illustrates the process involved in verifying a digital signature.
A hash value consists of a small amount of binary data, typically around 160 bits. This is produced by using a hashing algorithm. A number of these algorithms are listed later in this section.
All hash values share the following properties, regardless of the algorithm used:
- The length of the hash value is determined by the type of algorithm used, and its length does not vary with the size of the message. The most common hash value lengths are either 128 or 160 bits.
- Every pair of non-identical messages translates into a completely different hash value, even if the two messages differ only by a single bit. Using today’s technology, it is not feasible to discover a pair of messages that translate to the same hash value without breaking the hashing algorithm.
- Each time a particular message is hashed using the same algorithm, the same hash value is produced.
- All hashing algorithms are one-way. Given a hash value, it is not possible to recover the original message. In fact, none of the properties of the original message can be determined given the hash value alone.
Add or remove a digital signature in Office files
This article explains digital signatures (also known as digital ID), what they can be used for, and how you can use digital signatures in the following Microsoft Office programs: Word, Excel, and PowerPoint.
In this article
What is a digital signature?
A digital signature is an electronic, encrypted, stamp of authentication on digital information such as e-mail messages, macros, or electronic documents. A signature confirms that the information originated from the signer and has not been altered.
Signing certificate and certificate authority
Signing certificate To create a digital signature, you have to have a signing certificate, which proves identity. When you send a digitally-signed macro or document, you also send your certificate and public key. Certificates are issued by a certification authority, and like a driver’s license, can be revoked. A certificate is usually valid for a year, after which, the signer must renew, or get a new, a signing certificate to establish identity.
Note: You can learn more about public and private keys in this article.
Certificate authority (CA) A certificate authority is an entity similar to a notary public. It issues digital certificates, signs certificates to verify their validity and tracks which certificates have been revoked or have expired.
Tip: For more information on obtaining a digital certificate see Obtain a digital certificate and create a digital signature.
What does a digital signature guarantee?
Authenticity The signer is confirmed as the signer.
Integrity The content has not been changed or tampered with since it was digitally signed.
Non-repudiation Proves to all parties the origin of the signed content. Repudiation refers to the act of a signer denying any association with the signed content.
Notarization Signatures in Word, Excel, or PowerPoint files, which are time stamped by a secure time-stamp server, under certain circumstances, have the validity of a notarization.
To make these assurances, the content creator must digitally sign the content by using a signature that satisfies the following criteria:
The digital signature is valid.
The certificate associated with the digital signature is current (not expired).
The signing person or organization, known as the publisher, is trusted.
Important: Signed documents, which have a valid time stamp, are considered to have valid signatures, regardless of the age, or revocation status, of the signing certificate.
The certificate associated with the digital signature is issued to the signing publisher by a reputable certificate authority (CA).
Signature lines in Word and Excel
A signature line resembles a typical signature placeholder that might appear in a printed document. However, it works differently. When a signature line is inserted into an Office file, the author can specify information about the intended signer, and instructions for the signer. When an electronic copy of the file is sent to the intended signer, this person sees the signature line and a notification that their signature is requested. The signer can:
Type a signature, or
Select a picture of an inked signature, or
Write a signature by using the inking feature of a touch-screen PC
When the signer adds a visible representation of a signature to the document, a digital signature is added at the same time to authenticate the signer’s identity.
Important: A digitally-signed document becomes read-only to prevent modifications.
Create a signature line in Word or Excel
In the document or worksheet, place your pointer where you want to create a signature line.
On the Insert tab, in the Text group, click the Signature Line list, and then click Microsoft Office Signature Line.
In the Signature Setup dialog box, type information that will appear beneath the signature line:
Suggested signer The signer’s full name.
Suggested signer’s title The signer’s title, if any.
Suggested signer’s e-mail address The signer’s e-mail address, if needed.
Instructions to the signer Add instructions for the signer, such as «Before signing the document, verify that the content is correct.»
Select one or both of the following check boxes:
Allow the signer to add comments in the Sign dialog box Allow the signer to type a purpose for signing.
Show sign date in signature line The date the document was signed will appear with the signature.
Tip: To add additional signature lines, repeat these steps.
Note: If the document remains unsigned, the Signatures Message Bar appears. Click View Signatures to complete the signature process.
Sign the signature line in Word or Excel
When you sign a signature line, you add a visible representation of your signature and a digital signature.
In the file, right-click the signature line.
Note: If the file opens in Protected View, click Edit Anyway, if the file is from a reliable source.
From the menu, select Sign.
To add a printed version of your signature, type your name in the box next to the X.
To select an image of your written signature, click Select Image. In the Select Signature Image dialog box, find the location of your signature image file, select the file that you want, and then click Select.
For customers using Chinese- (Traditional or Simplified), Korean-, or Japanese-language versions, the Stamp Signature Line option appears.
In addition, you can sign a signature line by double-clicking the signature line. Type your name next to the X. Or, in the Signature Pane, in the Requested Signatures section, click the arrow next to the signature. From the menu, select Sign.
To add a handwritten signature (Tablet PC users only), sign your name in the box next to the X by using the inking feature.
The Signatures button appears at the bottom of the document or worksheet.
The following image shows the Signatures button.
Remove digital signatures from Word or Excel
Open the document or worksheet that contains the visible signature you want to remove.
Right-click the signature line.
Click Remove Signature.
Note: In addition, you can remove a signature by clicking the arrow next to the signature in the Signature Pane. Click Remove Signature.
Invisible digital signatures in Word, Excel, or PowerPoint
An invisible digital signature, such as a visible digital signature line, assures the authenticity, integrity, and origin of a document. You can add invisible digital signatures to Word documents, Excel workbooks, and PowerPoint presentations.
Signed documents will have the Signatures button at the bottom of the document. In addition, for signed documents, signature information appears in the Info section that you see after you click the File tab.
Add invisible digital signatures in Word, Excel, or PowerPoint
To protect the authenticity of a document’s content, you can add an invisible digital signature. Signed documents have the Signatures button at the bottom of the document.
Click the File tab.
Click Protect Document, Protect Workbook or Protect Presentation.
Click Add a Digital Signature.
Read the Word, Excel, or PowerPoint message, and then click OK.
In the Sign dialog box, in the Purpose for signing this document box, type the purpose.
After a file is digitally signed, the Signatures button appears, and the file becomes read-only to prevent modifications.
Remove invisible digital signatures from Word, Excel, or PowerPoint
Open the document, worksheet, or presentation that contains the invisible signature you want to remove.
Click the File tab.
Click View Signatures.
The document, worksheet, or presentation view returns, and the Signatures pane appears.
Next to the signature name, click the arrow.