- How to open firewall ports in Windows 10 [Step-by-step guide]
- How do I open a port on my firewall?
- Why should I use a Firewall on my PC?
- Configure Firewall Port Requirements for Group Policy
- Remote Resultant Set of Policy (RSoP) Group Policy results: ports that require firewall rules
- Configure firewall rules by creating a GPO from the Group Policy Reporting Firewall Ports Starter GPO and linking to the domain
- To create a GPO from the Group Policy Reporting Firewall Ports Starter GPO and link to the domain
- Remote Group Policy refresh: ports that require firewall rules
- Configure firewall rules by creating a GPO from the Group Policy Remote Update Firewall Ports Starter GPO and linking to the domain
- To create a GPO from the Group Policy Remote Update Firewall Ports Starter GPO and link to the domain
- Создание правила порта для входящего трафика Create an Inbound Port Rule
How to open firewall ports in Windows 10 [Step-by-step guide]
If you’re looking for a simple solution for opening firewall ports in Windows 10, you’ll find all the necessary details in this article.
Opening Firewall ports allows apps and programs to communicate with the network. So, if some of your apps and programs fail to launch, opening firewall ports is one of the first troubleshooting solutions that you can use.
How do I open a port on my firewall?
Users can manually allow a program to get access to the Internet by opening a firewall port. All you need to know is what port it uses and the protocol to make this function.
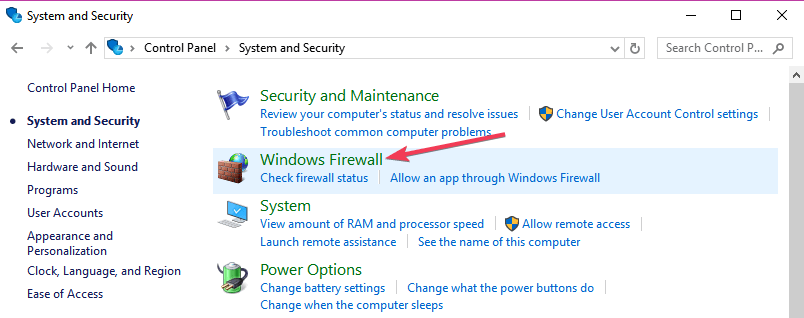
- Go to Control Panel> System and Security > Windows Firewall.
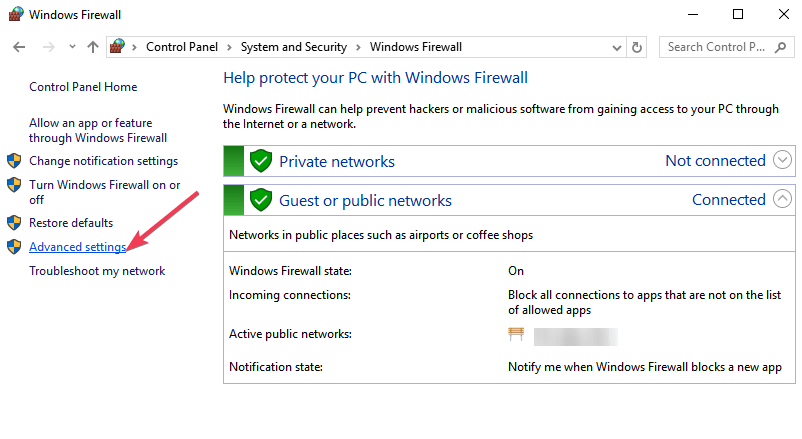
- Go to Advanced settings
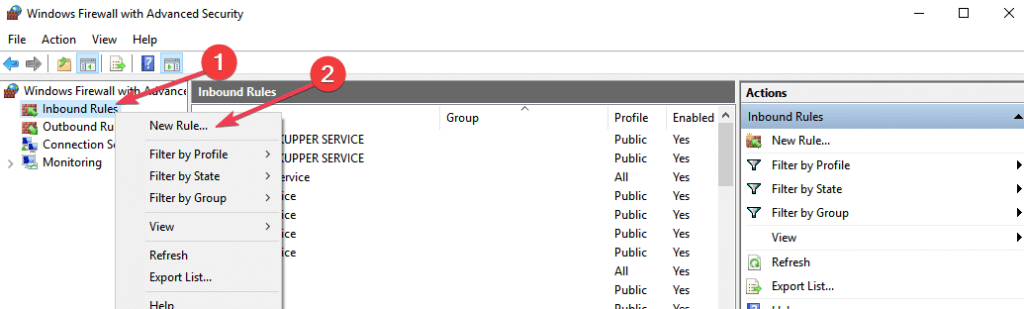
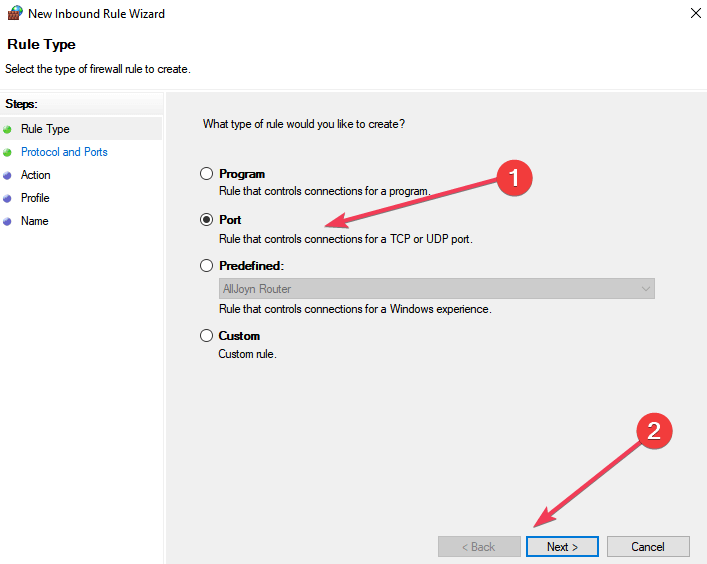
- Right-click Inbound Rules > select New Rule.
- Add the port you want to open > click Next.
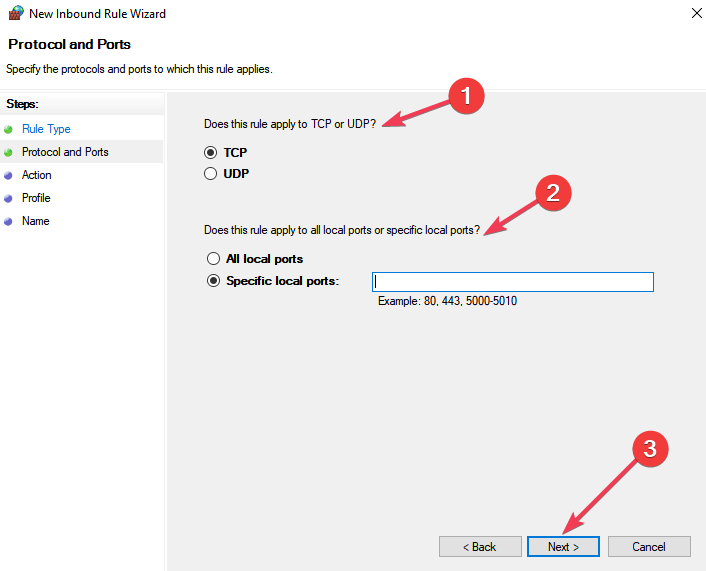
- Add the TCP or UDP protocol and the port number into the next window > click Next.
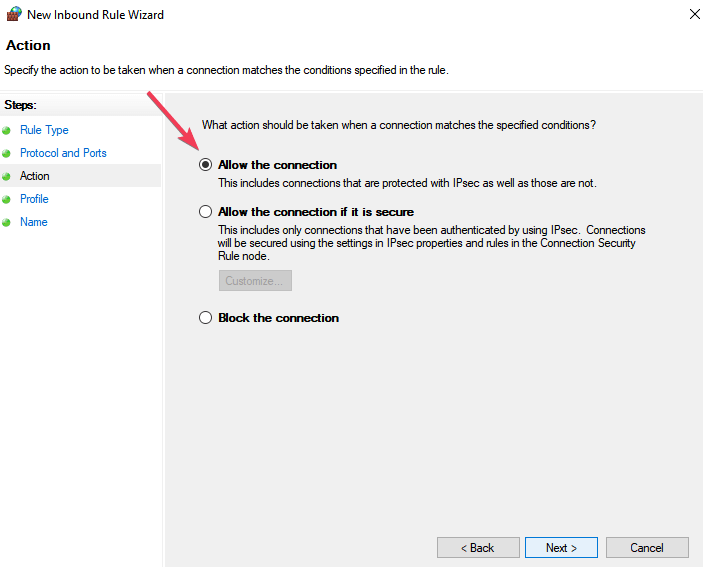
- Select Allow the connection > hit Next.
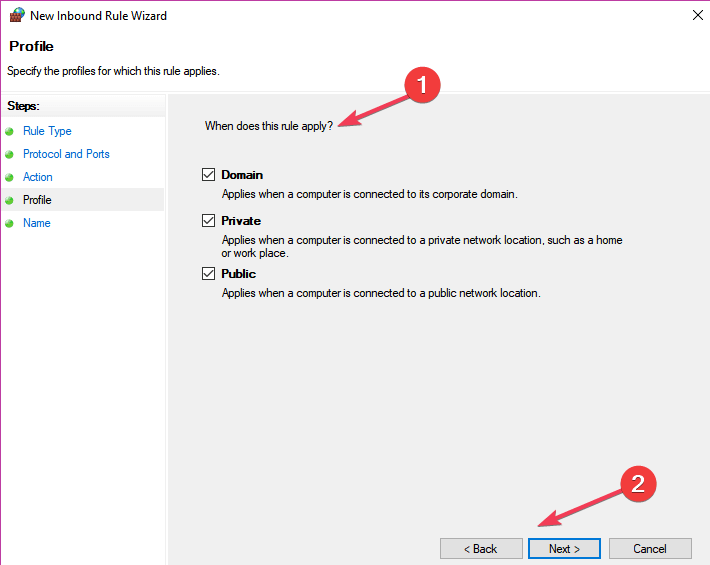
- Select the network type > click Next.
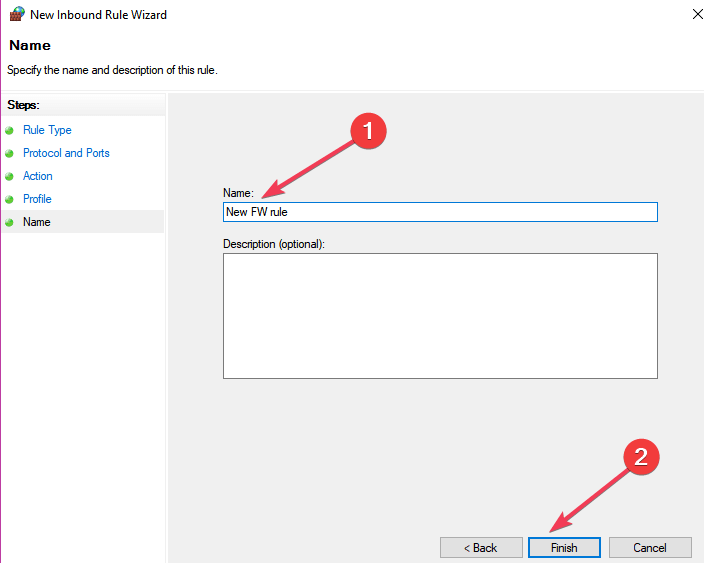
- Name the rule > click Finish.
These are all the necessary steps for opening a port in Windows 10. Remember that you can also use this method for blocking programs or ports.
Why should I use a Firewall on my PC?
Firewalls are targeted at protecting your network from various threats coming from outside and trying to get in or threats coming from inside trying to get out. A threat does this by blocking network-enabled ports.
Every time a program tries to communicate through this port, the firewall verifies its database rules to check if it is allowed or not. If it doesn’t know, it will ask the user and that’s why you sometimes see a prompt asking you if a certain program is allowed or not to access the Internet.
A firewall is an essential issue regarding computing and every PC must have one installed. This is the reason for which Windows has a firewall bundled and active as standard.
Windows firewall must occasionally be told to allow a program communicate with the network and this is the point where opening ports step into the picture.
RELATED STORIES TO CHECK OUT:
Configure Firewall Port Requirements for Group Policy
Applies To: Windows 8.1, Windows Server 2012 R2, Windows Server 2012, Windows 8
You can use the information in this topic to configure the firewall port requirements for Group Policy. Group Policy requires that firewall ports are opened on client computers for an administrator to perform these two remote operations:
By default, Windows Firewall enables all outbound network traffic,and it allows only inbound traffic that is enabled by firewall rules. This topic identifies the TCP and UDP ports for which you must have active firewall rules to allow the inbound traffic. This allows Group Policy to perform remote Group Policy Results reporting from client computers and to perform remote Group Policy refresh to client-based computers. You can use the information in this topic to configure non-Microsoft firewall products and to create a GPO to configure a client computer with the required firewall rules. This topic also presents two new starter Group Policy Objects (GPOs) that configure the proper firewall rules on client computers.
If you have configured client computers by using Group Policy, the Group Policy settings override any manual configuration of client computers to which the policies are applied. If you want to review these rules, from the Group Policy Management Console (GPMC), you can run a Group Policy Results report or Group Policy Planning report. Or from a client computer, open the Windows Firewall with Advanced Security MMC snap-in and click Inbound Rules . Membership in the Administrators group or equivalent is the minimum permissions required to make these configuration changes.
If you use a non-Microsoft firewall product, check your firewall product documentation for instructions about how to open these ports to allow network traffic as required by Group Policy.
Remote Resultant Set of Policy (RSoP) Group Policy results: ports that require firewall rules
You can use the RSoP feature of the GPMC to create detailed reports about the policy settings that are applied to computers or users who have signed in. When RSoP reporting targets remote computers, all connections are direct to each remote client from the computer running the GPMC (that is, not transitively through a domain controller).
To use RSoP reporting for remotely targeted computers through the firewall, you must have firewall rules that allow inbound network traffic on the ports listed in the following table. This allows remote WMI and event log traffic to flow between the computer running the GPMC and the remotely targeted computer.
Type of network traffic
TCP SMB 445, all services and programs
Remote Event Log Management (NP-in)
TCP RPC dynamic ports, EventLog (Windows Event Log service)
Remote Event Log Management (RPC)
TCP port 135, RPCSS (Remote Procedure Call service)
Remote Event Log Management (RPC-EPMAP)
TCP all ports, Winmgmt (Windows Management Instrumentation service)
Windows Management Instrumentation (WMI-in)
Configure firewall rules by creating a GPO from the Group Policy Reporting Firewall Ports Starter GPO and linking to the domain
In Windows Server 2012, Group Policy adds a new Starter GPO called, Group Policy Reporting Firewall Ports. This Starter GPO includes policy settings to configure the firewall rules that are specified in the previous table. This enables inbound network traffic on the ports, which is necessary to allow the GPMC to gather the Group Policy results RSoP information from a remote computer. It is a best practice to create a new GPO from this Starter GPO, and then link the new GPO to your domain with a higher precedence than the Default Domain GPO, so that you can configure all computers in the domain for remote Group Policy results reporting.
To create a GPO from the Group Policy Reporting Firewall Ports Starter GPO and link to the domain
In the GPMC console tree, right-click the domain for which you want to configure all computers to enable a remote Group Policy refresh, and then click Create a GPO in this domain, and Link it here…В
In the New GPO dialog box, type the name of the new Group Policy Object in the Name box.
Select the Group Policy Reporting Firewall Ports Starter GPO from the Source Starter GPO list that you want to use to create a new Group Policy Object.
If you do not see any Starter GPOs listed, cancel creating a GPO and do the following before you return to Step 1: Navigate to Starter GPOs . In the results pane, click Create Starter GPOs Folder .
Click OK.
In the results pane, click the Linked Group Policy Objects tab.
Select the GPO that you just created. Click the Up arrow until the GPO you just created is located above the Default Domain Policy. The new GPO will then have a smaller link-order value than the Default Domain Policy.
.jpeg)
The following Windows PowerShell cmdlet or cmdlets perform the same function as the preceding procedure. Enter each cmdlet on a single line, even though they may appear word-wrapped across several lines here because of formatting constraints.
You can use the New-GPO cmdlet with the –StarterGpoName parameter to create a new GPO. You can then pipe the output from the New-GPO cmdlet to the New-GPLink cmdlet.
For example, to create a new GPO, called Configure firewall rules for remote reporting, based on the Group Policy Reporting Firewall Ports Starter GPO, and link the GPO to the Contoso.com domain, type the following:
For more information about the New-GPO cmdlet and the New-GPLink cmdlet, see:
Remote Group Policy refresh: ports that require firewall rules
To schedule a remote Group Policy refresh for domain-joined computers you must have firewall rules that enable inbound network traffic on the ports listed in the following table.
Type of network traffic
TCP RPC dynamic ports, Schedule (Task Scheduler service)
Remote Scheduled Tasks Management (RPC)
TCP port 135, RPCSS (Remote Procedure Call service)
Remote Scheduled Tasks Management (RPC-EPMAP)
TCP all ports, Winmgmt (Windows Management Instrumentation service)
Windows Management Instrumentation (WMI-in)
Configure firewall rules by creating a GPO from the Group Policy Remote Update Firewall Ports Starter GPO and linking to the domain
In Windows Server 2012, Group Policy adds a new Starter GPO called Group Policy Remote Update Firewall Ports. This Starter GPO includes policy settings to configure the firewall rules that are specified in the previous table. This enables inbound network traffic on the ports, which is necessary to allow the remote Group Policy refresh to run. It is a best practice to create a new GPO from this Starter GPO, and then link the new GPO to your domain with a higher precedence than the Default Domain GPO, so that you can configure all computers in the domain to enable a remote Group Policy refresh.
To create a GPO from the Group Policy Remote Update Firewall Ports Starter GPO and link to the domain
In the GPMC console tree, right-click the domain for which you want to configure all computers to enable a remote Group Policy refresh, and then click Create a GPO in this domain, and Link it here…В
In the New GPO dialog box, type the name of the new Group Policy Object in the Name box.
Select the Group Policy Remote Update Firewall Ports Starter GPO from the Source Starter GPO list.
If you do not see any Starter GPOs listed, cancel creating a GPO and do the following before you return to the Step 1: Navigate to Starter GPOs In the results pane, click Create Starter GPOs Folder
Click OK.
In the results pane, click the Linked Group Policy Objects tab.
Select the GPO that you just created. Click the up arrow until the GPO you just created is above the Default Domain Policy in link order. The new GPO will then have a smaller link order value than the Default Domain Policy.
.jpeg)
The following Windows PowerShell cmdlet or cmdlets perform the same function as the preceding procedure. Enter each cmdlet on a single line, even though they may appear word-wrapped across several lines here because of formatting constraints.
You can use the New-GPO cmdlet with the –StarterGpoName parameter to create a new GPO. You can then pipe the output from the New-GPO cmdlet to the New-GPLink cmdlet.
For example, to create a new GPO, called Configure firewall rules for remote gpupdate, which is based on the Group Policy Remote Update Firewall Ports Starter GPO, and link the GPO to the Contoso.com domain, type the following:
For more information about the New-GPO cmdlet and the New-GPLink cmdlet, see:
Создание правила порта для входящего трафика Create an Inbound Port Rule
Область применения Applies to
- Windows 10 Windows 10
- Windows Server 2016 Windows Server 2016
Чтобы разрешить входящий сетевой трафик только по указанному номеру порта TCP или UDP, создайте правила брандмауэра с помощью брандмауэра Защитник Windows с дополнительными службами безопасности в оснастке управления групповыми политиками MMC. To allow inbound network traffic on only a specified TCP or UDP port number, use the Windows Defender Firewall with Advanced Security node in the Group Policy Management MMC snap-in to create firewall rules. Этот тип правила позволяет любой программе, которая прослушивает указанный TCP-порт или UDP-порт, получать сетевой трафик, отправленный на этот порт. This type of rule allows any program that listens on a specified TCP or UDP port to receive network traffic sent to that port.
Учетные данные администратора Administrative credentials
Для выполнения этих процедур необходимо быть членом группы «Администраторы домена» или получить другие делегирование разрешений на изменение таких групп. To complete these procedures, you must be a member of the Domain Administrators group, or otherwise be delegated permissions to modify the GPOs.
В этом разделе описывается создание стандартного правила порта для указанного протокола, TCP или номера порта UDP. This topic describes how to create a standard port rule for a specified protocol or TCP or UDP port number. Другие типы правил входящие порты см. в: For other inbound port rule types, see:
Создание правила порта для входящие To create an inbound port rule
Откройте консоль управления групповыми политиками для Защитник Windows брандмауэра с расширенными мерами безопасности. Open the Group Policy Management Console to Windows Defender Firewall with Advanced Security.
В области навигации щелкните «Правила для входящие». In the navigation pane, click Inbound Rules.
Щелкните «Действие» и выберите «Новое правило». Click Action, and then click New rule.
На странице «Тип правила» мастера «Новые правила для входящие» щелкните «Настраиваемый» и нажмите кнопку «Далее». On the Rule Type page of the New Inbound Rule Wizard, click Custom, and then click Next.
Примечание. Хотя правила можно создать, **** выбрав программу или порт, эти варианты ограничивают количество страниц, представленных мастером. Note: Although you can create rules by selecting Program or Port, those choices limit the number of pages presented by the wizard. Если выбрать настраиваемый, вы увидите все страницы и сможете с наибольшей гибкостью создавать правила. If you select Custom, you see all of the pages, and have the most flexibility in creating your rules.
На странице «Программа» щелкните «Все программы» и нажмите кнопку «Далее». On the Program page, click All programs, and then click Next.
Примечание. Этот тип правила часто используется в сочетании с программой или правилом службы. Note: This type of rule is often combined with a program or service rule. Если объединить типы правил, вы получите правило брандмауэра, которое ограничивает трафик указанным портом и разрешает трафик только при запуске указанной программы. If you combine the rule types, you get a firewall rule that limits traffic to a specified port and allows the traffic only when the specified program is running. Указанная программа не может принимать сетевой трафик через другие порты, а другие программы не могут принимать сетевой трафик на указанный порт. The specified program cannot receive network traffic on other ports, and other programs cannot receive network traffic on the specified port. Если вы решили сделать это, выполните действия, перечисленные в процедуре создания программы или правила службы для входящие данной процедуры, чтобы создать одно правило, которое фильтрует сетевой трафик с использованием программных и портовых критериев. If you choose to do this, follow the steps in the Create an Inbound Program or Service Rule procedure in addition to the steps in this procedure to create a single rule that filters network traffic using both program and port criteria.
На странице «Протокол и порты» выберите тип протокола, который необходимо разрешить. On the Protocol and Ports page, select the protocol type that you want to allow. Чтобы ограничить правило указанным номером порта, необходимо выбрать TCP или UDP. To restrict the rule to a specified port number, you must select either TCP or UDP. Так как это входящий правило, обычно настраивается только номер локального порта. Because this is an incoming rule, you typically configure only the local port number.
Если выбран другой протокол, то через брандмауэр будут разрешены только пакеты, поле протокола которых в IP-загорелом ip-адресе соответствует этому правилу. If you select another protocol, then only packets whose protocol field in the IP header match this rule are permitted through the firewall.
Чтобы выбрать протокол по его **** номеру, выберите «Настраиваемый» в списке и введите номер в поле «Номер протокола». To select a protocol by its number, select Custom from the list, and then type the number in the Protocol number box.
Настроив протоколы и порты, нажмите кнопку «Далее». When you have configured the protocols and ports, click Next.
На странице «Область» можно указать, что правило применяется только к сетевому трафику с IP-адресов, введенного на этой странице, или с них. On the Scope page, you can specify that the rule applies only to network traffic to or from the IP addresses entered on this page. Настройте его соответствующим образом и нажмите кнопку «Далее». Configure as appropriate for your design, and then click Next.
На странице действий выберите «Разрешить подключение» и нажмите кнопку «Далее». On the Action page, select Allow the connection, and then click Next.
На странице «Профиль» выберите типы сетевых расположений, к которым применяется это правило, и нажмите кнопку «Далее». On the Profile page, select the network location types to which this rule applies, and then click Next.
Примечание. Если этот объект GPO ориентирован на серверные компьютеры под управлением Windows Server 2008, которые никогда не перемещаются, рассмотрите возможность изменения правил для применения во всех профилях типов сетевых расположений. Note: If this GPO is targeted at server computers running Windows Server 2008 that never move, consider modifying the rules to apply to all network location type profiles. Это предотвращает непредвиденное изменение применяемых правил, если тип сетевого расположения изменяется из-за установки новой сетевой карты или отключения существующего кабеля сетевой карты. This prevents an unexpected change in the applied rules if the network location type changes due to the installation of a new network card or the disconnection of an existing network card’s cable. Отключенная сетовая карта автоматически назначена типу расположения в общедоступных сетях. A disconnected network card is automatically assigned to the Public network location type.
На странице «Имя» введите имя и описание правила и нажмите кнопку «Готово». On the Name page, type a name and description for your rule, and then click Finish.