- Create an Outbound Program or Service Rule
- Включение стандартных правил для исходящего трафика Enable Predefined Outbound Rules
- Best practices for configuring Windows Defender Firewall
- Keep default settings
- Understand rule precedence for inbound rules
- Create rules for new applications before first launch
- Inbound allow rules
- Known issues with automatic rule creation
- Establish local policy merge and application rules
- Know how to use «shields up» mode for active attacks
- Create outbound rules
- Document your changes
Create an Outbound Program or Service Rule
Applies to
- WindowsВ 10
- Windows Server 2016
By default, Windows Defender Firewall allows all outbound network traffic unless it matches a rule that prohibits the traffic. To block outbound network traffic for a specified program or service, use the Windows Defender Firewall with Advanced Security node in the Group Policy Management console to create firewall rules. This type of rule prevents the program from sending any outbound network traffic on any port.
Administrative credentials
To complete these procedures, you must be a member of the Domain Administrators group, or otherwise be delegated permissions to modify the GPOs.
To create an outbound firewall rule for a program or service
In the navigation pane, click Outbound Rules.
Click Action, and then click New rule.
On the Rule Type page of the New Outbound Rule Wizard, click Custom, and then click Next.
Note:В В Although you can create many rules by selecting Program or Port, those choices limit the number of pages presented by the wizard. If you select Custom, you see all of the pages, and have the most flexibility in creating your rules.
On the Program page, click This program path.
Type the path to the program in the text box. Use environment variables as appropriate to ensure that programs installed in different locations on different computers work correctly.
Do one of the following:
If the executable file contains a single program, click Next.
If the executable file is a container for multiple services that must all be blocked from sending outbound network traffic, click Customize, select Apply to services only, click OK, and then click Next.
If the executable file is a container for a single service or contains multiple services but the rule only applies to one of them, click Customize, select Apply to this service, and then select the service from the list. If the service does not appear in the list, then click Apply to service with this service short name, and type the short name for the service in the text box. Click OK, and then click Next.
If you want the program to be allowed to send on some ports, but blocked from sending on others, then you can restrict the firewall rule to block only the specified ports or protocols. On the Protocols and Ports page, you can specify the port numbers or protocol numbers for the blocked traffic. If the program tries to send to or from a port number different from the one specified here, or by using a protocol number different from the one specified here, then the default outbound firewall behavior allows the traffic. For more information about the protocol and port options, see Create an Outbound Port Rule. When you have configured the protocol and port options, click Next.
On the Scope page, you can specify that the rule applies only to network traffic to or from the IP addresses entered on this page. Configure as appropriate for your design, and then click Next.
On the Action page, select Block the connection, and then click Next.
On the Profile page, select the network location types to which this rule applies, and then click Next.
On the Name page, type a name and description for your rule, and then click Finish.
Включение стандартных правил для исходящего трафика Enable Predefined Outbound Rules
Область применения Applies to
- Windows 10 Windows 10
- Windows Server 2016 Windows Server 2016
По умолчанию брандмауэр Защитник Windows с дополнительными мерами безопасности разрешает весь исходящие сетевые трафик, если он не соответствует правилу, запрещая этот трафик. By default, Windows Defender Firewall with Advanced Security allows all outbound network traffic unless it matches a rule that prohibits the traffic. Защитник Windows брандмауэра включает множество предопределяющих правил исходящие трафика, которые можно использовать для блокировки сетевого трафика для общих сетевых ролей и функций. Windows Defender Firewall includes many predefined outbound rules that can be used to block network traffic for common networking roles and functions. Когда вы устанавливаете новую роль сервера на компьютер или включаете сетевой функцию на клиентский компьютер, установщик может установить, но обычно не включает правила блокировки исходящие почты для этой роли. When you install a new server role on a computer or enable a network feature on a client computer, the installer can install, but typically does not enable, outbound block rules for that role. При развертывании правил брандмауэра на компьютерах в сети можно использовать эти предопределяющие правила вместо создания новых. When deploying firewall rules to the computers on the network, you can take advantage of these predefined rules instead of creating new ones. Это помогает обеспечить согласованность и точность, так как правила были тщательно протестированы и готовы к использованию. Doing this helps to ensure consistency and accuracy, because the rules have been thoroughly tested and are ready for use.
Учетные данные администратора Administrative credentials
Для выполнения этих процедур необходимо быть членом группы «Администраторы домена» или получить другие делегирование разрешений на изменение таких групп. To complete these procedures, you must be a member of the Domain Administrators group, or otherwise be delegated permissions to modify the GPOs.
Развертывание предопределения правил брандмауэра, которые блокируют исходящие сетевые трафикы для общих сетевых функций To deploy predefined firewall rules that block outbound network traffic for common network functions
Откройте консоль управления групповыми политиками для Защитник Windows брандмауэра с расширенными мерами безопасности. Open the Group Policy Management Console to Windows Defender Firewall with Advanced Security.
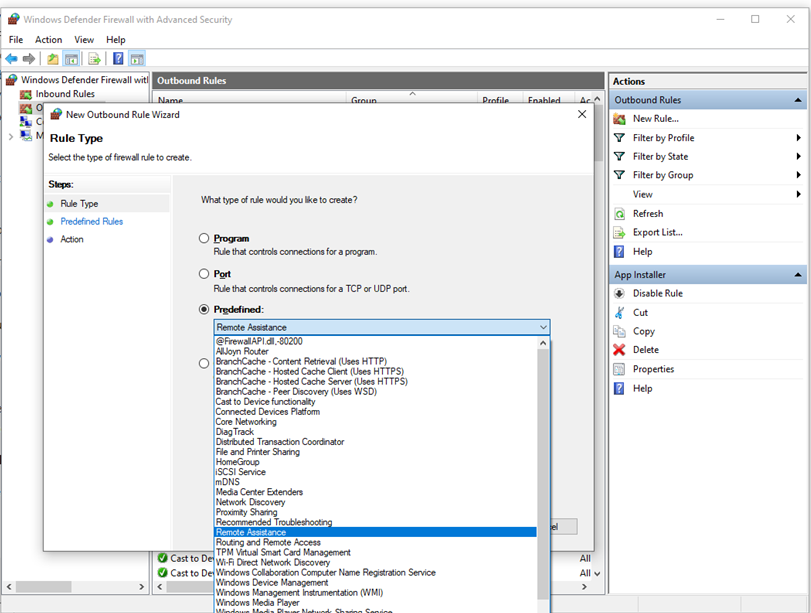
В области навигации щелкните «Правила исходящие жатия». In the navigation pane, click Outbound Rules.
Щелкните «Действие» и выберите «Новое правило». Click Action, and then click New rule.
На странице «Тип правила» мастера «Новые правила для входящие» щелкните «Предопределен», **** выберите категорию правил из списка и нажмите кнопку «Далее». On the Rule Type page of the New Inbound Rule Wizard, click Predefined, select the rule category from the list, and then click Next.
На странице «Предварительно определенные правила» отображается список правил, определенных в группе. On the Predefined Rules page, the list of rules defined in the group is displayed. Все они выбраны по умолчанию. They are all selected by default. Для правил, которые не нужно развертывать, сделайте флажки рядом с правилами и нажмите кнопку «Далее». For rules that you do not want to deploy, clear the check boxes next to the rules, and then click Next.
На странице действий выберите «Заблокировать подключение» и нажмите кнопку «Готово». On the Action page, select Block the connection, and then click Finish.
Выбранные правила добавляются в GPO. The selected rules are added to the GPO.
Best practices for configuring Windows Defender Firewall
Applies to
Windows operating systems including WindowsВ 10
Windows Server Operating Systems
Windows Defender Firewall with Advanced Security provides host-based, two-way network traffic filtering and blocks unauthorized network traffic flowing into or out of the local device. Configuring your Windows Firewall based on the following best practices can help you optimize protection for devices in your network. These recommendations cover a wide range of deployments including home networks and enterprise desktop/server systems.
To open Windows Firewall, go to theВ StartВ menu, selectВ Run, typeВ WF.msc, and then selectВ OK. See also Open Windows Firewall.
Keep default settings
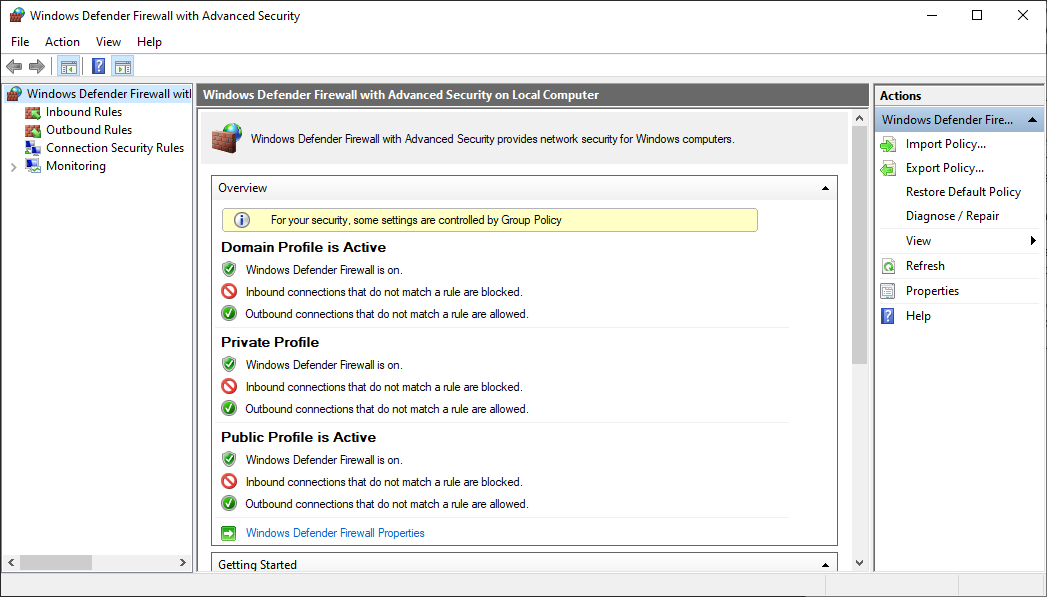
When you open the Windows Defender Firewall for the first time, you can see the default settings applicable to the local computer. The Overview panel displays security settings for each type of network to which the device can connect.
Figure 1: Windows Defender Firewall
Domain profile: Used for networks where there is a system of account authentication against a domain controller (DC), such as an Azure Active Directory DC
Private profile: Designed for and best used in private networks such as a home network
Public profile: Designed with higher security in mind for public networks like Wi-Fi hotspots, coffee shops, airports, hotels, or stores
View detailed settings for each profile by right-clicking the top-level Windows Defender Firewall with Advanced Security node in the left pane and then selecting Properties.
Maintain the default settings in Windows Defender Firewall whenever possible. These settings have been designed to secure your device for use in most network scenarios. One key example is the default Block behavior for Inbound connections.
Figure 2: Default inbound/outbound settings
To maintain maximum security, do not change the default Block setting for inbound connections.
Understand rule precedence for inbound rules
In many cases, a next step for administrators will be to customize these profiles using rules (sometimes called filters) so that they can work with user apps or other types of software. For example, an administrator or user may choose to add a rule to accommodate a program, open a port or protocol, or allow a predefined type of traffic.
This can be accomplished by right-clicking either Inbound Rules or Outbound Rules, and selecting New Rule. The interface for adding a new rule looks like this:
Figure 3: Rule Creation Wizard
This article does not cover step-by-step rule configuration. See the Windows Firewall with Advanced Security Deployment Guide for general guidance on policy creation.
In many cases, allowing specific types of inbound traffic will be required for applications to function in the network. Administrators should keep the following rule precedence behaviors in mind when allowing these inbound exceptions.
Explicitly defined allow rules will take precedence over the default block setting.
Explicit block rules will take precedence over any conflicting allow rules.
More specific rules will take precedence over less specific rules, except in the case of explicit block rules as mentioned in 2. (For example, if the parameters of rule 1 includes an IP address range, while the parameters of rule 2 include a single IP host address, rule 2 will take precedence.)
Because of 1 and 2, it is important that, when designing a set of policies, you make sure that there are no other explicit block rules in place that could inadvertently overlap, thus preventing the traffic flow you wish to allow.
A general security best practice when creating inbound rules is to be as specific as possible. However, when new rules must be made that use ports or IP addresses, consider using consecutive ranges or subnets instead of individual addresses or ports where possible. This avoids creation of multiple filters under the hood, reduces complexity, and helps to avoid performance degradation.
Windows Defender Firewall does not support traditional weighted, administrator-assigned rule ordering. An effective policy set with expected behaviors can be created by keeping in mind the few, consistent, and logical rule behaviors described above.
Create rules for new applications before first launch
Inbound allow rules
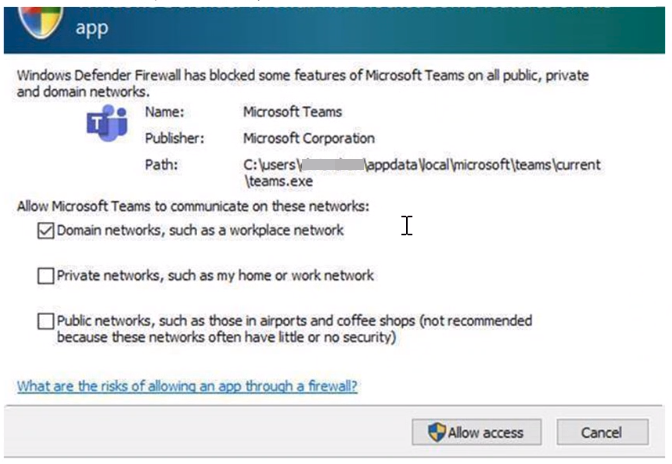
When first installed, networked applications and services issue a listen call specifying the protocol/port information required for them to function properly. As there is a default block action in Windows Defender Firewall, it is necessary to create inbound exception rules to allow this traffic. It is common for the app or the app installer itself to add this firewall rule. Otherwise, the user (or firewall admin on behalf of the user) needs to manually create a rule.
If there are no active application or administrator-defined allow rule(s), a dialog box will prompt the user to either allow or block an application’s packets the first time the app is launched or tries to communicate in the network.
If the user has admin permissions, they will be prompted. If they respond No or cancel the prompt, block rules will be created. Two rules are typically created, one each for TCP and UDP traffic.
If the user is not a local admin, they will not be prompted. In most cases, block rules will be created.
In either of the scenarios above, once these rules are added they must be deleted in order to generate the prompt again. If not, the traffic will continue to be blocked.
The firewall’s default settings are designed for security. Allowing all inbound connections by default introduces the network to various threats. Therefore, creating exceptions for inbound connections from third-party software should be determined by trusted app developers, the user, or the admin on behalf of the user.
Known issues with automatic rule creation
When designing a set of firewall policies for your network, it is a best practice to configure allow rules for any networked applications deployed on the host. Having these rules in place before the user first launches the application will help ensure a seamless experience.
The absence of these staged rules does not necessarily mean that in the end an application will be unable to communicate on the network. However, the behaviors involved in the automatic creation of application rules at runtime requires user interaction.
To determine why some applications are blocked from communicating in the network, check for the following:
A user with sufficient privileges receives a query notification advising them that the application needs to make a change to the firewall policy. Not fully understanding the prompt, the user cancels or dismisses the prompt.
A user lacks sufficient privileges and is therefore not prompted to allow the application to make the appropriate policy changes.
Local Policy Merge is disabled, preventing the application or network service from creating local rules.
Figure 4: Dialog box to allow access
Establish local policy merge and application rules
Firewall rules can be deployed:
- Locally using the Firewall snap-in (WF.msc)
- Locally using PowerShell
- Remotely using Group Policy if the device is a member of an Active Directory Name, System Center Configuration Manager (SCCM), or Intune (using workplace join)
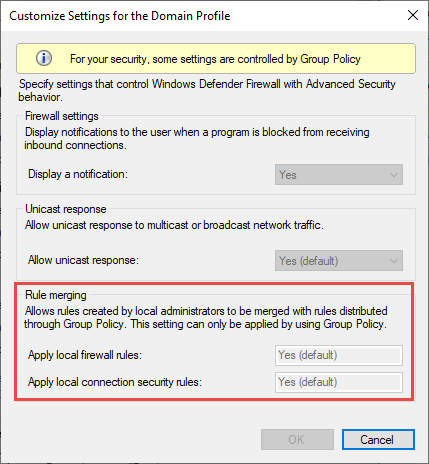
Rule merging settings control how rules from different policy sources can be combined. Administrators can configure different merge behaviors for Domain, Private, and Public profiles.
The rule merging settings either allow or prevent local admins from creating their own firewall rules in addition to those obtained from Group Policy.
Figure 5: Rule merging setting
In the firewall configuration service provider, the equivalent setting is AllowLocalPolicyMerge. This setting can be found under each respective profile node, DomainProfile, PrivateProfile, and PublicProfile.
If merging of local policies is disabled, centralized deployment of rules is required for any app that needs inbound connectivity.
Admins may disable LocalPolicyMerge in high security environments to maintain tighter control over endpoints. This can impact some apps and services that automatically generate a local firewall policy upon installation as discussed above. For these types of apps and services to work, admins should push rules centrally via group policy (GP), Mobile Device Management (MDM), or both (for hybrid or co-management environments).
Firewall CSP and Policy CSP also have settings that can affect rule merging.
As a best practice, it is important to list and log such apps, including the network ports used for communications. Typically, you can find what ports must be open for a given service on the app’s website. For more complex or customer application deployments, a more thorough analysis may be needed using network packet capture tools.
In general, to maintain maximum security, admins should only push firewall exceptions for apps and services determined to serve legitimate purposes.
The use of wildcard patterns, such as C:*\teams.exe is not supported in application rules. We currently only support rules created using the full path to the application(s).
Know how to use «shields up» mode for active attacks
An important firewall feature you can use to mitigate damage during an active attack is the «shields up» mode. It is an informal term referring to an easy method a firewall administrator can use to temporarily increase security in the face of an active attack.
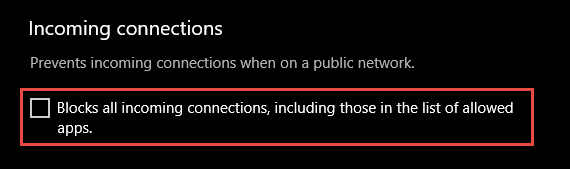
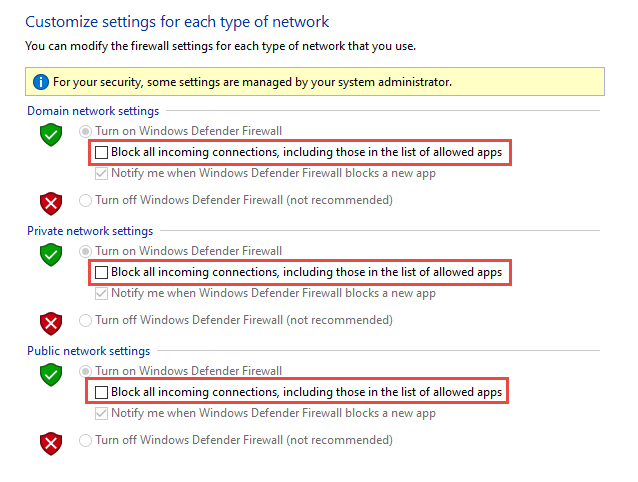
Shields up can be achieved by checking Block all incoming connections, including those in the list of allowed apps setting found in either the Windows Settings app or the legacy file firewall.cpl.
Figure 6: Windows settings App/Windows Security/Firewall Protection/Network Type
Figure 7: Legacy firewall.cpl
By default, the Windows Defender Firewall will block everything unless there is an exception rule created. This setting overrides the exceptions.
For example, the Remote Desktop feature automatically creates firewall rules when enabled. However, if there is an active exploit using multiple ports and services on a host, you can, instead of disabling individual rules, use the shields up mode to block all inbound connections, overriding previous exceptions, including the rules for Remote Desktop. The Remote Desktop rules remain intact but remote access will not work as long as shields up is activated.
Once the emergency is over, uncheck the setting to restore regular network traffic.
Create outbound rules
What follows are a few general guidelines for configuring outbound rules.
The default configuration of Blocked for Outbound rules can be considered for certain highly secure environments. However, the Inbound rule configuration should never be changed in a way that Allows traffic by default.
It is recommended to Allow Outbound by default for most deployments for the sake of simplification around app deployments, unless the enterprise prefers tight security controls over ease-of-use.
In high security environments, an inventory of all enterprise-spanning apps must be taken and logged by the administrator or administrators. Records must include whether an app used requires network connectivity. Administrators will need to create new rules specific to each app that needs network connectivity and push those rules centrally, via group policy (GP), Mobile Device Management (MDM), or both (for hybrid or co-management environments).
For tasks related to creating outbound rules, see Checklist: Creating Outbound Firewall Rules.
Document your changes
When creating an inbound or outbound rule, you should specify details about the app itself, the port range used, and important notes like creation date. Rules must be well-documented for ease of review both by you and other admins. We highly encourage taking the time to make the work of reviewing your firewall rules at a later date easier. AndВ neverВ create unnecessary holes in your firewall.